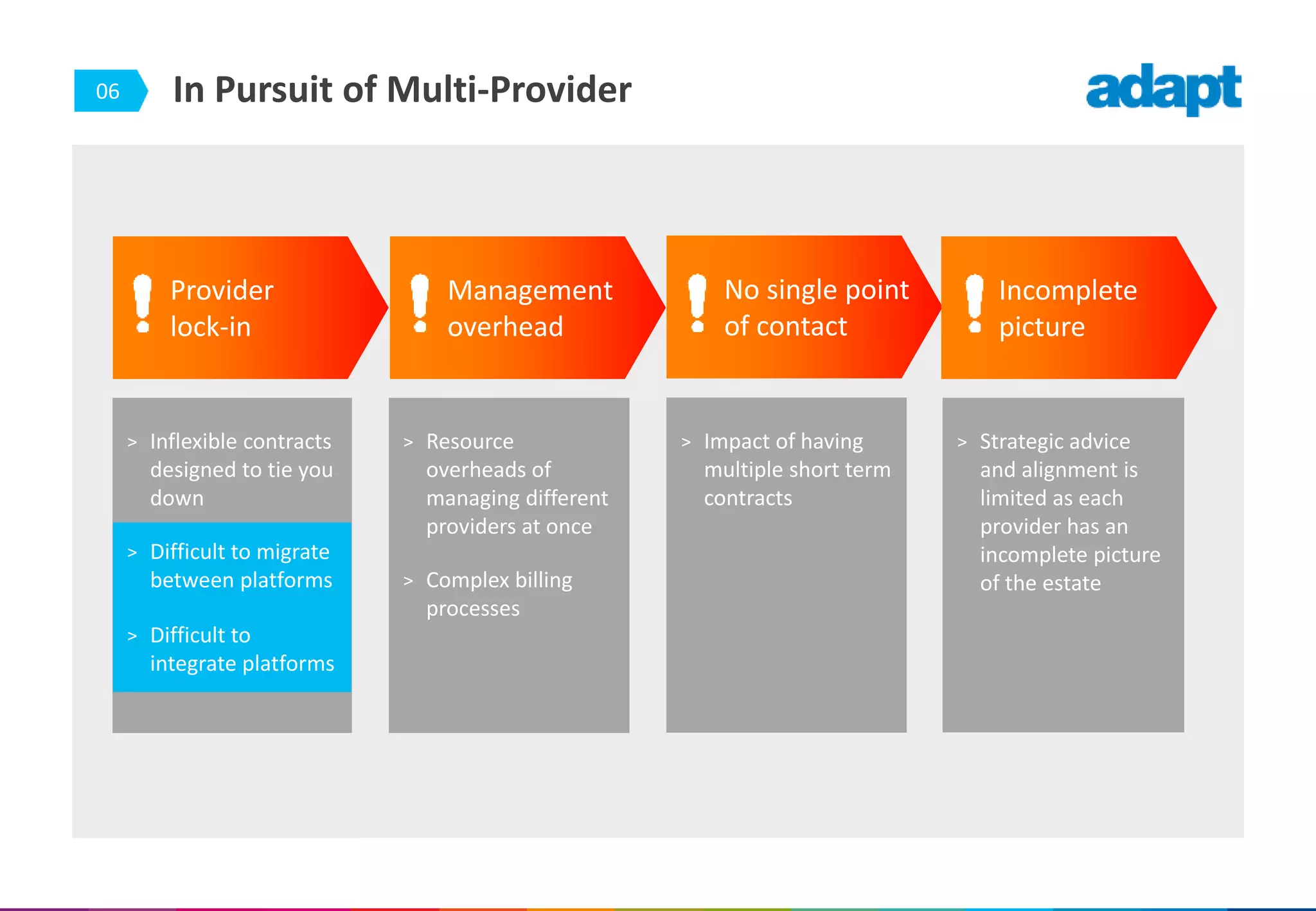
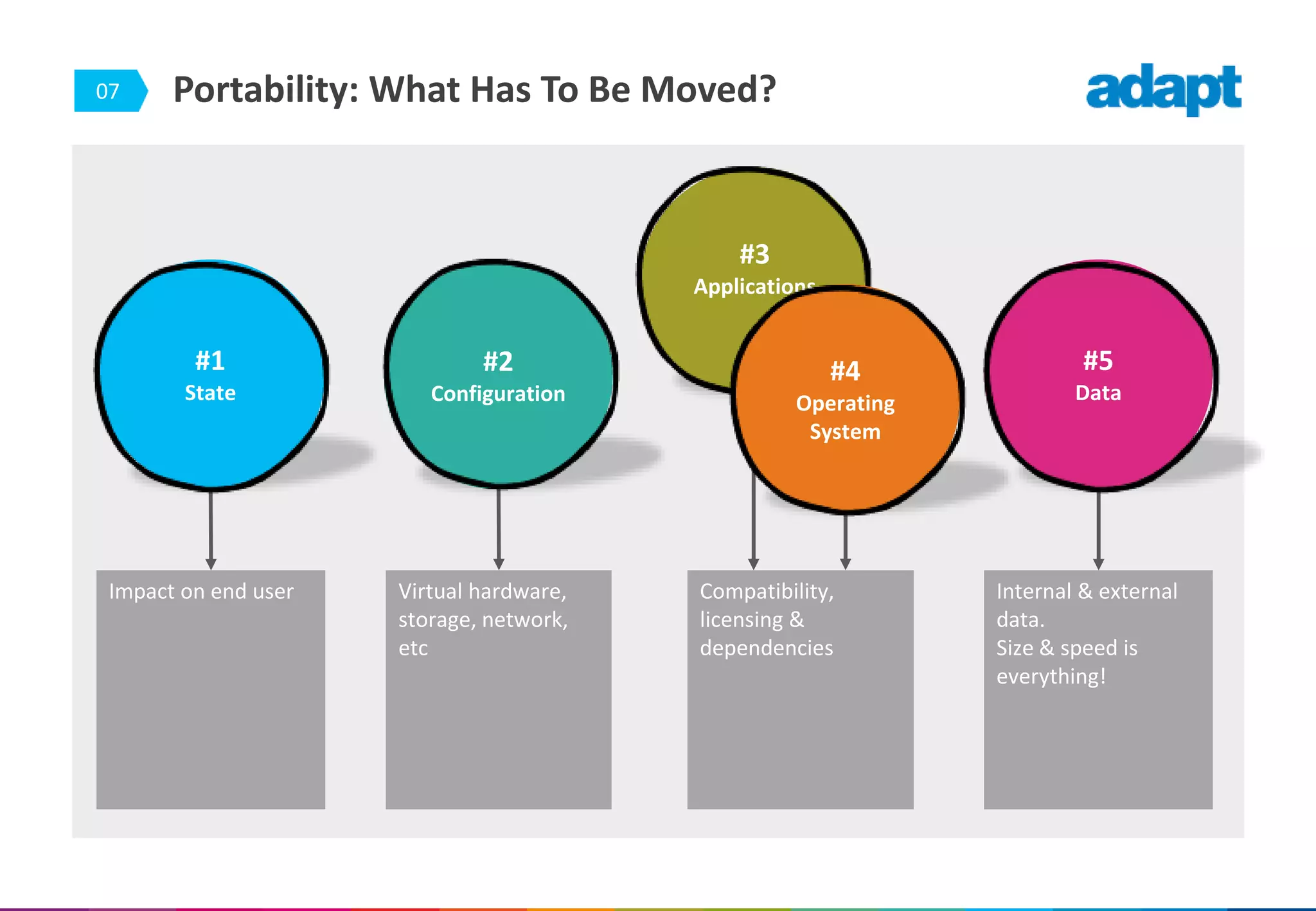
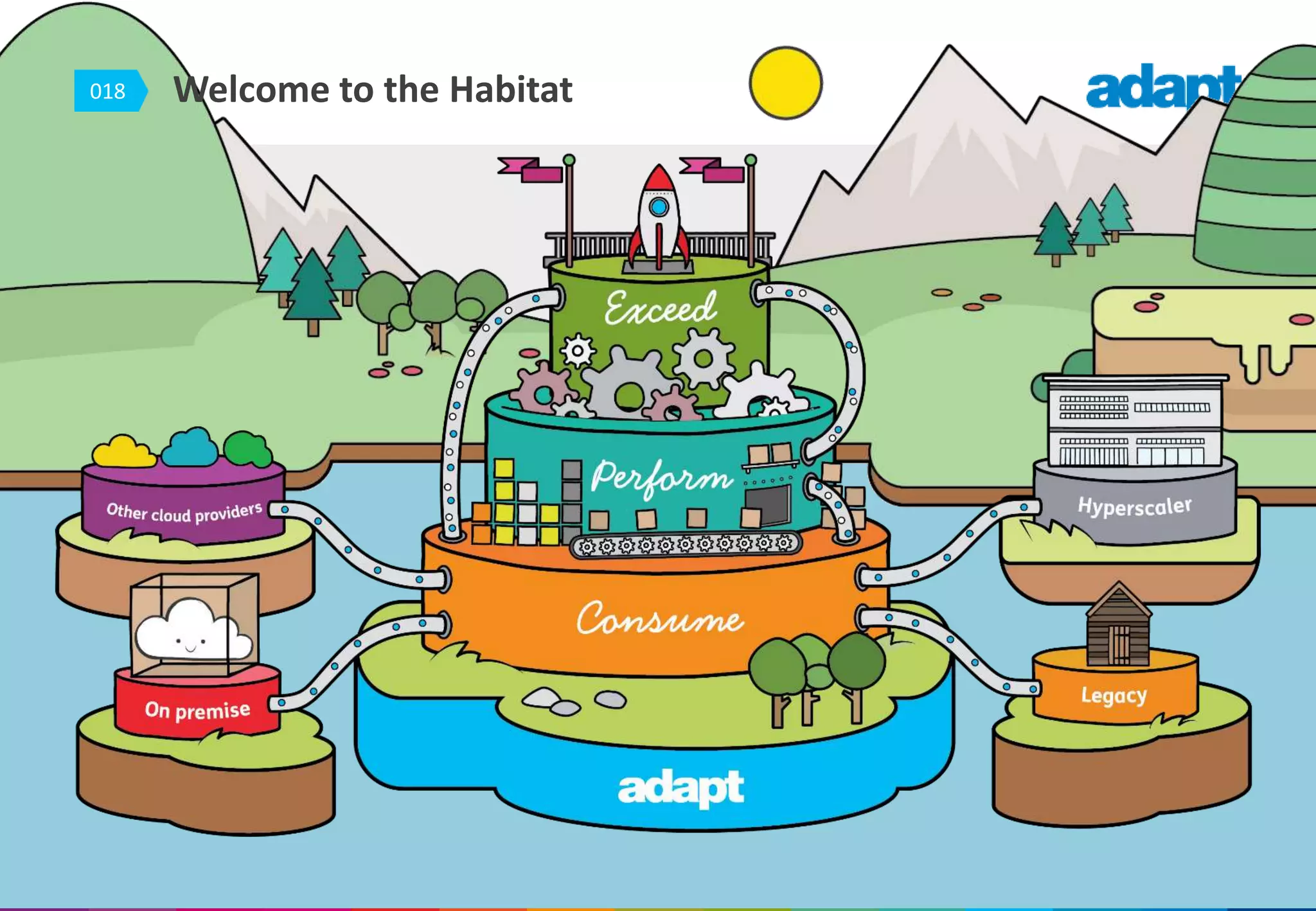
The document discusses the challenges of workload portability within multi-provider cloud environments, highlighting issues like inflexible contracts, difficulties in migration and integration, and the complexities of managing multiple providers. It details key considerations for moving data, operating systems, and applications, with emphasis on licensing, configuration, and data management. Additionally, it showcases solutions offered by companies like Zerto and Cisco to facilitate seamless transitions between different cloud platforms.