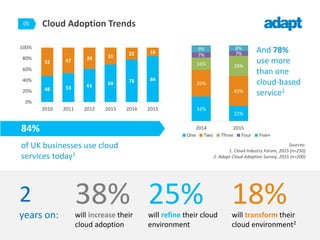
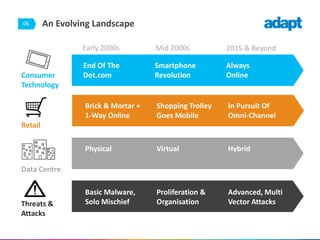
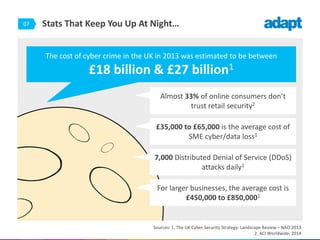
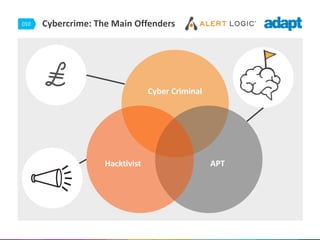
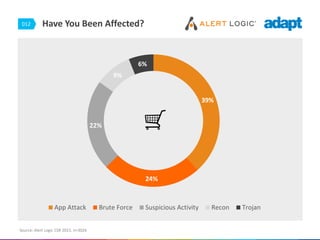
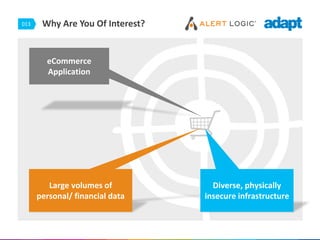
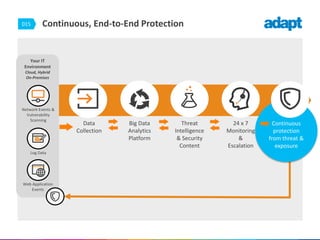
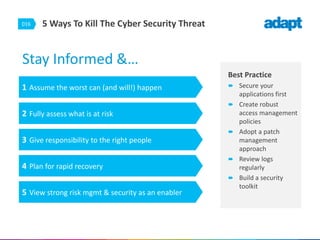
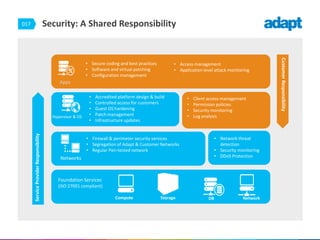
The document discusses cloud security in the retail sector, emphasizing the growing adoption of cloud technologies and the increasing cyber threats these businesses face. Key statistics are highlighted, including a significant percentage of consumers distrusting retail security and the high costs associated with cybercrime. To mitigate threats, it proposes comprehensive security measures, including continuous monitoring, robust access policies, and effective patch management.