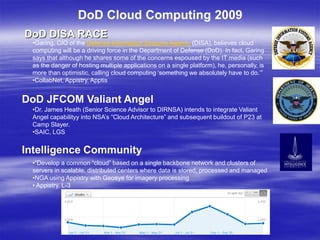
The document discusses the adoption of cloud computing across various parts of the US Department of Defense (DoD) and intelligence community. It outlines several early cloud computing projects from 2009 including the DoD DISA RACE and JFCOM Valiant Angel programs. It also discusses the National Security Agency's adoption of Hadoop and MapReduce for intelligence gathering. The document concludes that cloud computing adoption in the DoD and intelligence community has been rapid as the benefits are seen to outweigh security concerns, with system integrators building cloud offerings to support operational use cases.