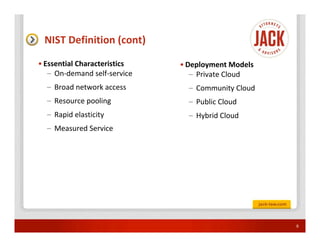
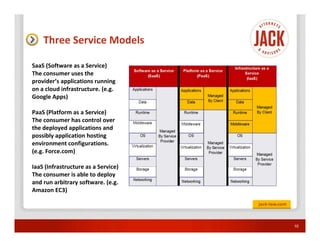
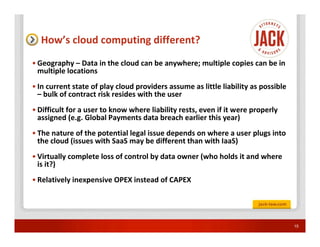
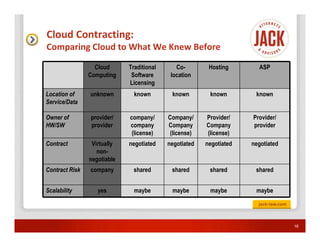
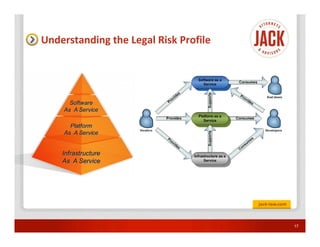
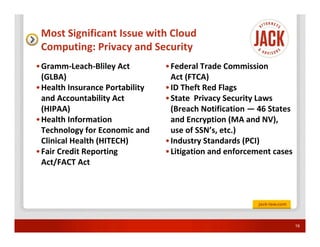
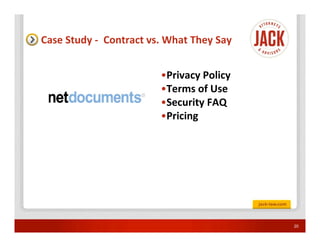
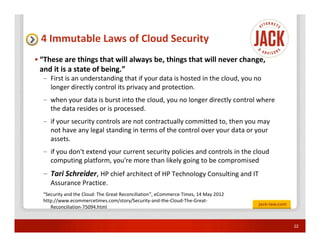
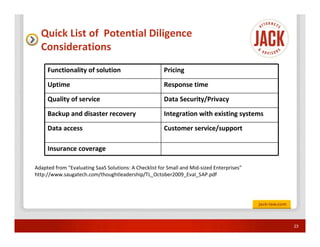
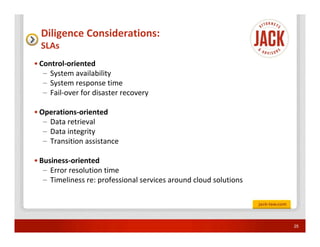
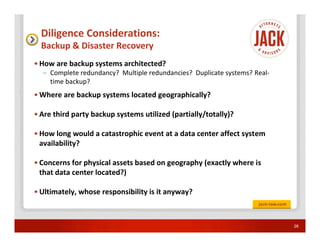
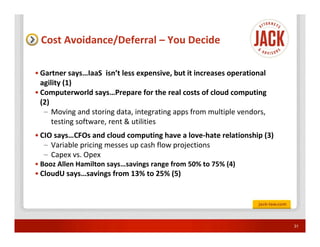
The document discusses the evolving landscape of cloud computing, highlighting its definitions, service models, and the significant considerations around contracting, privacy, and security. As organizations increasingly adopt cloud services for efficiency and cost-saving, the document emphasizes the need for due diligence in understanding legal risks and the importance of contractual protections. It concludes with practical takeaways for businesses to evaluate their cloud strategies thoughtfully.