The document outlines a plan to improve cybersecurity and resilience through acquisition reform. It discusses:
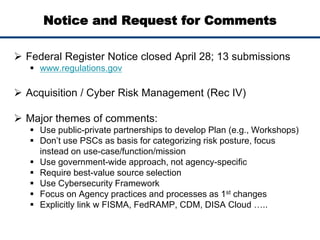
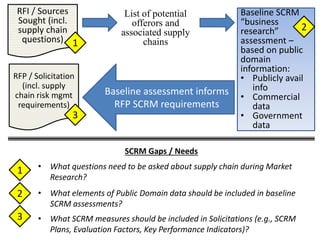
1) The need for acquisition reform to address cybersecurity risks that persist throughout an acquired item's lifespan. Currently, varied practices make consistently managing risks difficult.
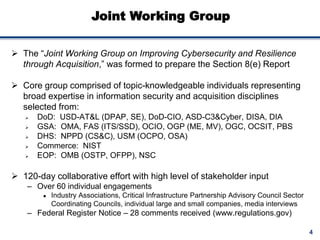
2) An executive order directing agencies to provide stronger protections for critical systems. A joint working group was formed to prepare recommendations.
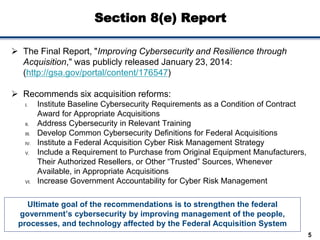
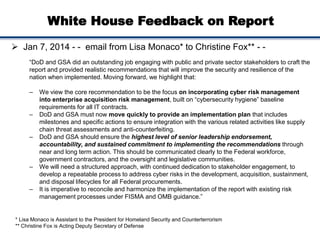
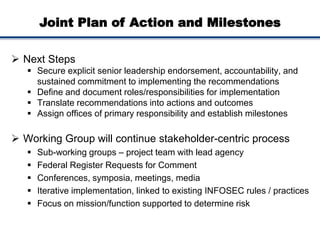
3) The working group's final report, which recommends six acquisition reforms, including instituting baseline cybersecurity requirements and developing common definitions. The White House supported moving quickly to an implementation plan with milestones.