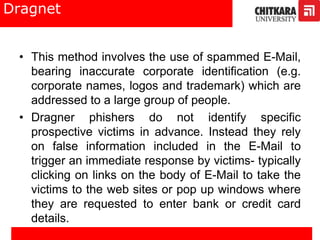
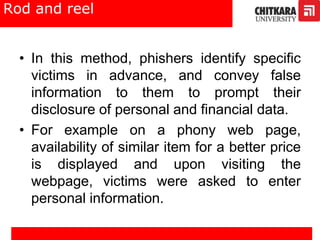
This document discusses phishing and identity theft. It defines phishing as attempting to acquire sensitive information like usernames, passwords, and credit card details by disguising as a trustworthy entity. Common phishing techniques mentioned include URL manipulation, filters, website forgery, flash phishing, social phishing, and phone phishing. The document also covers identity theft types and prevention methods.