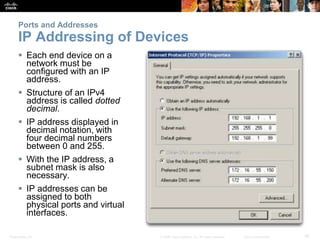
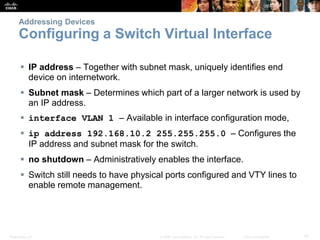
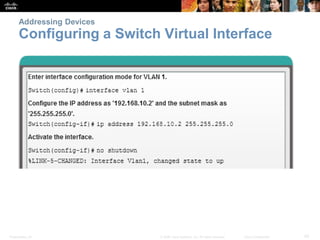
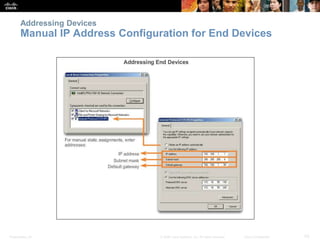
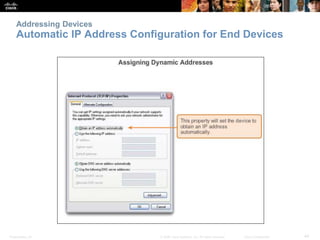
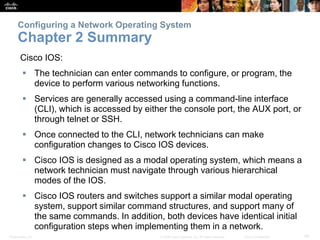
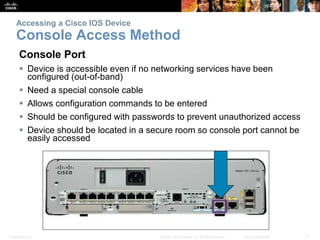
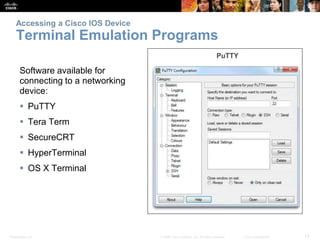
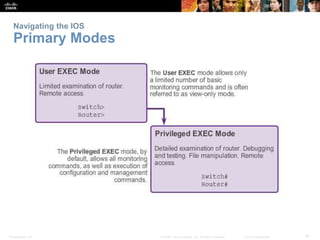
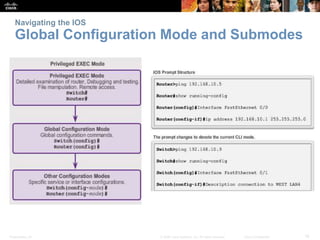
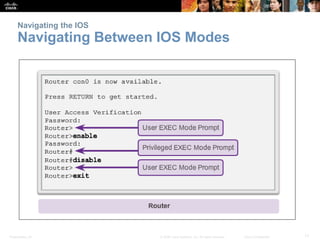
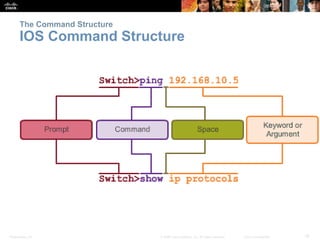
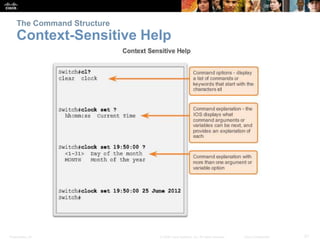
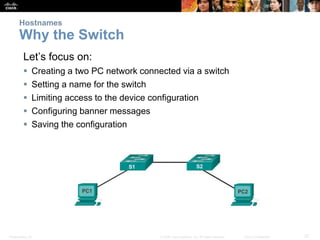
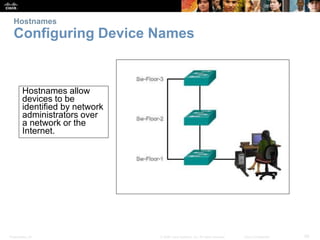
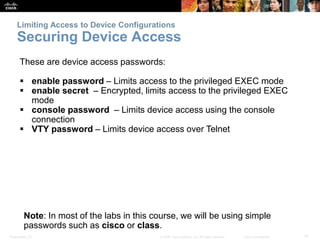
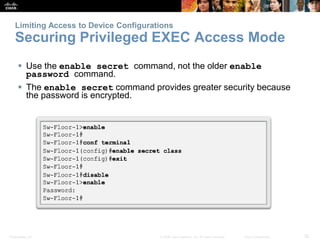
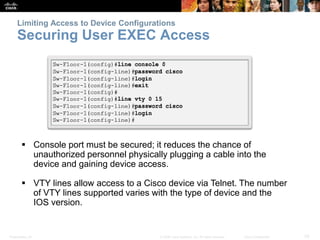
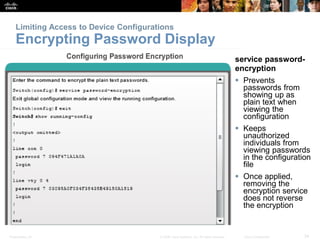
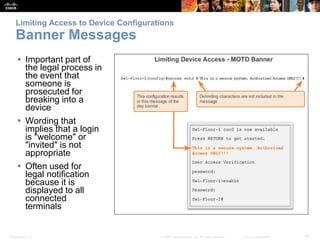
This document provides an overview of Cisco IOS, its purpose, and how to configure it for networking devices. Key topics include accessing the IOS via different methods, configuring device hostnames, managing access and passwords, and setting up IP addressing. The document emphasizes the importance of command-line interface (CLI) navigation and defining basic configurations for network connectivity.
![Presentation_ID 36© 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential
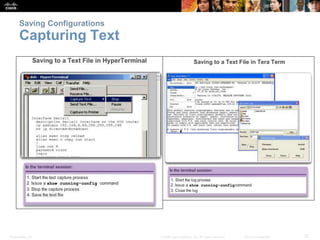
Saving Configurations
Configuration Files Switch# reload
System configuration has
been modified. Save?
[yes/no]: n
Proceed with reload?
[confirm]
Startup configuration is
removed by using
the erase startup-
config
Switch# erase startup-
config
On a switch, you must also
issue the delete
vlan.dat
Switch# delete
vlan.dat
Delete filename
[vlan.dat]?
Delete flash:vlan.dat?
[confirm]](https://image.slidesharecdn.com/chapter2-configuringanetworkoperatingsystem-170611140615/85/Chapter-2-Configuring-a-network-operating-system-36-320.jpg)