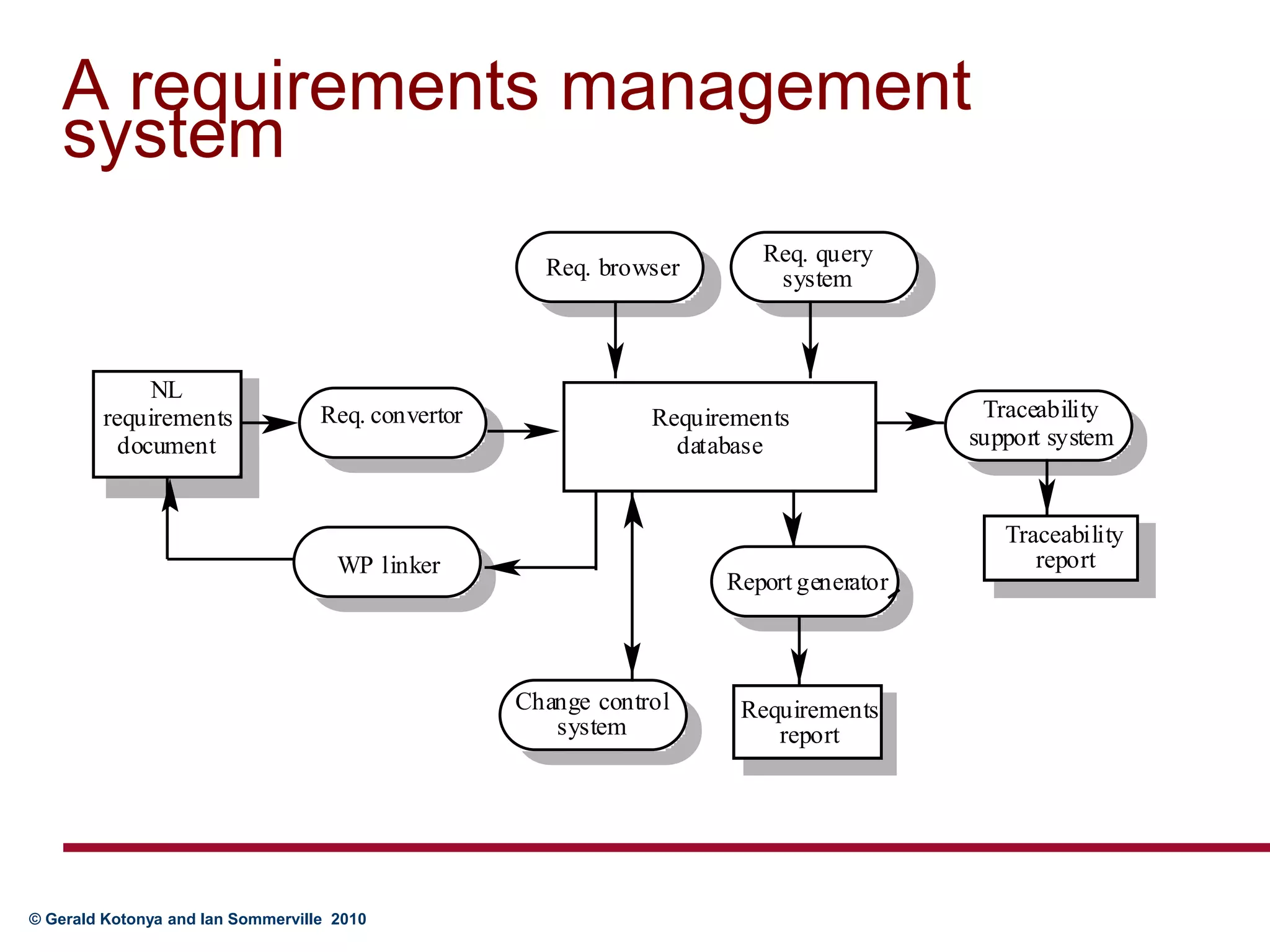
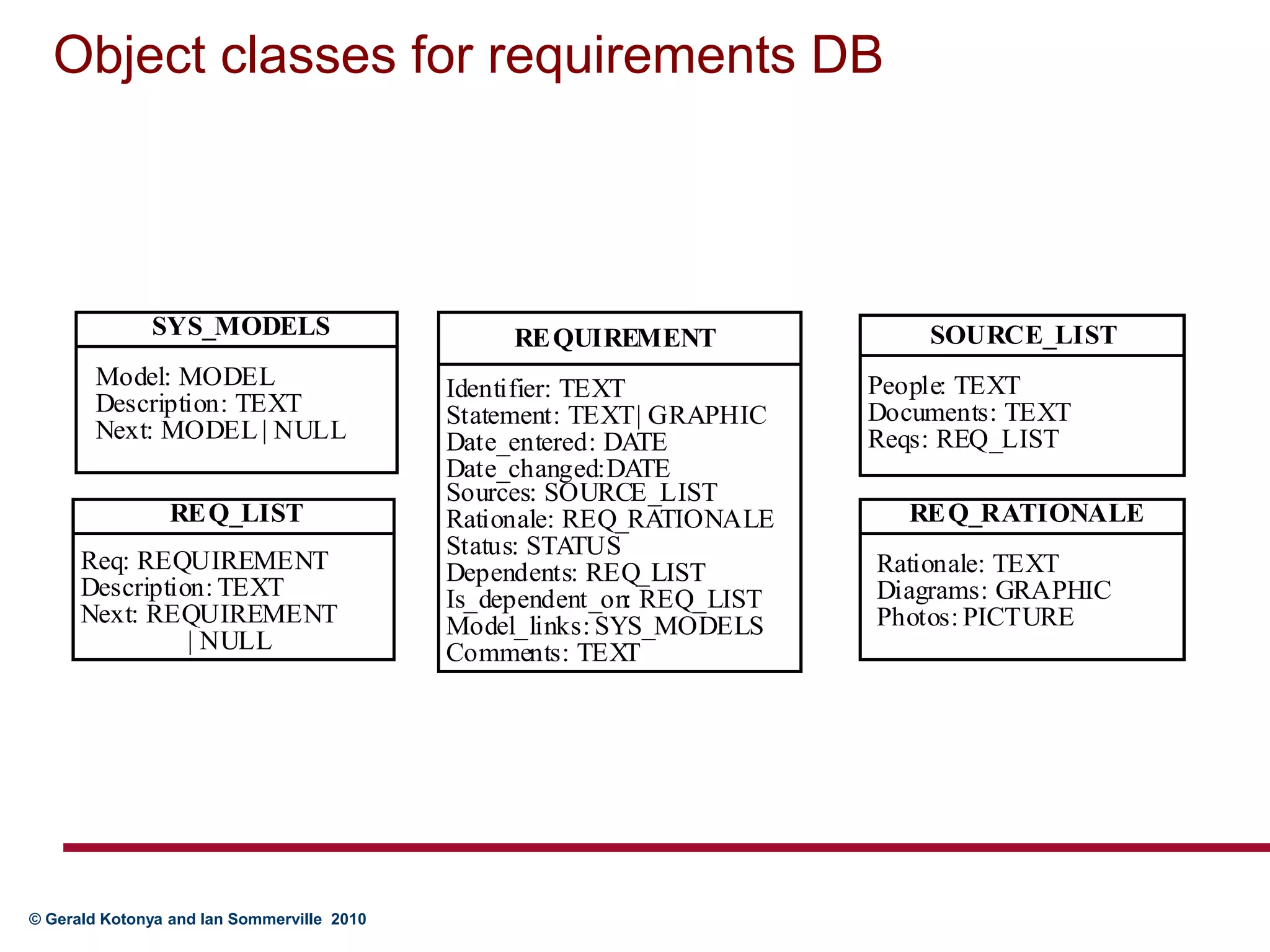
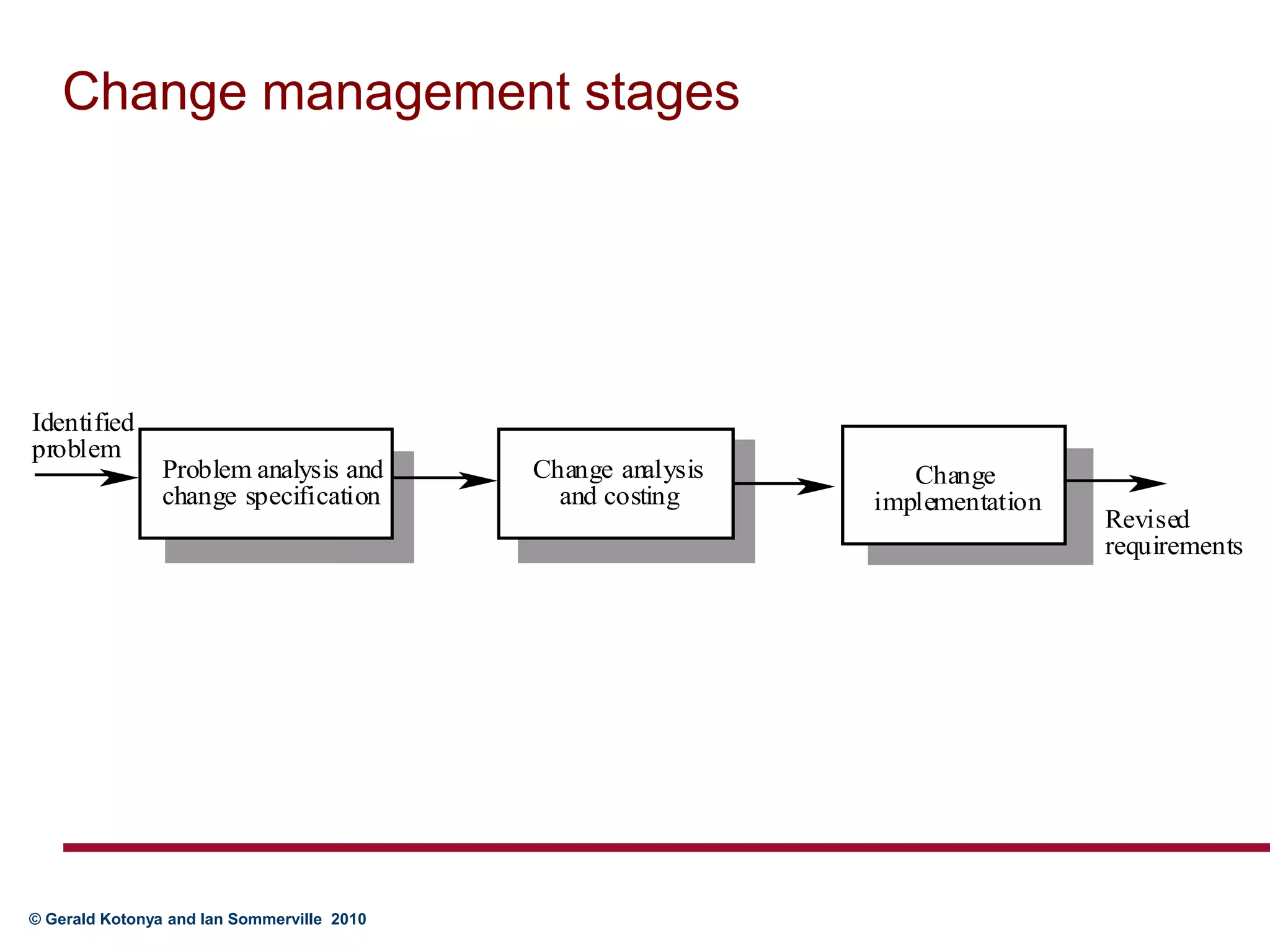
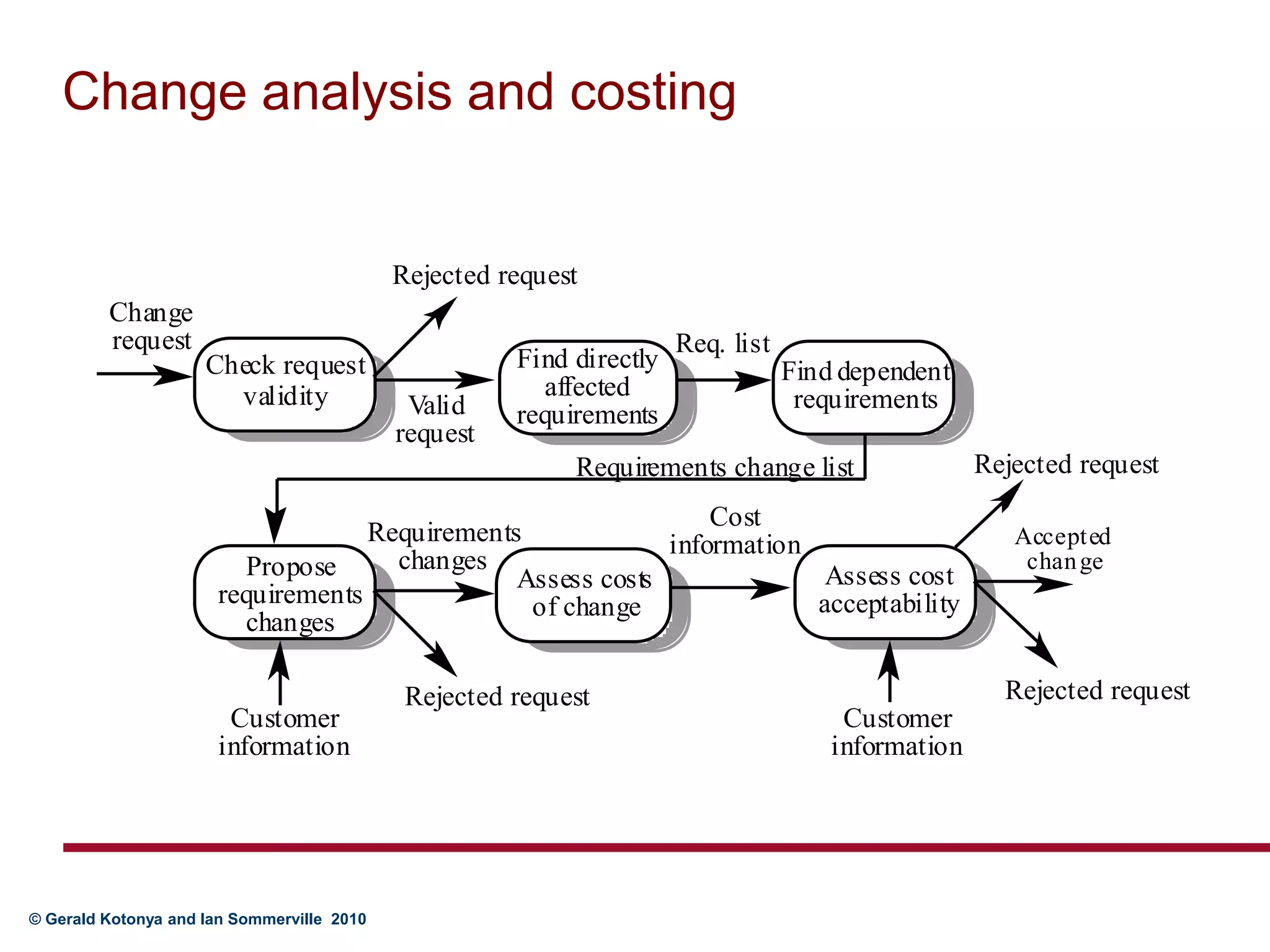
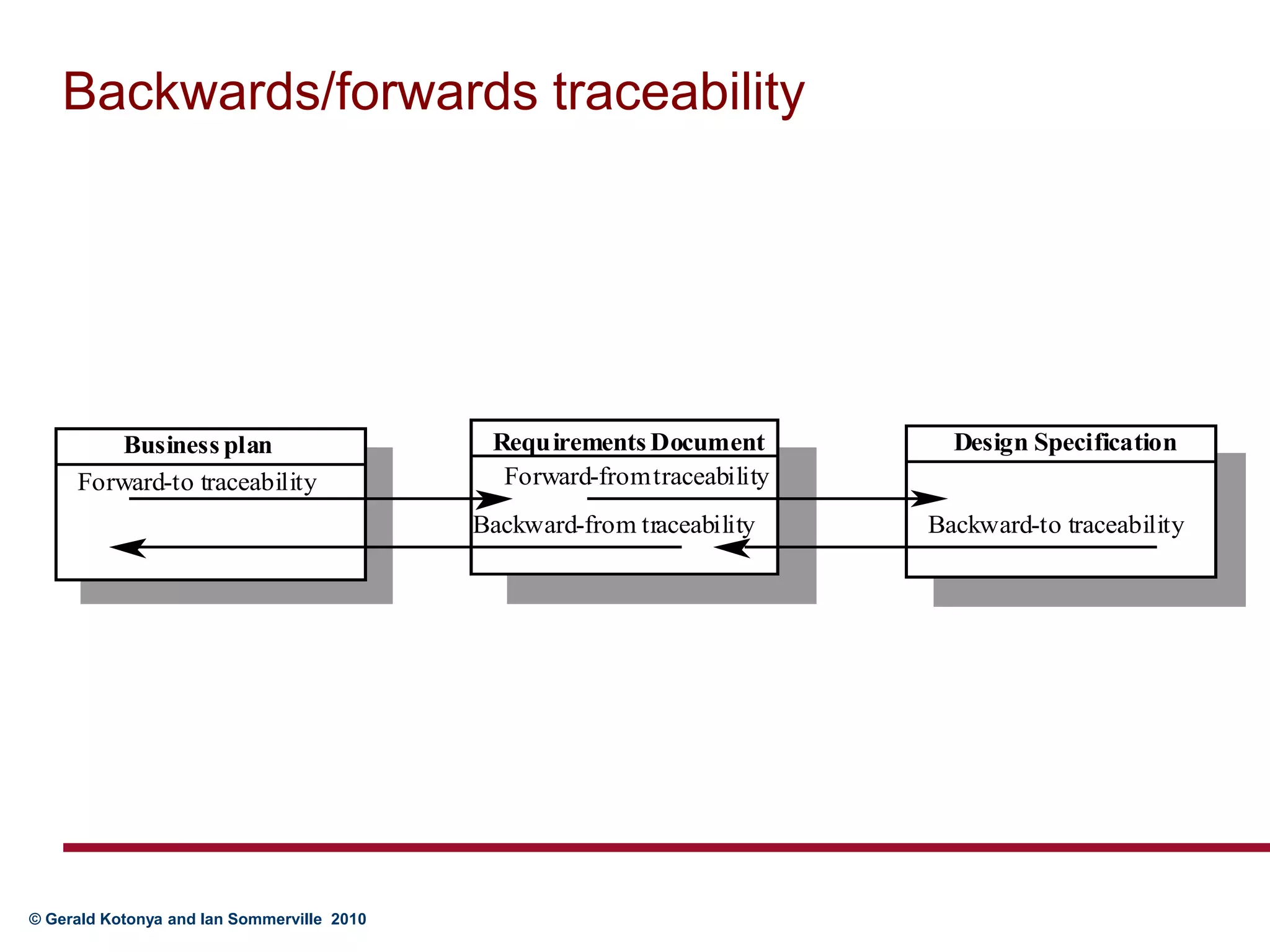
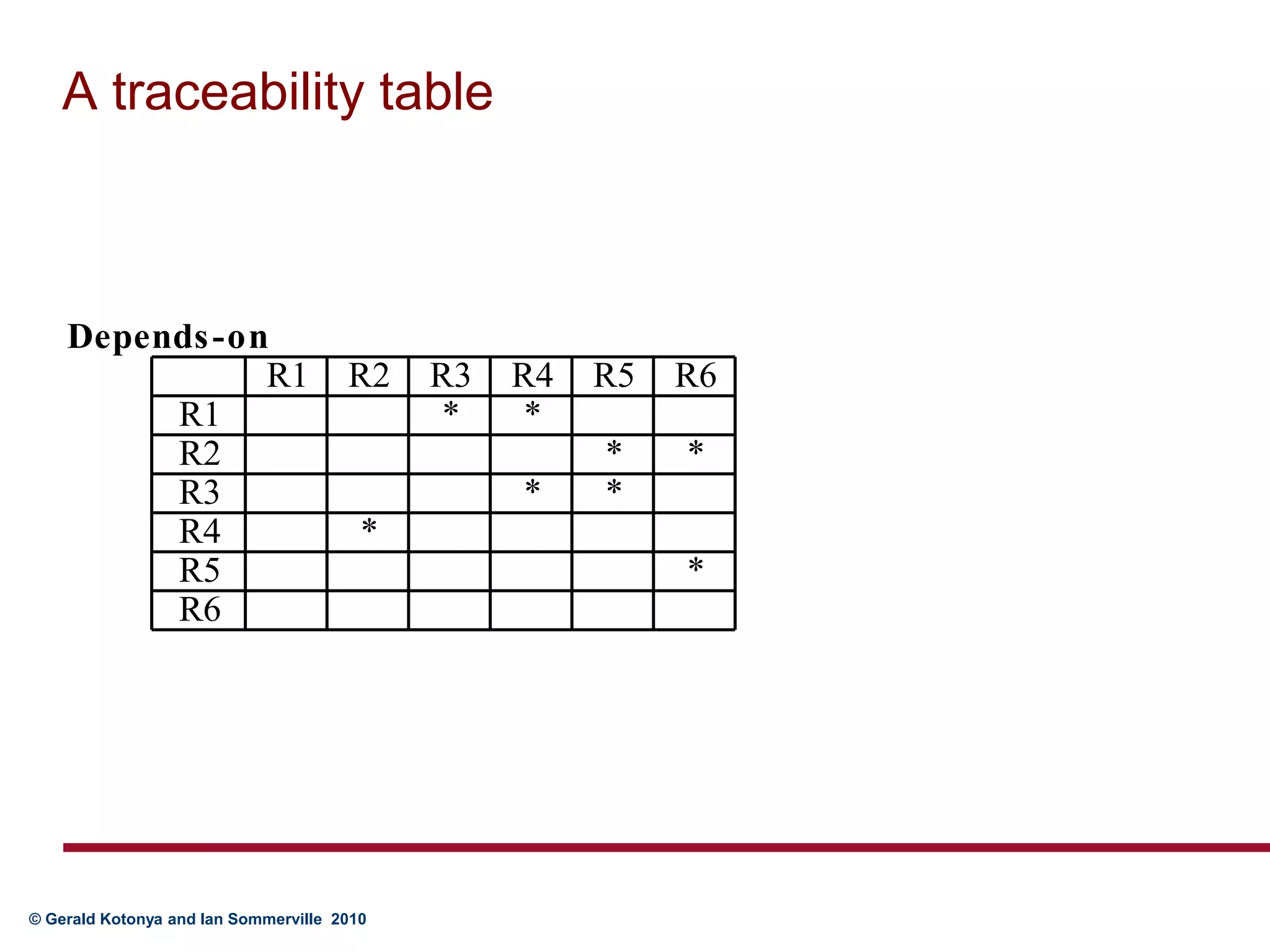
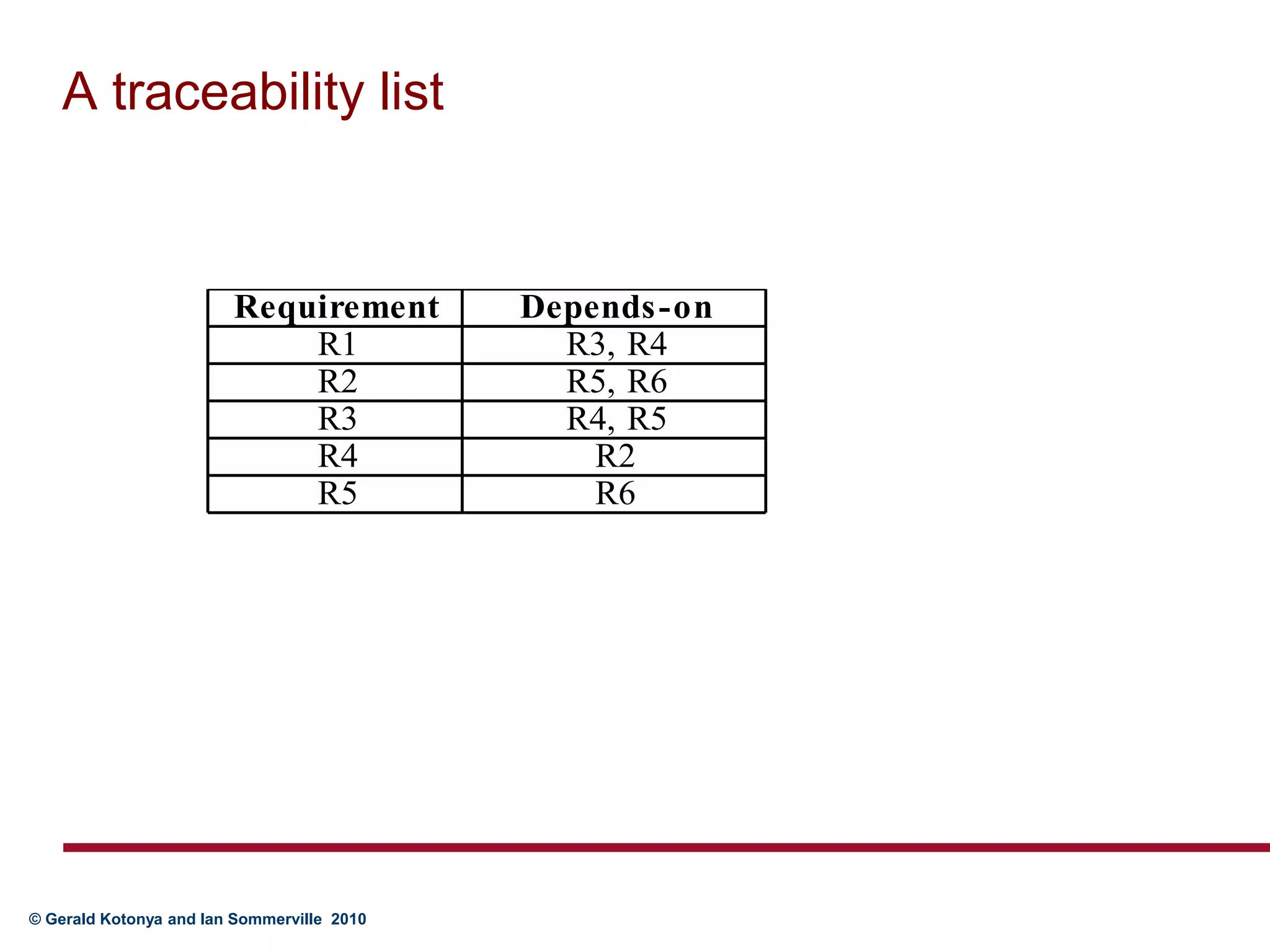
Requirements management involves collecting, storing, and maintaining requirements and related information. It aims to manage changes to requirements and dependencies between requirements. Traceability links requirements to their sources and related designs/documents. Change management defines processes for handling change requests, analyzing impacts, and implementing changes. Traceability and change management policies help control costs by defining what information to collect and maintain.