The document discusses the process of requirements engineering for software development. It involves four main steps:
1) Feasibility study to determine if the project is possible.
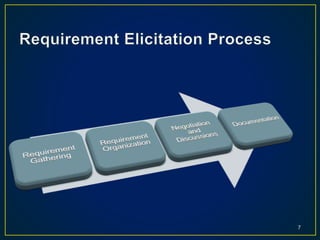
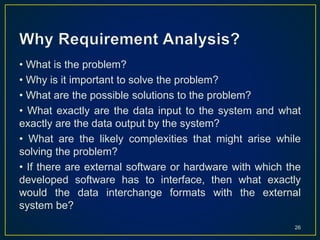
2) Requirements gathering by communicating with clients and users to understand what the software should do.
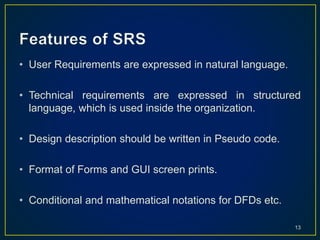
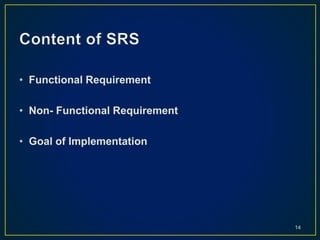
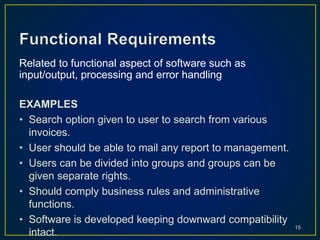
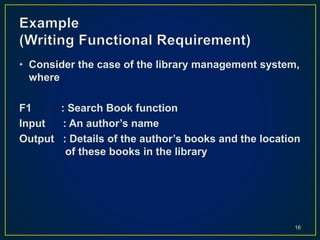
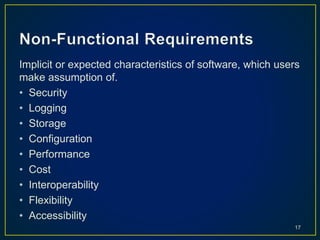
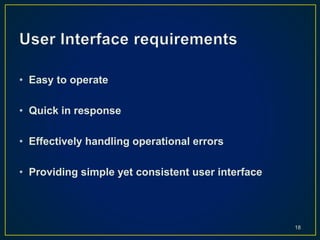
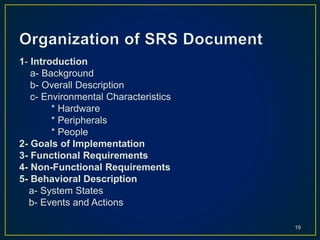
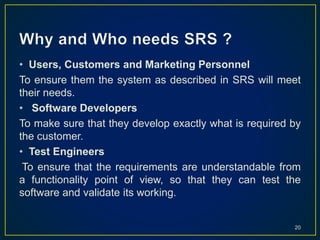
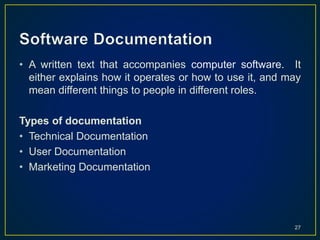
3) Creating a software requirements specification (SRS) document that defines system functions and constraints.
4) Validating requirements to ensure they are clear, consistent, and can be implemented.