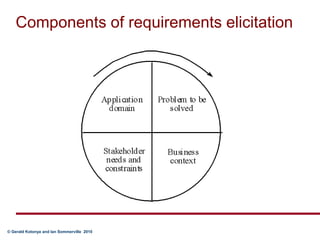
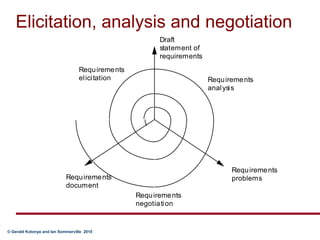
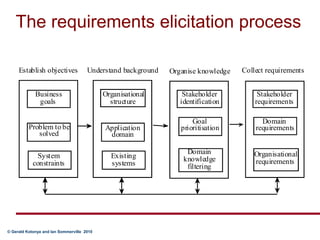
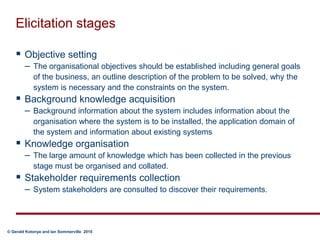
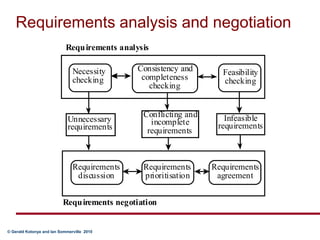
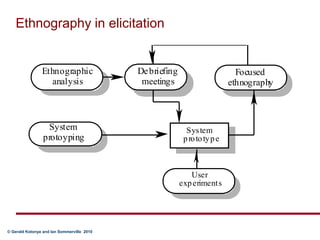
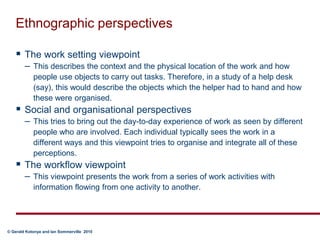
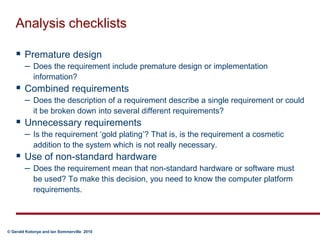
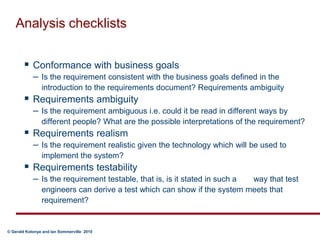
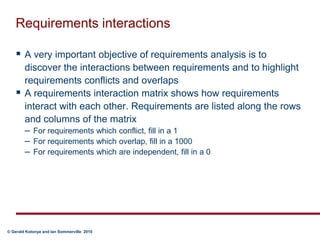
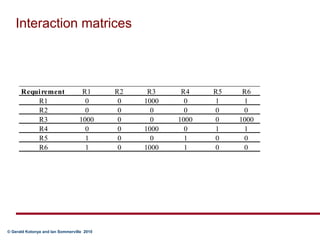
This document discusses requirements elicitation and analysis. It describes the components and stages of elicitation including understanding the problem domain, stakeholders' needs, and collecting requirements. Analysis techniques are discussed like necessity, consistency, and feasibility checking. Requirements elicitation involves iterative negotiation when conflicts arise. Various techniques are presented like interviews, scenarios, prototyping and observation to understand requirements.