The document provides details of two lab assignments for a computer programming course. The first assignment introduces concepts like variables, data types, if/else statements and asks students to write 10 programs demonstrating these concepts. The second assignment covers loops, arrays, switch case and asks students to write 6 programs applying these concepts. It provides the details, date and expectations for evaluating the assignments.
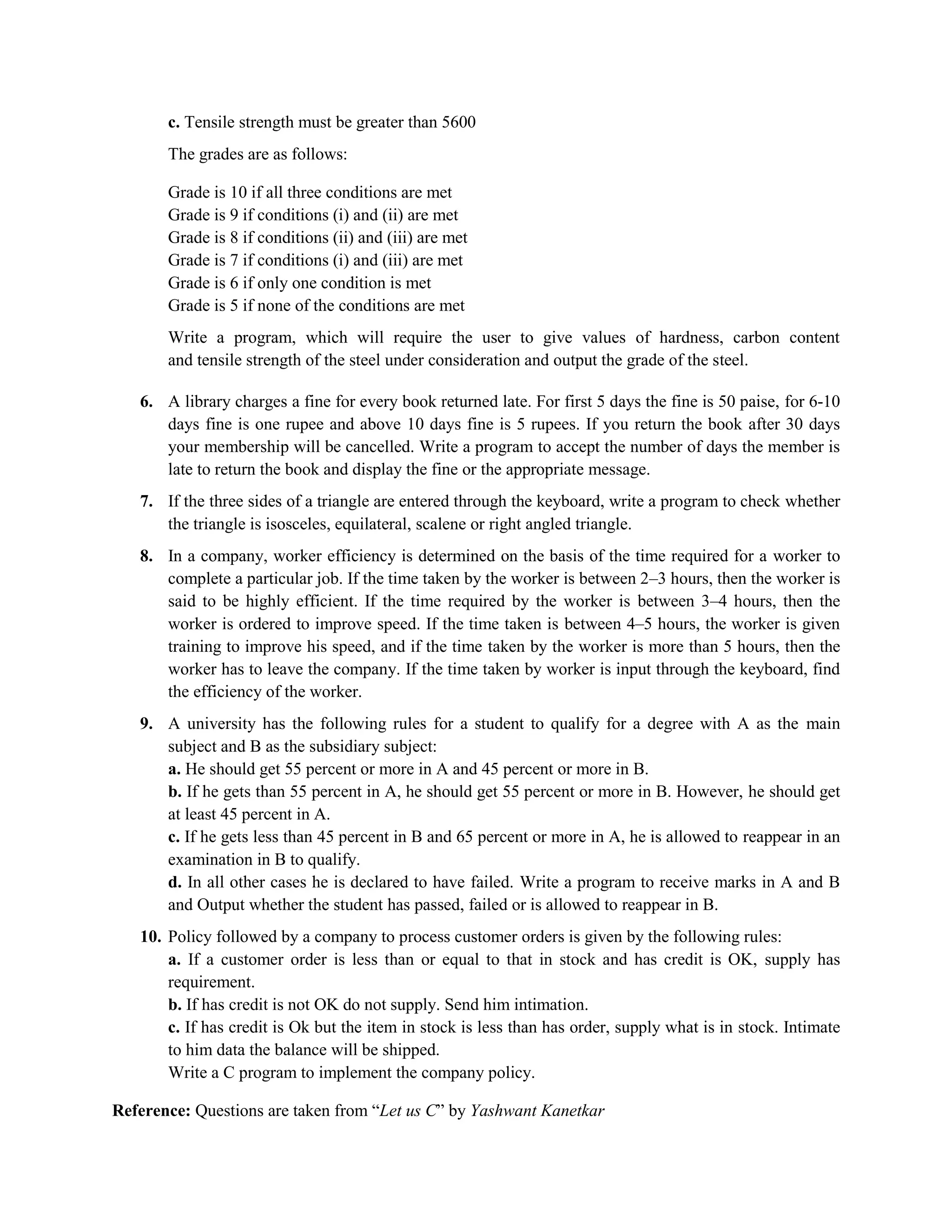

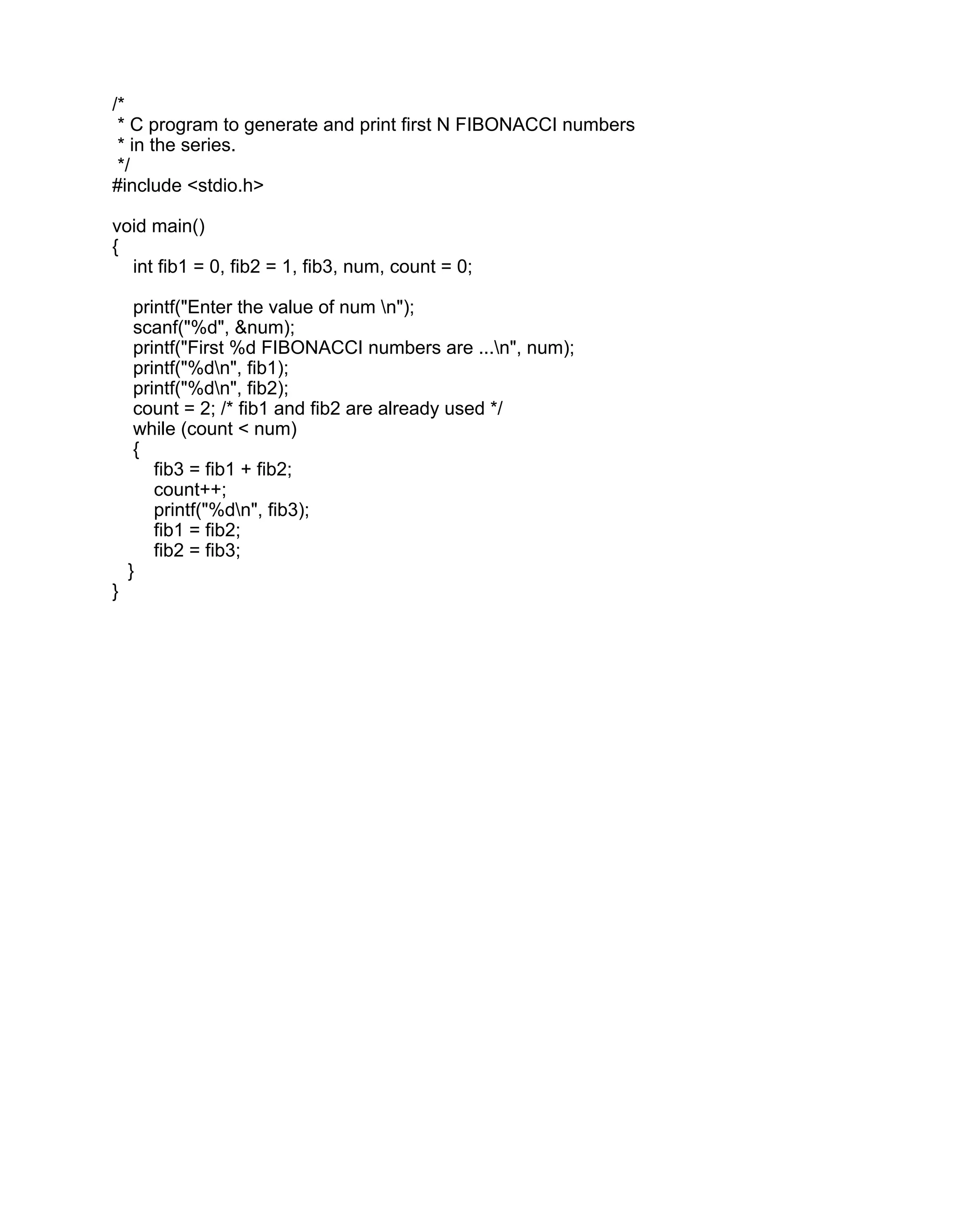
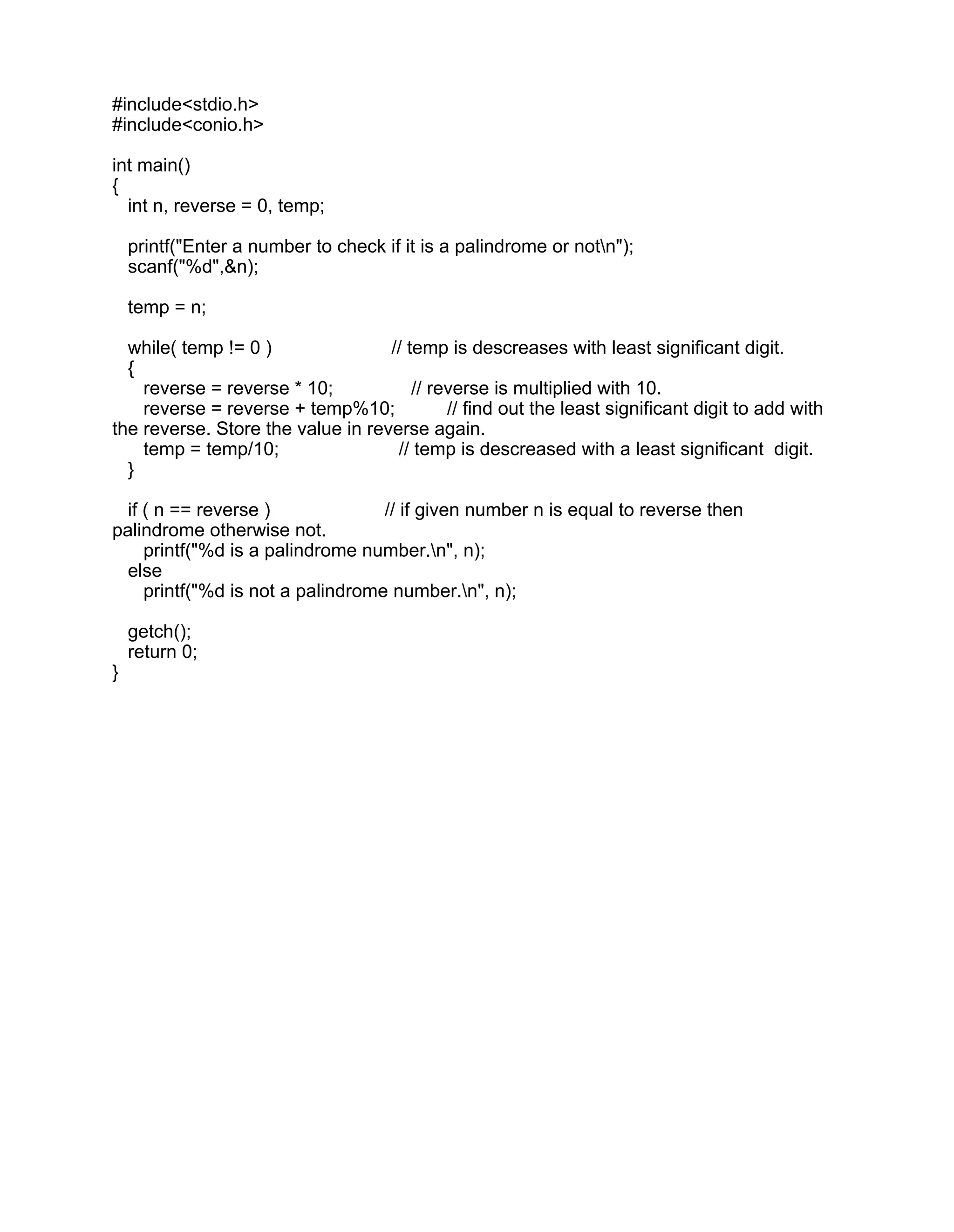
![#include<stdio.h>
main( )
{
int avg, sum = 0 ;
int i ;
int marks[30] ; /* array declaration */
for ( i = 0 ; i <= 29 ; i++)
{
printf ( "nEnter marks " ) ;
scanf ( "%d", &marks[i] ) ; /* store data in array */
}
for ( i = 0 ; i <= 29 ; i++ )
sum = sum + marks[i] ; /* read data from an array*/
avg = sum / 30 ;
printf ( "nAverage marks = %d", avg ) ;
}](https://image.slidesharecdn.com/assignment1and2-210330153246/75/C-Programming-Assignment-1-and-2-11-2048.jpg)
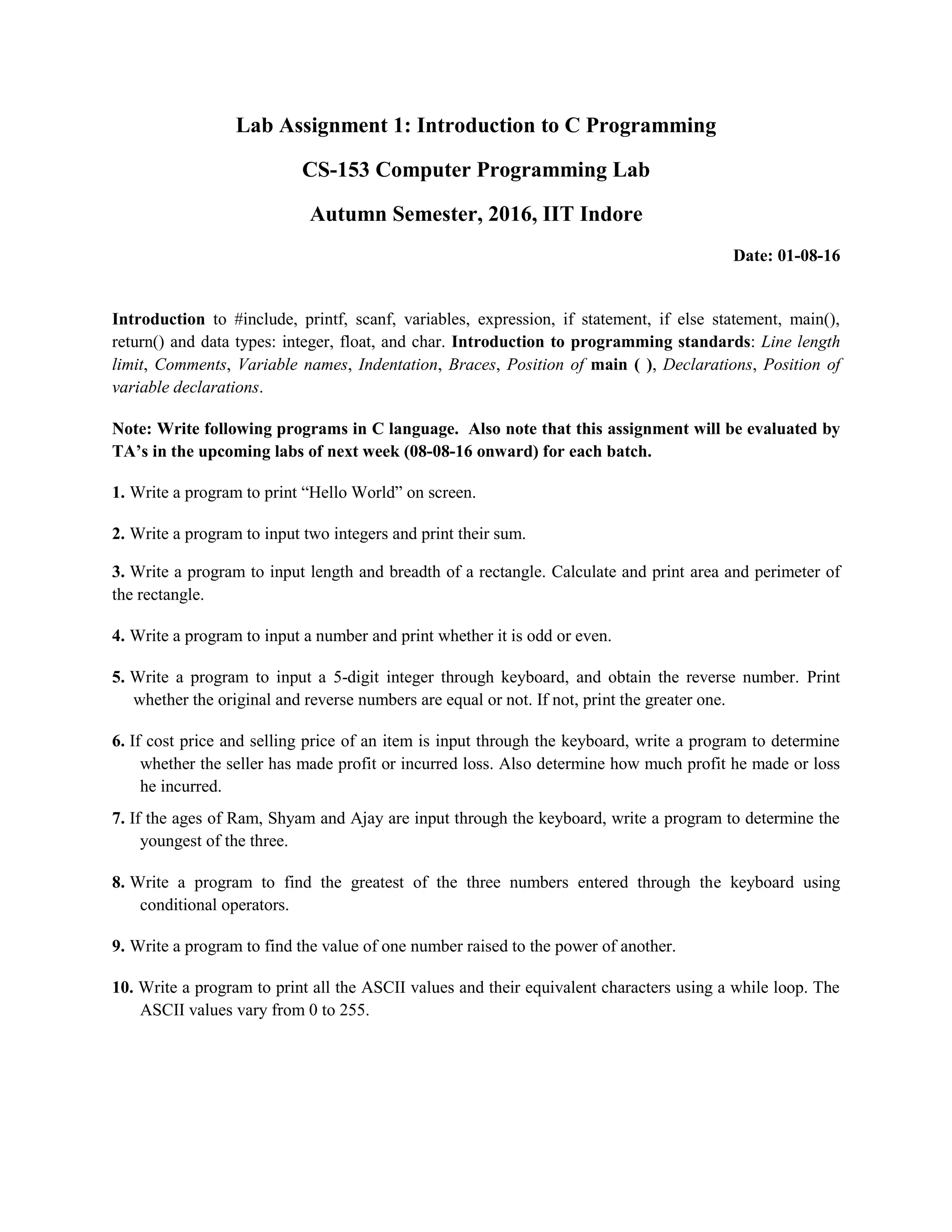
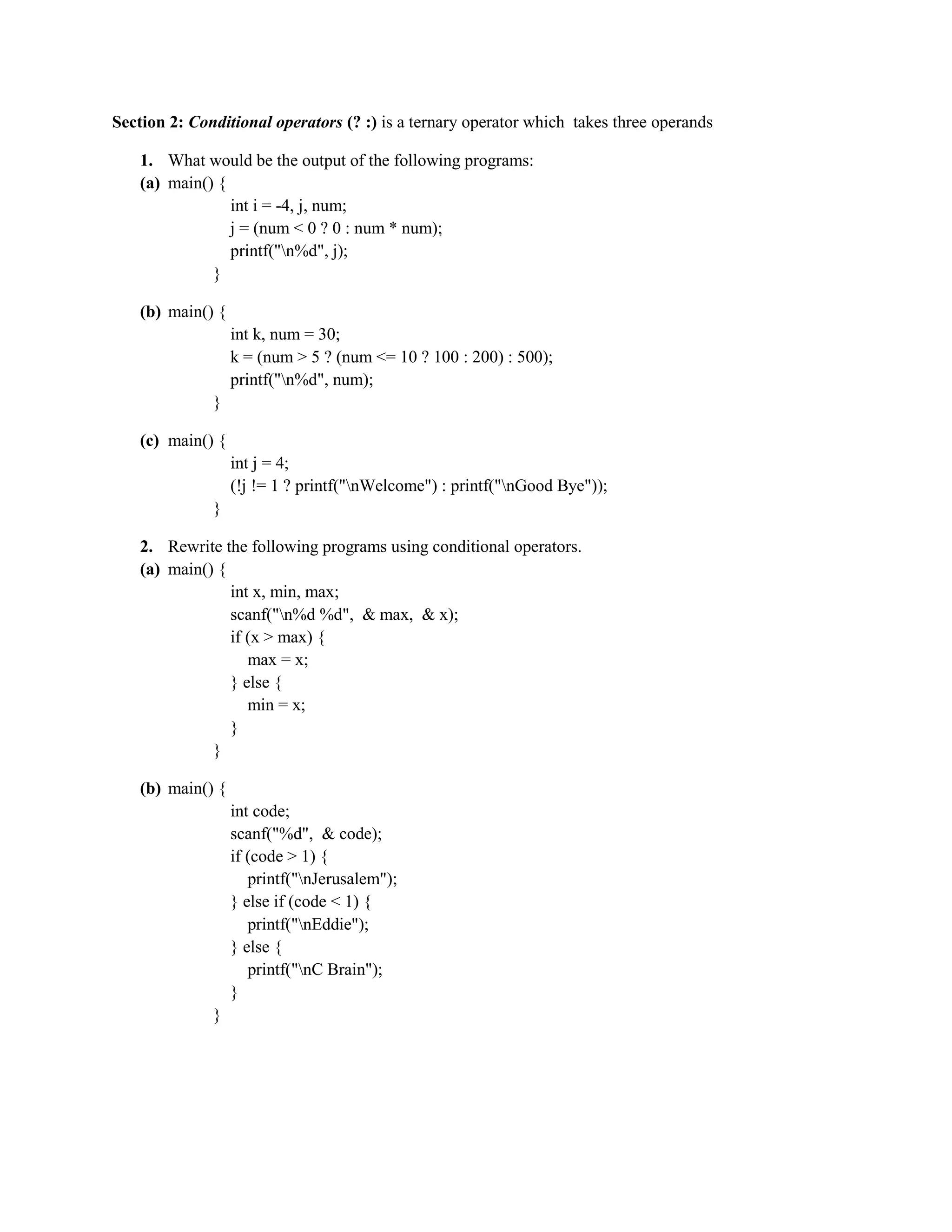
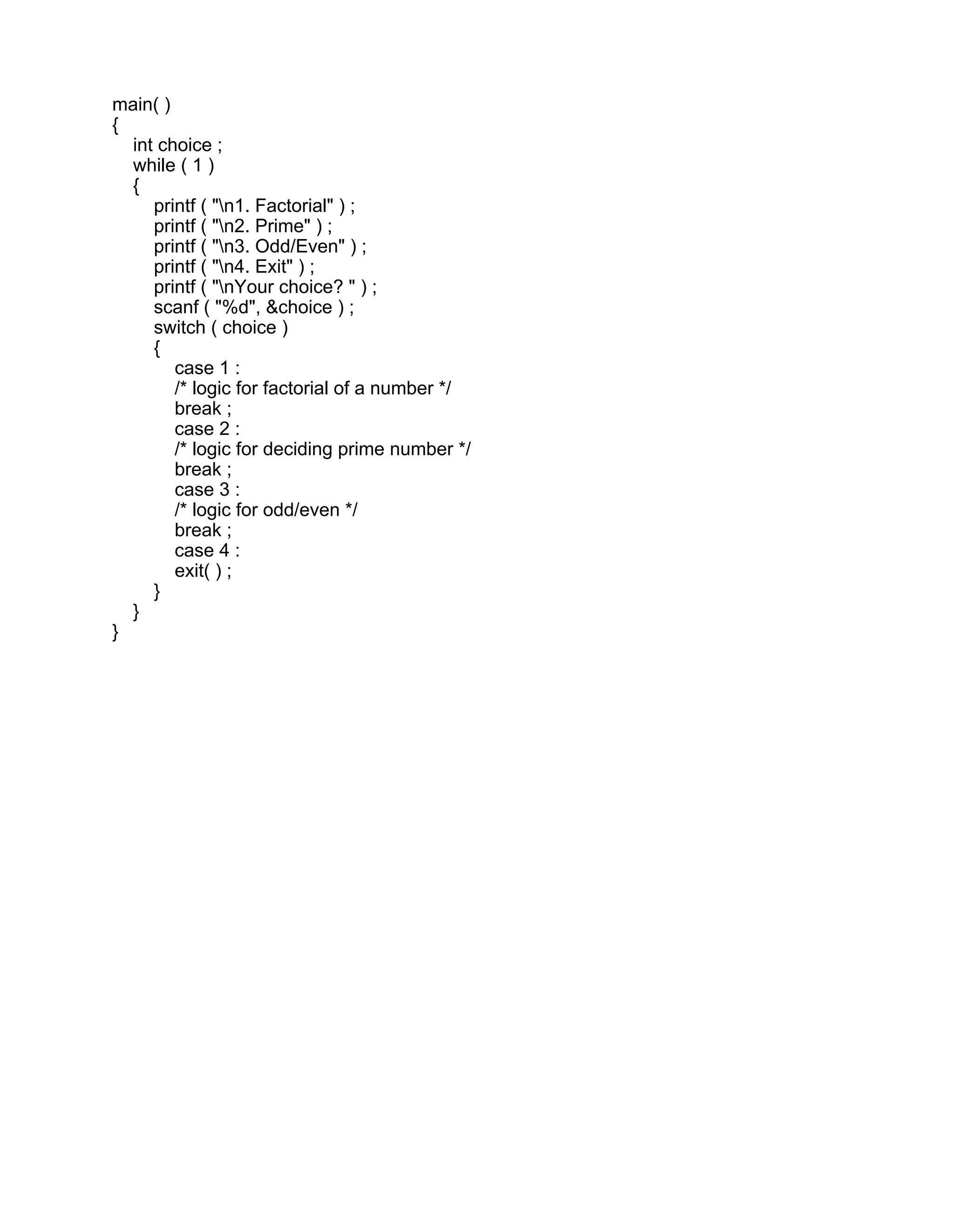
![#include<stdio.h>
int main()
{
int array[];
int i, N, v, frequency=0;
printf("Enter the size of the arrayn");
scanf("%d",&N);
printf("Enter %d numbersn", N);
for(i=0;i<N;i++)
{
scanf("%d",&array[i]);
}
printf("Enter the value for which frequency is to be computedn");
scanf("%d", &v);
for(i=0; i<N; i++)
{
if(array[i]==v)
{
frequency++;
}
}
printf("The frequency is %d", frequency);
}](https://image.slidesharecdn.com/assignment1and2-210330153246/75/C-Programming-Assignment-1-and-2-12-2048.jpg)