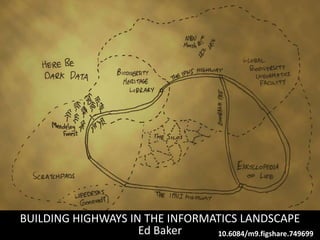
Building highways in the informatics landscape
•Download as PPTX, PDF•
1 like•1,498 views
The document discusses the need for a common data standard, called a "lingua franca", to allow different informatics systems to communicate as their data models, programming languages, and formats are currently incompatible. It proposes using the Darwin Core standard, which defines data terms and file formats for sharing biodiversity data in a way that is easily understood by both people and machines. The benefits are that any system can read and write Darwin Core formatted data, allowing data to be more easily aggregated, searched, and shared across a growing number of users and datasets.
Report
Share
Report
Share
Recommended
Multi View Constructed Right

Developers have been facing increasingly stronger requirements
regarding application interfaces. Current UIs have to support
different resolutions, match different devices and be
themeable. Besides that, the technology used is ever-changing thus
trying to keep such applications with a fresh look may require a lot
of rework.
Many theories have been proposed for this problem but the actual
solutions not always work due to failures in real world
implementations.
The story of a Wikipedia page

In October 2008 I started a page on Wikipedia. This is what happened next.
New tools for monitoring biodiversity and environments

How do we do science when the computer of 15 years ago now fits in your pocket and costs less than the battery you need to run it? Should biodiversity scientists work with the hacker and maker community? Should we forge links with engineering departments? Should hardware become a standard tool of the biodiversity informatician?
What will a digitial Natural History Museum look like in 10 years time?

With more than a little nod to Michael Edson
Recommended
Multi View Constructed Right

Developers have been facing increasingly stronger requirements
regarding application interfaces. Current UIs have to support
different resolutions, match different devices and be
themeable. Besides that, the technology used is ever-changing thus
trying to keep such applications with a fresh look may require a lot
of rework.
Many theories have been proposed for this problem but the actual
solutions not always work due to failures in real world
implementations.
The story of a Wikipedia page

In October 2008 I started a page on Wikipedia. This is what happened next.
New tools for monitoring biodiversity and environments

How do we do science when the computer of 15 years ago now fits in your pocket and costs less than the battery you need to run it? Should biodiversity scientists work with the hacker and maker community? Should we forge links with engineering departments? Should hardware become a standard tool of the biodiversity informatician?
What will a digitial Natural History Museum look like in 10 years time?

With more than a little nod to Michael Edson
Difference between .net core and .net framework

We are all familiar with .NET Core, .NET Framework and how they have been leading the programming world for building mobile, web-based and desktop applications. But wait, are they both same or have different infrastructure? You might be confused about both of them and probably that’s why you’re here.
Overview of ESB at Azilen Tech Meetup

An ESB (Enterprise Service Bus) technology meetup was organized by Azilen on 25th June 2016, Saturday at Ahmedabad Management Association.
IT09 L24: MANAGEMENT INFORMATION SYSTEMS- Module 2

Management Information System - The Managers view
Robert Schultheis
Mary Sumner
Kerscher, Gunderson, and Wise "Unprecedented Access: Improving the User Expe...

Kerscher, Gunderson, and Wise "Unprecedented Access: Improving the User Expe...National Information Standards Organization (NISO)
This presentation was provided by George Kershcer of The DAISY Consortium, Jon R. Gunderson of The University of Illinois at Urbana-Champaign, and Alicia Wise of Elsevier, during the NISO Webinar "Unprecedented Access: Improving the User Experience for People with Print Disabilities" which was held on December 8, 2010.No more BITS - Blind Insignificant Technologies ands Systems by Roger Roberts...

No more BITS - Blind Insignificant Technologies ands Systems by Roger Roberts of RTBF TITAN
Primer encuentro BIG MEDIA
Conectando Media, Audiencia y Publicidad con Datos
24 de junio 2014, Madrid
• Sponsor Platinum : Perfect Memory
• Sponsor Gold : Stratio, Paradigma
• Con el apoyo de : Big Data Spain, Medios On
• Socio tecnológico : Agora News
• Organizadores : Actuonda y Cátedra Big Data UAM-IBM
• Contacto : Nicolas Moulard (Actuonda) moulard@actuonda.com @Radio_20
www.bigmediaconnect.es
Introduction to oop with c++

mandatory basic knowledge of object oriented programming before you start
Open Data and Standard APIs

Open Data and Standard APIs learning material for iCOINS: Industry 4.0 competences for SMEs - Awareness raising tools - project. The iCOINS project aimed at developing common EU competences for raising awareness of SMEs on Industry 4.0 through an innovative Training Course. The primary target groups are VET teachers, trainers and mentors. Additionally, iCOINS serves the needs of SMEs staff, higher education staff and students, vocational institutions, vocational higher education institutions/teachers, public administration staff.
Cloud Computing & Distributed Computing

Cloud Computing & Distributed ComputingAmity University | FMS - DU | IMT | Stratford University | KKMI International Institute | AIMA | DTU
Cloud computing is used to define a new class of computing that is based on the network technology. Cloud computing takes place over the internet. It comprises of a collection of integrated and networked hardware, software and internet infrastructures. These infrastructures are used to provide various services to the users. Distributed computing comprises of multiple software components that belong to multiple computers. The system works or runs as a single system. Cloud computing can be referred to as a form that originated from distributed computing and virtualization.Data Sharing in Ecoacoustics

What are the challenges and opportunities for data sharing in bioacoustics? Lorentz Workshop, Leiden.
Ecoacoustic Challenges: UKAN Soundscapes Workshop

Challenges facing the eco acoustics community. Presentation for the UK Acoustics Network workshop on Soundscapes.
More Related Content
Similar to Building highways in the informatics landscape
Difference between .net core and .net framework

We are all familiar with .NET Core, .NET Framework and how they have been leading the programming world for building mobile, web-based and desktop applications. But wait, are they both same or have different infrastructure? You might be confused about both of them and probably that’s why you’re here.
Overview of ESB at Azilen Tech Meetup

An ESB (Enterprise Service Bus) technology meetup was organized by Azilen on 25th June 2016, Saturday at Ahmedabad Management Association.
IT09 L24: MANAGEMENT INFORMATION SYSTEMS- Module 2

Management Information System - The Managers view
Robert Schultheis
Mary Sumner
Kerscher, Gunderson, and Wise "Unprecedented Access: Improving the User Expe...

Kerscher, Gunderson, and Wise "Unprecedented Access: Improving the User Expe...National Information Standards Organization (NISO)
This presentation was provided by George Kershcer of The DAISY Consortium, Jon R. Gunderson of The University of Illinois at Urbana-Champaign, and Alicia Wise of Elsevier, during the NISO Webinar "Unprecedented Access: Improving the User Experience for People with Print Disabilities" which was held on December 8, 2010.No more BITS - Blind Insignificant Technologies ands Systems by Roger Roberts...

No more BITS - Blind Insignificant Technologies ands Systems by Roger Roberts of RTBF TITAN
Primer encuentro BIG MEDIA
Conectando Media, Audiencia y Publicidad con Datos
24 de junio 2014, Madrid
• Sponsor Platinum : Perfect Memory
• Sponsor Gold : Stratio, Paradigma
• Con el apoyo de : Big Data Spain, Medios On
• Socio tecnológico : Agora News
• Organizadores : Actuonda y Cátedra Big Data UAM-IBM
• Contacto : Nicolas Moulard (Actuonda) moulard@actuonda.com @Radio_20
www.bigmediaconnect.es
Introduction to oop with c++

mandatory basic knowledge of object oriented programming before you start
Open Data and Standard APIs

Open Data and Standard APIs learning material for iCOINS: Industry 4.0 competences for SMEs - Awareness raising tools - project. The iCOINS project aimed at developing common EU competences for raising awareness of SMEs on Industry 4.0 through an innovative Training Course. The primary target groups are VET teachers, trainers and mentors. Additionally, iCOINS serves the needs of SMEs staff, higher education staff and students, vocational institutions, vocational higher education institutions/teachers, public administration staff.
Cloud Computing & Distributed Computing

Cloud Computing & Distributed ComputingAmity University | FMS - DU | IMT | Stratford University | KKMI International Institute | AIMA | DTU
Cloud computing is used to define a new class of computing that is based on the network technology. Cloud computing takes place over the internet. It comprises of a collection of integrated and networked hardware, software and internet infrastructures. These infrastructures are used to provide various services to the users. Distributed computing comprises of multiple software components that belong to multiple computers. The system works or runs as a single system. Cloud computing can be referred to as a form that originated from distributed computing and virtualization.Similar to Building highways in the informatics landscape (20)
IT09 L24: MANAGEMENT INFORMATION SYSTEMS- Module 2

IT09 L24: MANAGEMENT INFORMATION SYSTEMS- Module 2
Kerscher, Gunderson, and Wise "Unprecedented Access: Improving the User Expe...

Kerscher, Gunderson, and Wise "Unprecedented Access: Improving the User Expe...
No more BITS - Blind Insignificant Technologies ands Systems by Roger Roberts...

No more BITS - Blind Insignificant Technologies ands Systems by Roger Roberts...
cloudcomputingdistributedcomputing-171208050503 (1).pdf

cloudcomputingdistributedcomputing-171208050503 (1).pdf
More from Edward Baker
Data Sharing in Ecoacoustics

What are the challenges and opportunities for data sharing in bioacoustics? Lorentz Workshop, Leiden.
Ecoacoustic Challenges: UKAN Soundscapes Workshop

Challenges facing the eco acoustics community. Presentation for the UK Acoustics Network workshop on Soundscapes.
Towards automated monitoring of Orthoptera (and some other noisy stuff)

Talk for the Orthopterists' Society 2016 meeting.
NHM Data Portal: first steps toward the Graph-of-Life

Talk from the SPNHC meeting in Berlin, June 2016
BioAcoustica: an online repository and analysis platform for wildlife sound

What is BioAcoustica? Why did we develop it? Where is it going?
Phasmids as Pests of Agriculture and Forestry

Introductory presentation on stick insects (Insecta: Phasmida) as pests of agriculture and forestry, with examples from the USA, Australia, Fiji and China.
Cite as:
Baker, Edward (2015): Phasmids as Pests of Agriculture and Forestry. figshare.
http://dx.doi.org/10.6084/m9.figshare.1472902
NHM MSc: Automated Acoustic Identification

Slides for NHM MSc course on automated acoustic identification of insects.
Measuring Impact: Towards a data citation metric

How the ViBRANT and eMonocot projects are building tools, including a modified implementation of Bourne and Fink's 'Scholar Factor', the Biodiversity Data Journal, and Scratchpad's user metrics and statistics modules.
Scratchpads & Citizen Science

Video available here: http://www.youtube.com/watch?v=2Og11_Au_to&list=PLYBO7pOvStFwlxpzXXgc959TiKHwsLIvo&index=8
Scratchpads Training Course

Scratchpads training course at the Natural History Museum, London on 16th October 2012
More from Edward Baker (20)
Towards automated monitoring of Orthoptera (and some other noisy stuff)

Towards automated monitoring of Orthoptera (and some other noisy stuff)
NHM Data Portal: first steps toward the Graph-of-Life

NHM Data Portal: first steps toward the Graph-of-Life
BioAcoustica: an online repository and analysis platform for wildlife sound

BioAcoustica: an online repository and analysis platform for wildlife sound
Phasmid Study Group: Name changes talk (Summer Meeting 2014)

Phasmid Study Group: Name changes talk (Summer Meeting 2014)
Biodiversity Informatics of the Cyperaceae: Where we stand and where we’re he...

Biodiversity Informatics of the Cyperaceae: Where we stand and where we’re he...
Biodiversity Informatics at the Natural History Museum

Biodiversity Informatics at the Natural History Museum
Nature Live!: Cockroaches from the beginning (May 2012)

Nature Live!: Cockroaches from the beginning (May 2012)
Swiss Orchid Foundation Scratchpads and ViBRANT overview

Swiss Orchid Foundation Scratchpads and ViBRANT overview
Connecting the dots: Natural Science Collections and the Web

Connecting the dots: Natural Science Collections and the Web
Recently uploaded
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on the notifications, alerts, and approval requests using Slack for Bonterra Impact Management. The solutions covered in this webinar can also be deployed for Microsoft Teams.
Interested in deploying notification automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Recently uploaded (20)
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
Building highways in the informatics landscape
- 1. BUILDING HIGHWAYS IN THE INFORMATICS LANDSCAPE Ed Baker 10.6084/m9.figshare.749699
- 2. We need to move from this…
- 3. …to this
- 4. HOW?
- 5. All of these systems: • Have different data models • Are written in different programming languages • Are mutually incompatible
- 6. How do we make these systems talk? Requirements
- 7. How do we make these systems talk? Requirements Each pair can define a way of communicating with each other
- 8. How do we make these systems talk? Requirements
- 9. How do we make these systems talk? Requirements
- 10. We need a lingua franca of biodiversity informatics Requirements
- 11. We need a lingua franca of biodiversity informatics Requirements Any language that is widely used as a means of communication among speakers of other languages.
- 13. Easily understood • People • Machines Easy to share • Using existing technology and infrastructure Requirements
- 14. Easily understood • People • Machines Easy to share • Using existing technology and infrastructure Can read in Excel Requirements
- 15. Easily understood • People • Machines Easy to share • Using existing technology and infrastructure Can read in Excel Everything precisely defined Requirements
- 16. Easily understood • People • Machines Easy to share • Using existing technology and infrastructure Can read in Excel Everything precisely defined Standard formats: csv, zip Standard delivery: via the web Requirements
- 22. Core File (classificati on) Images Literature Specimens Taxonomic treatments Meta.xml What is each file? What does each column in a file contain?
- 25. dwca.zip
- 26. dwca.zip
- 27. dwca.zip
- 29. dwca.zipdwca.zip dwca.zip dwca.zip dwca.zip dwca.zip
- 30. dwca.zipdwca.zip dwca.zip dwca.zip dwca.zip dwca.zip
- 31. dwca.zipdwca.zip dwca.zip dwca.zip dwca.zip dwca.zip ?
- 32. These images came from the Scratchpad
- 33. These images came from the Scratchpad So did this description
- 35. This map didn’t
- 36. Aggregators allow us to… • provide a single user interface to many different systems. • search easily across multiple datasets simultaneously (and combine results).
- 37. You can also share data with …
- 38. You can also share data with … ANY OF THE INCREASING NUMBER OF PEOPLE WHO SUPPORT THE STANDARD
