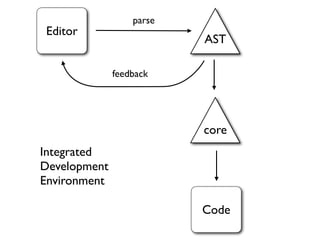
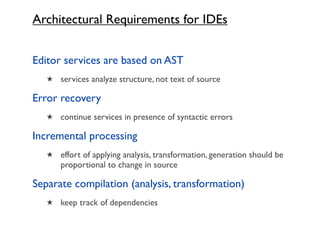
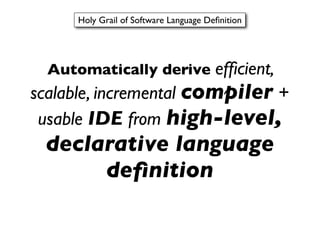
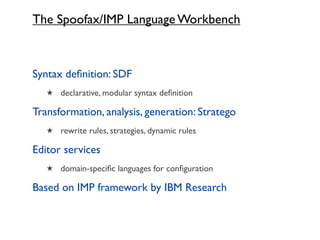
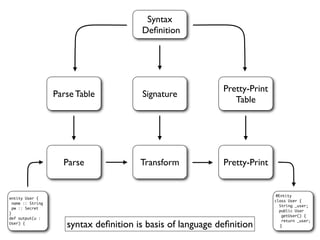
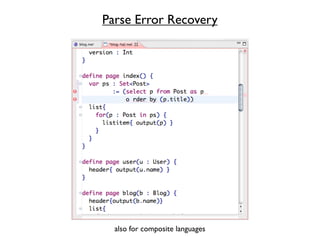
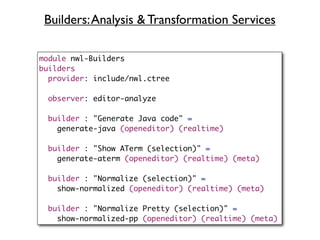
This document discusses the Spoofax language workbench, which is a tool for building domain-specific languages (DSLs). It addresses key concerns in developing DSLs such as the tradeoffs between internal and external DSLs, textual vs graphical syntax, code generation vs interpretation, and static vs dynamic typing. The Spoofax workbench uses declarative syntax definitions and rewrite rules to provide features like syntax checking, error recovery, and incremental processing for integrated development environments.



![Full Text Search
define page search() {
var query : String
action show() {
var pubs : List<Publication> := searchPublication(query);
if(pubs.length > 0) {
replace(results, results(query,pubs));
} else {
replace(results, noresults()); entity Publication {
title :: String (name,searchable)
}
journal :: String (searchable)
} year :: Int (searchable)
main{ month :: String (searchable)
section{ ...
}
header{"Search"}
form{ input(query)[onkeyup:=show()] }
placeholder results{}
}
}
}](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-14-320.jpg)
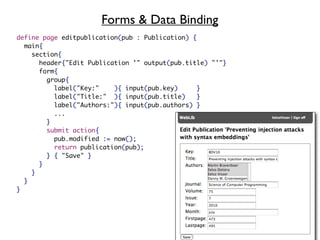
![Access Control Rules
define showReview(review : Review) {
action delete() { ... }
section{ ...
navigate(editReview(review)){"[Edit]"}
submitlink delete() {"[X]"}
}
}](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-21-320.jpg)
![Access Control Rules
define showReview(review : Review) {
action delete() { ... }
section{ ...
navigate(editReview(review)){"[Edit]"}
submitlink delete() {"[X]"}
}
}
access control rules
principal is User with credentials username, password
predicate isReviewer(review : Review) {
review.reviewer == securityContext.principal
}
rule template showReview(review : Review, pubLink : Bool) {
review.public || isReviewer(review)
rule action delete() {
loggedIn() && isReviewer(review)
}
}
rule page editReview(review : Review) {
loggedIn() && isReviewer(review)
}](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-22-320.jpg)

![Data Validation: Form Input Validation
label("Acronym (without year)"){
input(acronym){
validate(!isEmptyString(acronym),
"Provide acronym")
validate(!(/[ ]/.find(acronym)),
"Acronym should not contain spaces")
validate(!(/[0-9][0-9][0-9][0-9]/.find(acronym)),
"Acronym should not contain year")
}
}](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-24-320.jpg)


![Terms to Represent Abstract Syntax
Entity(“Blog”,
[Property(“name”,SimpleType(“String”)),
Property(“author”, SimpleType(“User”))]
)](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-52-320.jpg)

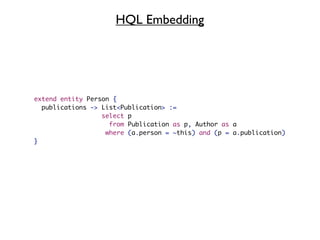
![Embedding HQL
module expressions
imports Common
imports HQL
exports
context-free syntax
SelectStatement -> Exp
define page index() {
list{
for(p : Post in select p from Post as p order by (p.title)) {
listitem{ output(p) }
}
}
}
ForElem("p", SimpleType("Post")
, QueryRule(
SelectFrom(
Some(Select(None(), [AliasedExpression(Path(["p"]), None())]))
, FromClause([FromRangeJoin(FromClass(Path(["Post"]), Some(AsAlias(Alias("p"
)
, Some(OrderByClause([OrderElement(Paren([Path(["p", "title"])]), None())]))
)
, [CallElems("listitem", [CallArgs("output", [Var("p")])])]
)](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-65-320.jpg)

![Syntax Properties
module nwl-Syntax.generated
language Syntax properties (static defaults)
// Comment constructs:
line comment : "//"
block comment : "/*" * "*/"
// Fences (used for matching,
// inserting, indenting brackets):
fences : [ ]
( )
{ }
// Automatic indent hints
// (indent after these tokens):
indent after : "="
":"
// Regular expression for identifiers:
identifier lexical : "[A-Za-z0-9_]+"](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-74-320.jpg)
![Term Rewrite Rule
left-hand side pattern
label/name
desugar :
Property(x, t) -> Property(x, t, [])
variable
right-hand side pattern](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-81-320.jpg)
![Rewriting with Concrete Object Syntax
elem-to-java-servlet :
tc@elem|[ x(e)[passign*]{elem*} ]| ->
<wrap-input-render-java-code>
bstm* |[
String x_temp = ident+"~inputident"+uniqueid;
~*<render-error-messages-with-error-template(|java:expr|[ x_temp ]|,
<ErrorTemplateInput>)> bstm*|[
bstm_call*
]|
]|
where <is-input-template> tc
with inputident := <get-inputnumber> tc
; x_temp := <newname> "temp"
; bstm_call* := <control-flow-tcall-helper(|"render",expr|[ x_temp ]|)> tc
Stratego + embedded Java](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-87-320.jpg)
![Error Checking: Binary Operators
check :
e@BinOp(e1, op, e2) ->
(e, $[operator [op] not defined for [<pp>t1] and [<pp>t2]])
where t1 := <type-of> e1
where t2 := <type-of> e2
where require(<type-of> e)](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-97-320.jpg)
![Pretty-Printing with String Interpolation
pp : Entity(x, prop*) ->
$[entity [x] {
[<map(pp)>prop*]
}]
pp : Property(x,t) ->
$[[x] : [<pp>t]
]
pp : SimpleType(x) -> x
pp : SetType(t) -> $[Set<[<pp> t]>]
pp : [] -> $[]
pp : [t] -> <pp>t
pp : [t1,t2|ts] -> $[[<pp>t1],[<pp>[t2|ts]]]](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-98-320.jpg)
![Type Analysis: Binary Operators
type-of :
BinOp(e1, op, e2) -> t
where t := <function-type>(op, [<type-of>e1, <type-of>e2])
function-type :
("+", [SimpleType("String"), SimpleType("String")]) -> SimpleType("String")
function-type :
("+", [SimpleType("Int"), SimpleType("Int")]) -> SimpleType("Int")
function-type :
("-", [SimpleType("Int"), SimpleType("Int")]) -> SimpleType("Int")](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-101-320.jpg)
![Variables: Check
check :
e@Var(x) -> (e, $[Variable '[x]' not declared])
where require(<type-of>e)](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-107-320.jpg)


![Rewrite Rules are Context-free
desugar :
Property(x, t) -> Property(x, t, [])](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-124-320.jpg)
![Rewrite in Context
Inline :
[def@TemplateDef(f,[],elem1*) | def1*] -> [def | def2*]
where def2* := <alltd((Call(f) -> Call("container", elem1*)))> def1*
local traversal bound in context
container needed to replace single call with multiple elements](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-126-320.jpg)
![Rewrite in Context
Inline :
[def@TemplateDef(f,[],elem1*) | def1*] -> [def | def2*]
where def2* := <alltd((Call(f) -> Call("container", elem1*)))> def1*
bound in context](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-133-320.jpg)
![Inline :
[def@TemplateDef(f,[],elem*) | def1*] -> [def | def2*]
where def2* := <alltd((Call(f) -> Call("container", elem*)))> def1*
f elem*
[ TemplateDef(
"footer"
, []
, [Navigate(PageRef("webdsl", []), [String("WebDSL")])]
)
, TemplateDef(
"blog"
, [Param("b", SimpleType("Blog"))]
, [Call("footer")]
)
]
Call(f)
def1*](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-134-320.jpg)
![Rules with Parameters
Transform all elements of a list
map(s) : [] -> []
map(s) : [x|xs] -> [<s>x | <map(s)> xs]
Invert order of elements of a list
inverse(|ys) : [] -> ys
inverse(|ys) : [x|xs] -> <inverse(|[x|ys])> xs
Pair elements of two lists
zip(s) : ([],[]) -> []
zip(s) : ([x|xs],[y|ys]) -> [<s>(x,y) | <zip(s)>(xs,ys)]](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-136-320.jpg)
![Rewrite in Context: Local Traversal
Inline :
[def@TemplateDef(f,[],elem1*) | def1*] -> [def | def2*]
where def2* := <alltd((Call(f) -> Call("container", elem1*)))> def1*
local traversal](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-139-320.jpg)
![Rewrite in Context: Not Optimal
Inline :
[def@TemplateDef(f,[],elem1*) | def1*] -> [def | def2*]
where def2* := <alltd((Call(f) -> Call("container", elem1*)))> def1*
requires def before use
local traversal for each declaration](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-141-320.jpg)
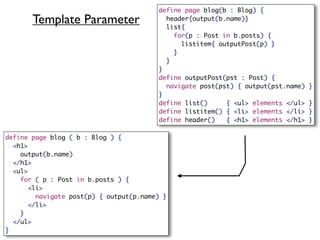
![Dynamic Rewrite Rules
Inline :
[def@TemplateDef(f,[],elem1*) | def1*] -> [def | def2*]
where def2* := <alltd((Call(f) -> Call("container", elem1*)))> def1*
declare-inline :
TemplateDef(f,[],elem1*) -> TemplateDef(f,[],elem1*)
where rules(
InlineTemplate : Call(f) -> Call("container", elem1*)
)
inline =
alltd(declare-inline);
topdown(try(InlineTemplate))
separate traversal from rule definition (binding closures)](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-142-320.jpg)
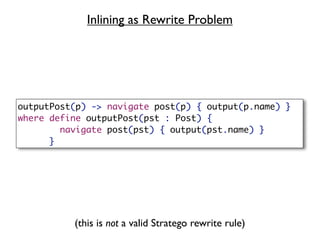
![Inlining as Rewrite Problem (Revisited)
outputPost(p) -> navigate post(p) { output(p.name) }
where define outputPost(pst : Post) {
navigate post(pst) { output(pst.name) }
}
(informal)
declare-inline :
TemplateDef(f,[],elem1*) -> TemplateDef(f,[],elem1*)
where rules(
InlineTemplate : Call(f) -> Call("container", elem1*)
)
(formal; but not yet complete)](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-143-320.jpg)
![Inlining Templates with Parameters
declare-inline :
def@TemplateDef(mod*,f,param*,elem1*) -> def
where rules(
InlineTemplate :
Call(f, e*, []) -> Call("container", [], elem3*)
where elem3* := <substitute> (param*, e*, elem1*)
)
substitute :
(param*, e*, elem1*) -> elem2*
where {| Subst
: <zip(bind-arg)> (param*, e*)
; elem2* := <alltd(Subst)> elem1*
|}
bind-arg :
(Param(x, t), e) -> (Param(x, t), e)
where rules( Subst : Var(x) -> e )](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-145-320.jpg)
![Element Parameters
define list() { <ul> elements </ul> }
declare-inline :
def@TemplateDef(mod*,f,param*,elem1*) -> def
where rules(
InlineTemplate :
Call(f, e*, elem2*) -> Call("container", [], elem3*)
where {| Subst
: rules(
Subst : Elements() -> Call("container",[],elem2*)
)
; elem3* := <substitute> (param*, e*, elem1*)
|}
)](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-146-320.jpg)
![Removing Intermediate Structures
rules // remove containers
desugar-container :
[Call("container",[], elem1*) | elem2*] -> [elem1*, elem2*]
desugar :
elem1* -> elem2*
where elem2* := <at-suffix(desugar-container)> elem1*
container needed to replace single call with multiple elements](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-147-320.jpg)
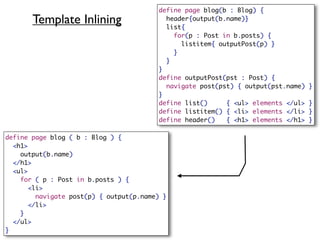
![module template-inlining
imports libstratego-lib
imports include/nwl
imports desugar
strategies
inline-all =
desugar-all;
alltd(declare-inline);
innermost(desugar <+ InlineTemplate)
rules
declare-inline :
TemplateDef(mod*,f,param*,elem1*) -> TemplateDef(mod*,f,param*,elem1*)
where rules(
InlineTemplate :
Call(f, e*, elem2*) -> Call("container", [], elem3*)
Template Inlining where {| Subst
: rules( Subst : Elements() -> Call("container", [], elem2*) )
; elem3* := <substitute> (param*, e*, elem1*)
Transformation )
|}
substitute :
(param*, e*, elem1*) -> elem2*
where {| Subst
: <zip(bind-arg)> (param*, e*)
; elem2* := <alltd(Subst)> elem1*
|}
bind-arg :
(Param(x, t), e) -> (Param(x, t), e)
where rules( Subst : Var(x) -> e )
rules // remove containers
desugar-container :
[Call("container",[], elem1*) | elem2*] -> [elem1*, elem2*]
desugar :
elem1* -> elem2*
where elem2* := <at-suffix(desugar-container)> elem1*](https://image.slidesharecdn.com/codegen10-100618054627-phpapp01/85/Building-DSLs-with-the-Spoofax-Language-Workbench-149-320.jpg)