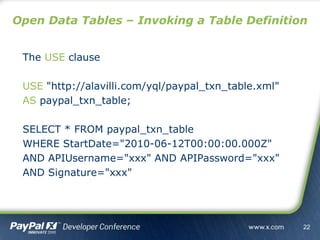
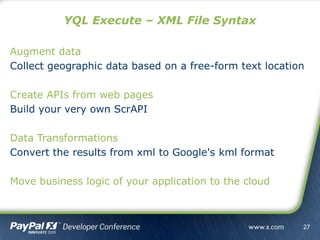
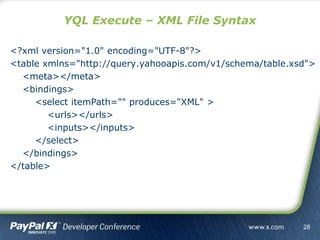
This document discusses Yahoo! Query Language (YQL) which allows users to query and manipulate data from various web services and online data sources. It covers how to structure YQL queries, available data tables, open data tables that allow users to expose their own APIs or data, and YQL Execute which allows running server-side JavaScript code. The goal of YQL is to help developers build adaptive applications by accessing online data through a simple SQL-like interface.





![http://query.yahooapis.com/v1/yql?[params]
http://query.yahooapis.com/v1/public/yql?[params]
Params
• q=[QUERY]
• format=[XML / JSON]
• diagnostics=[true / false]
• debug=[true / false]
• callback=[function name]
Running Queries – URL Format
13](https://image.slidesharecdn.com/yqloverview-101028105307-phpapp01/85/Building-Adaptive-Payment-Systems-with-YQL-13-320.jpg)
![http://query.yahooapis.com/v1/yql?[params]
http://query.yahooapis.com/v1/public/yql?[params]
Params
• q=[QUERY]
• format=[XML / JSON / JSONP / JSONP-X]
• diagnostics=[true / false]
• debug=[true / false]
• callback=[function name]
Running Queries – URL Format
14](https://image.slidesharecdn.com/yqloverview-101028105307-phpapp01/85/Building-Adaptive-Payment-Systems-with-YQL-14-320.jpg)




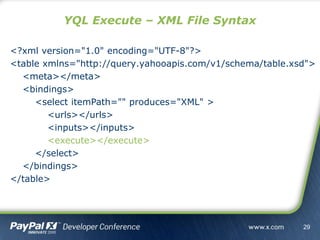
![<execute>
<![CDATA[
var arrQueries = inputs['query'].split('|');
var elQueries = <queries/>;
.
.
.
]]>
</execute>
YQL Execute – XML File Syntax
30](https://image.slidesharecdn.com/yqloverview-101028105307-phpapp01/85/Building-Adaptive-Payment-Systems-with-YQL-30-320.jpg)