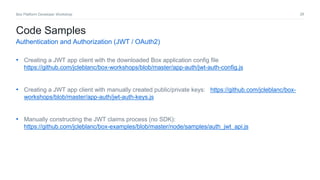
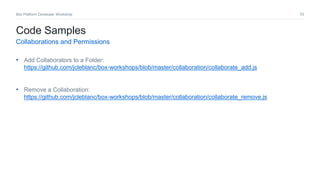
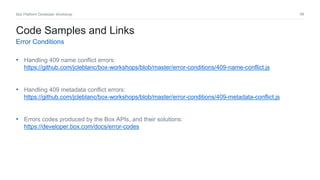
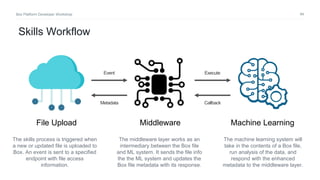
The document provides an overview of common user models, authentication types, and permission patterns for building applications on the Box platform. It discusses classic user models that separate external app users from internal managed users, as well as models where all users are app users or where a service account represents the application. The document also covers authentication using JWT or OAuth2, scopes for controlling application permissions, and best practices for user, collaboration, and error handling.