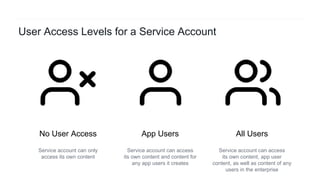
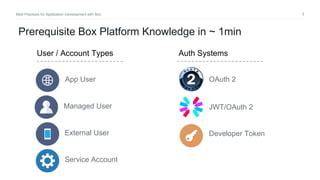
The document outlines best practices for application development with Box, focusing on key areas such as data integrity, token management, and access control. It highlights the importance of managing user and service account data securely while addressing common errors encountered during API interactions. Additionally, the document provides guidelines for handling token authentication, storing data, and navigating API error responses effectively.


![15Best Practices for Application Development with Box
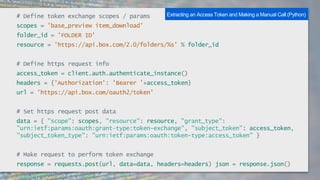
client.exchangeToken(appConfig.tokenScopes[service]).then((tokenInfo) => {
// token available in tokenInfo.accessToken
}).catch((err) => {
console.error(err);
});
Downscoping a Token (Node SDK)](https://image.slidesharecdn.com/best-practices-box-apps-v2-180829173330/85/Best-Practices-for-Application-Development-with-Box-15-320.jpg)