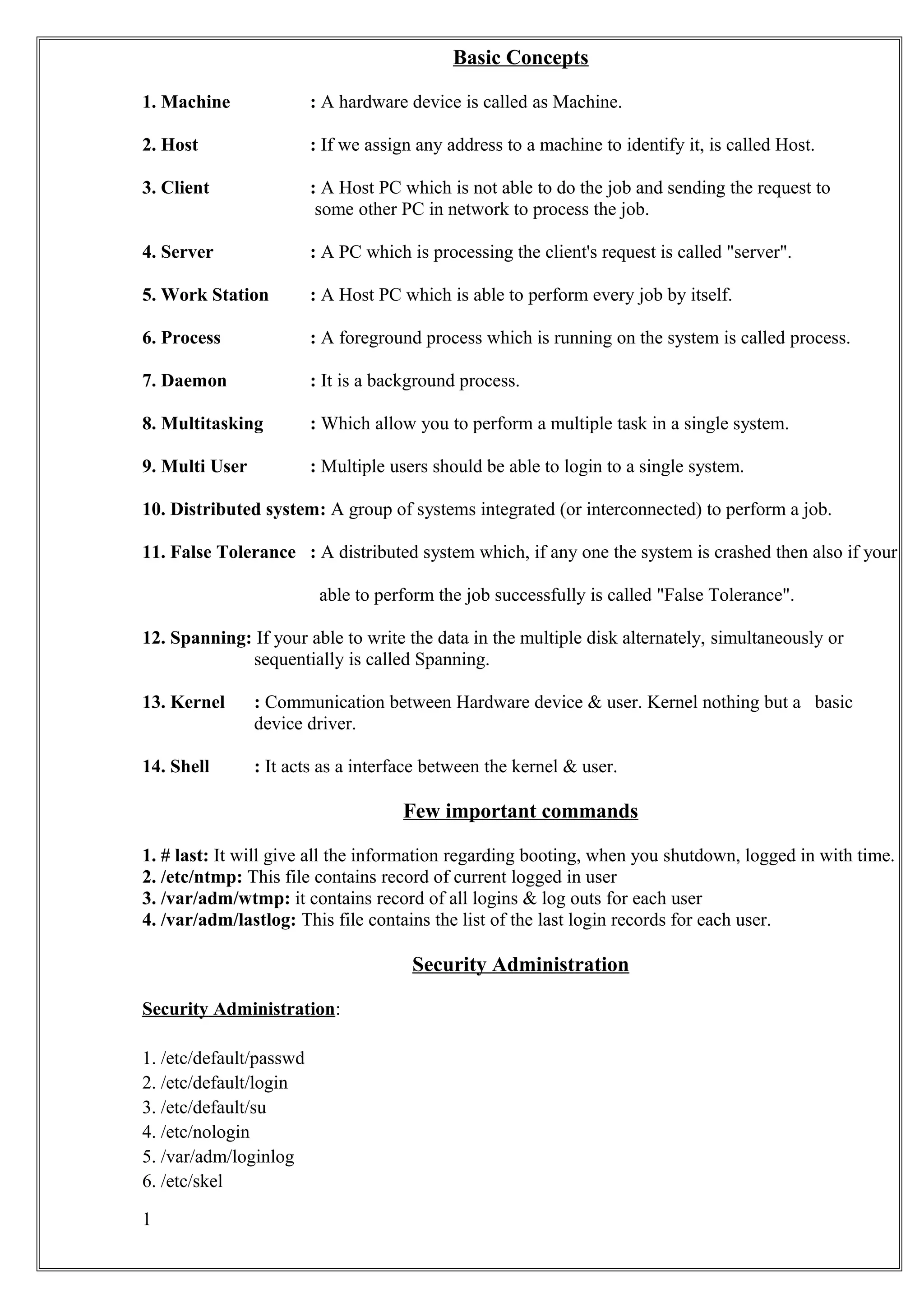
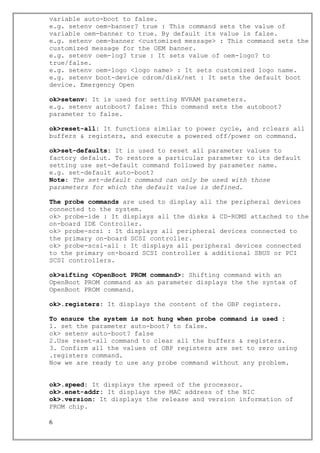
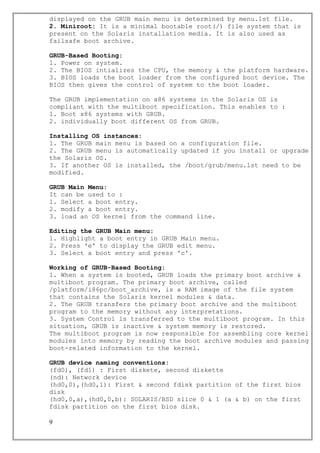
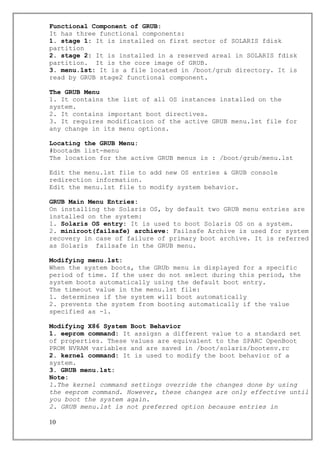
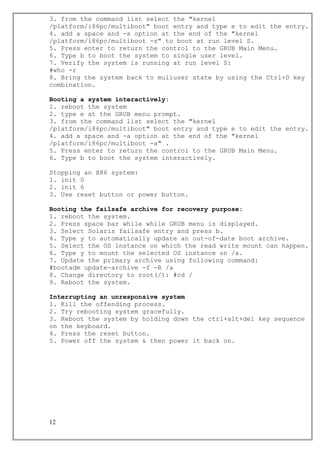
The document describes basic concepts related to machines, hosts, clients, servers, workstations, processes, daemons, distributed systems, and kernels. It then provides details about the boot PROM including its functions, components, configuration information storage, and commonly used commands. Finally, it outlines the boot PROM booting process and describes emergency sequences and diagnostic modes that can be accessed using stop key sequences.