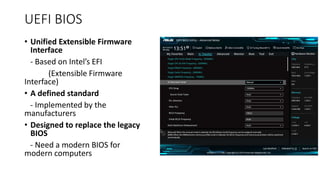
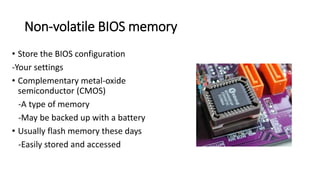
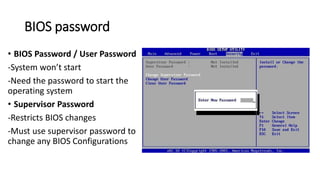
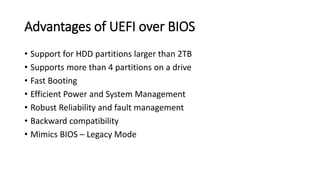
The document discusses BIOS and UEFI firmware. It explains that BIOS initializes the computer's hardware and allows booting an operating system, while UEFI is newer standard that supports larger drives and partitions. The document outlines some key advantages of UEFI like supporting drives over 2TB and allowing booting from non-hard drive media. It also discusses UEFI BIOS security features like encryption, theft protection, and secure boot verification of software.