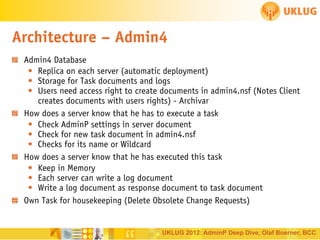
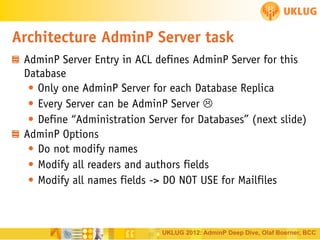
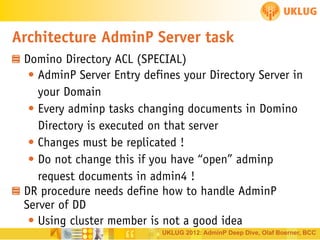
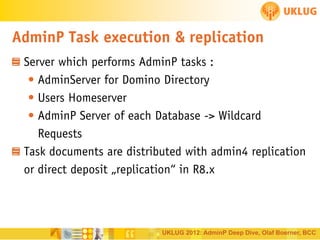
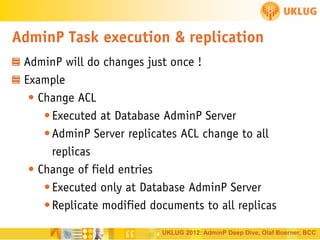
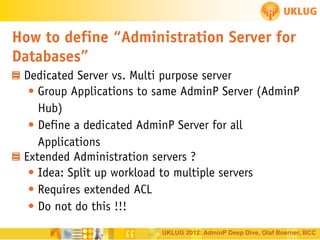
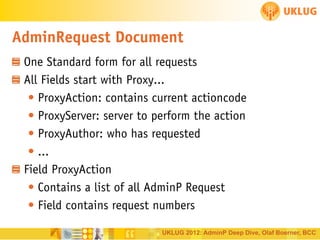
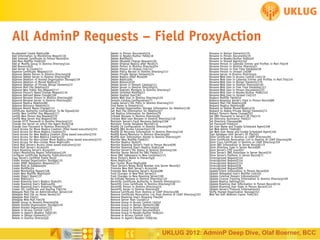
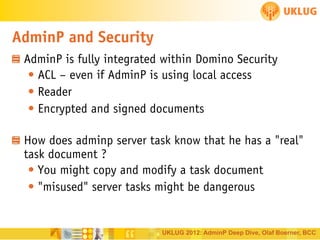
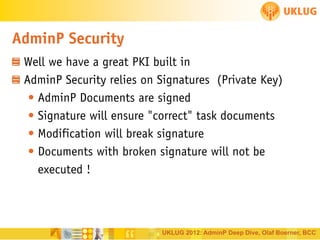
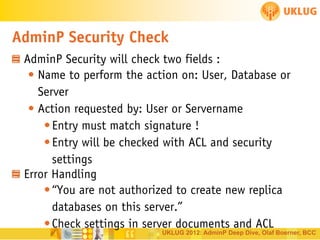
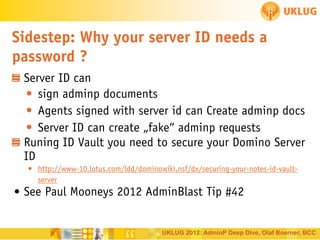
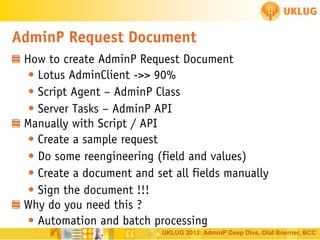
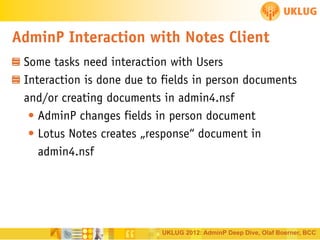
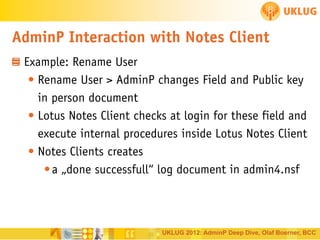
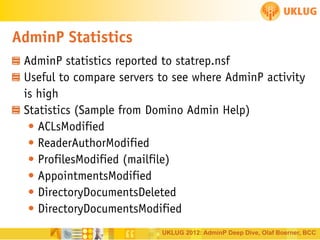
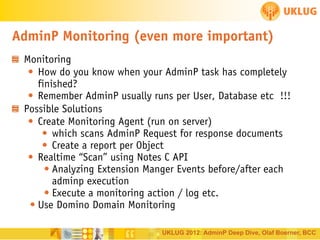
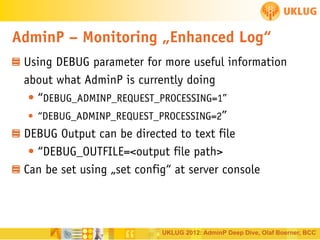
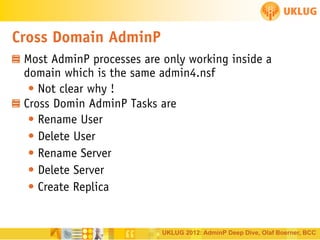
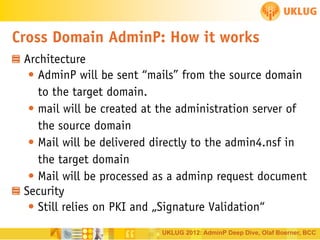
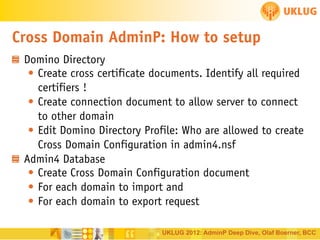
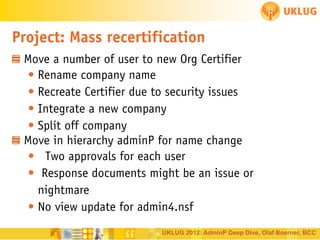
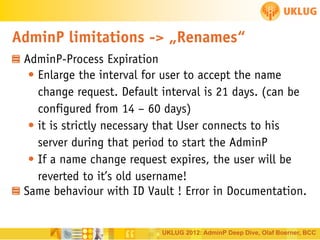
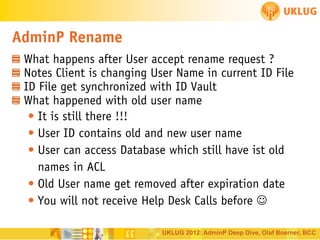
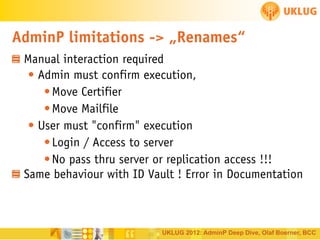
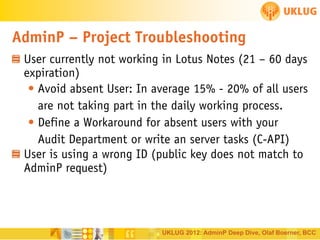
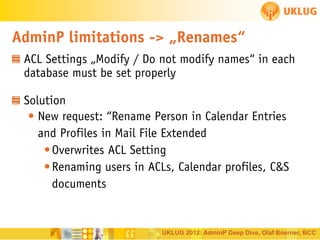
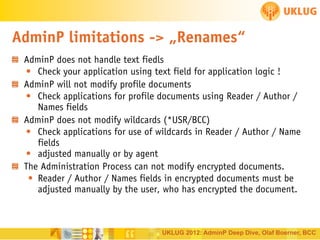
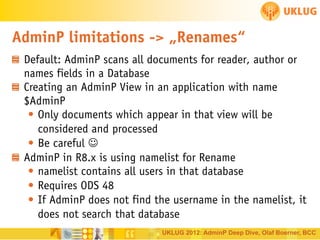
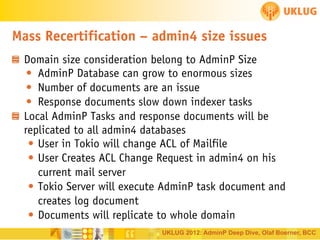
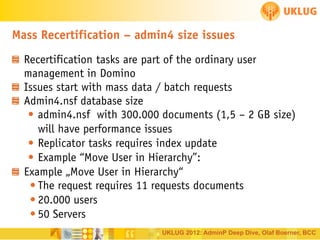
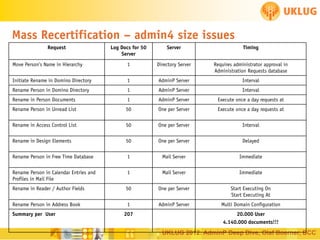
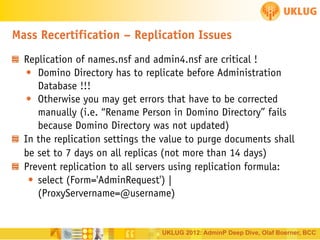
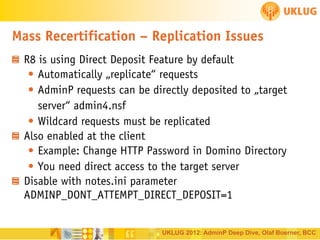
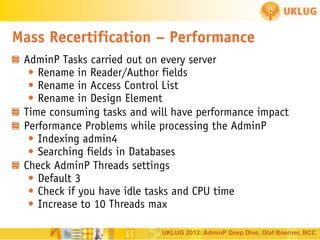
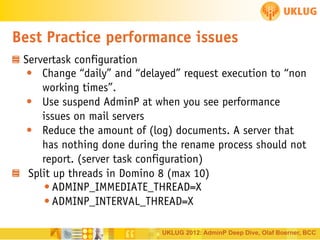
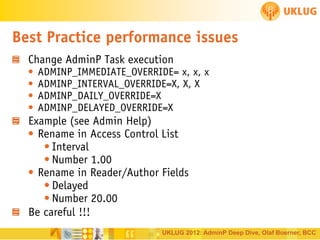
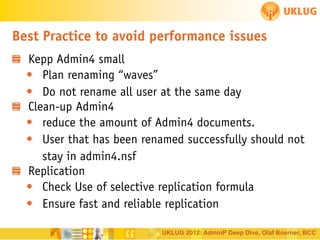
The document presents a detailed overview of the AdminP feature in Lotus Domino, introduced in version 4 for efficient server administration, inspired by client needs. It discusses the architecture of AdminP, including the Admin4 database functionality, task execution mechanisms, and security measures to ensure document integrity. Additionally, it highlights the importance of handling various administrative requests through a structured process that involves ACLs and client interactions.