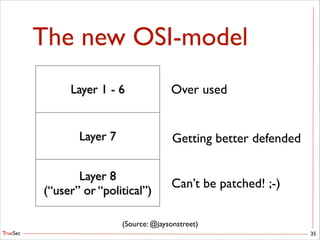
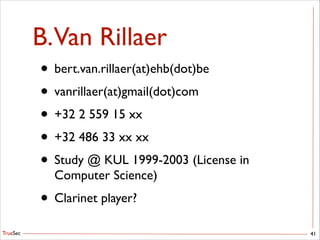
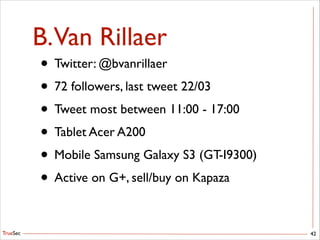
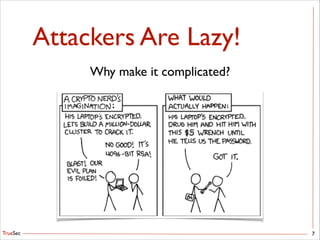
This document discusses social engineering and how humans can be manipulated to gain access to information. It provides historical examples of social engineering attacks and explains that social engineering works because people are kind, naive, trusting and scared. The document outlines the social engineering process of identifying a target, determining the objective, and creating a plan to manipulate the target into divulging information. It argues that in today's digital world, people leave extensive online footprints that can be used against them in social engineering attacks.
![TrueSec
$ man 3 human
• People aren’t stupid (…well, only some :-])
• But they are…
• Kind
• Naive
• Trustful
• Voluntary
• Scared
11](https://image.slidesharecdn.com/keynote-se-140404152453-phpapp02/85/Because-we-are-just-humans-11-320.jpg)