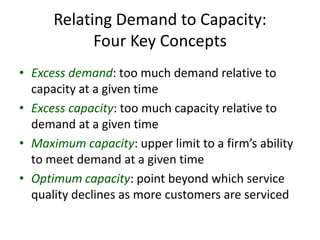
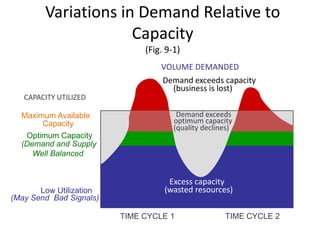
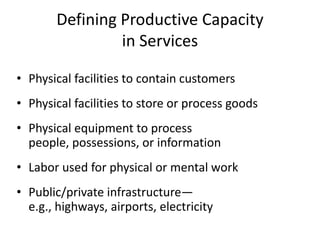
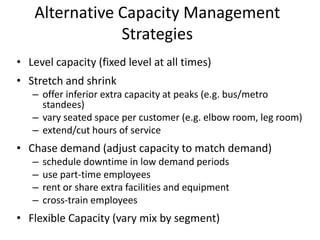
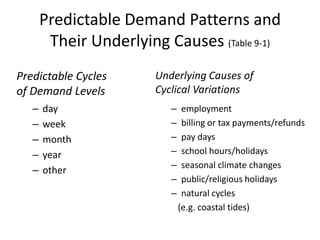
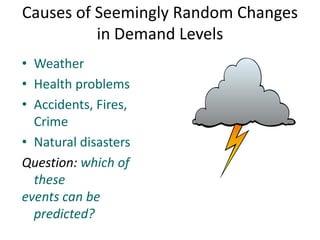
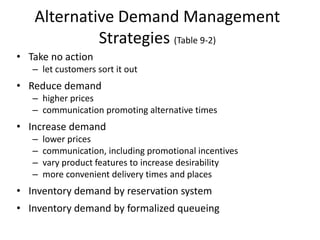
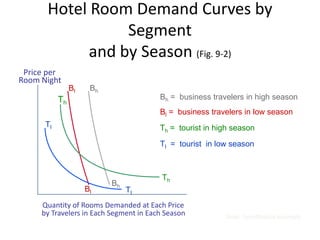
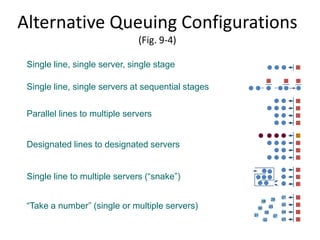
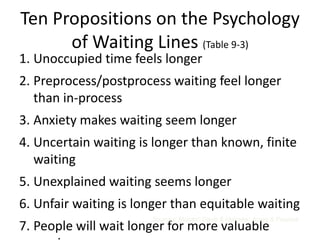
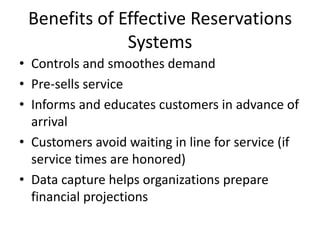
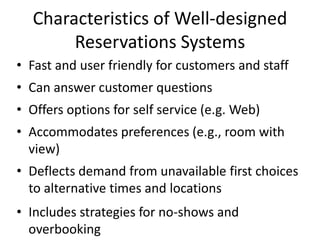
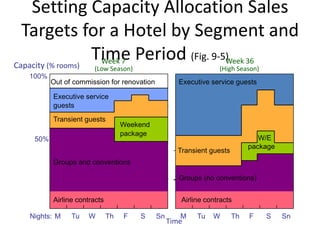
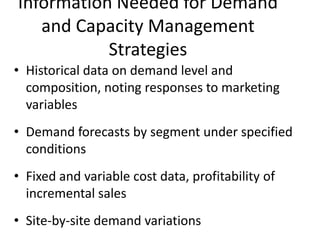
This document discusses balancing demand and capacity in services. It introduces key concepts like excess demand, excess capacity, maximum capacity and optimum capacity. It describes how demand can vary relative to capacity over time and strategies for managing capacity like leveling, stretching/shrinking, chasing demand and flexible capacity. The document also discusses predicting demand patterns, managing queues, using reservations systems and setting capacity allocation targets.