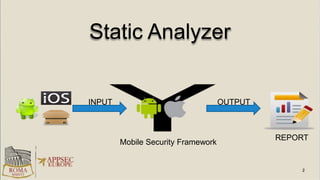
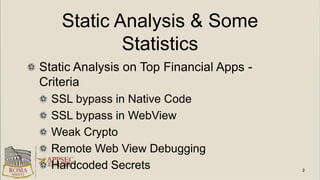
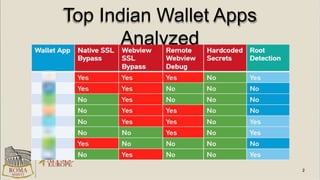
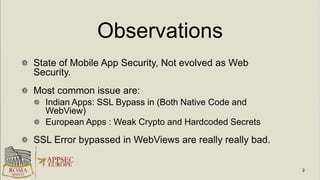
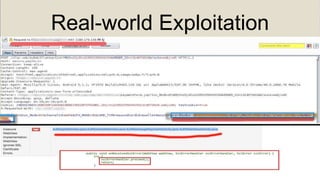
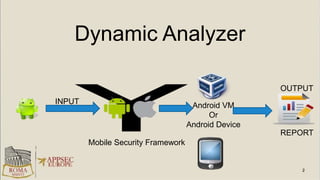
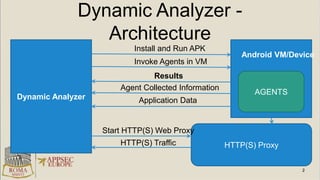
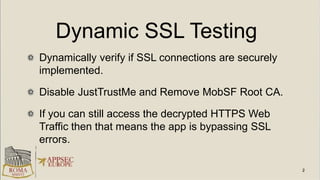
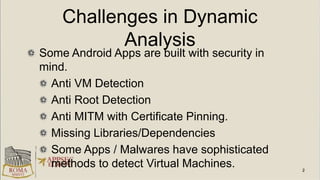
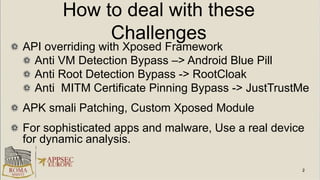
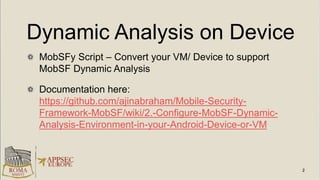
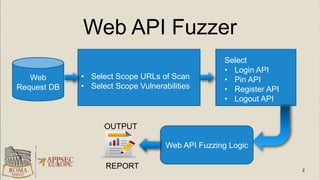
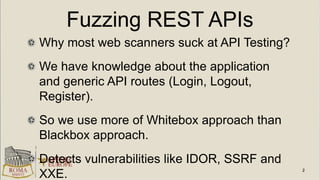
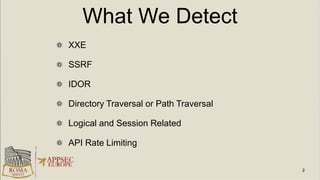
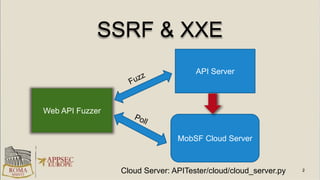
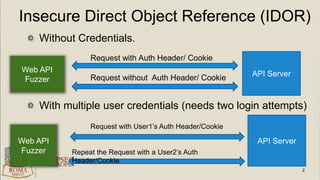
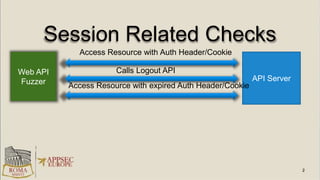
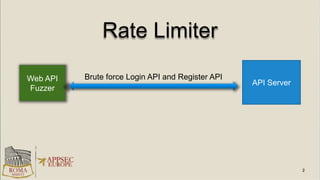
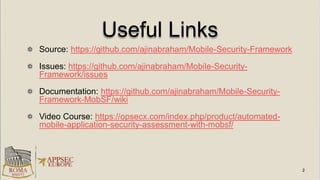
The document discusses the Mobile Security Framework (MobSF), an open-source automated pentesting framework for security testing of mobile applications on Android and iOS. It covers various topics including static and dynamic analysis, architecture, identified vulnerabilities in financial mobile apps, and challenges faced during dynamic analysis. Additionally, it mentions the capability of MobSF to conduct web API fuzzing and provides insights into common issues with mobile app security in various regions.