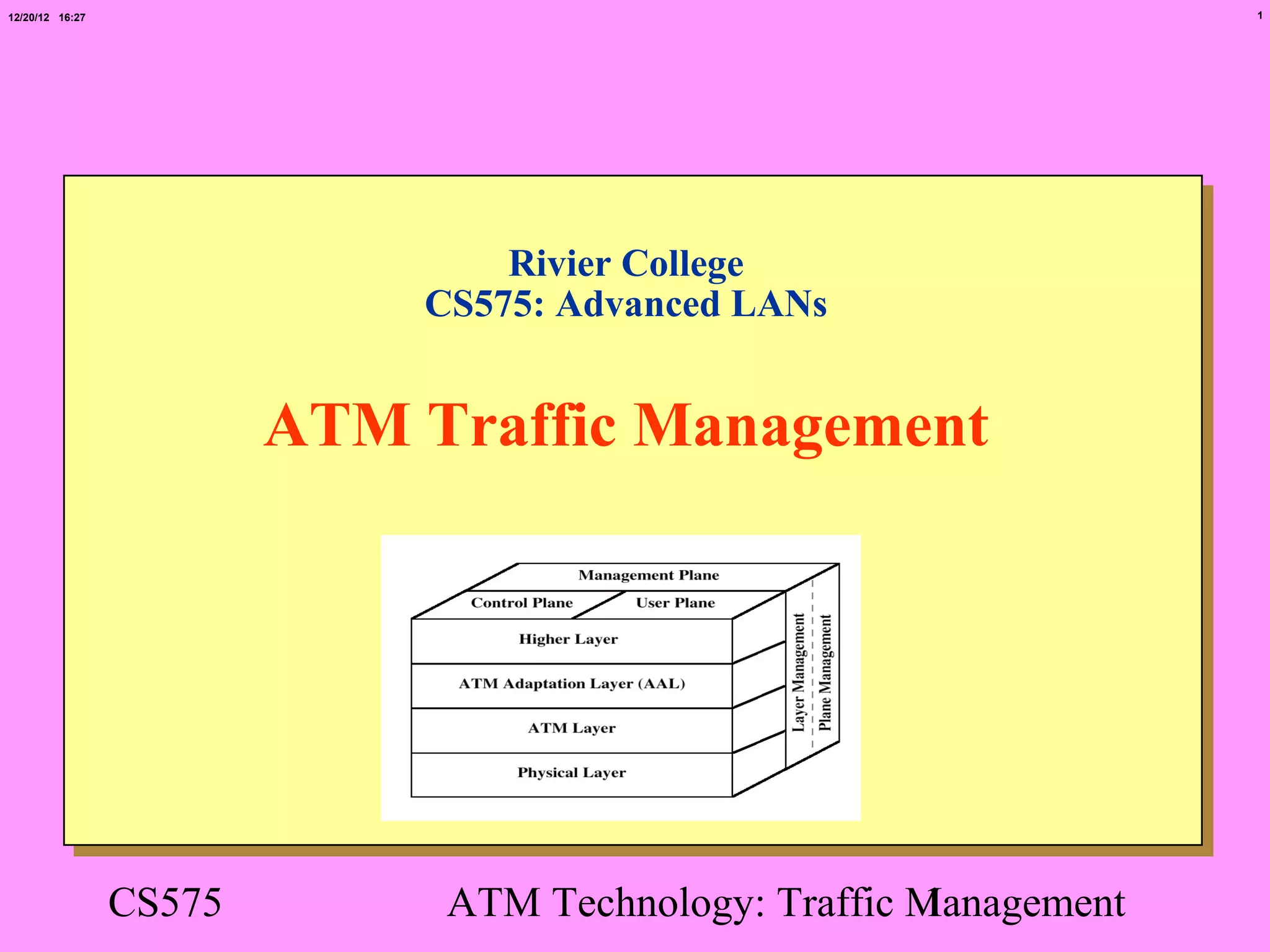
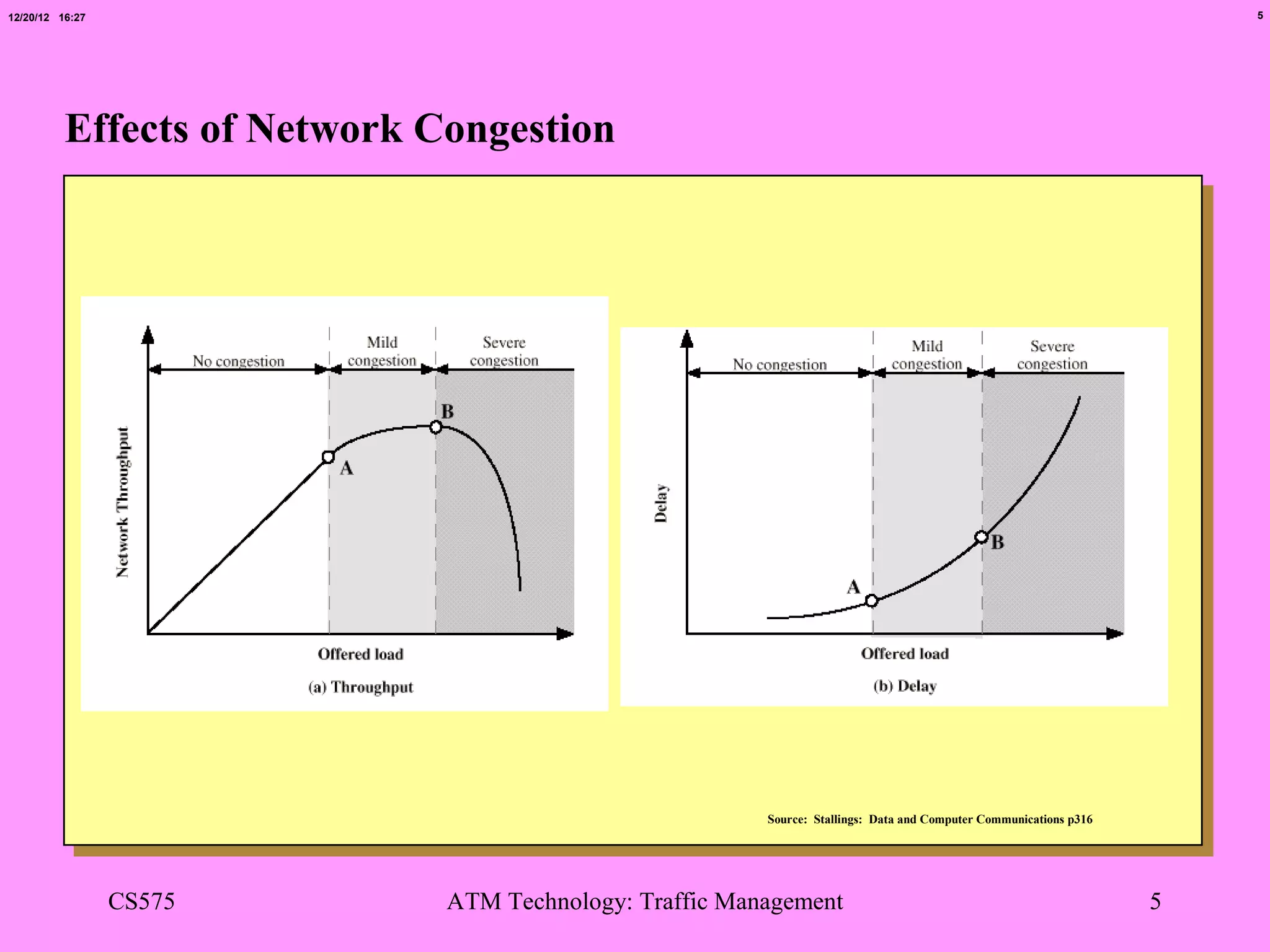
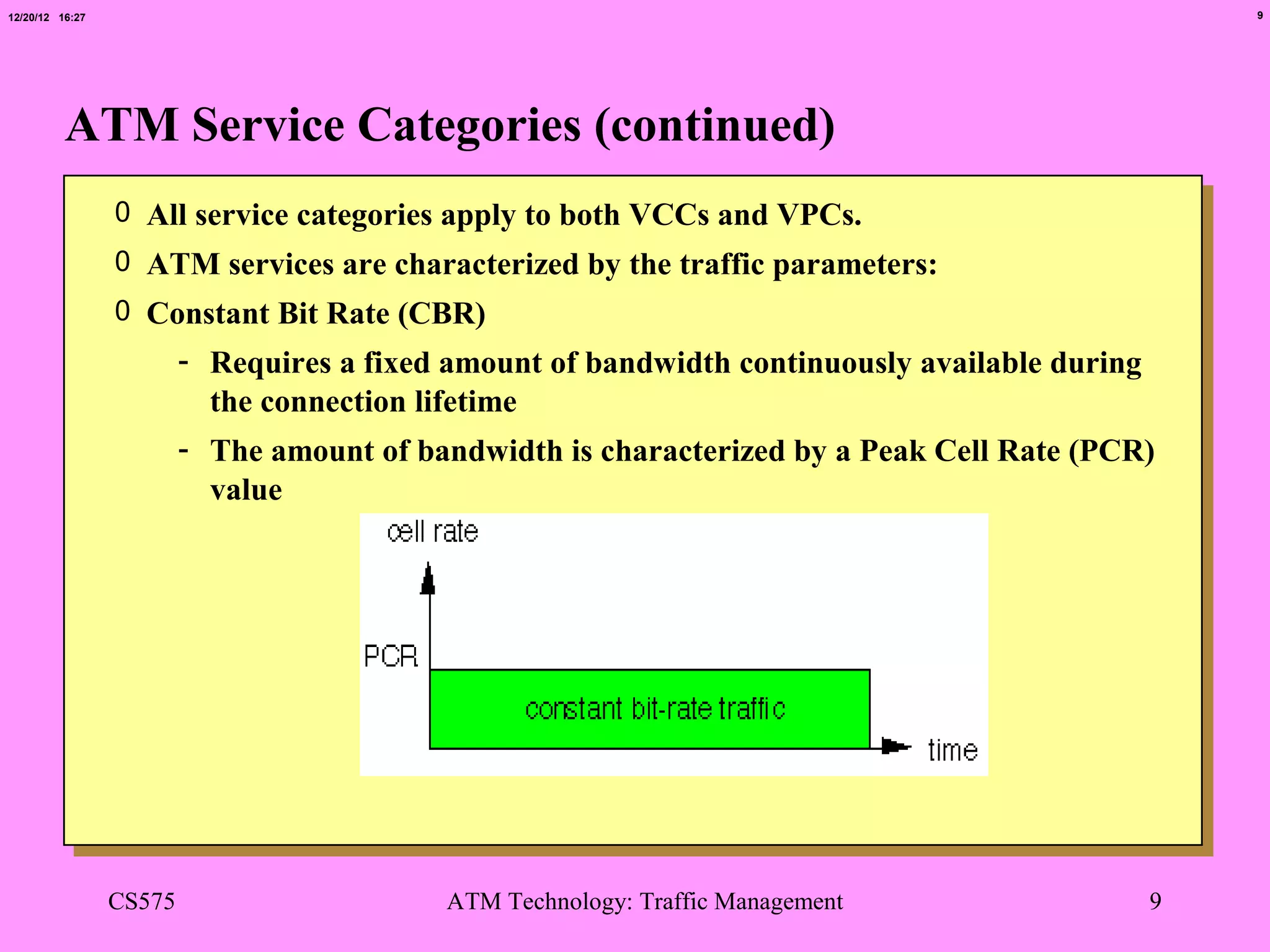
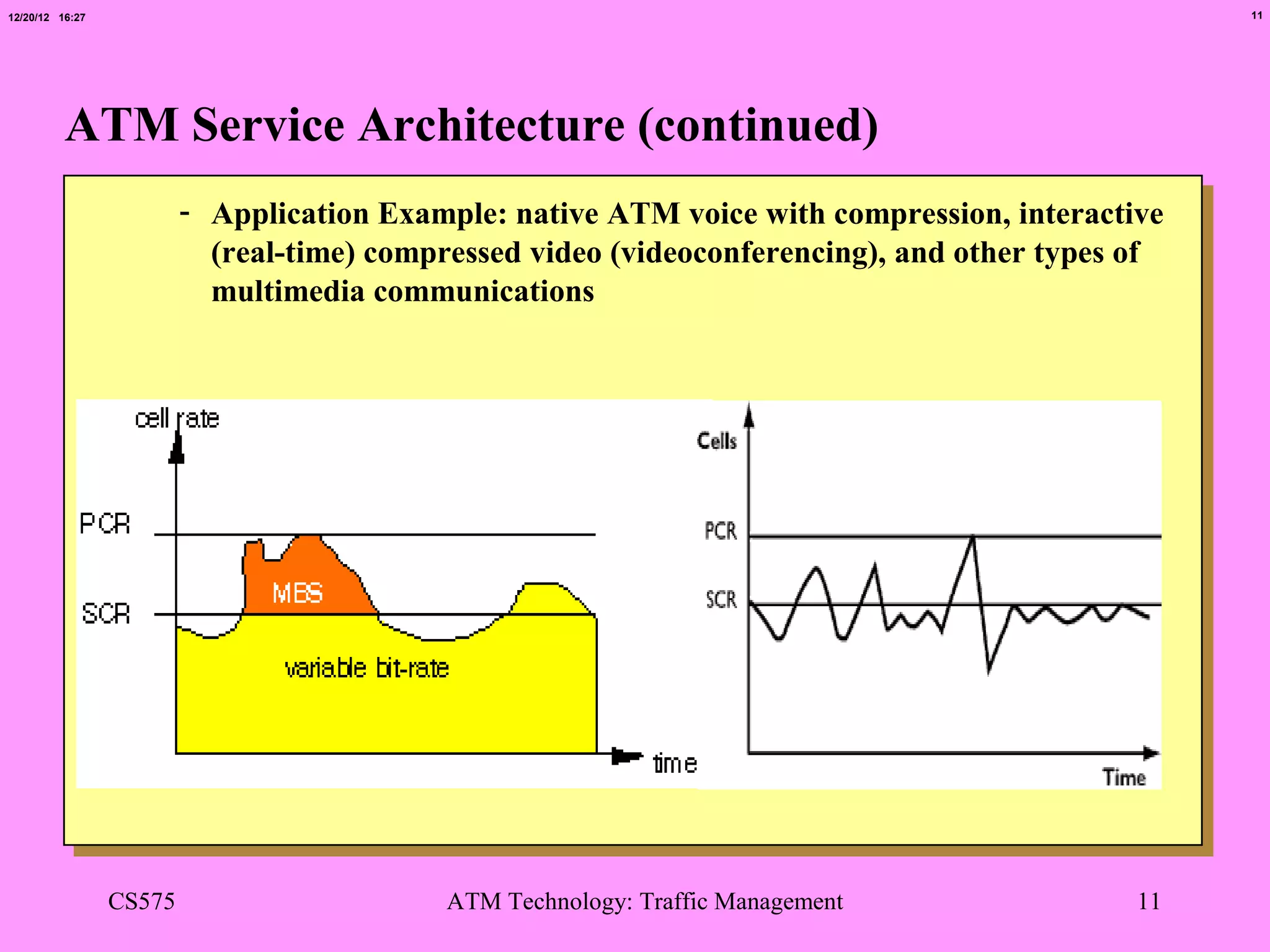
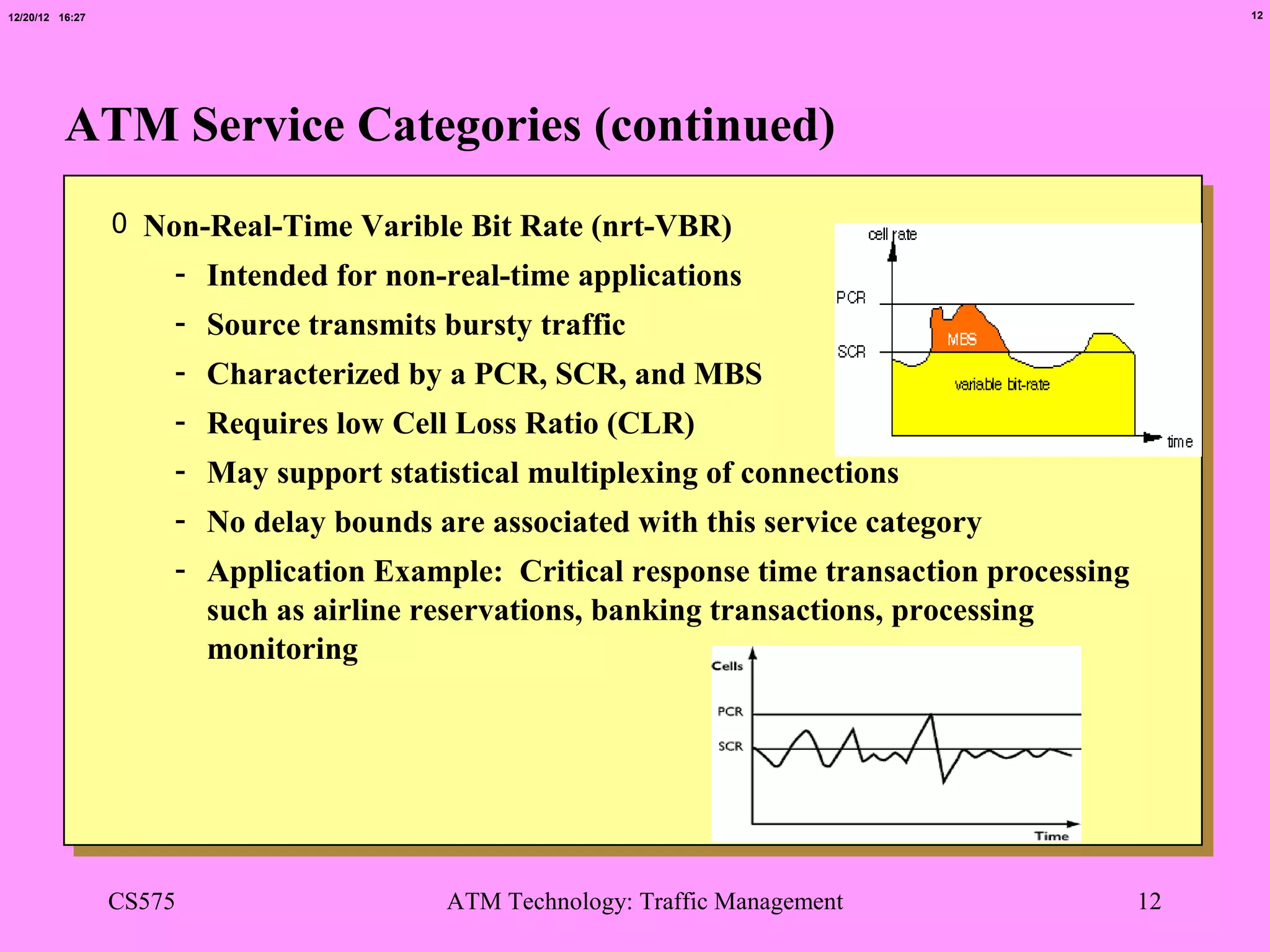
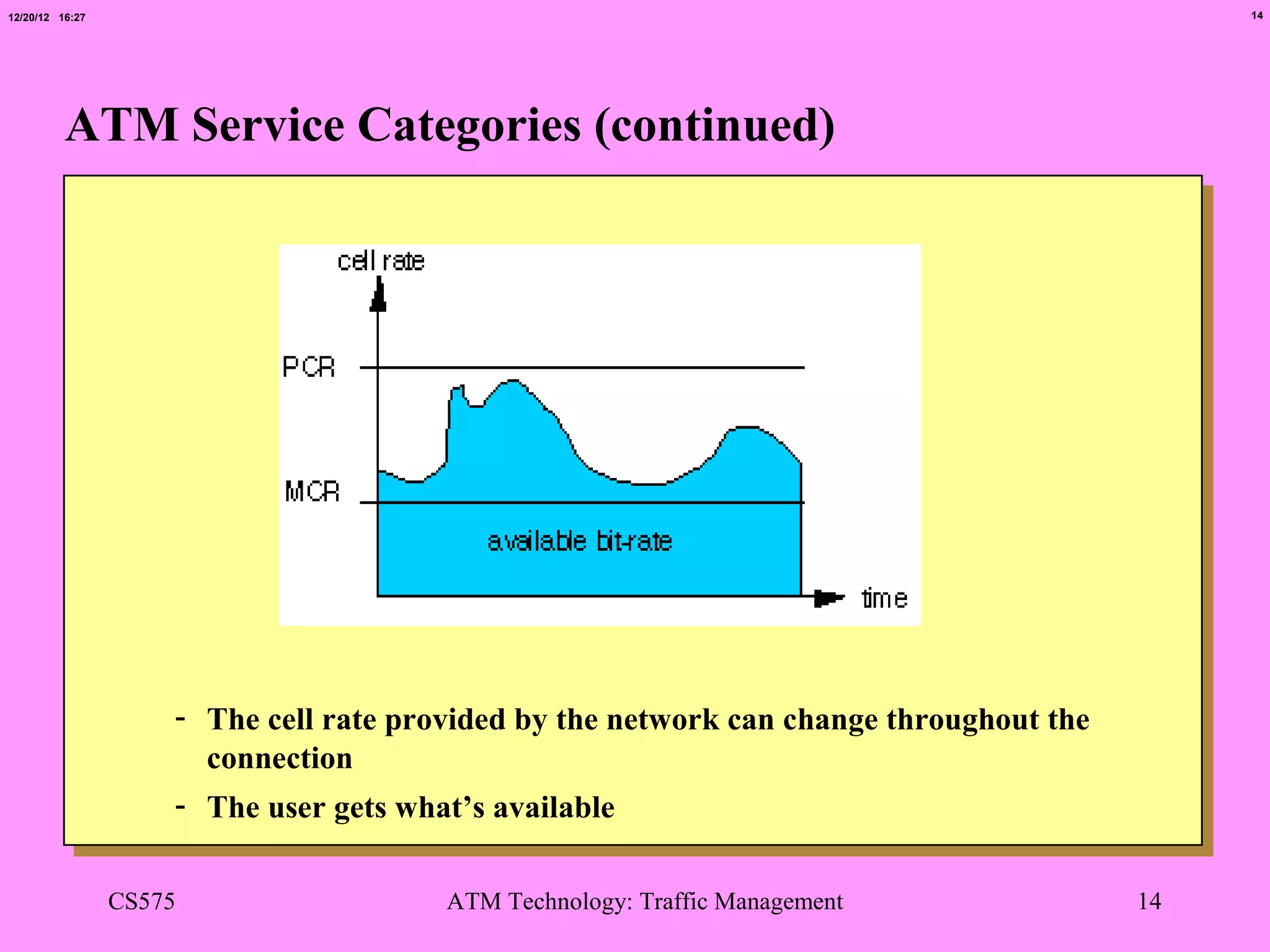
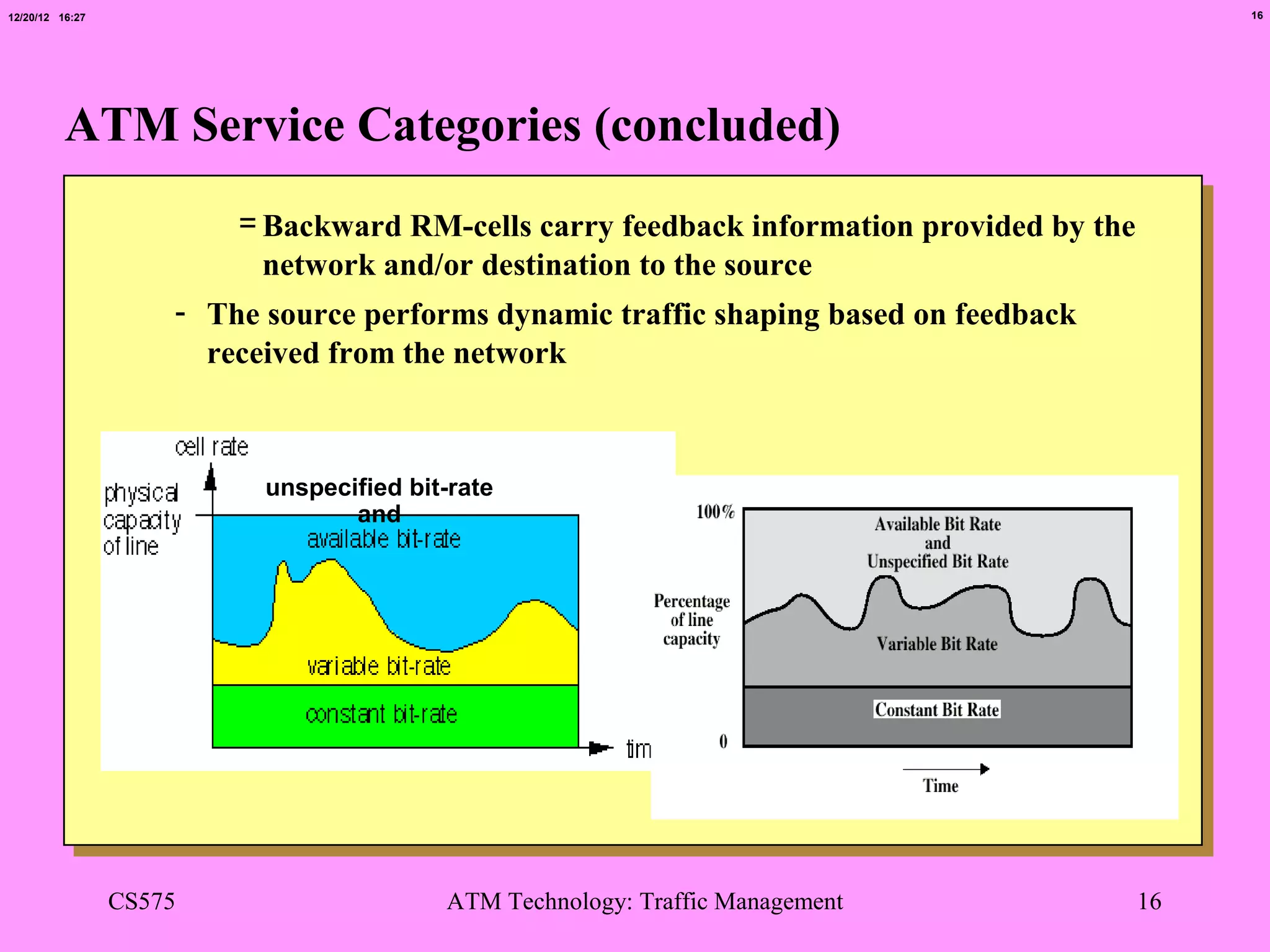
This document provides an overview of ATM traffic management. It discusses why traffic management is needed in ATM networks to support different applications and allocate resources fairly. It describes how network congestion can occur and the effects of congestion. It also defines important traffic parameters used in ATM like Peak Cell Rate and Sustainable Cell Rate. Furthermore, it outlines the different ATM service categories including Constant Bit Rate, Real-Time Variable Bit Rate, and Available Bit Rate, and provides examples of applications for each category.