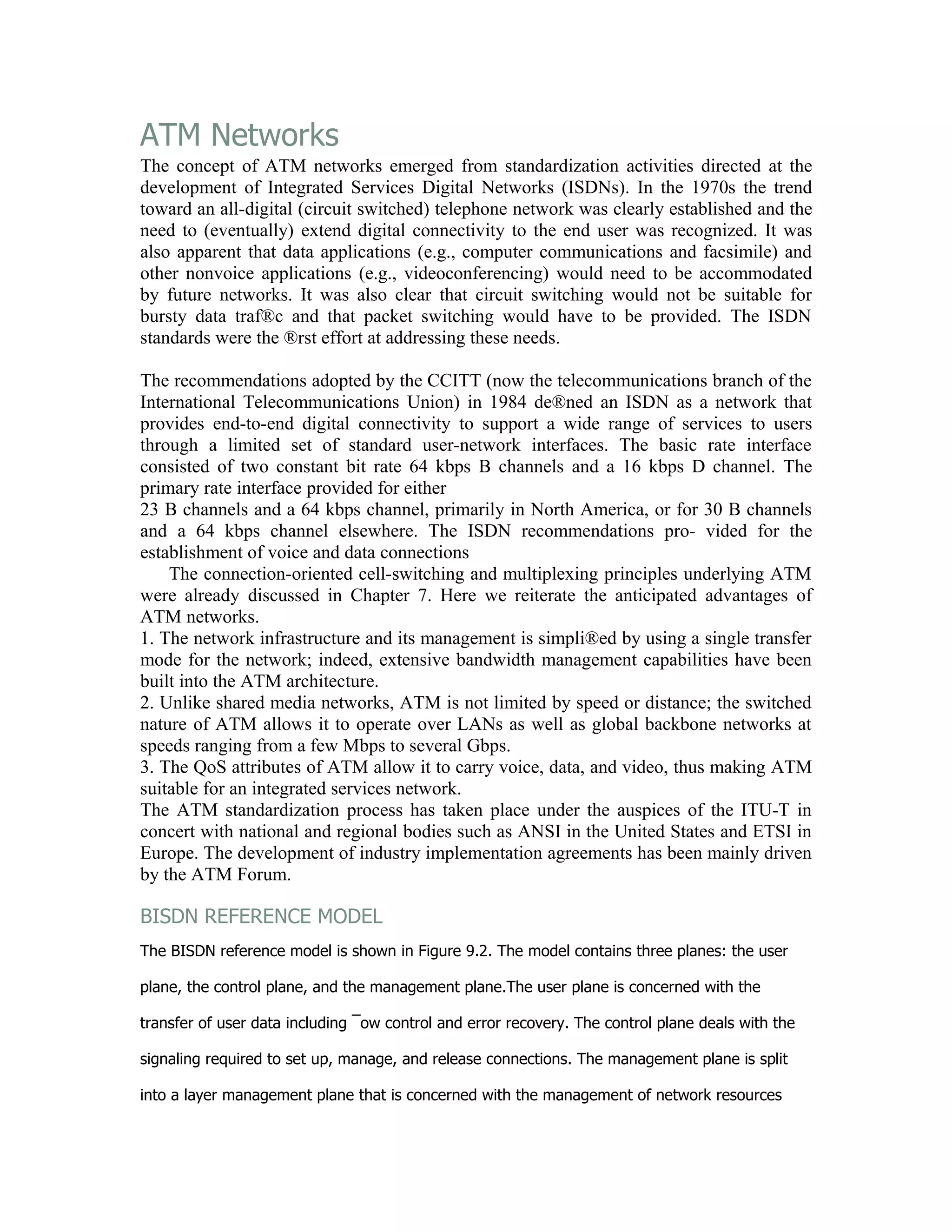
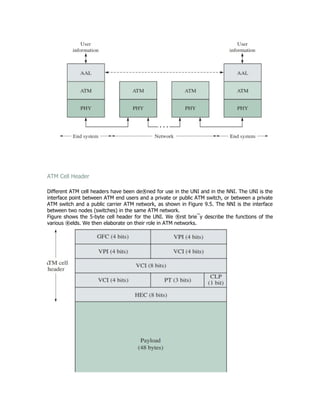
The document discusses the history and development of ATM networks. It explains that ATM networks emerged from standardization activities around Integrated Services Digital Networks (ISDN) in the 1970s. This was driven by the trend toward an all-digital telephone network and the need to support digital connectivity for end users as well as non-voice applications like data and video. The document then provides details on the ATM cell header format and its various fields that are used to identify connections and support different types of traffic and services.