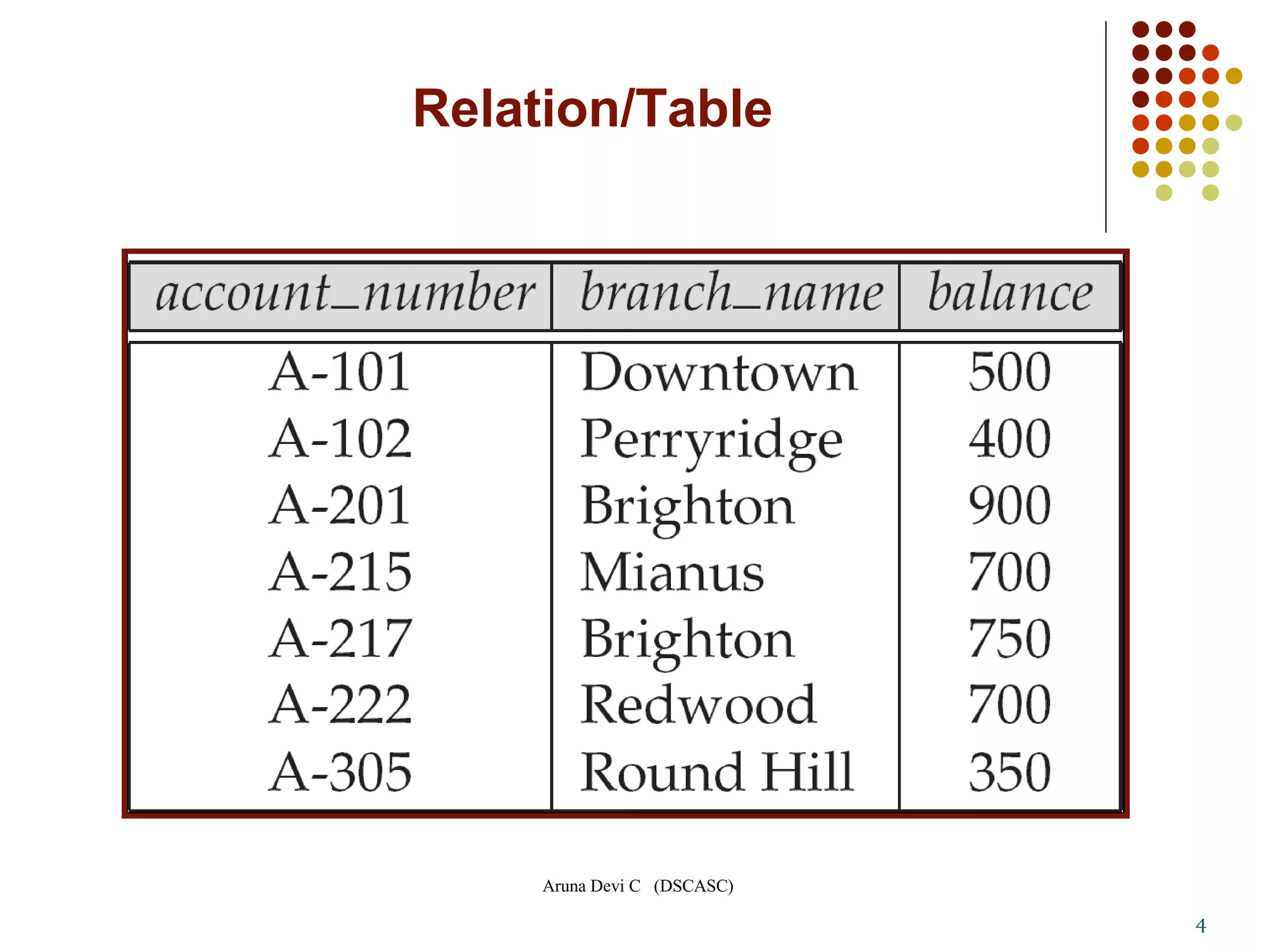
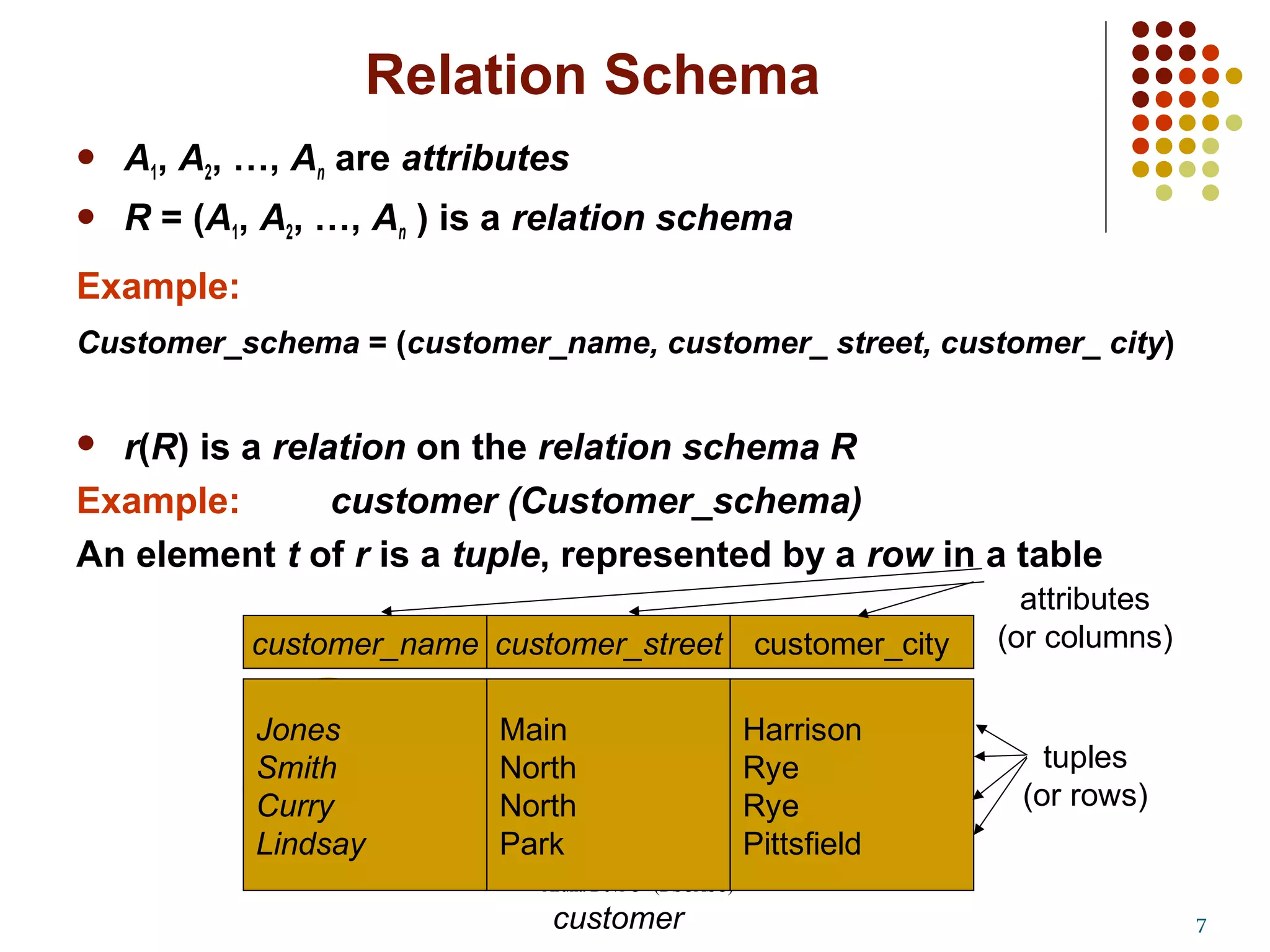
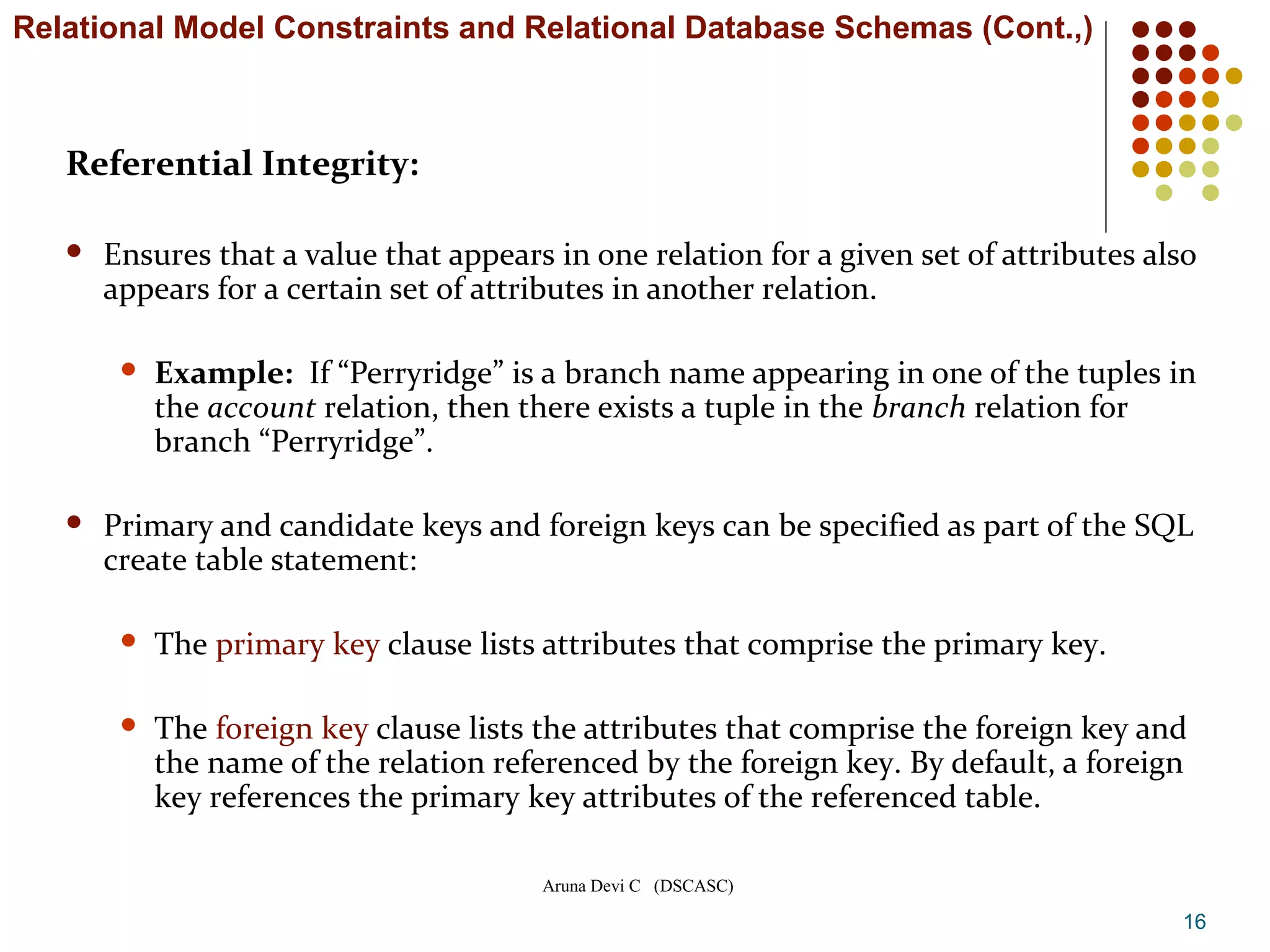
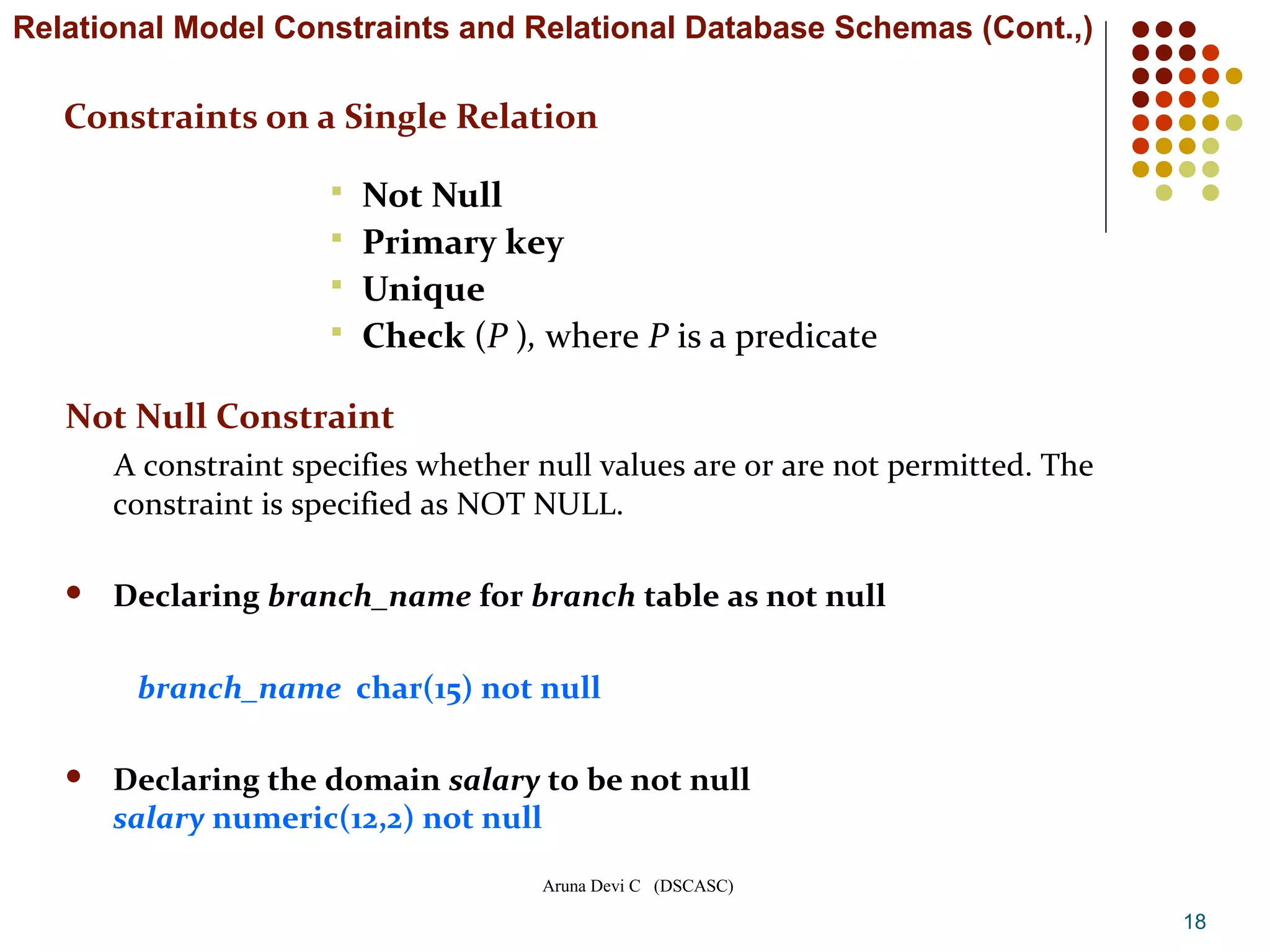
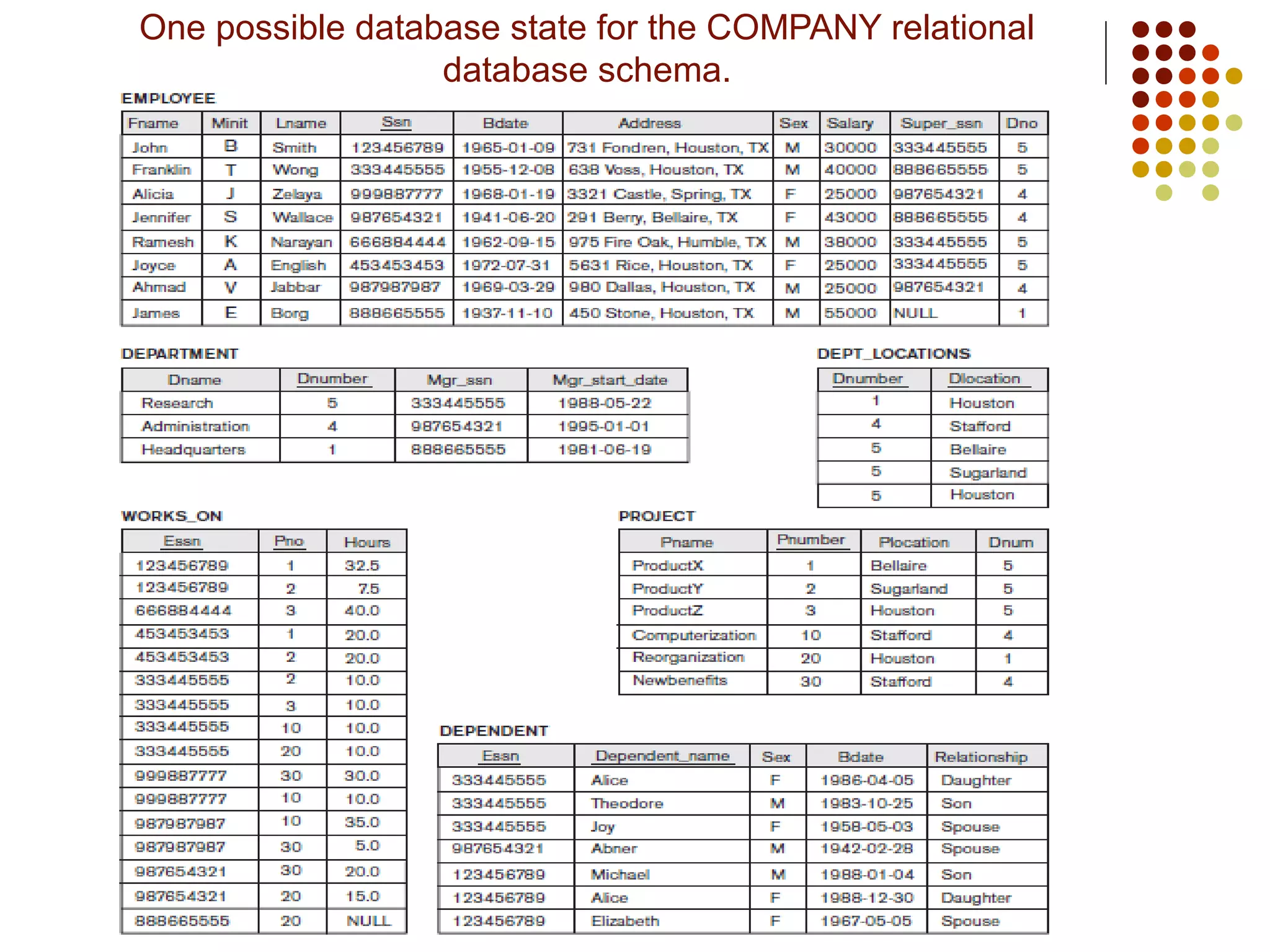
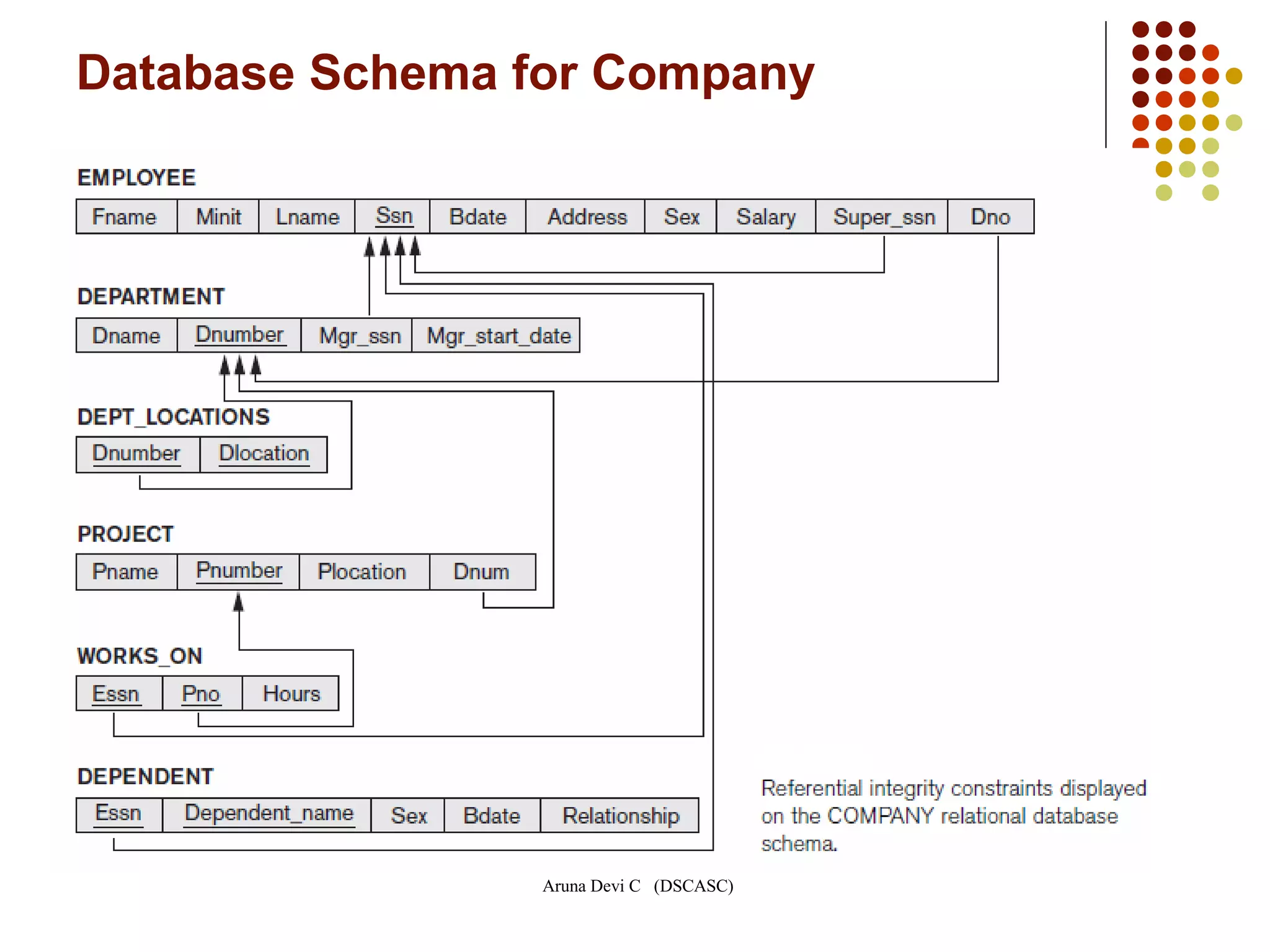
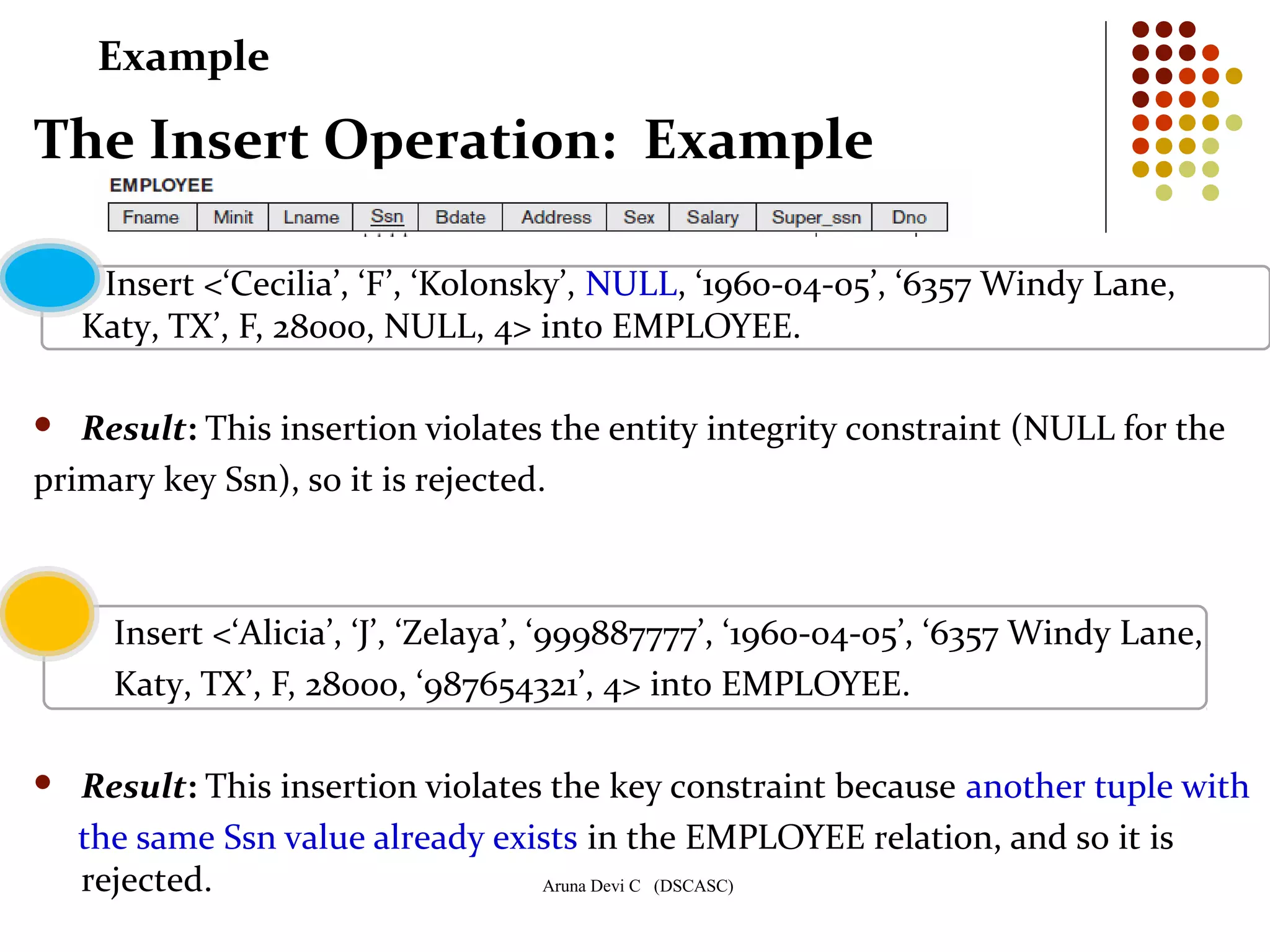
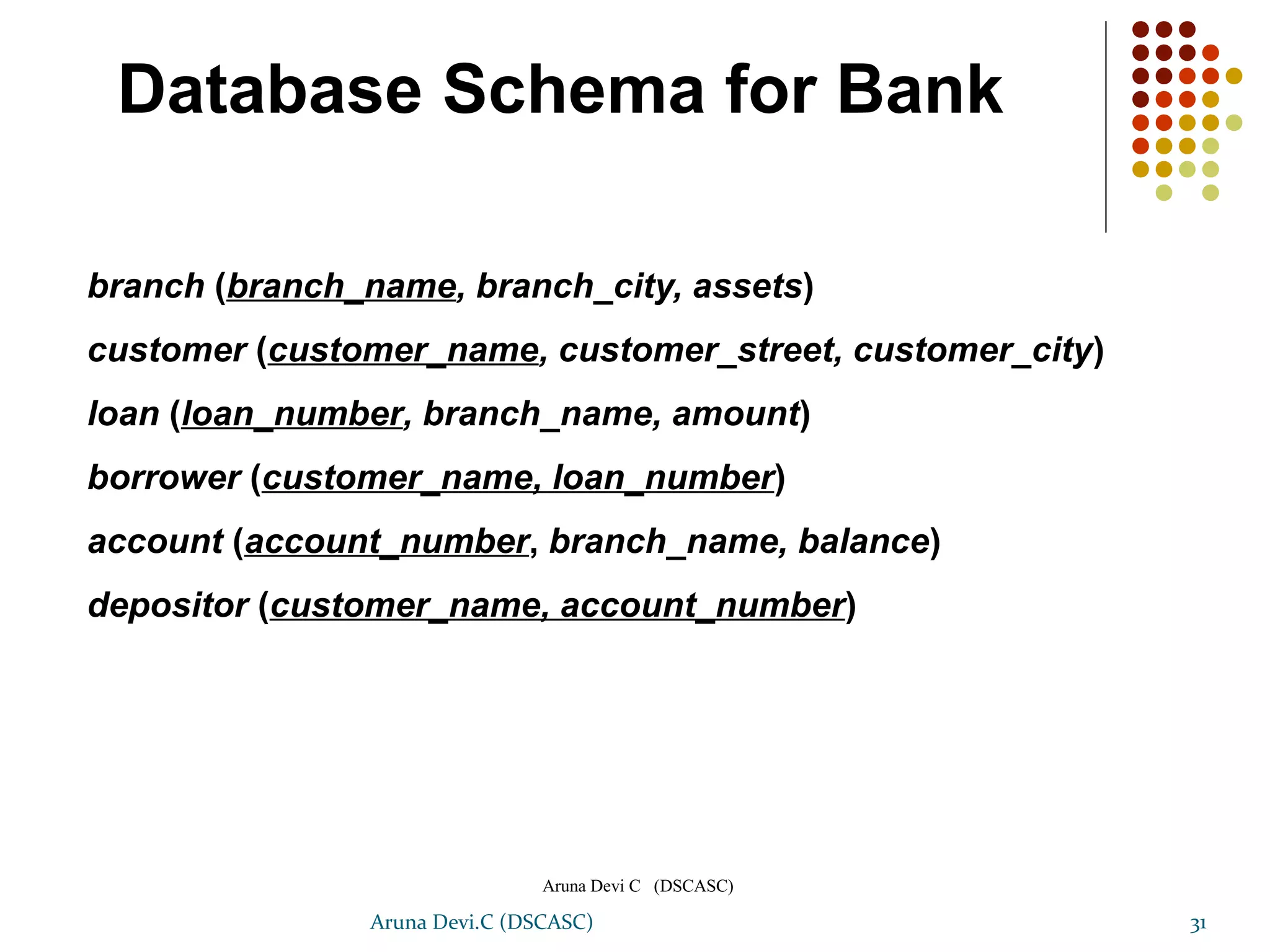
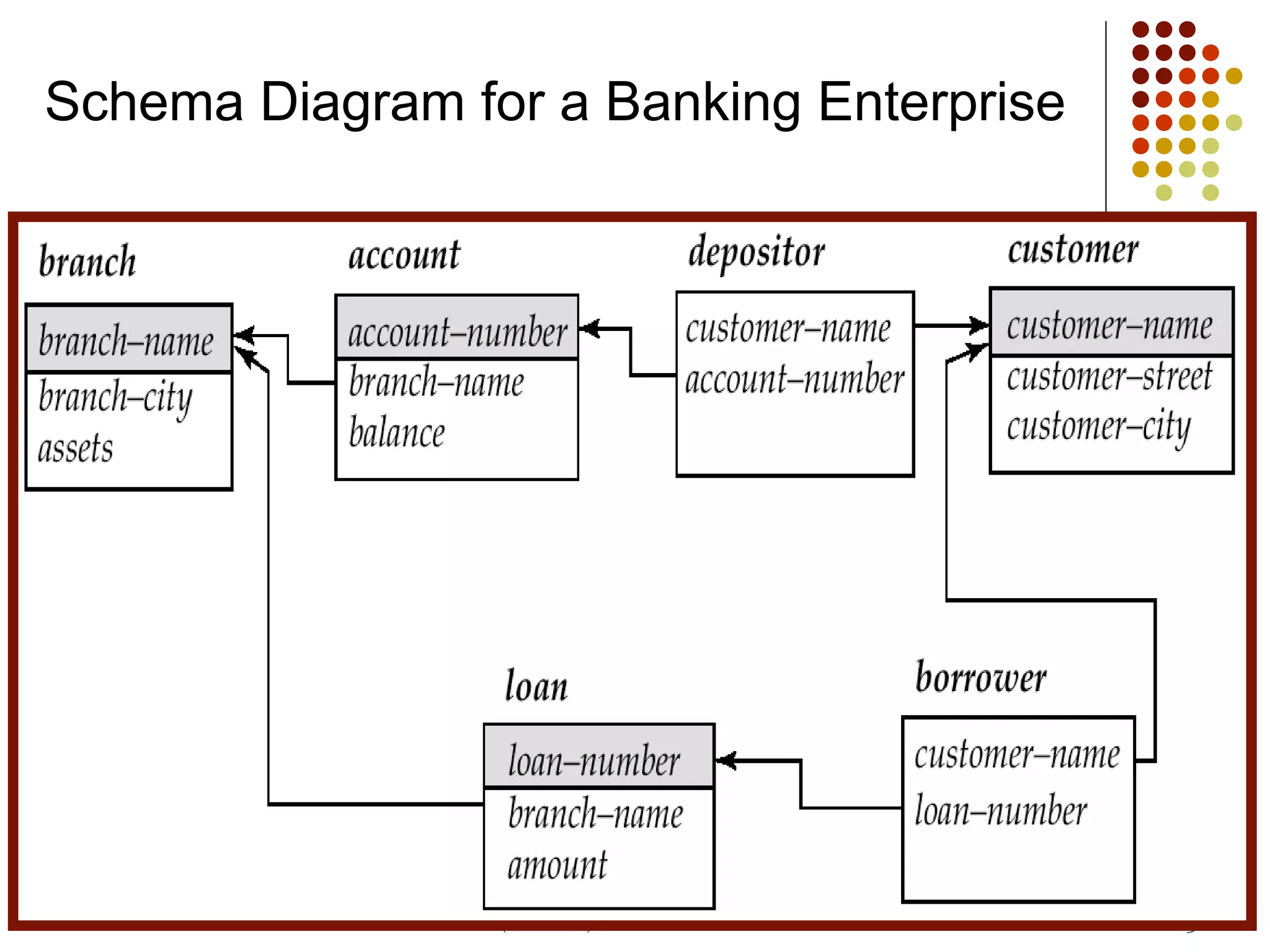
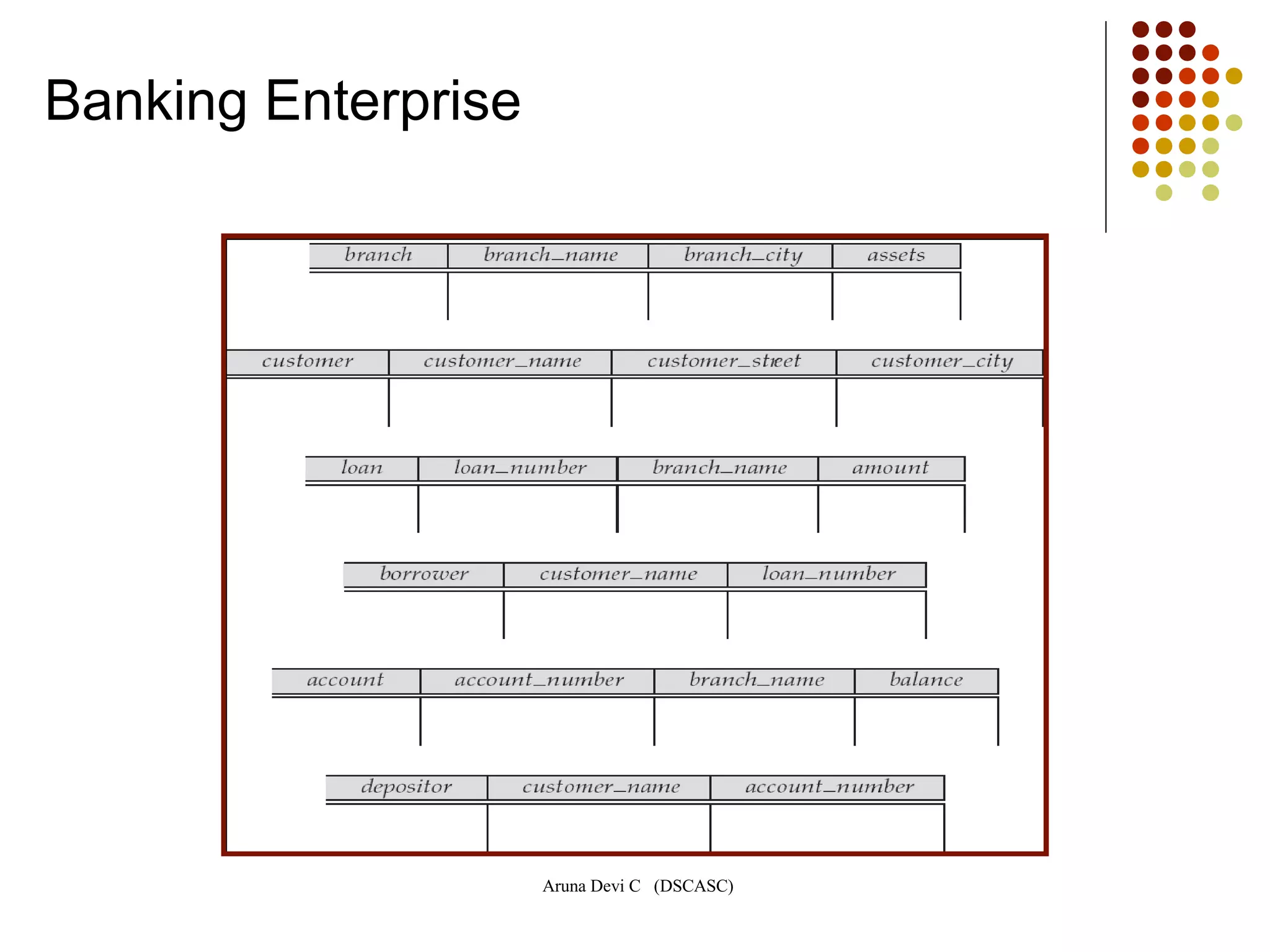
The document discusses the relational data model, introduced commercially in the 1980s, outlining its structure, capabilities, and key components such as attributes, tuples, and domains. It elaborates on relational schemas, constraints, and operations including inserting, updating, and deleting records, with emphasis on integrity constraints like primary keys and referential integrity. The content also explains how transactions involve a series of operations affecting the database state and highlights the importance of business rules in maintaining data validity.
![Aruna Devi C (DSCASC)
1
Data Base Management System
[DBMS]
Chapter 4
Unit III
Relational Model](https://image.slidesharecdn.com/dbms-iimca-ch4-relationalmodel-2013-150630114115-lva1-app6891/75/Dbms-ii-mca-ch4-relational-model-2013-1-2048.jpg)