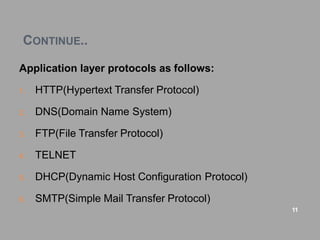
The document discusses several key application layer protocols:
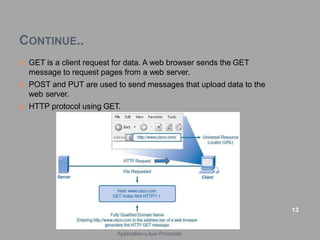
1. HTTP is used to transfer web pages over the internet using requests and responses between clients and servers. It operates over TCP port 80.
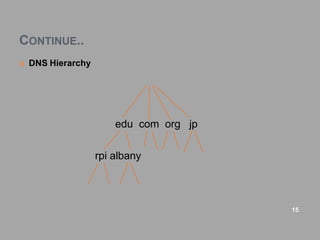
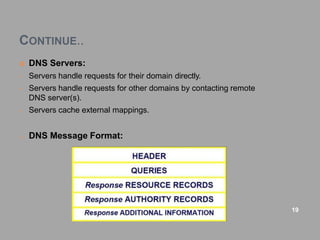
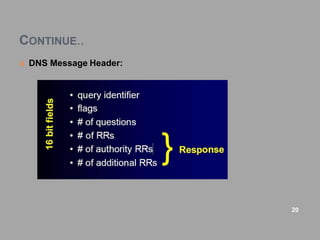
2. DNS is used to translate between hostnames and IP addresses in a hierarchical system of top-level and subdomain names. It allows humans to use easy-to-remember names.
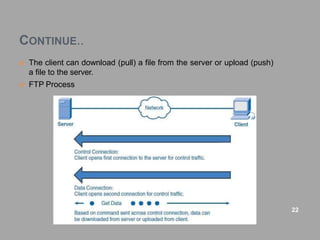
3. FTP establishes two TCP connections to transfer files between a client and server, using different ports for control commands and the file data. It allows downloading and uploading of files.