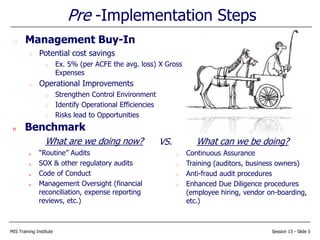
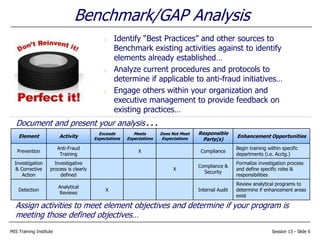
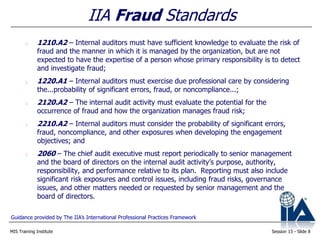
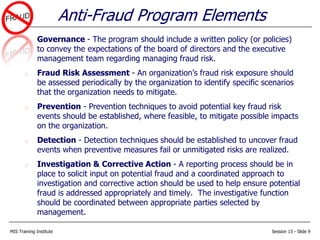
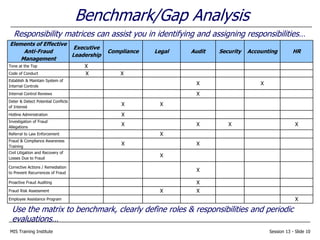
The document outlines strategies for implementing an effective anti-fraud program, including establishing governance, conducting fraud risk assessments, implementing prevention and detection controls, investigating fraud allegations, and taking corrective actions. It discusses benchmarking existing anti-fraud activities, defining roles and responsibilities, identifying key risk categories and schemes, measuring risks, and prioritizing next steps such as obtaining management buy-in and continuously improving prevention and detection efforts. The overall goal is to prevent, detect, and address fraud through a formal, collaborative anti-fraud program.

![MIS Training Institute Session 13 - Slide 16
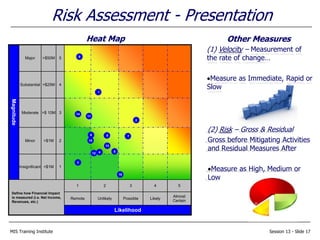
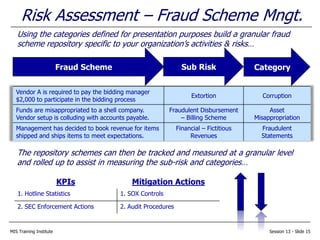
Risk Assessment - Measures
KPIs and Mitigating Activities provide “real” data to support your assessment;
however, Management should be updated and risks ranked by using the…
Magnitude (i.e. Significance):
High (3) = > $10 Million
Med (2) = Between $4 Million and $10 Million
Low (1) = < $4 Million
Likelihood (i.e. Controls, Mitigating Activity):
Strong (1) = Preferred Practice
Good (2) = Adequate
Low (3) = Needs Improvement
Likelihood (i.e. Pressure, Occurrence):
High (3) = Significant pressure
Med (2) = Moderate pressure
Low (1) = Little to no pressure
Magnitude + Likelihood [(Controls) + (Pressure)] = Rank
$s should reflect your Organization’s Appetite](https://image.slidesharecdn.com/antifraudprogram-151001031029-lva1-app6892/85/Anti-fraud-program-16-320.jpg)