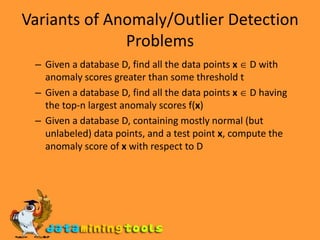
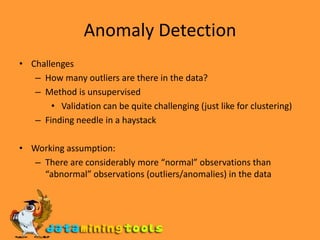
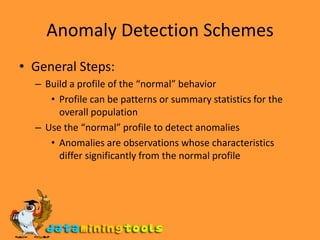
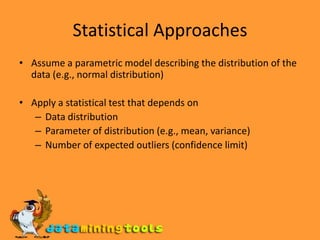
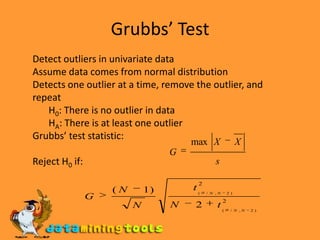
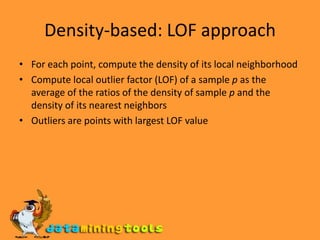
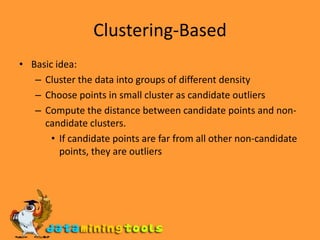
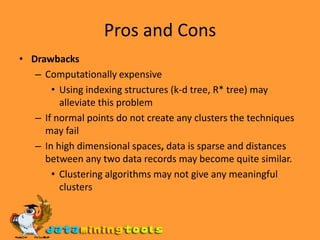
Anomaly detection techniques aim to identify outliers or anomalies in datasets. Statistical approaches assume a data distribution and use tests to detect outliers. Distance-based approaches represent data as vectors and use nearest neighbors, densities, or clustering to identify anomalies. Model-based approaches build profiles of normal behavior and detect anomalies as observations differing significantly from normal profiles. Key challenges are determining the number of outliers, handling unlabeled data, and detecting anomalies as needles in haystacks of normal data.