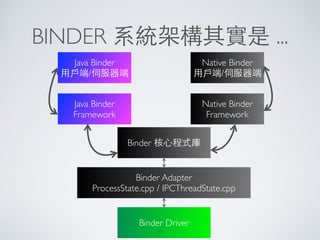
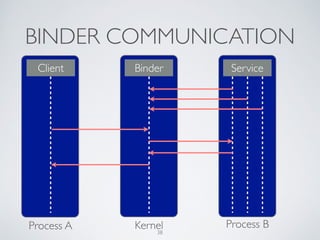
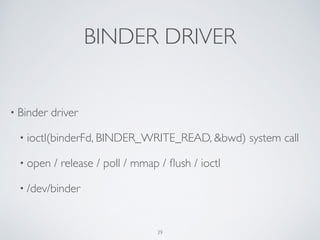
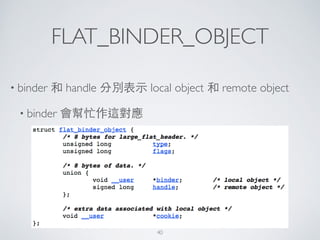
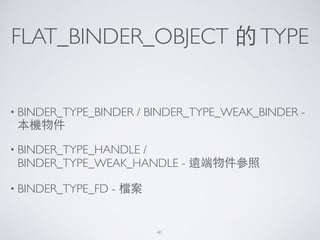
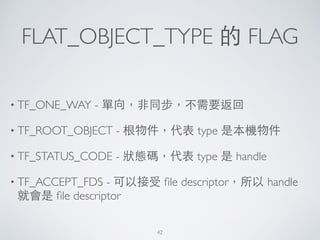
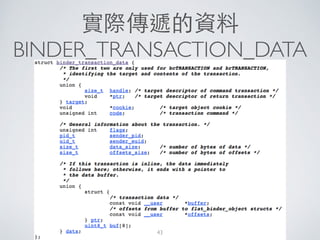
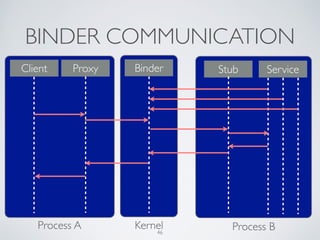
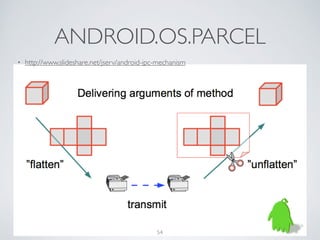
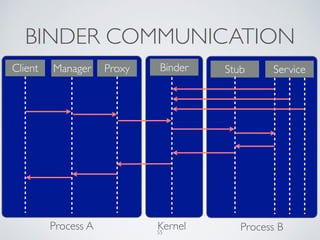
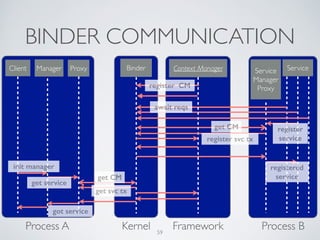
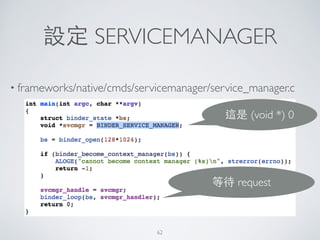
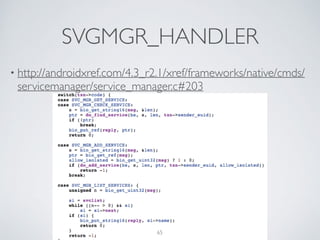
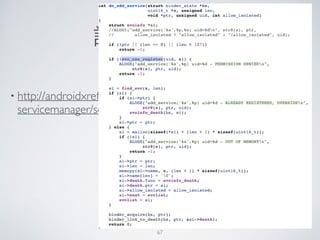
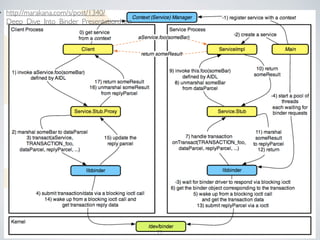
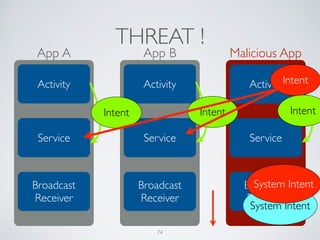
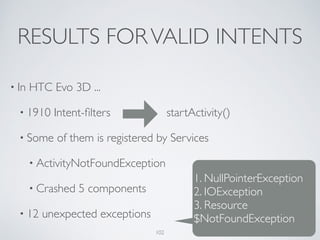
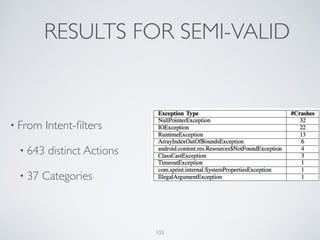
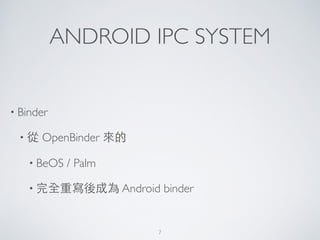
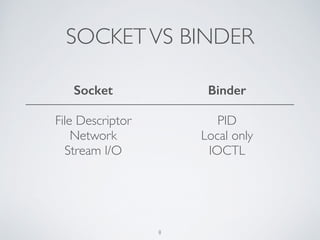
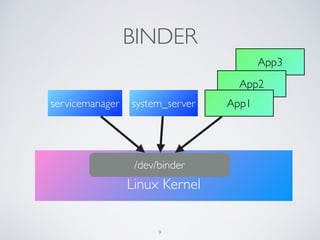
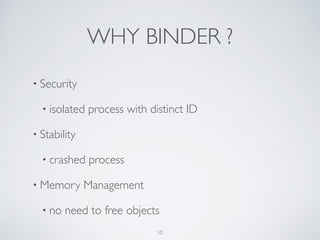
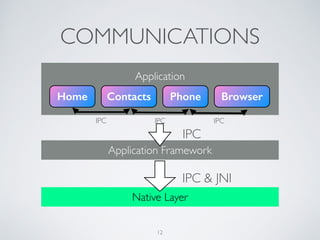
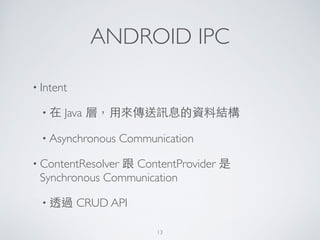
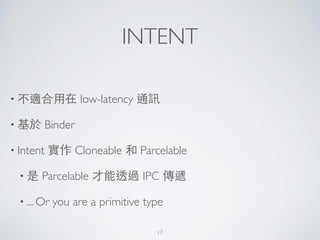
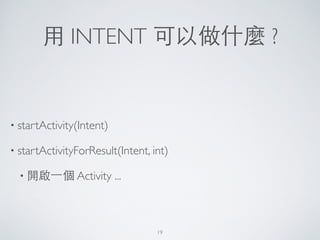
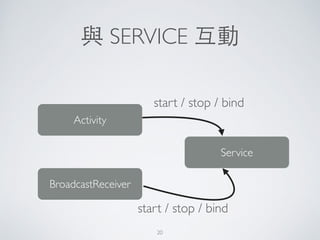
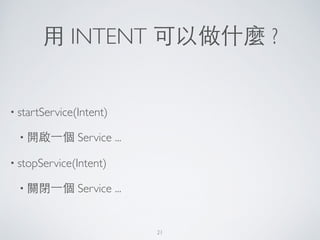
Android uses the Binder IPC mechanism for communication between processes. Binder allows for asynchronous remote procedure calls through a client-server model. It works by passing flat binder objects between processes using the binder driver in the kernel. Key aspects of Android IPC include Intents for asynchronous messaging, AIDL for synchronous RPCs across processes, and system services that are registered with the service manager.





![BINDER !
• 超重要的!
In the Android platform, the binder is used for
nearly everything that happens across processes
in the core platform. - Dianne Hackborn!
[https://lkml.org/lkml/2009/6/25/3]
34](https://image.slidesharecdn.com/androidipc-keynote11-140430081351-phpapp02/85/Android-IPC-Mechanism-34-320.jpg)