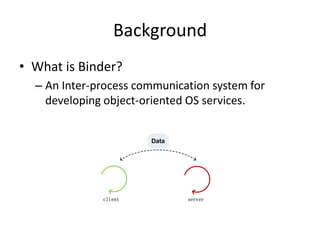
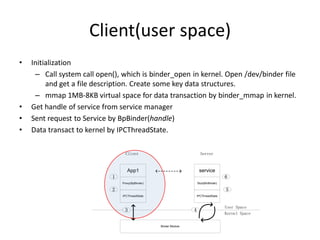
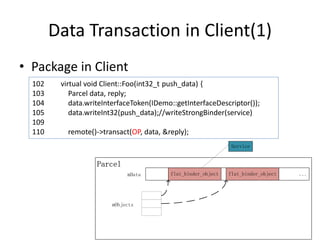
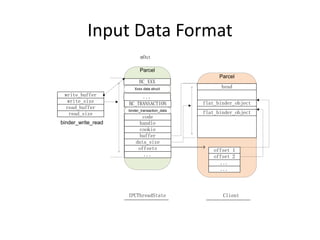
Binder is an inter-process communication system used in Android to allow processes to interact. It uses a client-server model where a client contacts a service via its binder handle. Data is packaged into a parcel and sent to the kernel binder driver via ioctl calls. The driver then delivers the transaction to the target service's thread to be processed by its stub and dispatched to the actual service code.


![Transaction in Binder –Client (2)
Target SpacedataCopyParcelParcelwrite_sizewrite_bufferread_sizeread_bufferbinder_write_readbufferdata_sizeoffsets... binder_transaction_datacodecookiehandleoffset 1offset 2... ... flat_binder_objectflat_binder_objectBC_TRANSACTIONBC_XXXXxxx data structmOut... headIPCThreadStateClientbufferpriorityoffsetssender_euidbinder_transactioncodeto_threadto_procdata... offsets_sizedata_sizetarget_nodebinder_bufferOffsets[] Copy](https://image.slidesharecdn.com/understandingbinderinandroid-140903210317-phpapp02/85/Understanding-binder-in-android-19-320.jpg)
![Transaction in Binder -- Server
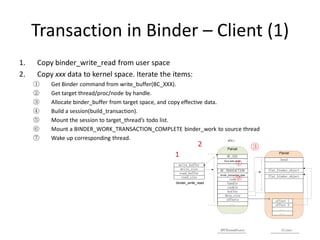
1.Server thread wake up and get a binder_work(binder_transaction) from todo list
2.Build a binder_transaction_data from binder_transaction
3.Set priority of current thread of client.
4.The buffer and offsets will be virtual address
–Virtual address = kernel address + address offset
5.Copy binder_transaction_data to mIn
6.Return from kernel
7.IPCThreadState iternate the command and data.
–For BR_TRANSACTION, call stub’s onTransact function,
which will call server service function finally.
Target Spacedatabufferpriorityoffsetssender_euidbinder_transactioncodeto_threadto_procdata... offsets_sizedata_sizetarget_nodebinder_bufferOffsets[] bufferdata_sizeoffsets... binder_transaction_datacodecookiehandle Kernel Space write_sizewrite_bufferread_sizeread_bufferbinder_write_readParcelmInBR_NOOPDatabinder_transaction_dataBR_TRANSACTIONCopy to user User Space](https://image.slidesharecdn.com/understandingbinderinandroid-140903210317-phpapp02/85/Understanding-binder-in-android-20-320.jpg)