Embed presentation
Download as PDF, PPTX
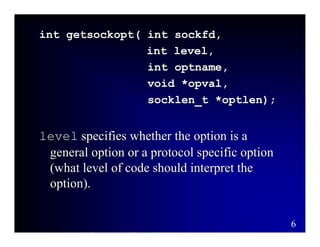
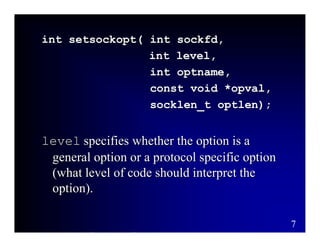
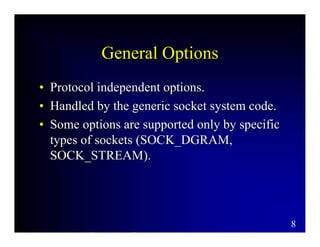
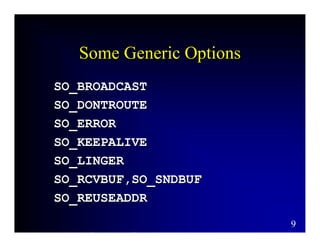
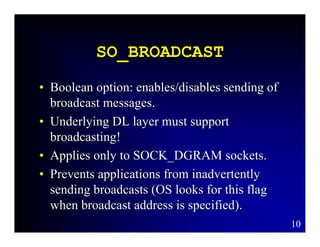
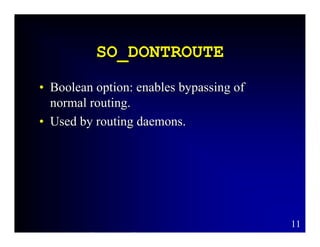
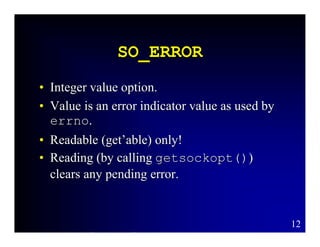
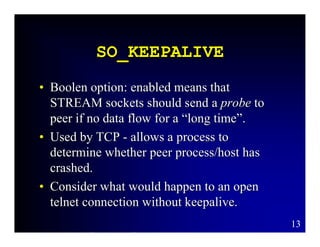
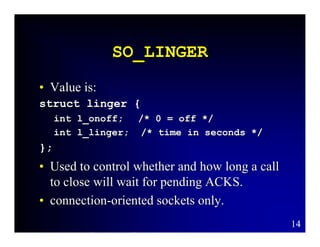
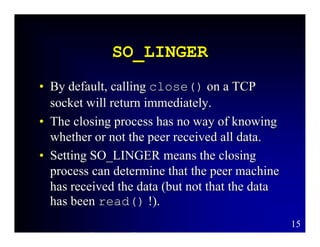

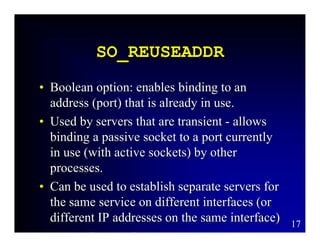
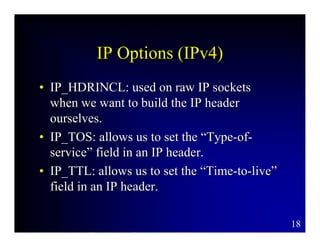
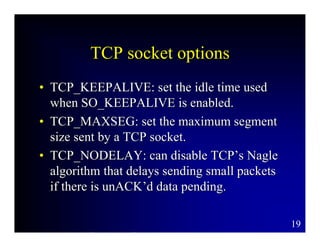
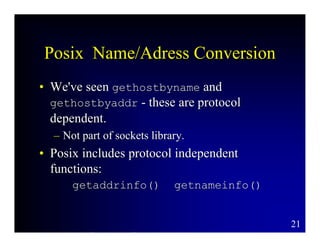
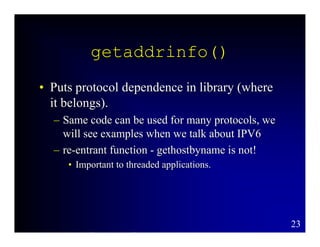
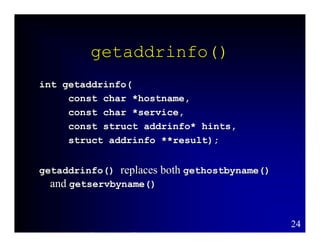
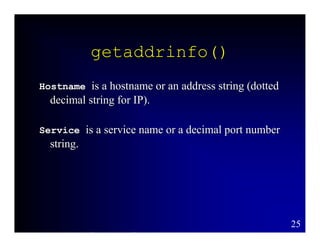
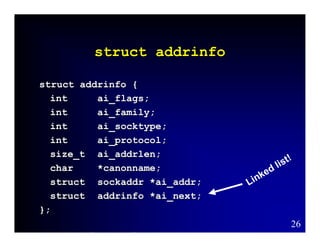
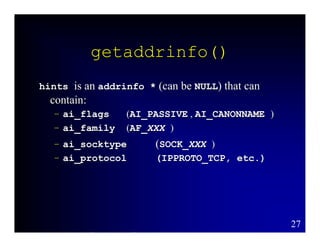
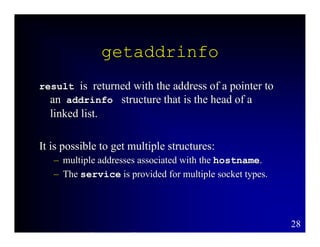
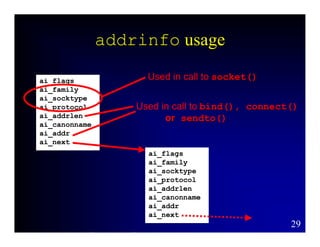
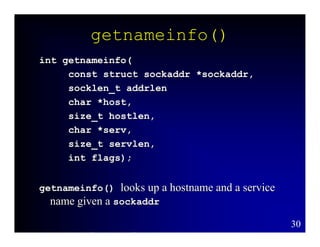
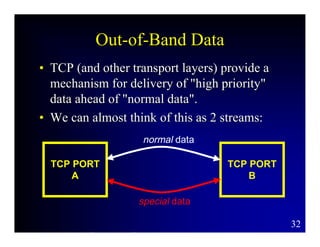
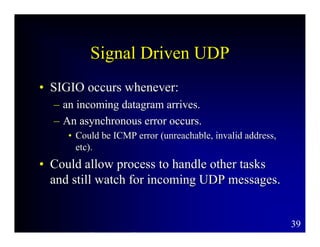
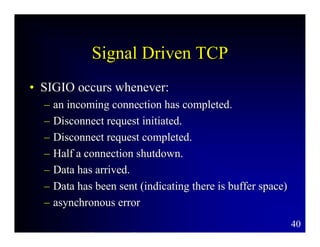

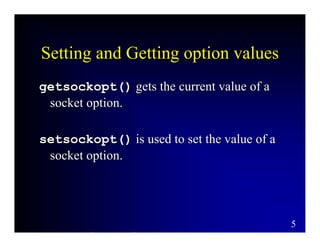
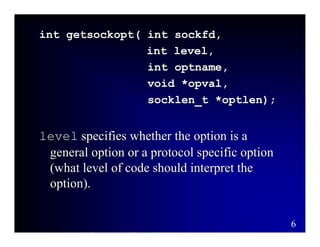
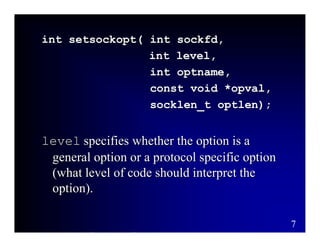
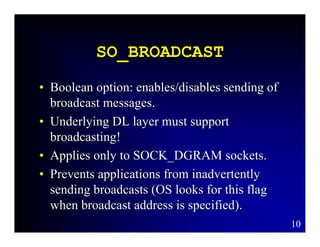
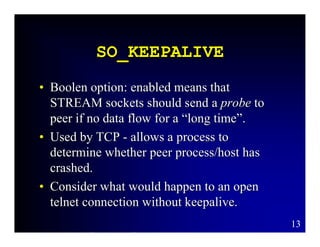
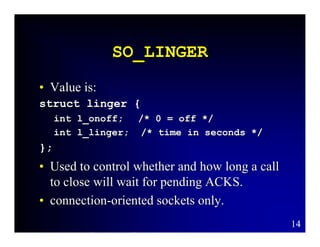
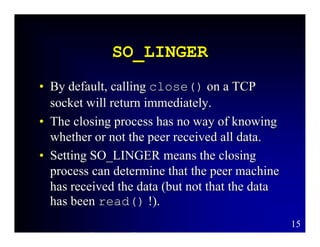
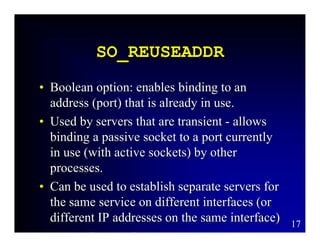
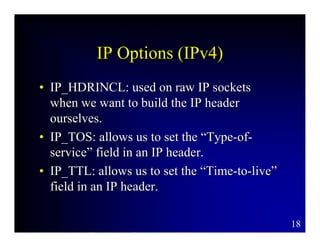
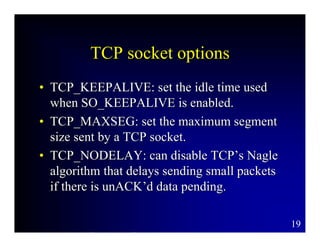
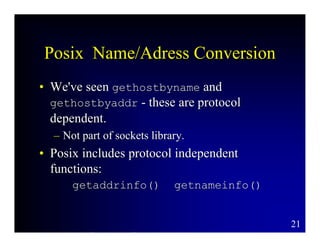
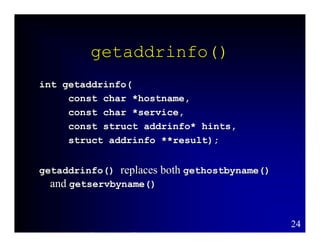
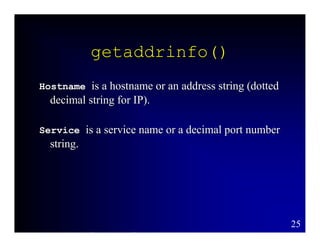
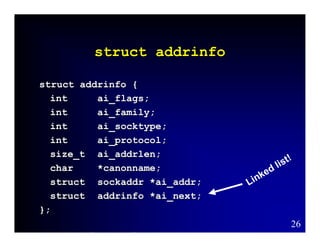
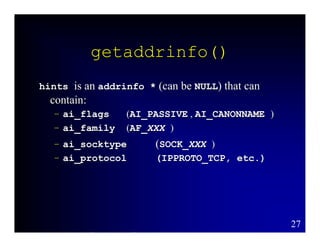
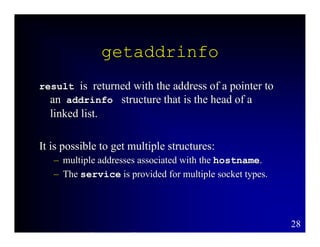
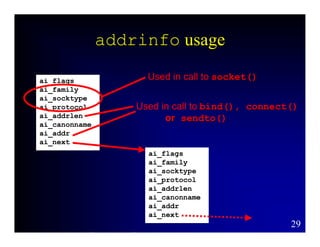
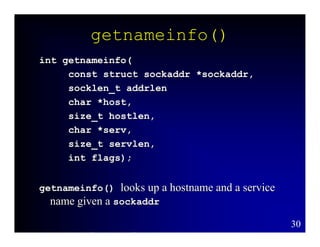
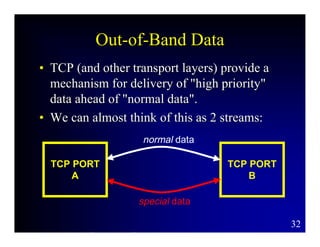
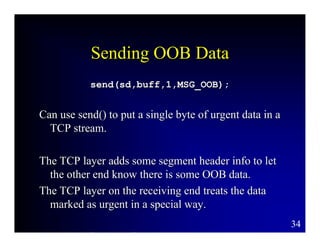
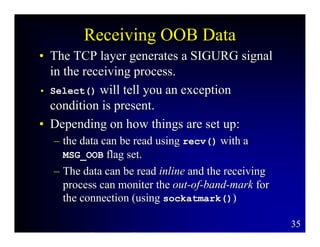
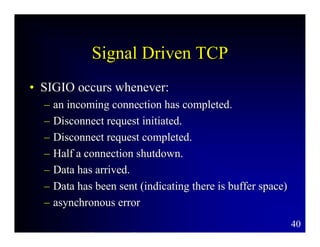
This document provides an overview of advanced socket programming concepts including socket options, POSIX name and address conversion functions like getaddrinfo() and getnameinfo(), out-of-band data, and signal driven I/O. It describes common socket options, their uses, and functions for getting and setting option values. It also summarizes POSIX replacement functions for hostname lookups and discusses how out-of-band data can be used to send high priority messages and when SIGIO signals may be generated.