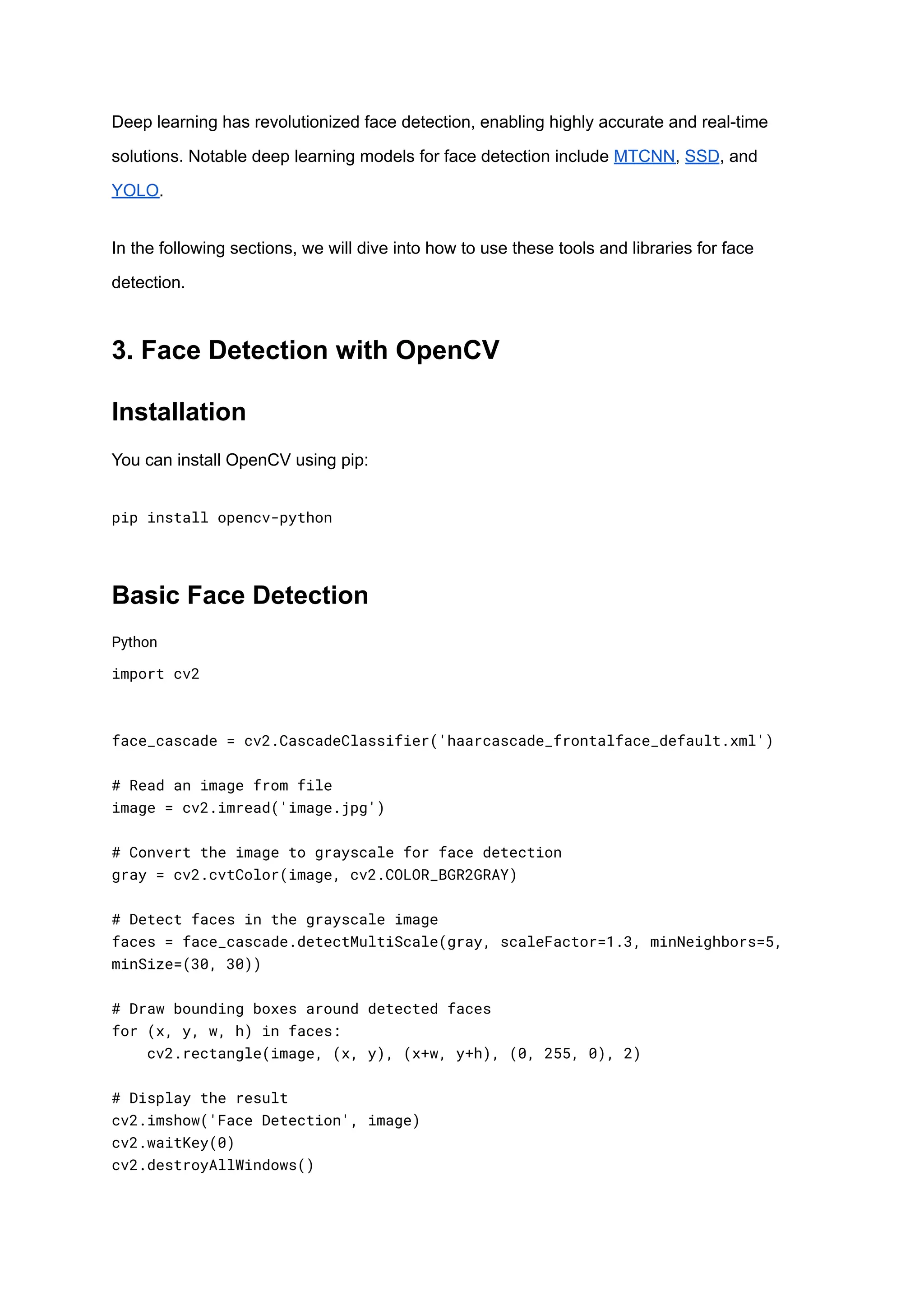
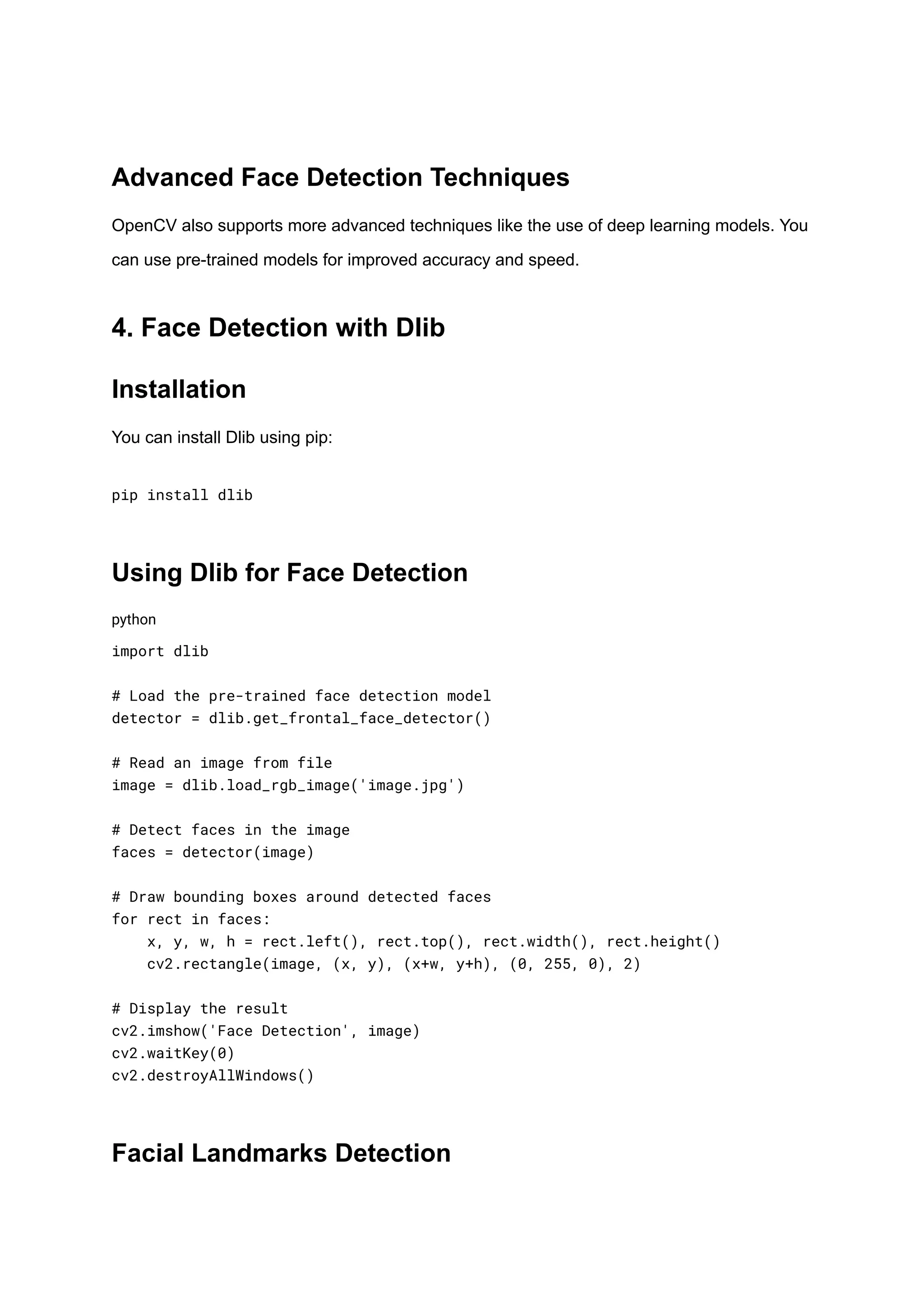
This guide provides an overview of face detection in Python, exploring various tools and libraries such as OpenCV, dlib, and deep learning approaches like MTCNN, SSD, and YOLO. It discusses the importance of face detection in applications ranging from security to healthcare, and offers insights on choosing the right methodologies based on accuracy, speed, and resource requirements. The document also includes practical steps for implementing face detection techniques, enhancing detection outcomes, and a look at future developments in the field.