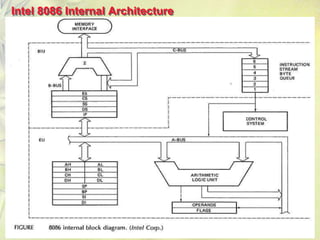
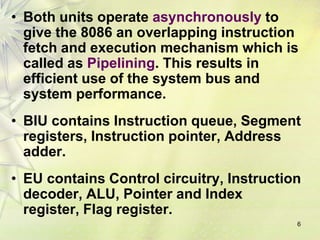
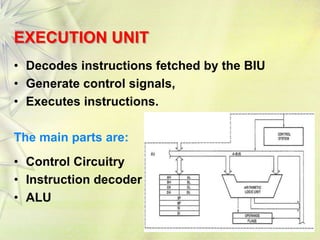
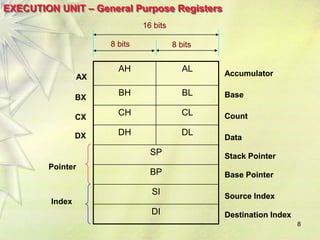
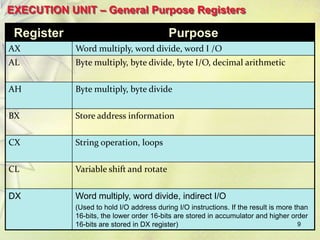
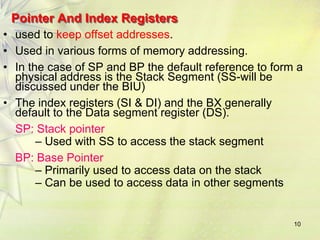
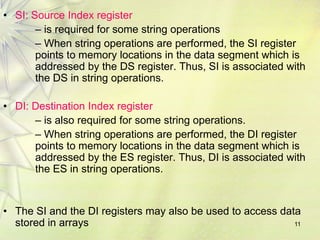
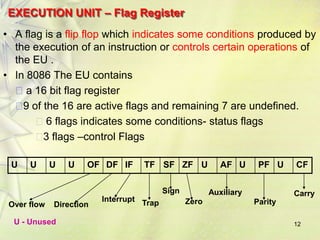
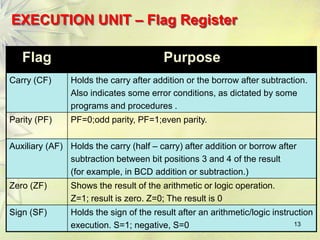
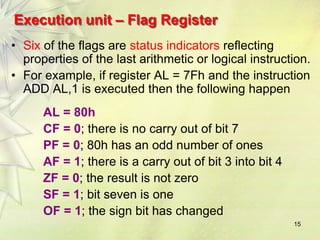
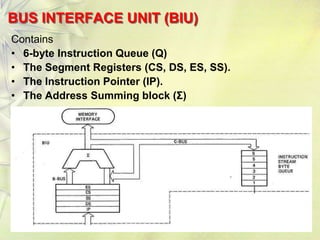
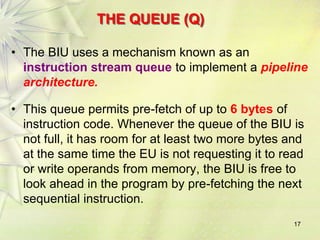
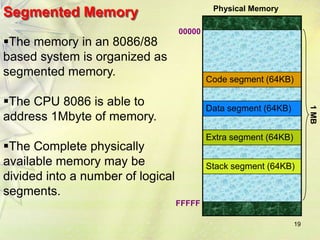
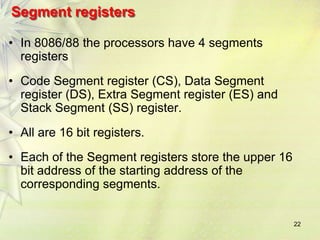
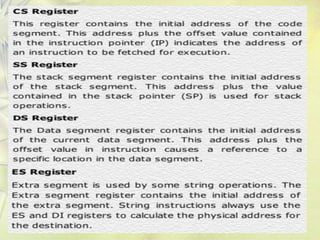
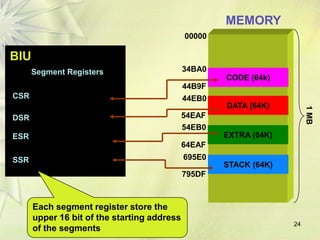
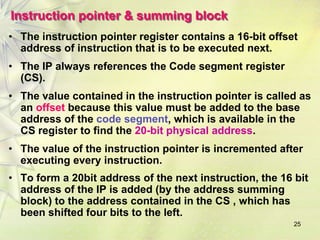
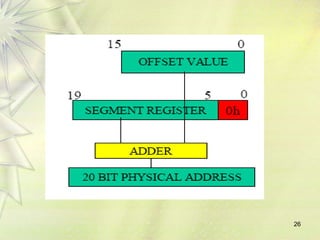
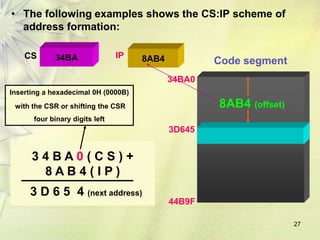
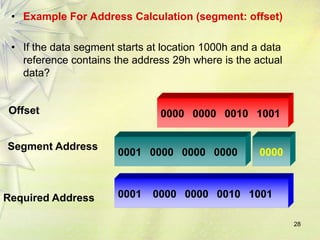
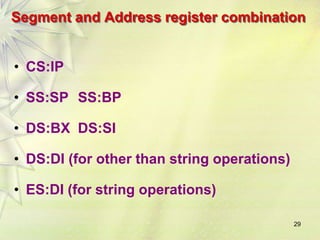
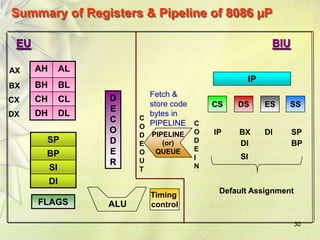
The Intel 8086 is a 16-bit microprocessor that can access up to 1 MB of memory. It has a 20-bit address bus and supports 64K I/O ports. The 8086 uses a pipeline architecture with an Execution Unit that decodes and executes instructions, and a Bus Interface Unit that handles memory access and address calculation. The 8086's registers include general-purpose registers like AX, BX, CX and DX, as well as segment registers and flags that provide status information.