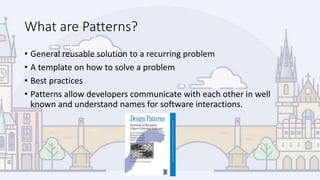
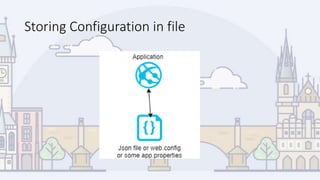
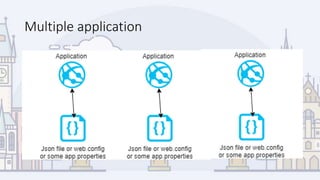
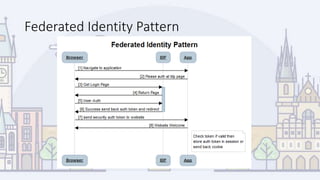
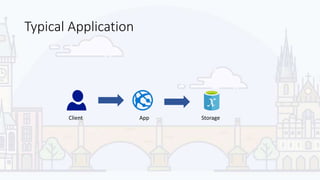
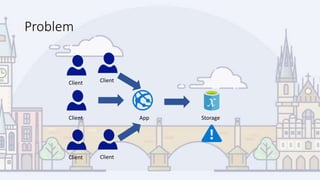
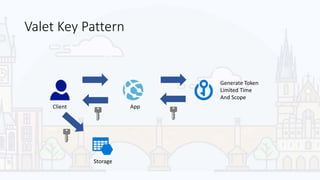
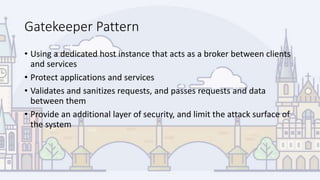
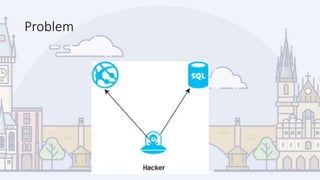
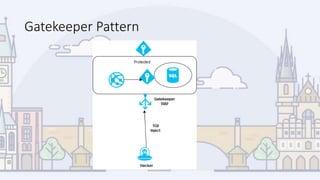
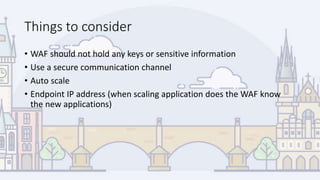
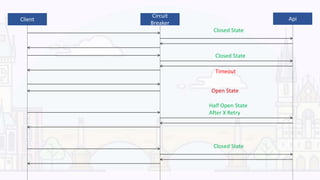
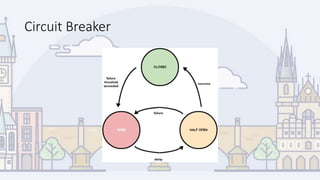
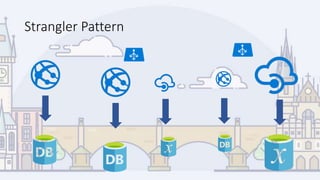
This document discusses 8 cloud design patterns: External Configuration, Cache Aside, Federated Identity, Valet Key, Gatekeeper, Circuit Breaker, Retry, and Strangler. It provides an overview of each pattern, including what problem it addresses, when to use it, considerations, and examples of cloud offerings that implement each pattern. It aims to help developers understand and apply common best practices for cloud application design.