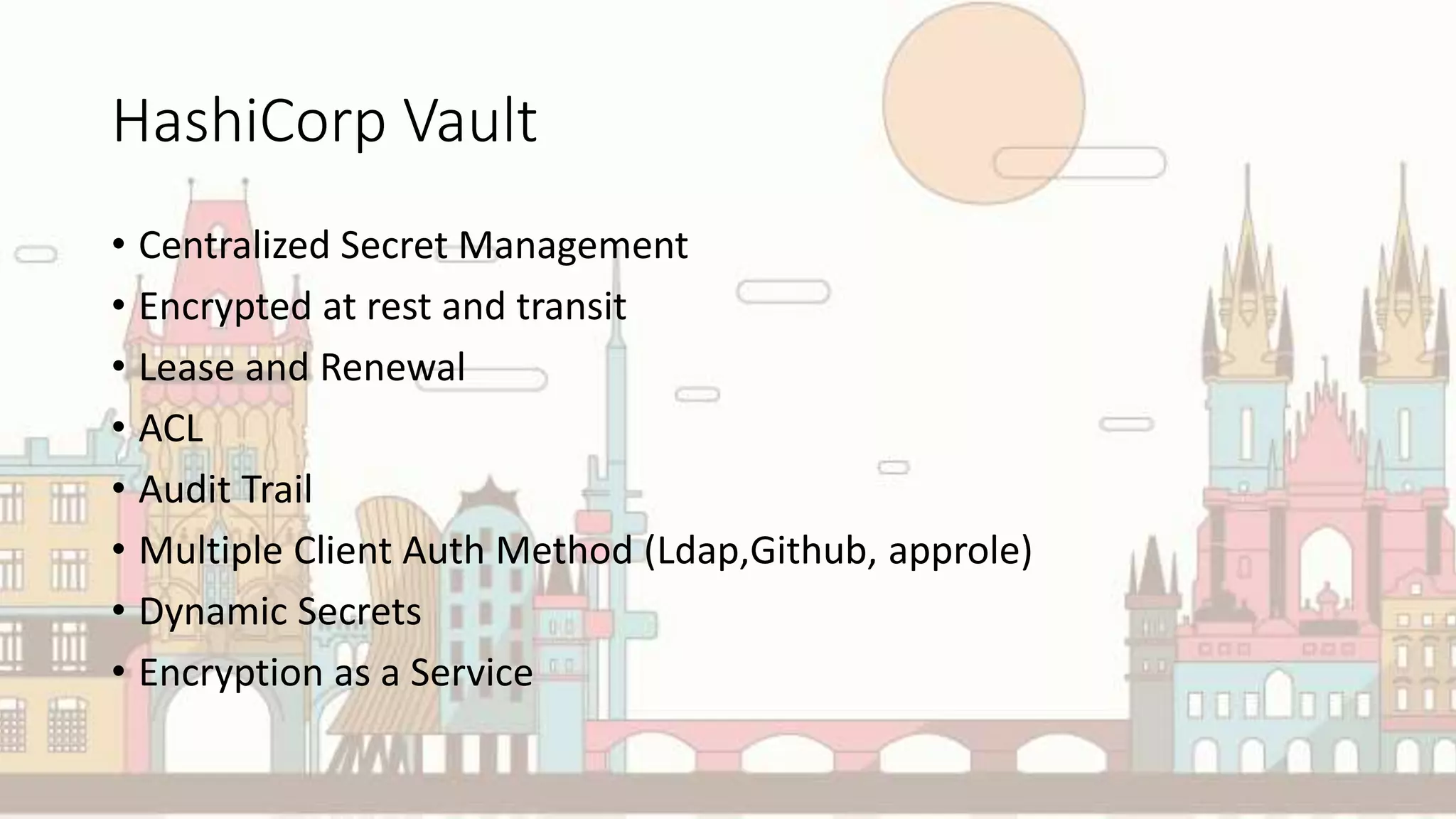
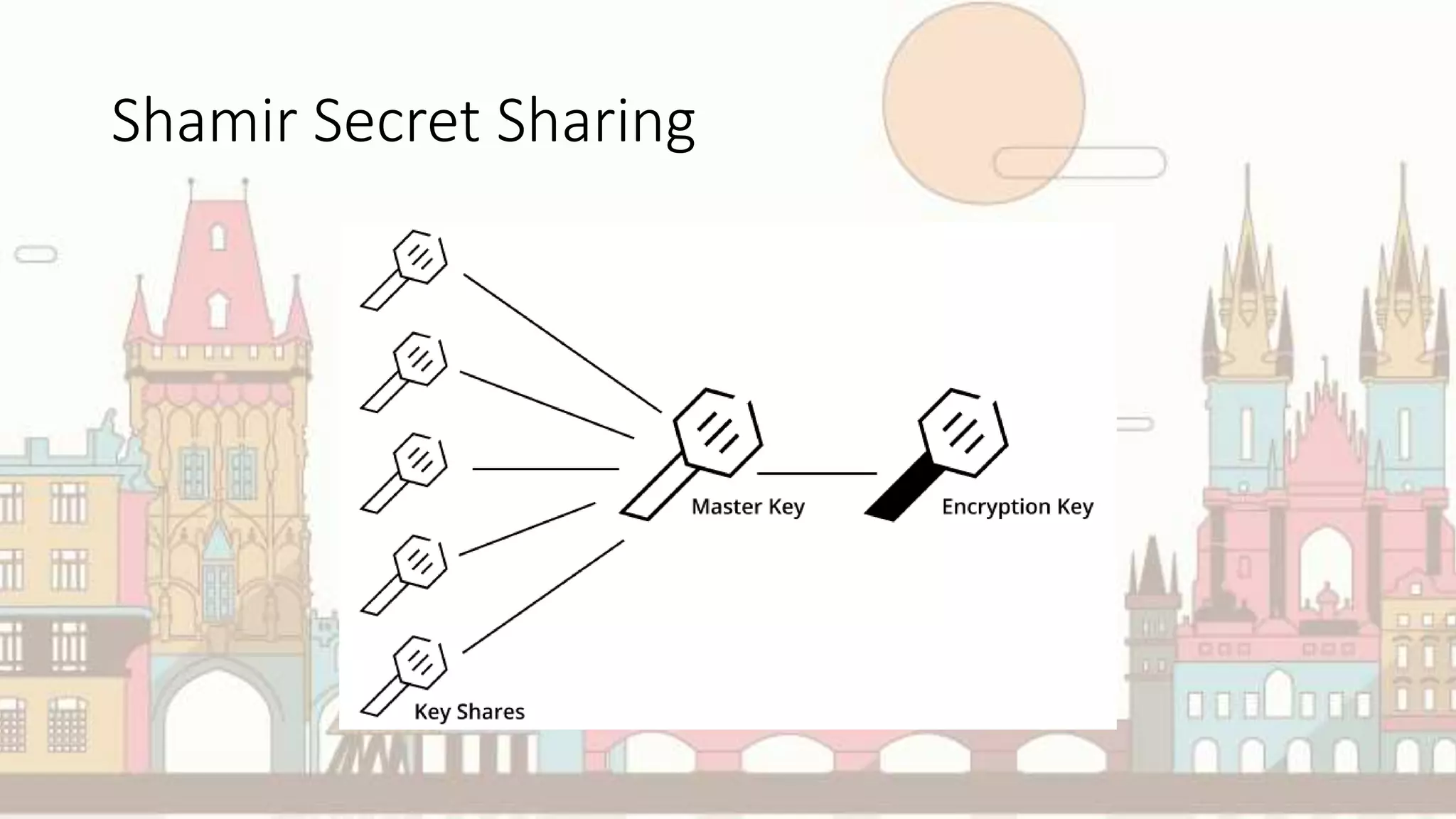
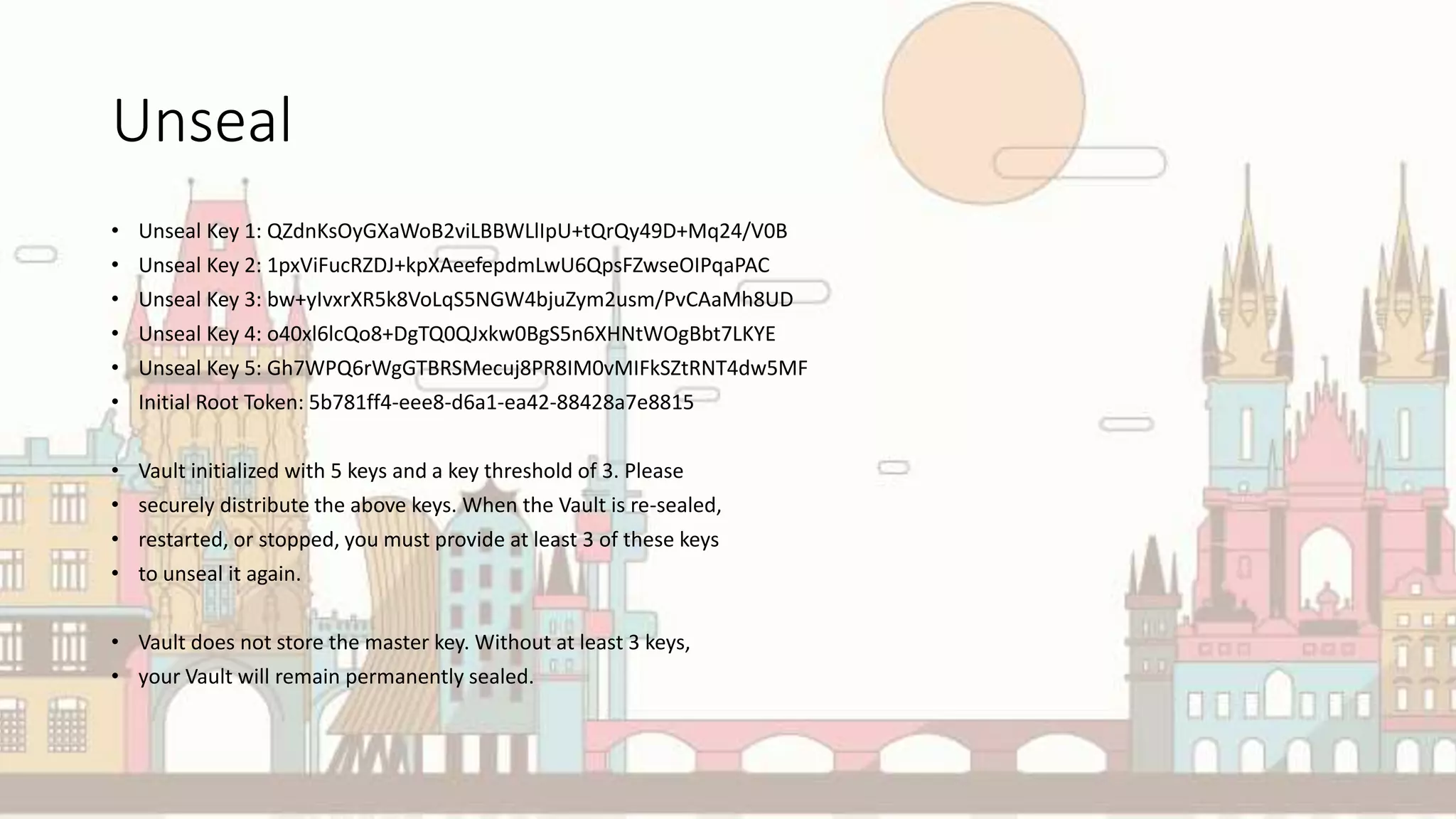
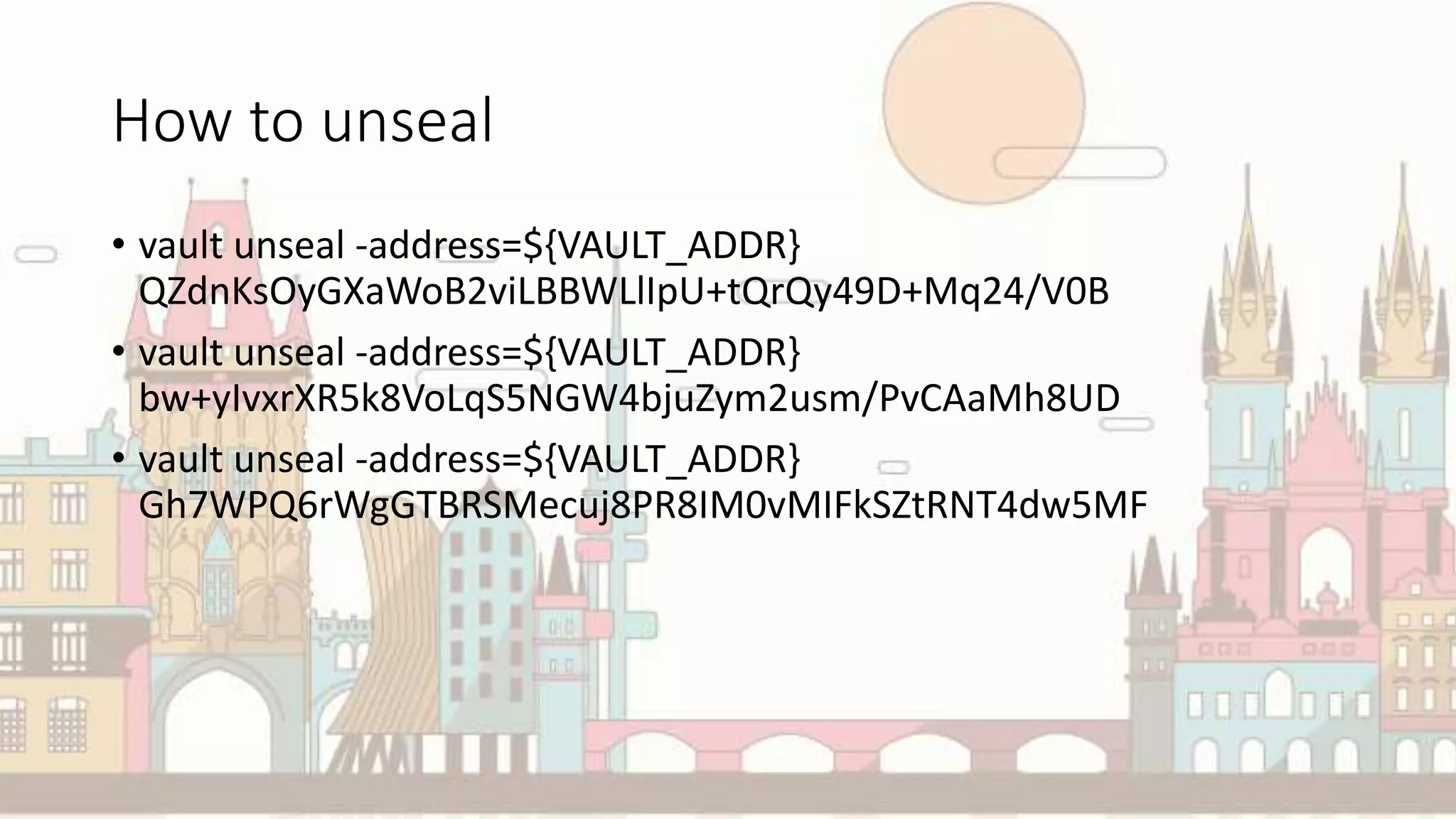
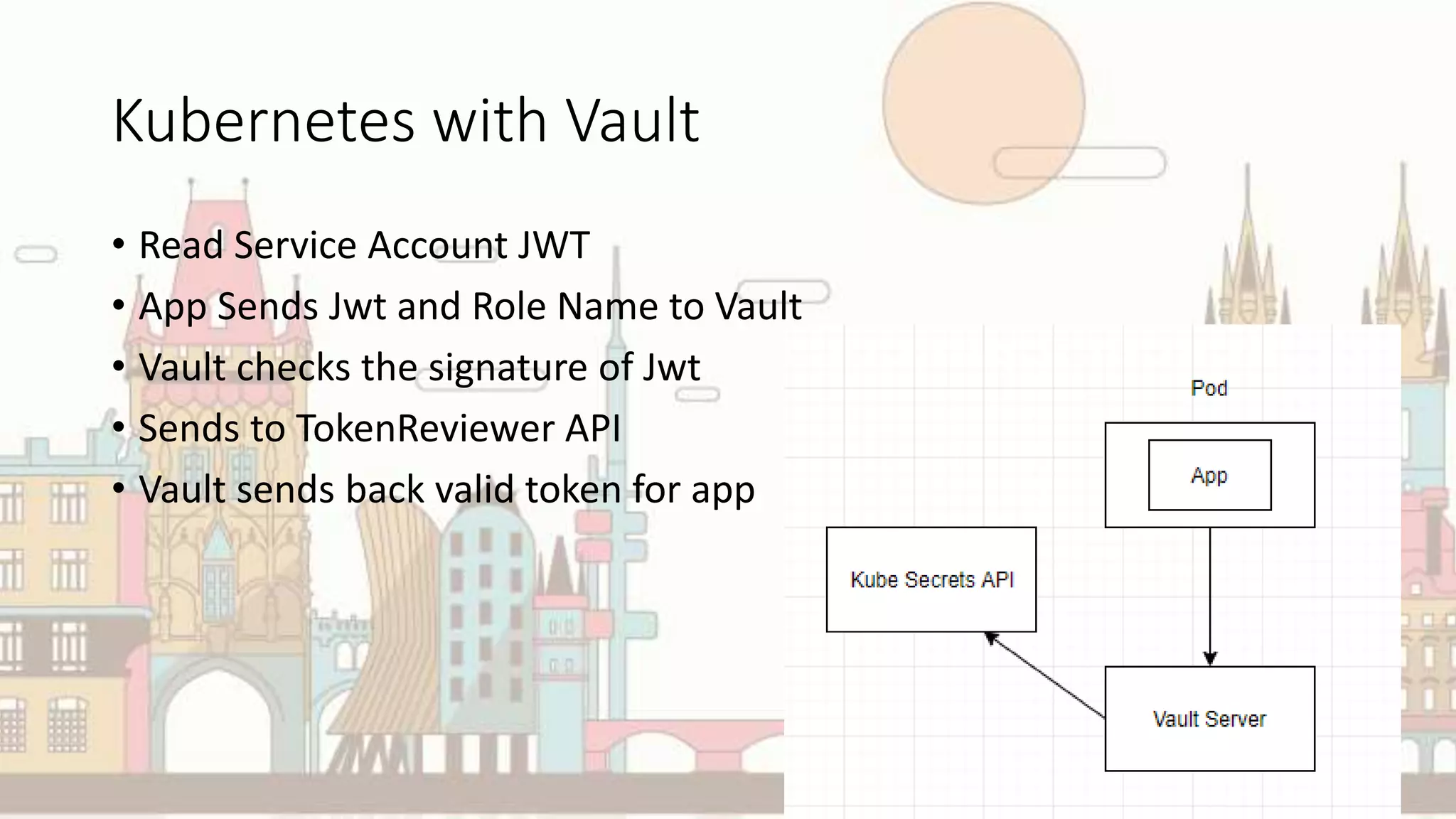
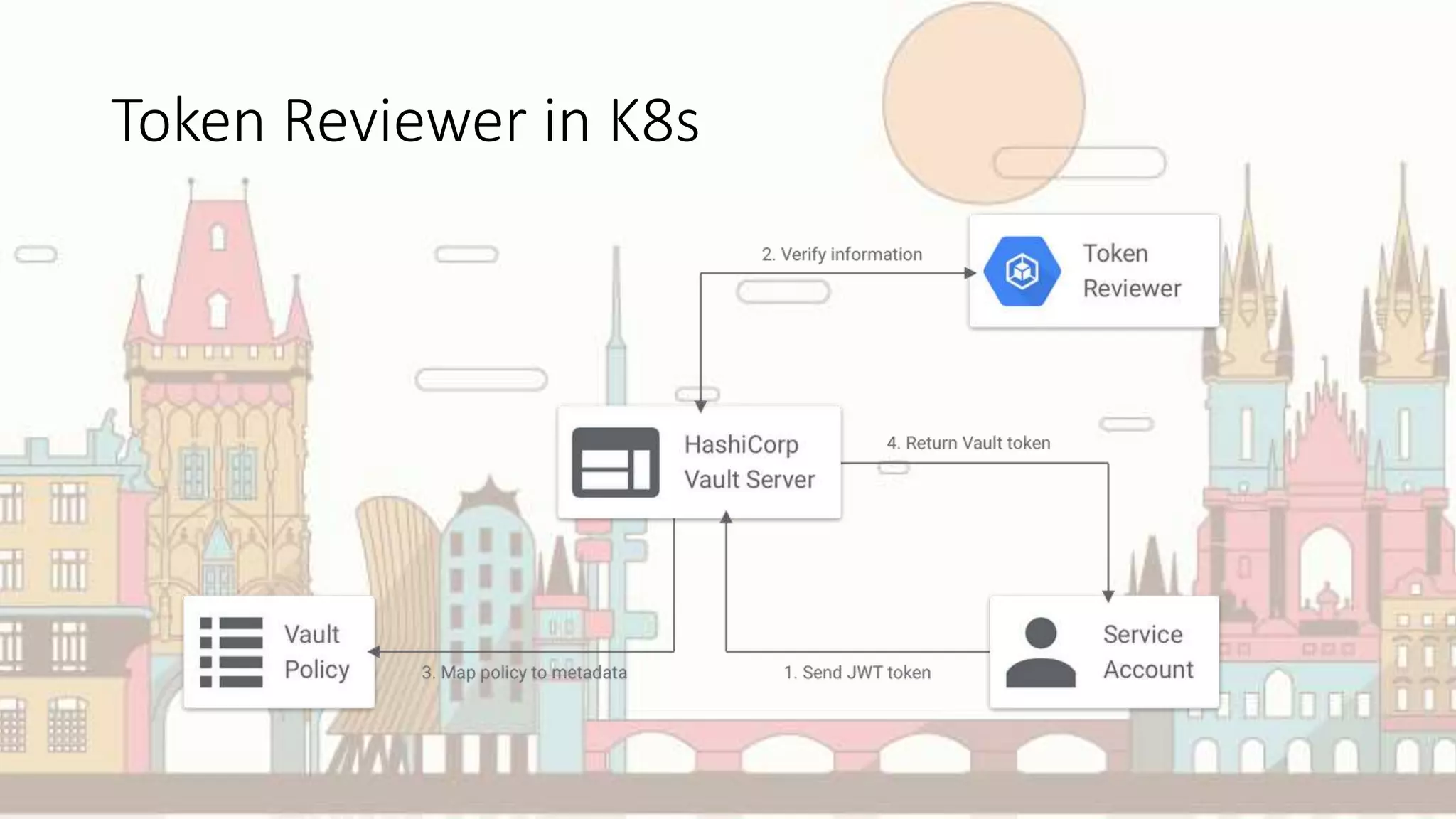
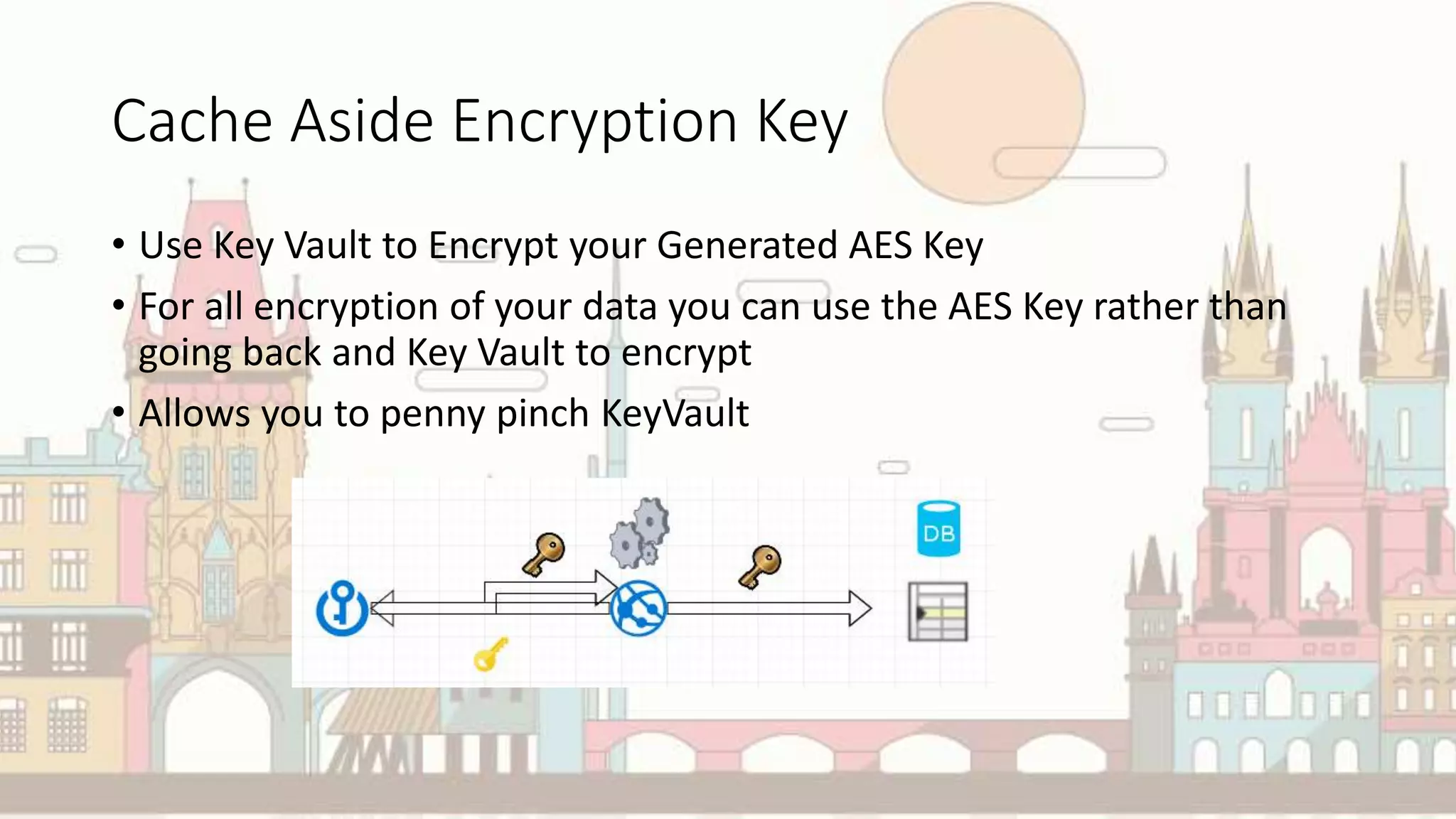
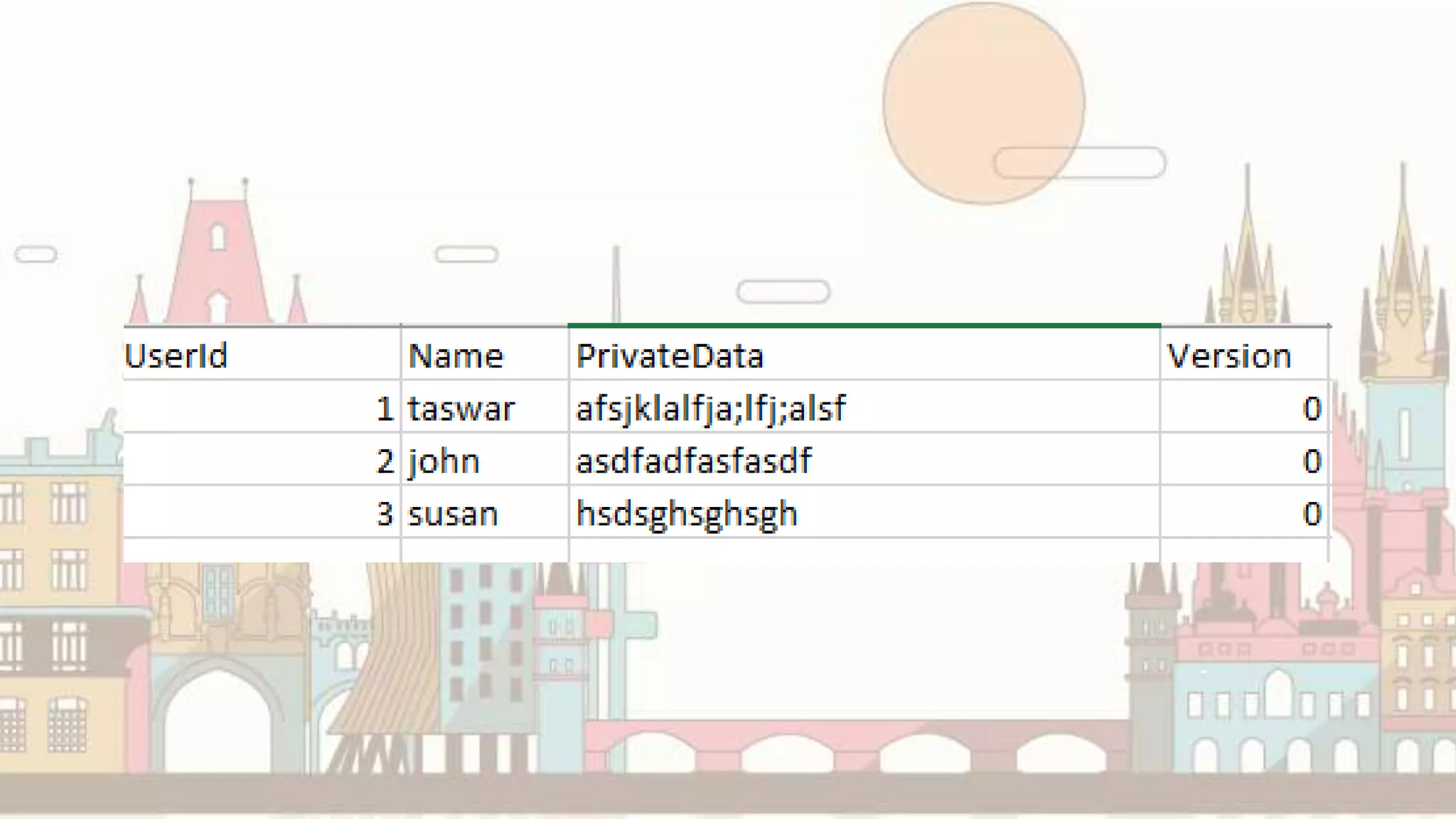
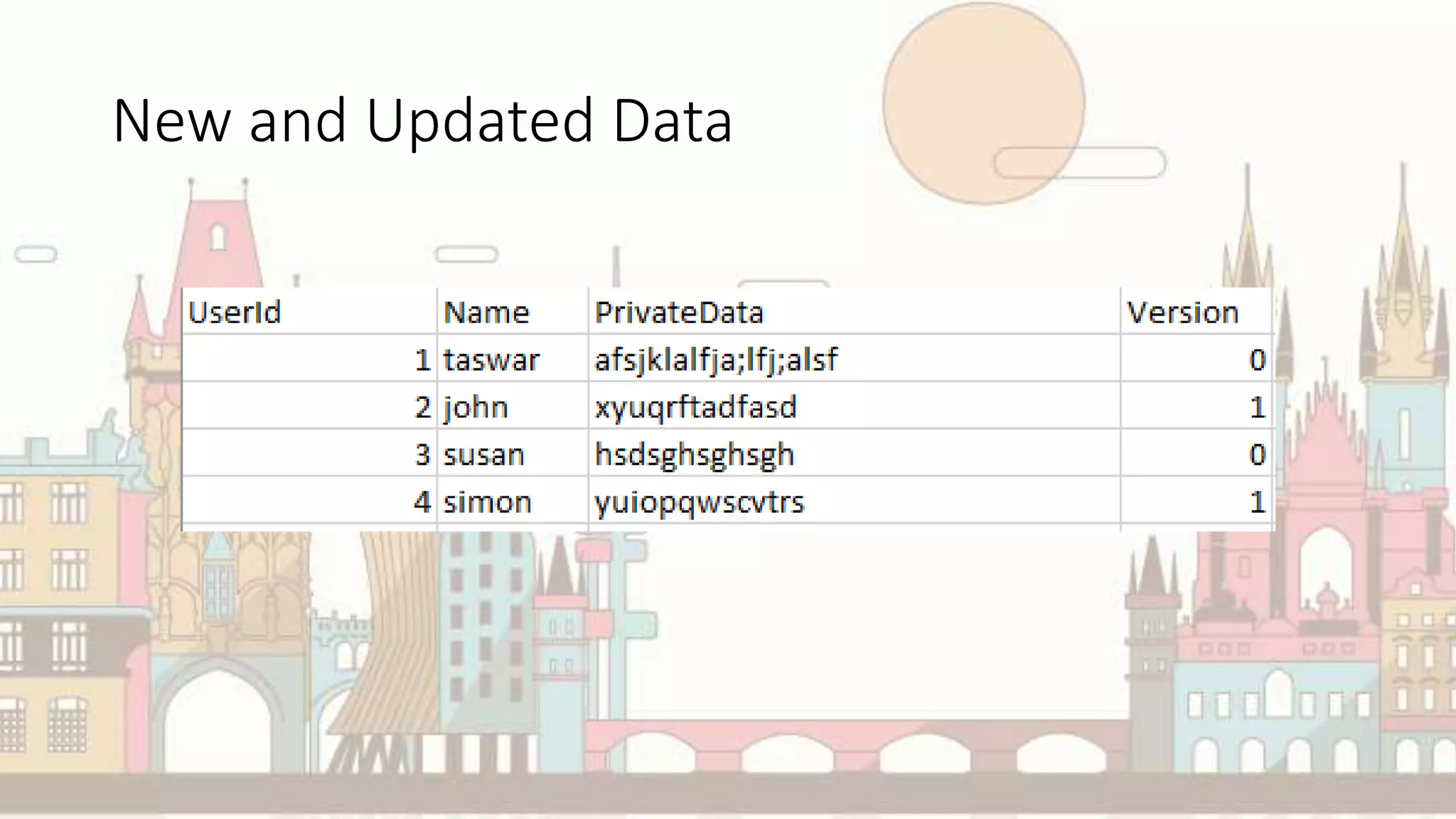
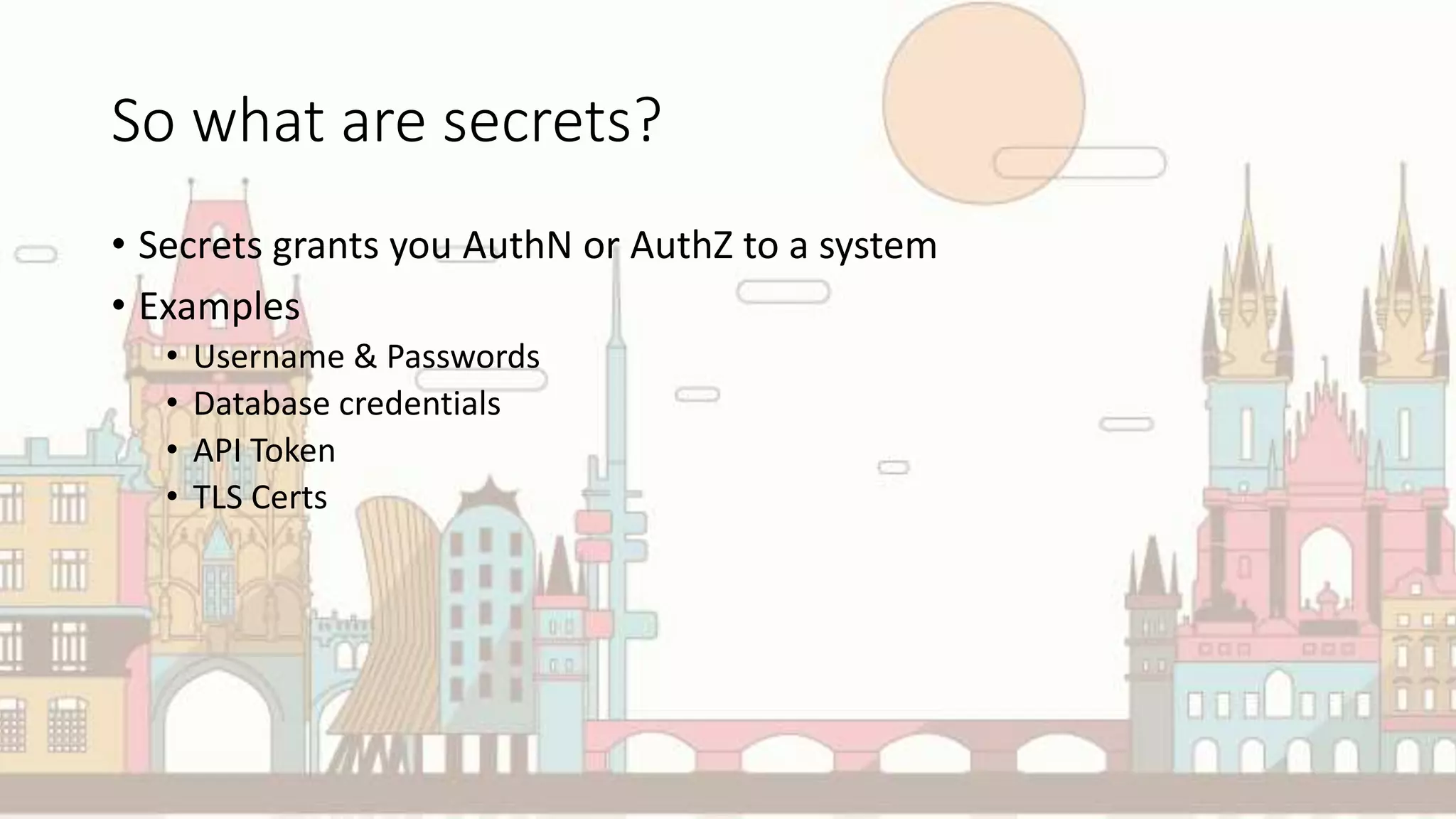
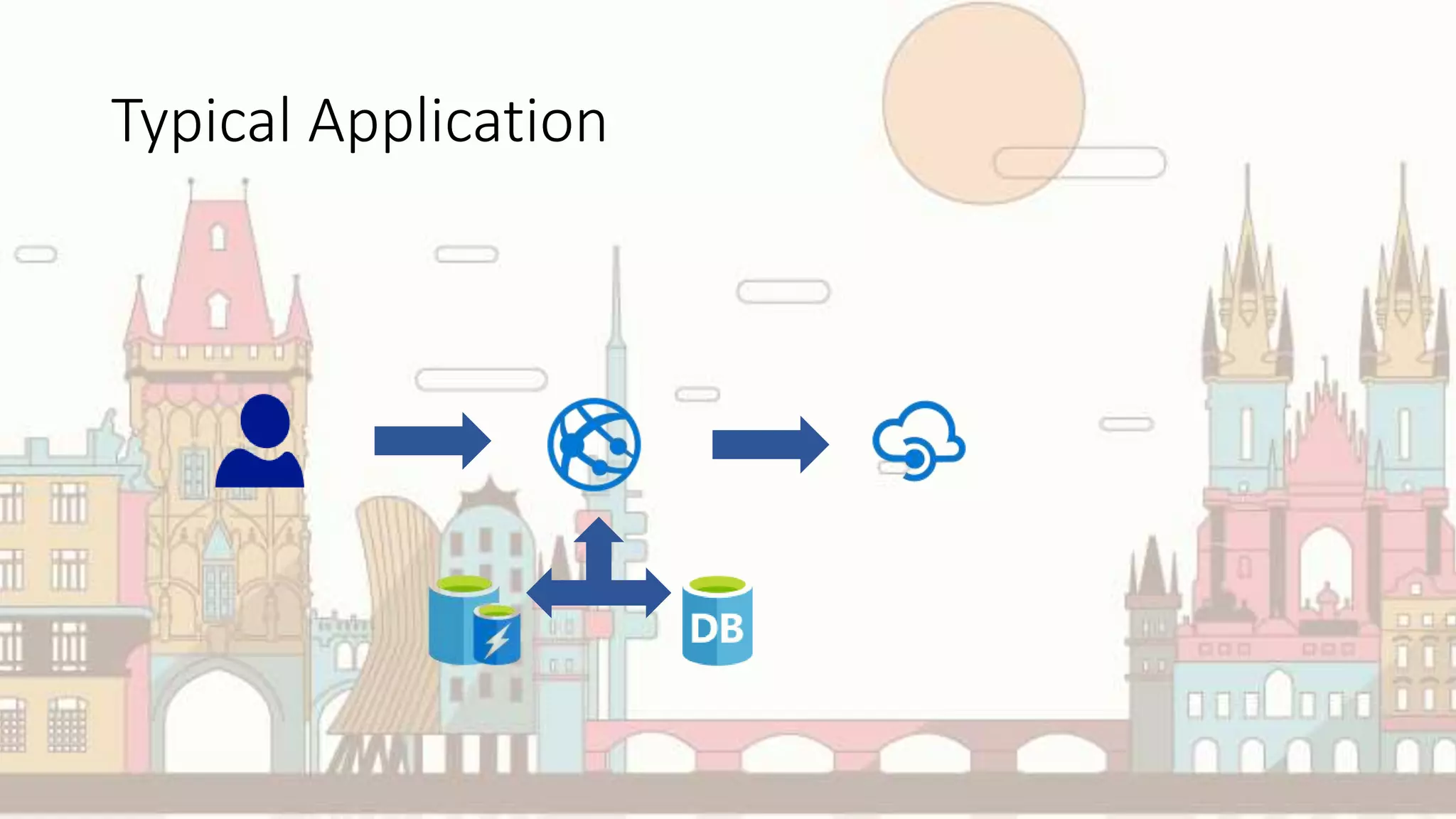
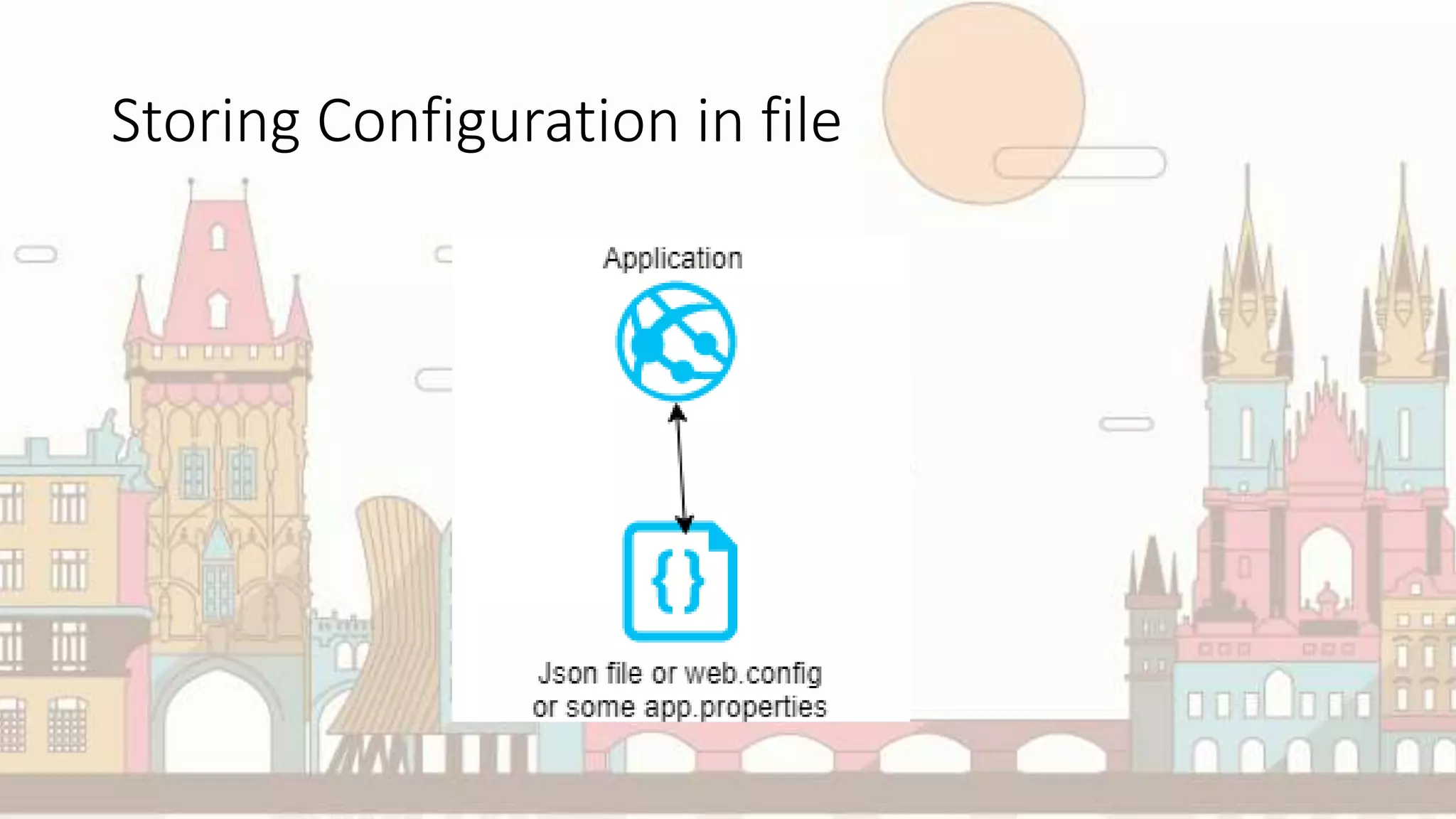
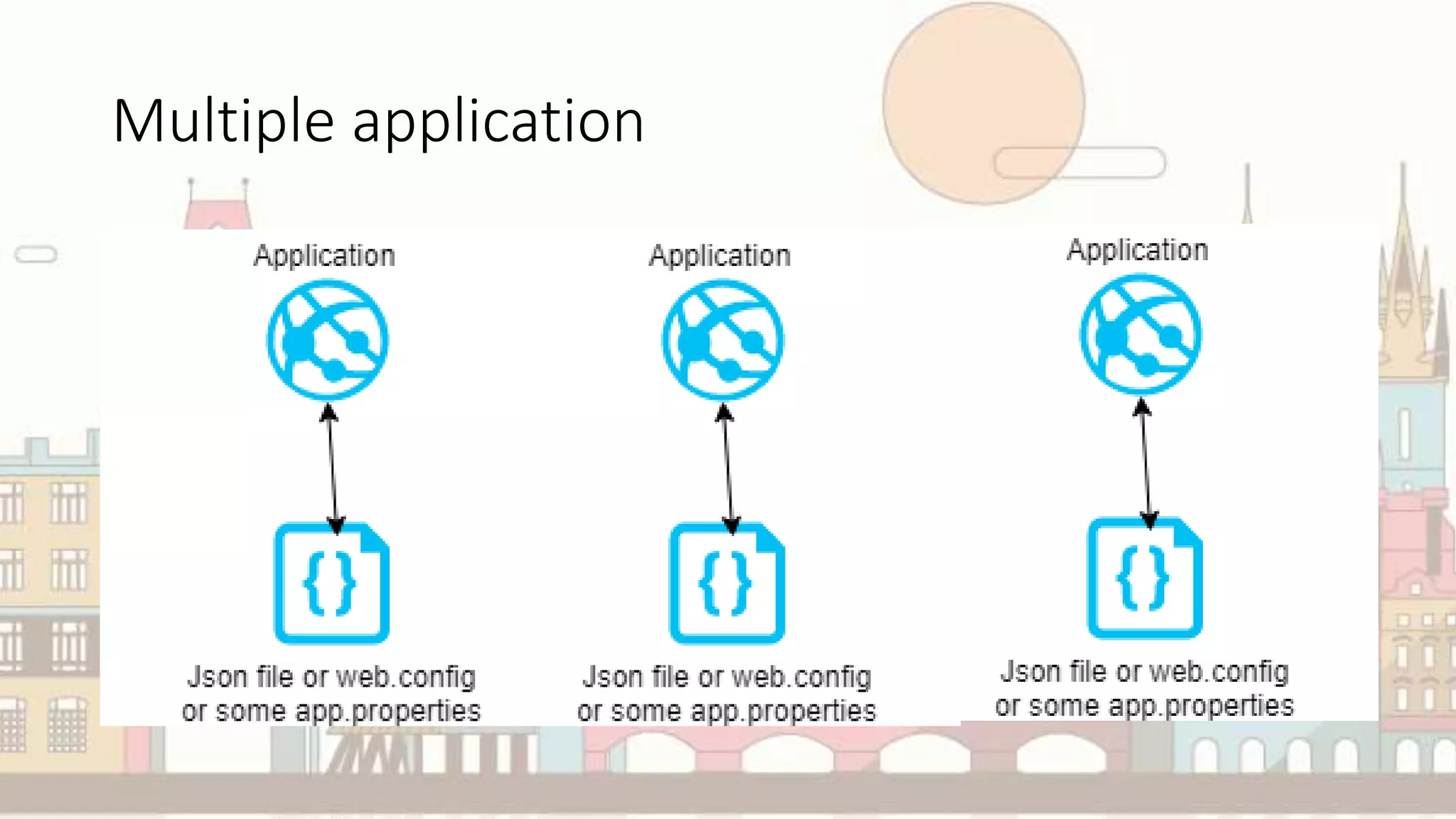
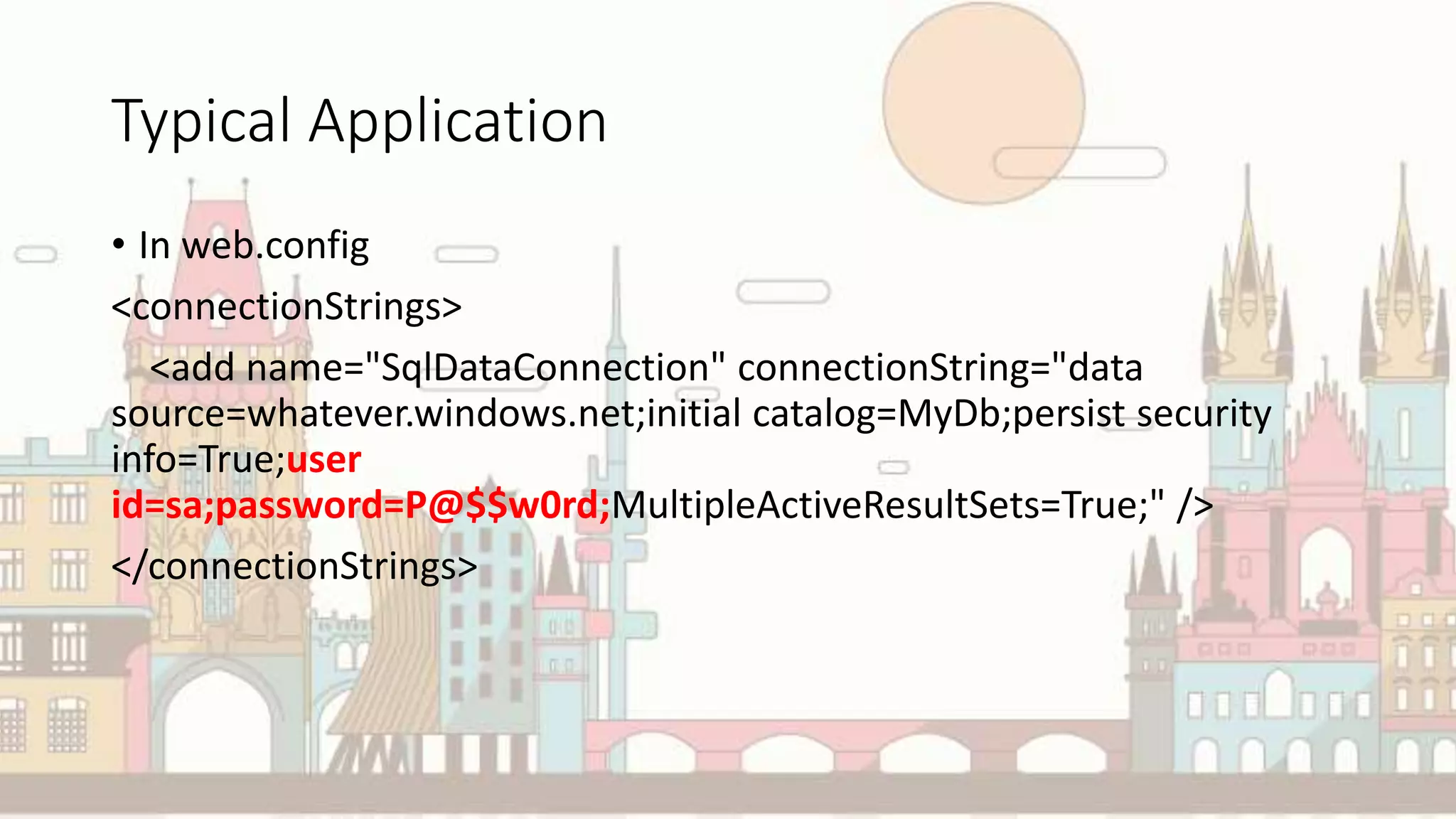
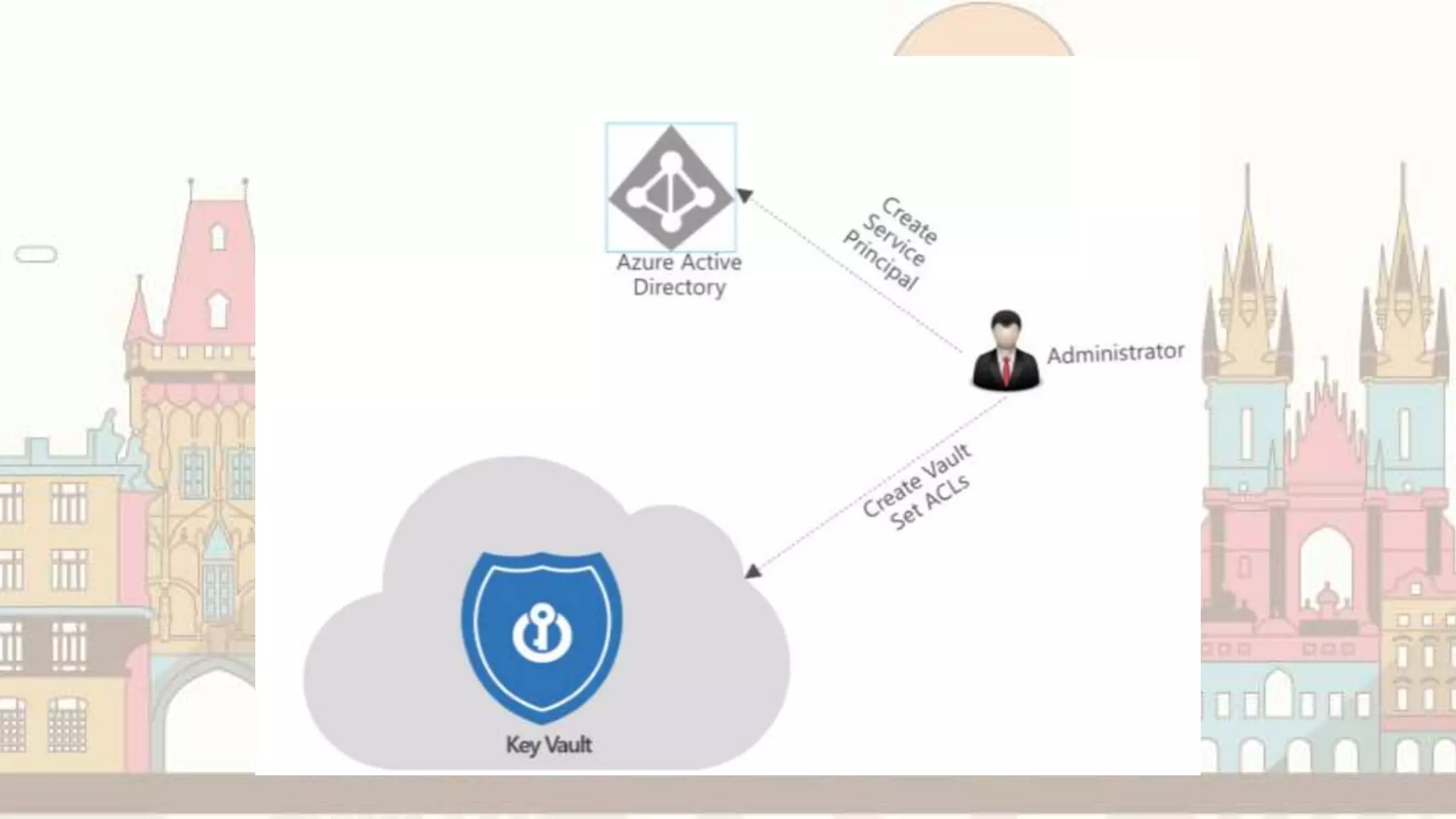
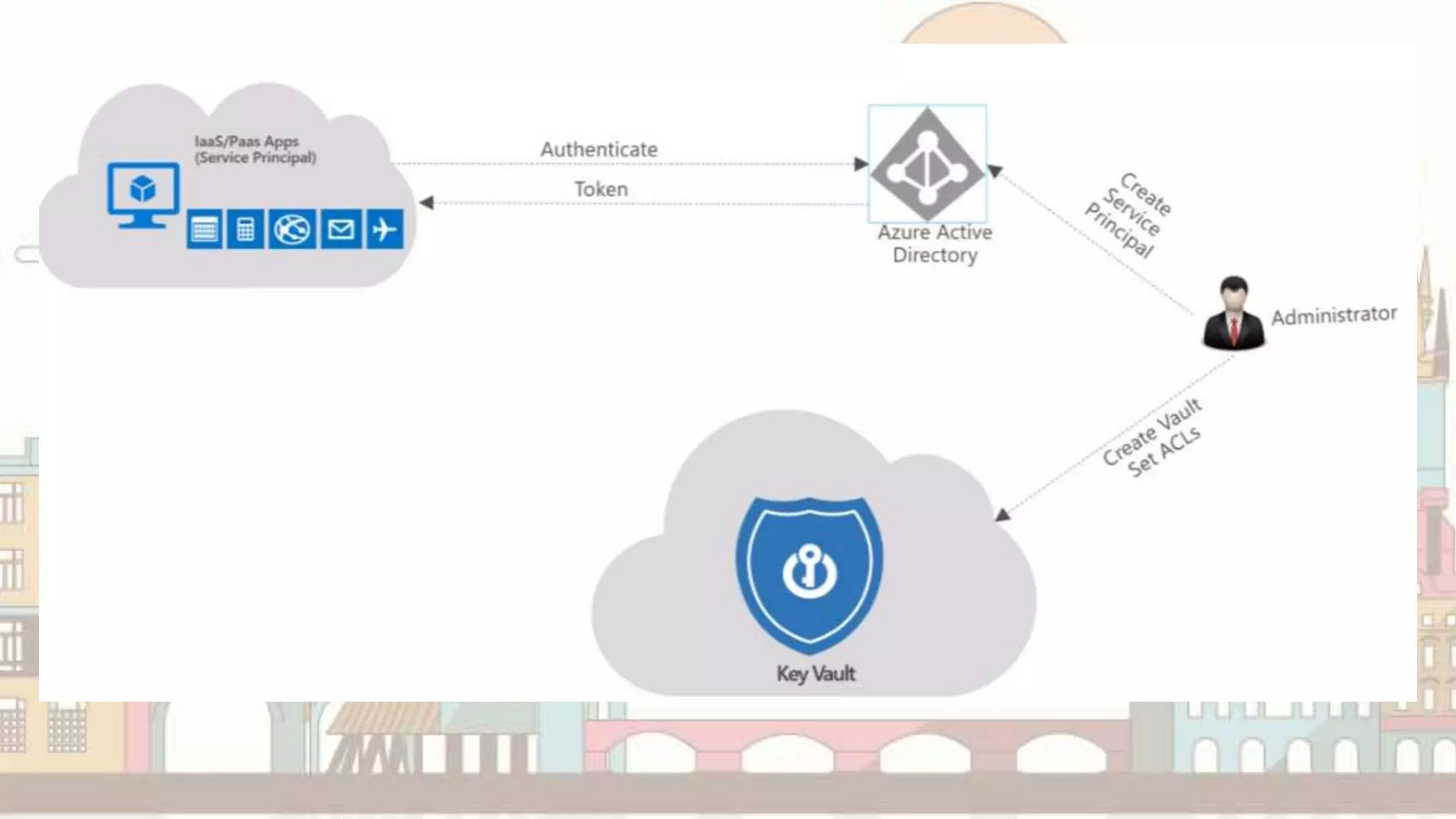
The document discusses managing secrets in cloud environments, focusing on Azure Key Vault and Hashicorp Vault for secure storage, access control, and encryption of sensitive information like passwords, API tokens, and SSL certificates. It highlights the issues with secret management in applications, such as secret sprawl and access challenges, and introduces best practices for using these vault technologies effectively. Additionally, the document features a demo, comparisons between vault solutions, and strategies for integration with systems like Docker and Kubernetes.












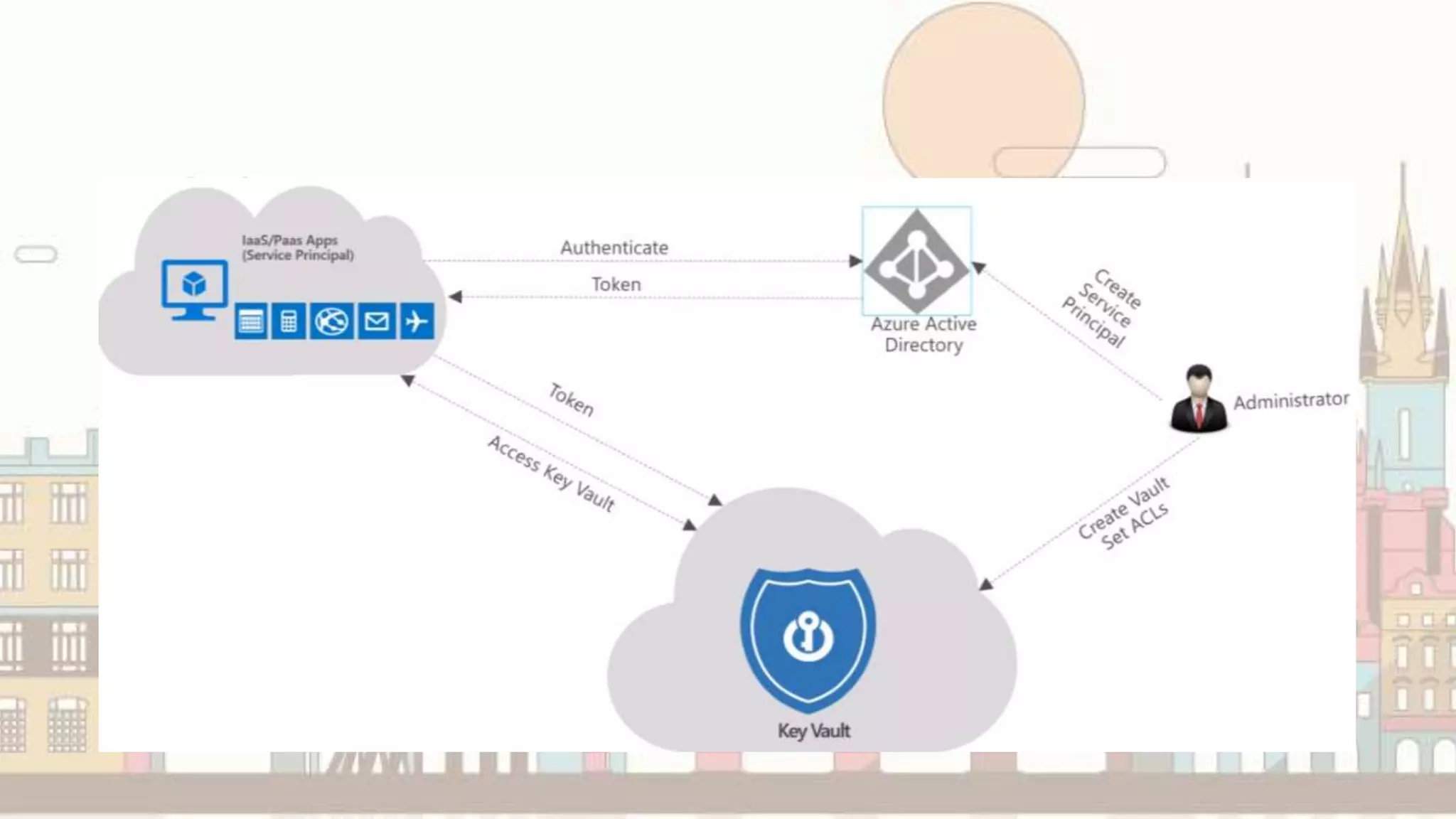

![Code that looks like this
ClientCredential clientCred = new ClientCredential(
WebConfigurationManager.AppSettings["ClientId"],
WebConfigurationManager.AppSettings["ClientSecret"]);](https://image.slidesharecdn.com/managingyoursecretsinacloudenvironment-190115183225/75/Managing-your-secrets-in-a-cloud-environment-33-2048.jpg)