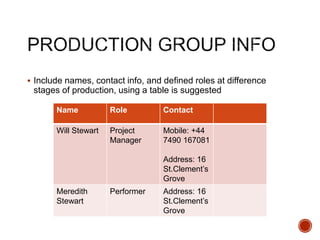
This document provides a template and guidance for planning a film production. It includes sections for visual planning, organizational planning, risk assessment, production scheduling, call sheets, location agreements, and soundtrack planning. Students are instructed to use the template to storyboard their film, create a shot list, outline the crew and roles, secure permissions, and plan the production schedule and risk mitigation. The template is intended to help students comprehensively plan each element of their short film production.

![ This template PowerPoint presentation includes all the relevant
elements you need to cover your film production.
It is suggested you save this PP in a different name so you
always have a copy – some sections require you to delete the
information on the slide and replace with your own work
Add more pages to each section where necessary [you should be
doing this!]
Add visuals as you see necessary
This document will be added to as you progress through the pre-
production phase.
Remember, you need to give as much attention to your
sound planning as you do to your visual planning](https://image.slidesharecdn.com/4-180410083018/85/4-pre-production-sf-2017-2-320.jpg)
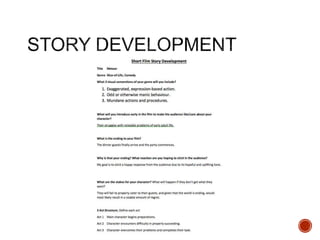
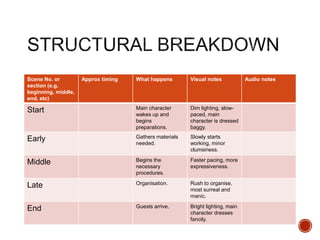
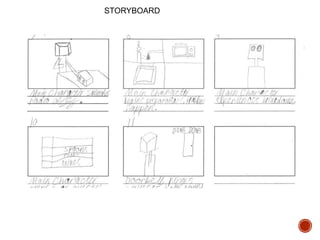
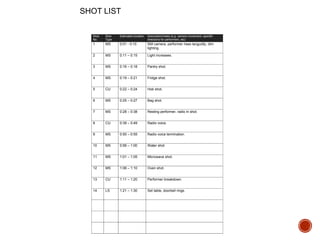
![ Breakdown your film into it’s basic sections [e.g. via scene
breakdown or similar] and apply broad visual ideas to each
section. You should list the shots required
You can use this as the master template for your production, then
add more shots to each section when you develop your full visual
plan
From this you could work on a conventional script if you want, but
using the scene breakdowns should be enough](https://image.slidesharecdn.com/4-180410083018/85/4-pre-production-sf-2017-6-320.jpg)