Embed presentation
Downloaded 11 times



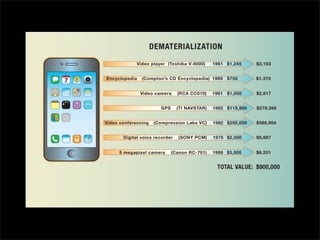




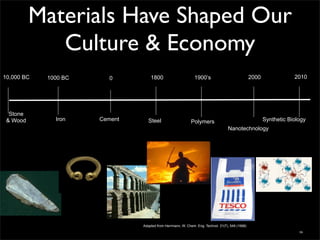
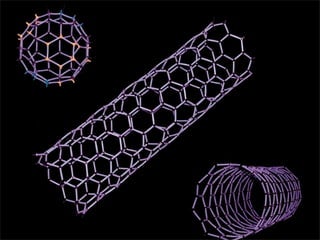


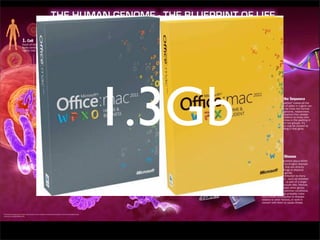
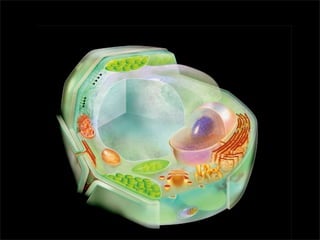
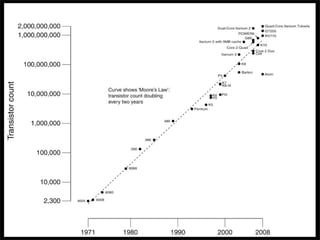






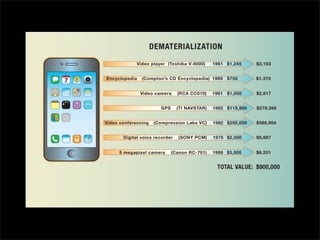
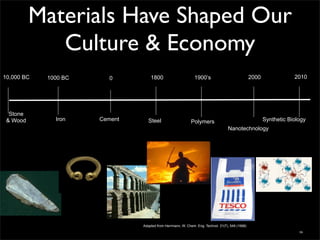
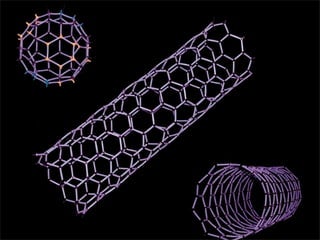
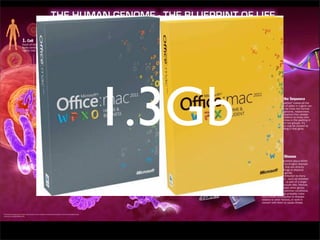
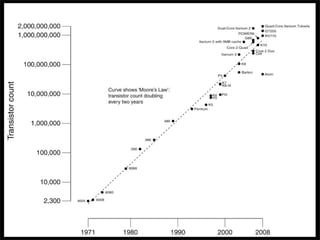
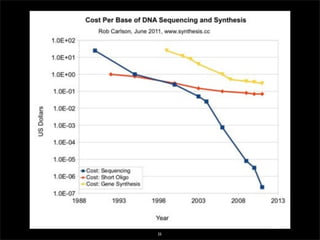
The document discusses the implications of 21st-century innovations on societal and economic structures, emphasizing the importance of digitization and maintaining a focus on sustainable technology to support growing populations. It references historical material advancements and suggests a future-oriented approach that transcends simple improvements in technology. Ultimately, it calls for responsible use of existing tools to address global challenges.