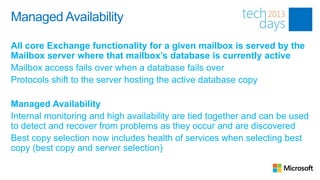
1. Exchange Server 2013 improves mailbox server availability by consolidating previously separate roles onto single mailbox servers and replicating mailbox databases across multiple servers in a database availability group (DAG).
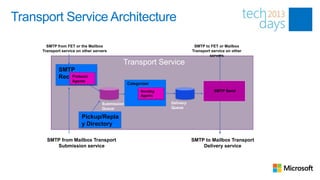
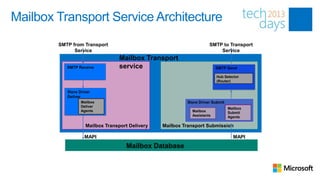
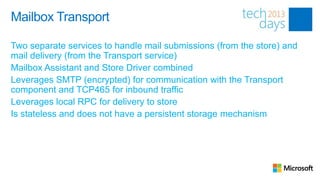
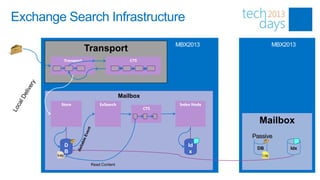
2. The mailbox transport service was redesigned with separate submission and delivery components to improve mail flow, and transport is now located on mailbox servers rather than front-end servers.
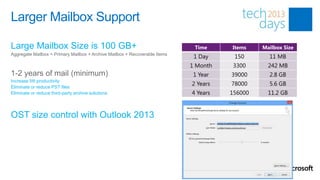
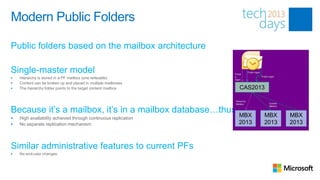
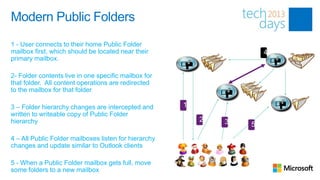
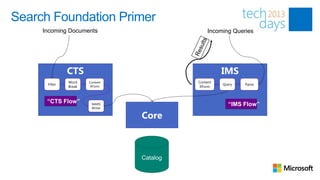
3. Exchange 2013 provides increased mailbox sizes up to 100GB, modernized public folders based on the mailbox model, and improved search capabilities with a new search foundation.

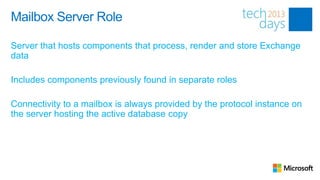




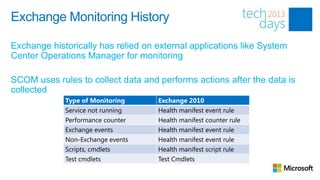





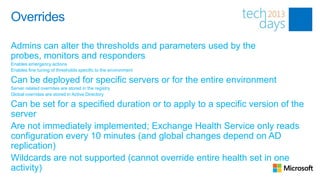
![Overrides
See what overrides have been set
Get-ServerMonitoringOverride –Server <Server>
Get-GlobalMonitoringOverride
Create an override
Add-ServerMonitoringOverride <HealthSet><Name> -Server <Server> -ItemType <Monitor,Probe,Responder> [-
Duration <Time> -ApplyVersion <Version>] -PropertyName <Property> -PropertyValue <Value>
Add-GlobalMonitoringOverride <HealthSet><Name> -ItemType <Monitor,Probe,Responder> [-Duration <Time> -
ApplyVersion <Version>] -PropertyName <Property> -PropertyValue <Value>
Remove Override
Remove-ServerMonitoringOverride
Remove-GlobalMonitoringOverride](https://image.slidesharecdn.com/02itproroom3deepdiveexchangeserverschottschnoll28-130312080426-phpapp02/85/Exchange-Server-2013-Architecture-Deep-Dive-Part-2-45-320.jpg)