The document discusses combinational logic circuits and Boolean algebra. It contains 17 questions covering topics such as:
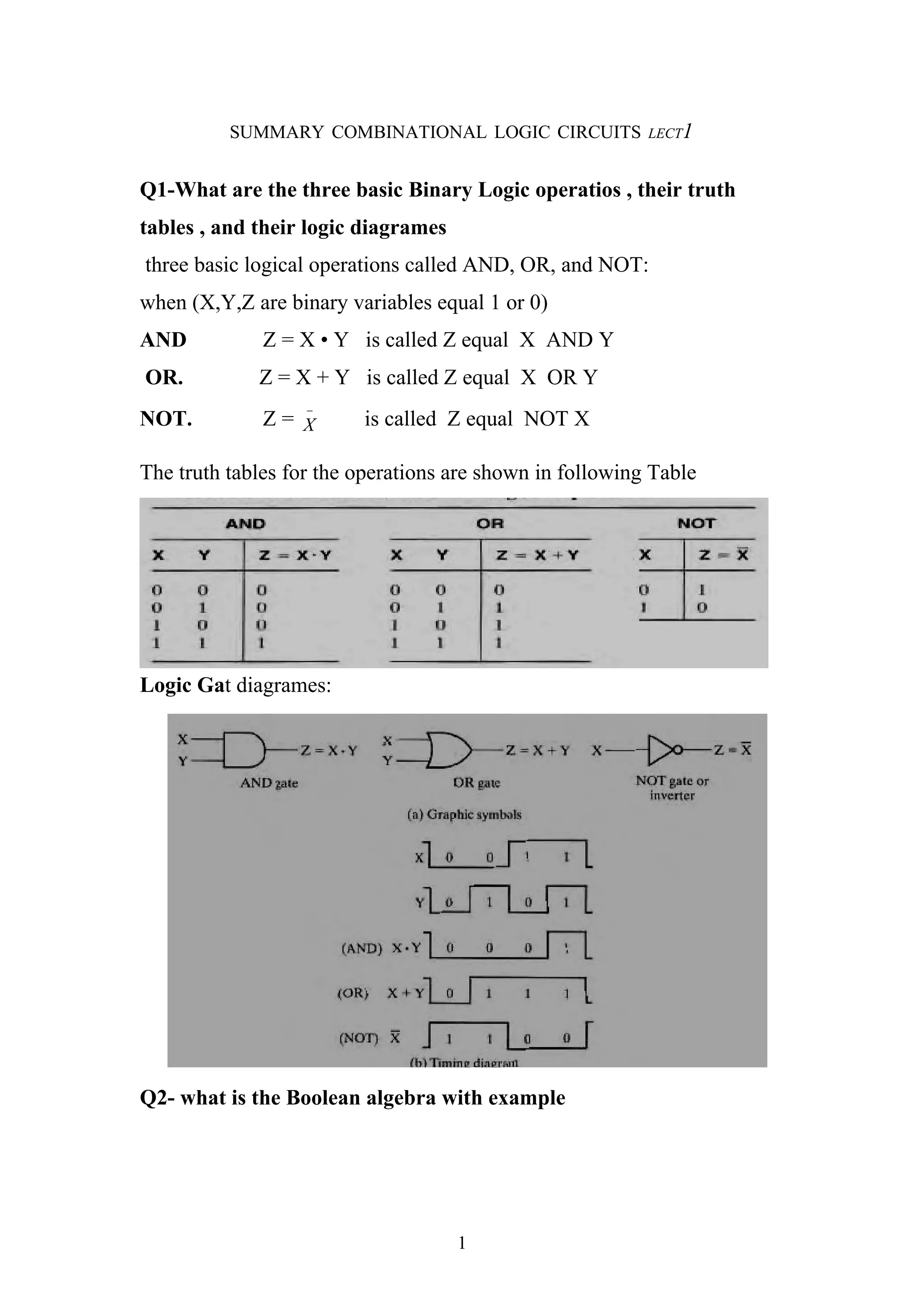
1. The three basic logic operations - AND, OR, NOT - and their truth tables and logic diagrams.
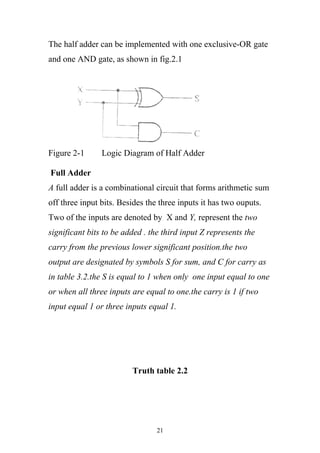
2. Boolean algebra, functions, truth tables, and logic diagrams.
3. Identities of Boolean algebra, dual expressions, and the consensus theorem.
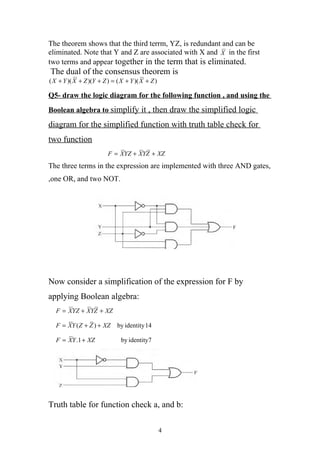
4. Minimizing logic functions using Boolean algebra identities and Karnaugh maps.
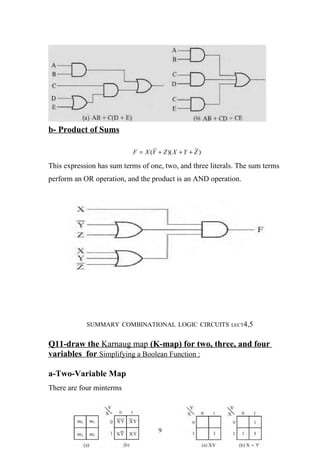
5. Minterms, maxterms, and representing logic functions with sums of products and products of sums.
6. Demorgan's theorem and complementing logic functions.
7. Simplifying logic functions through