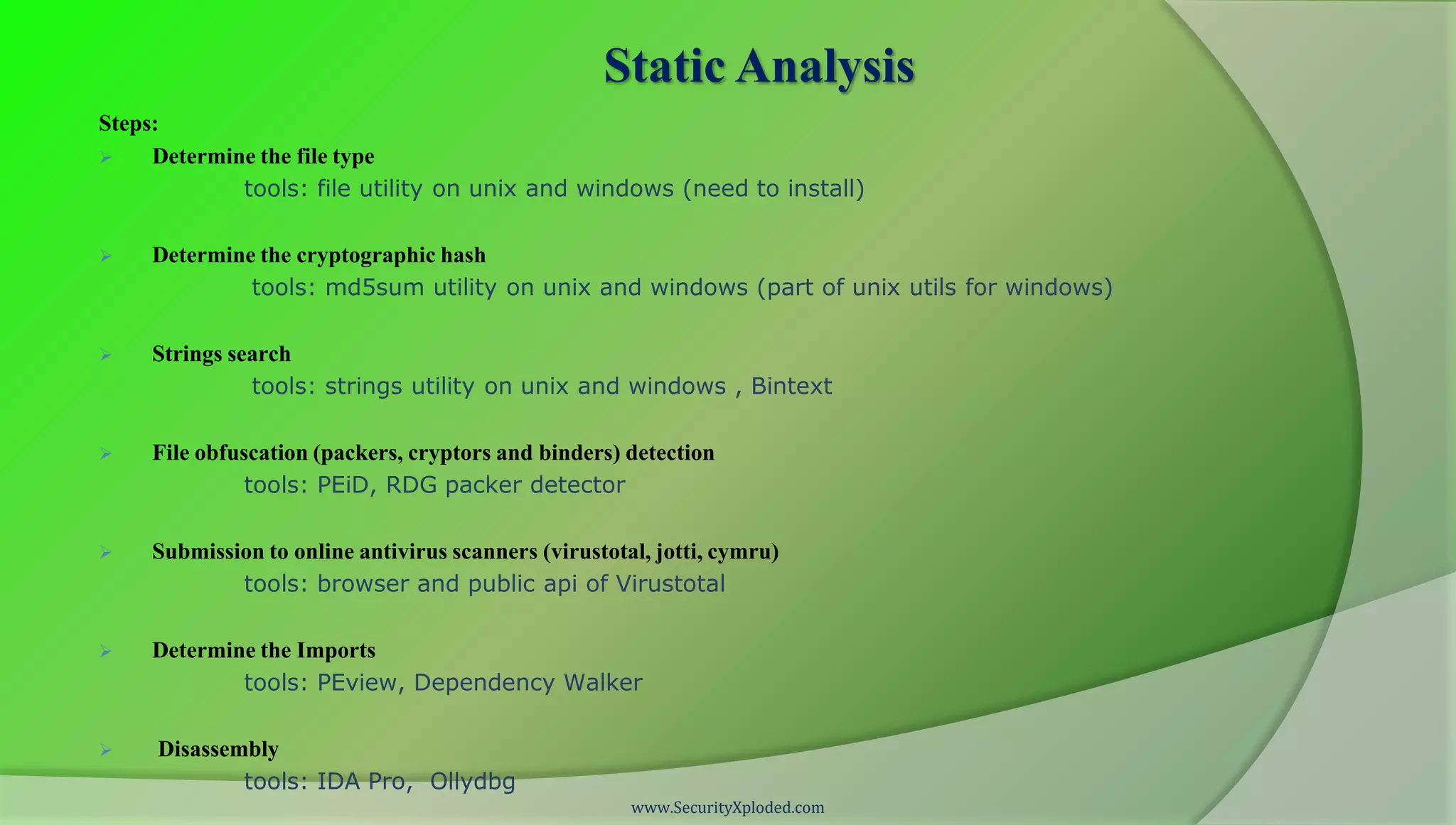
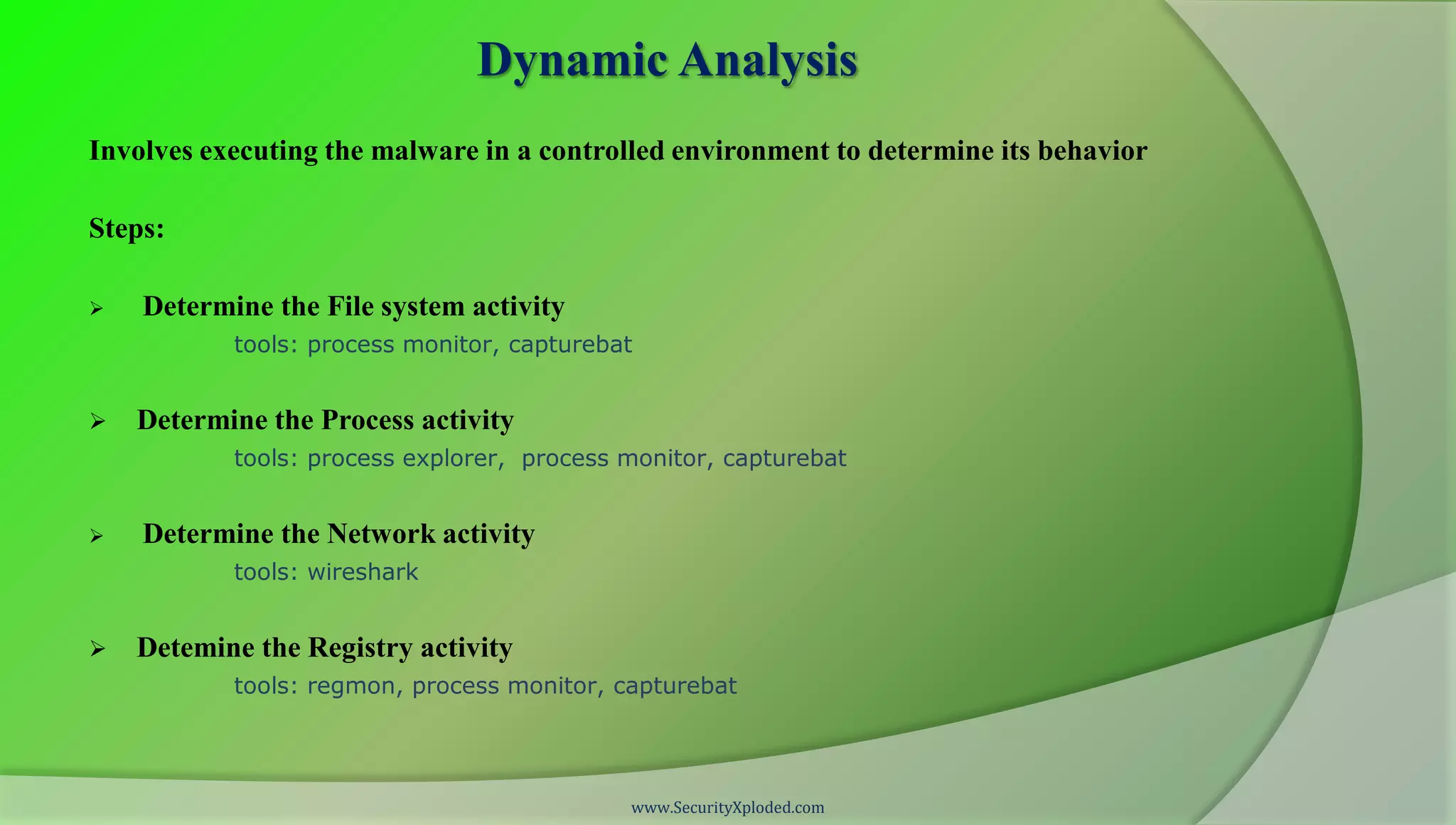
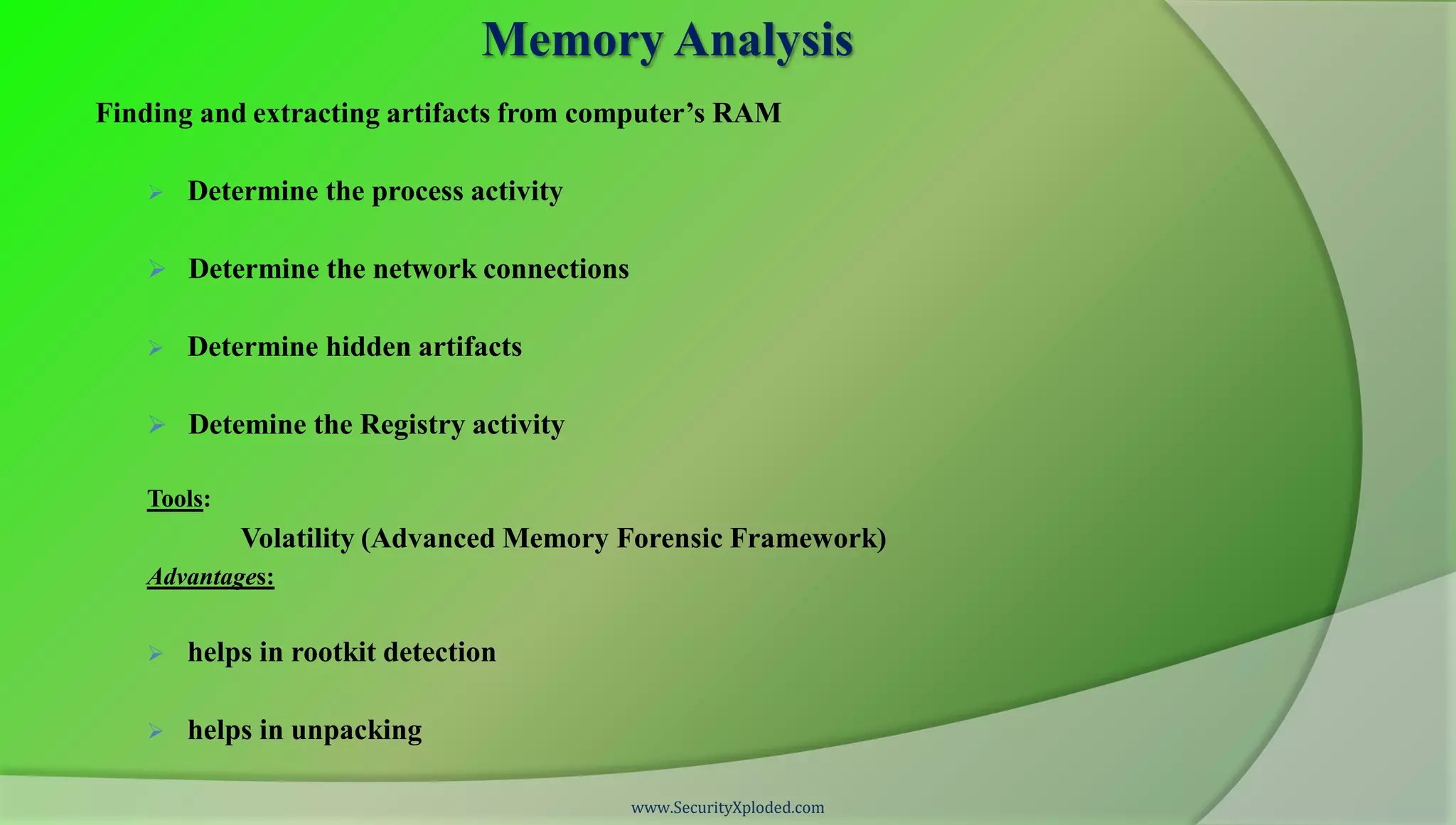
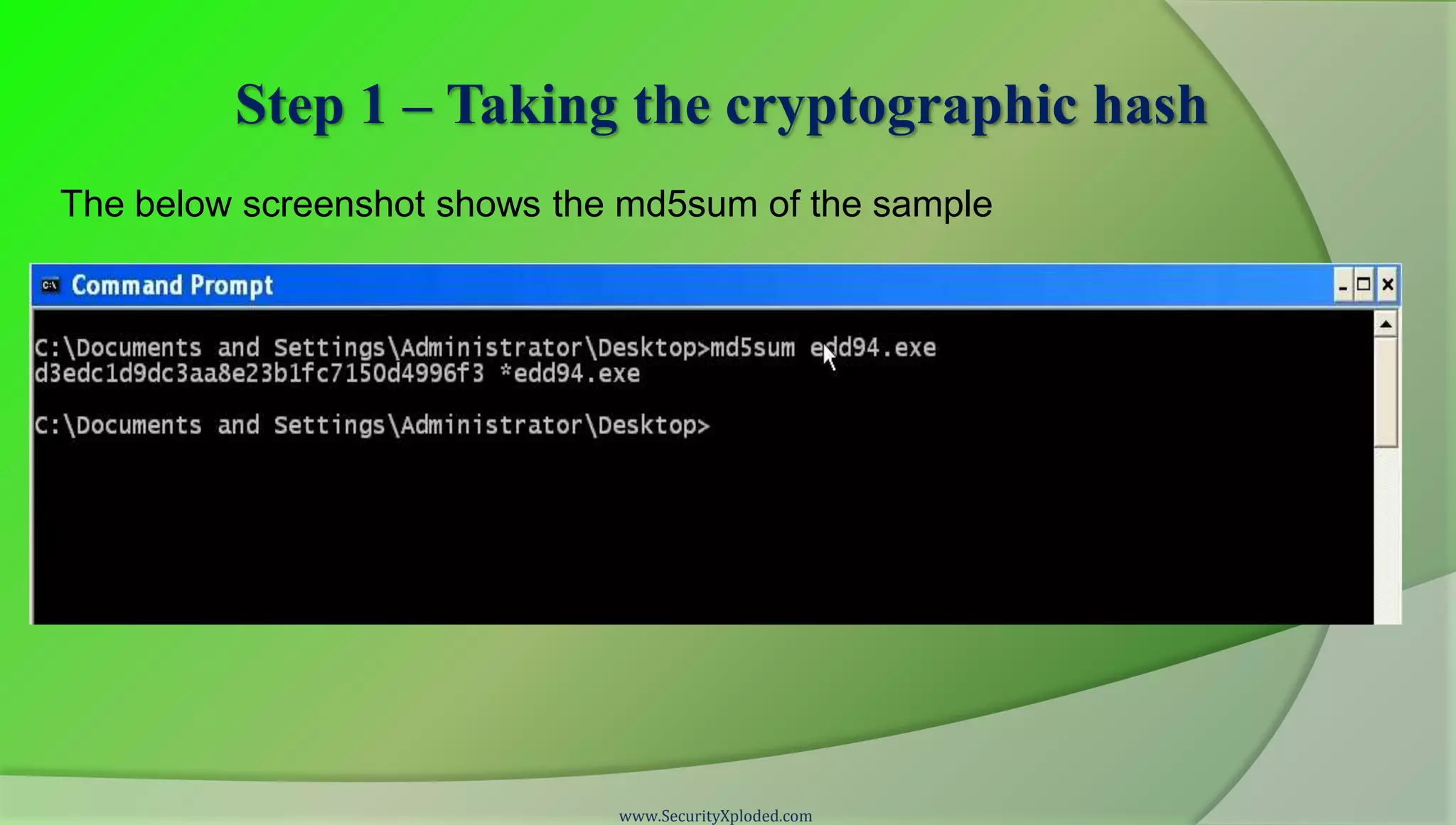
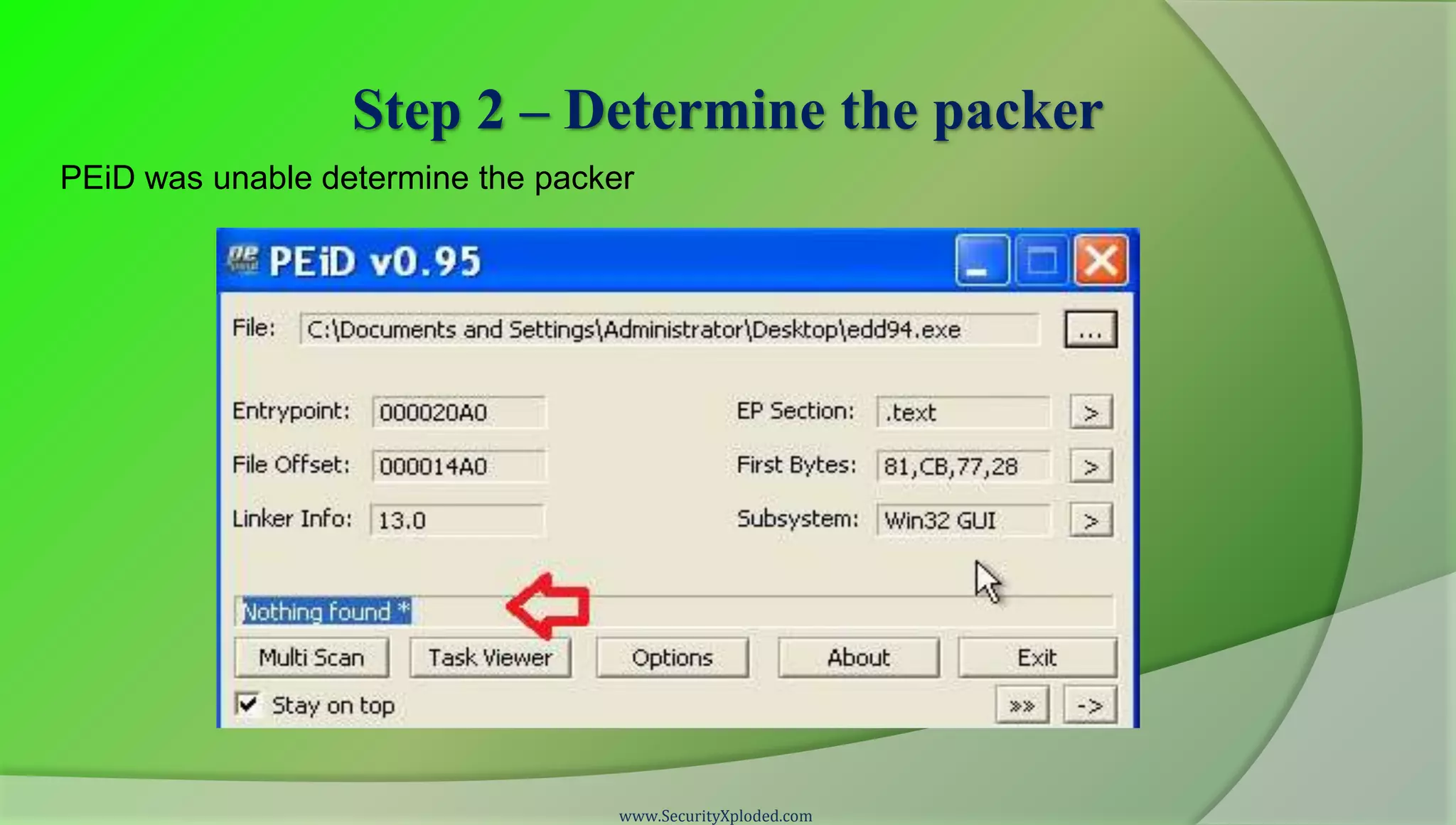
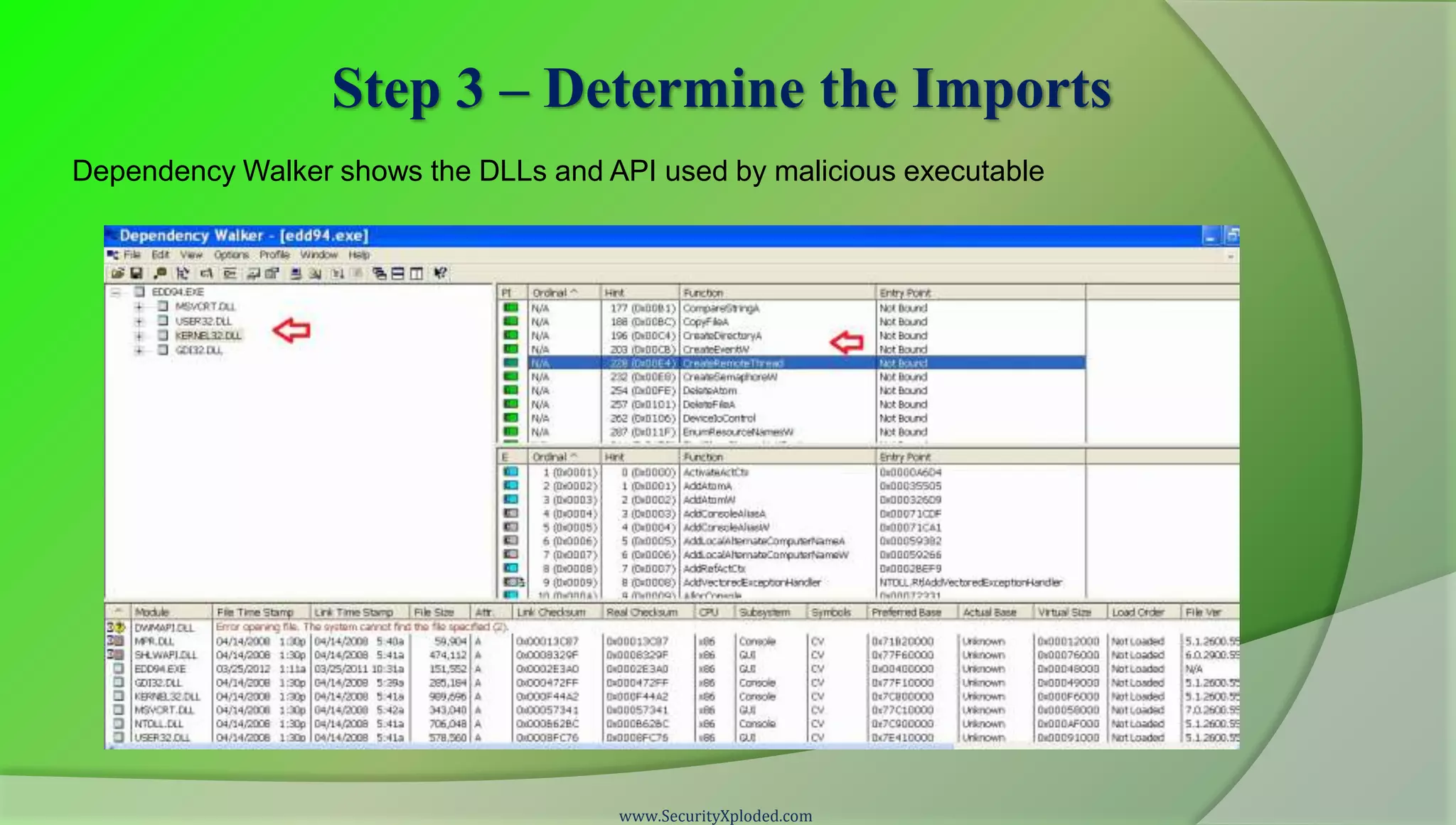
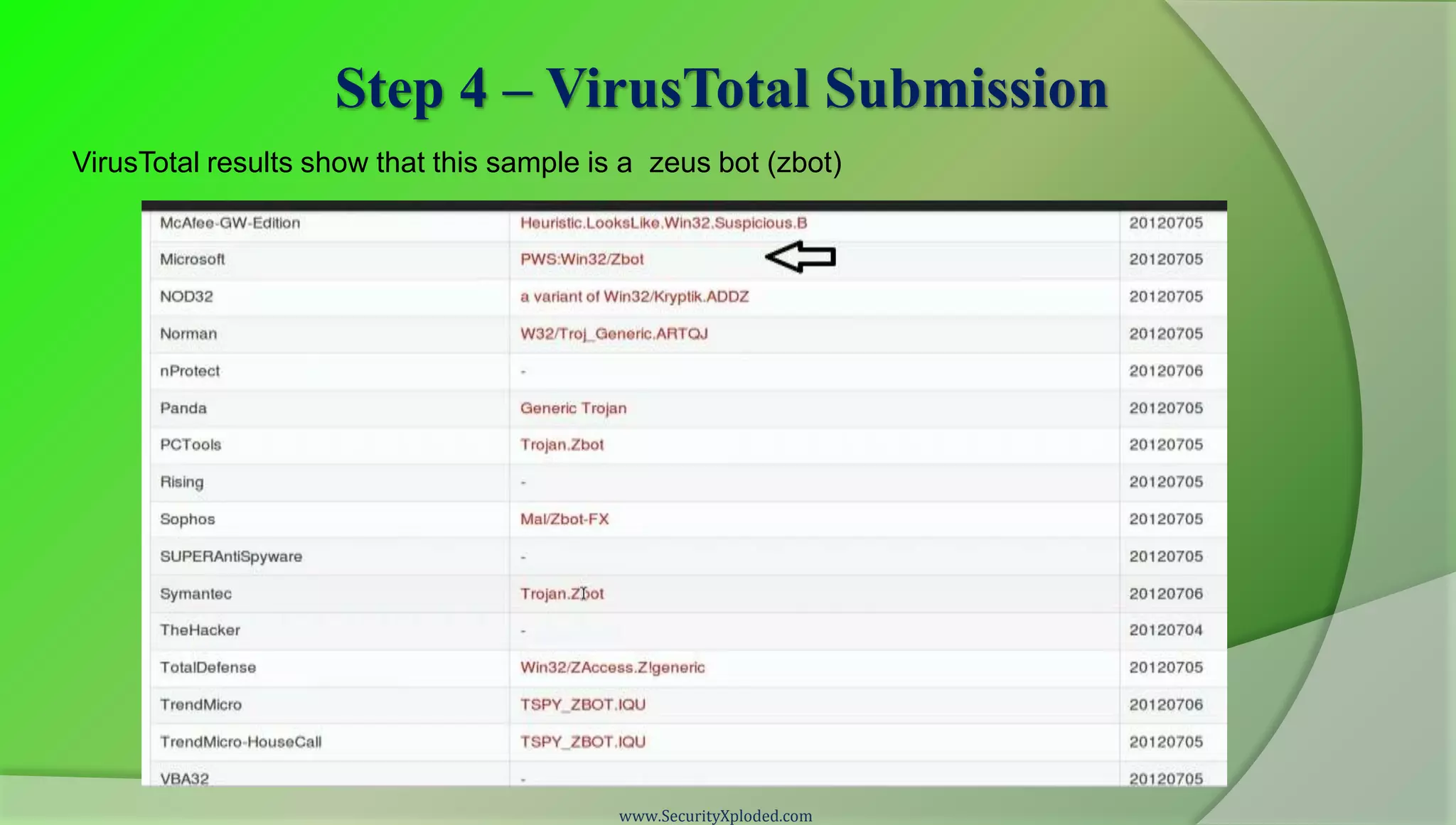
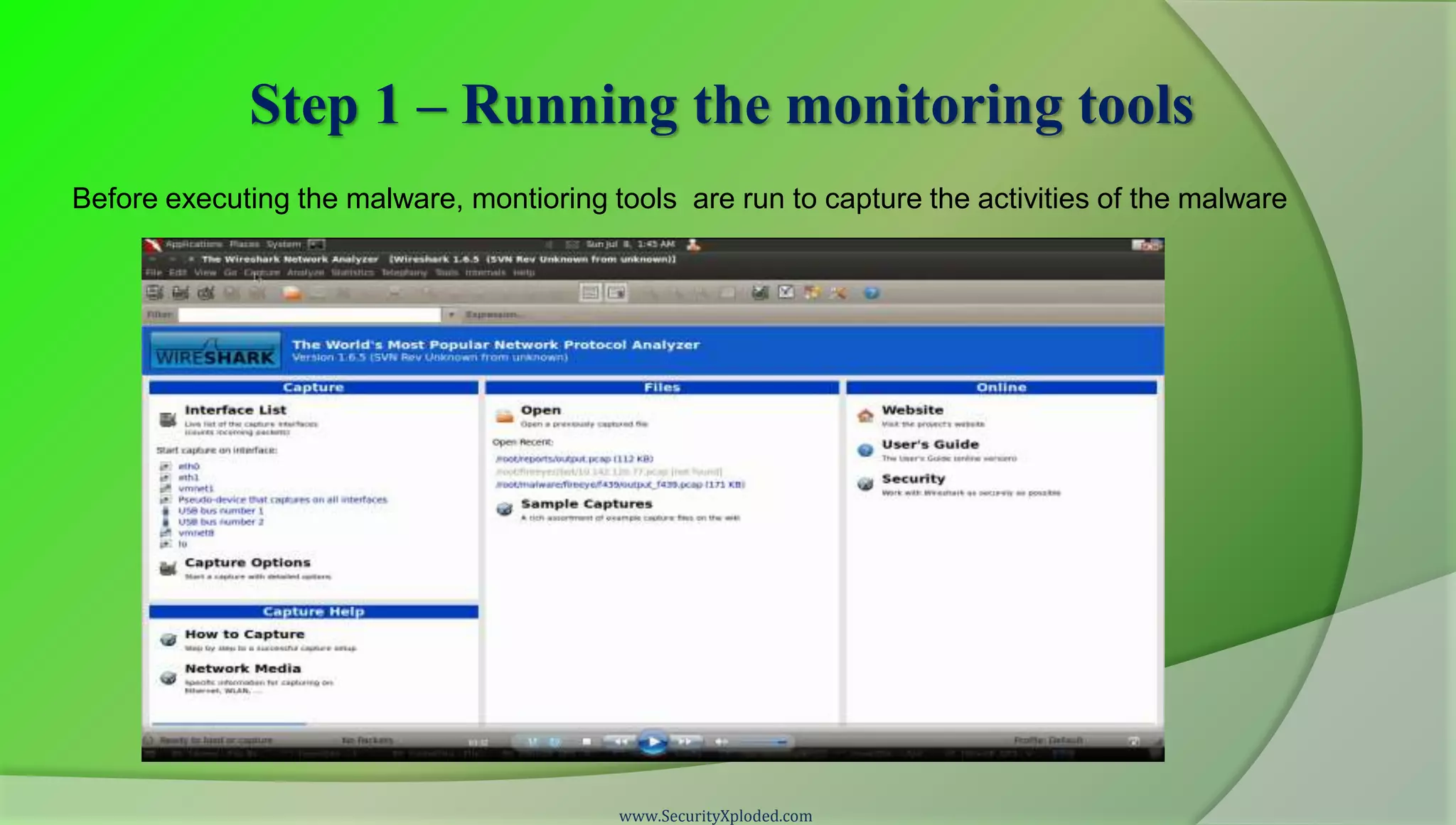
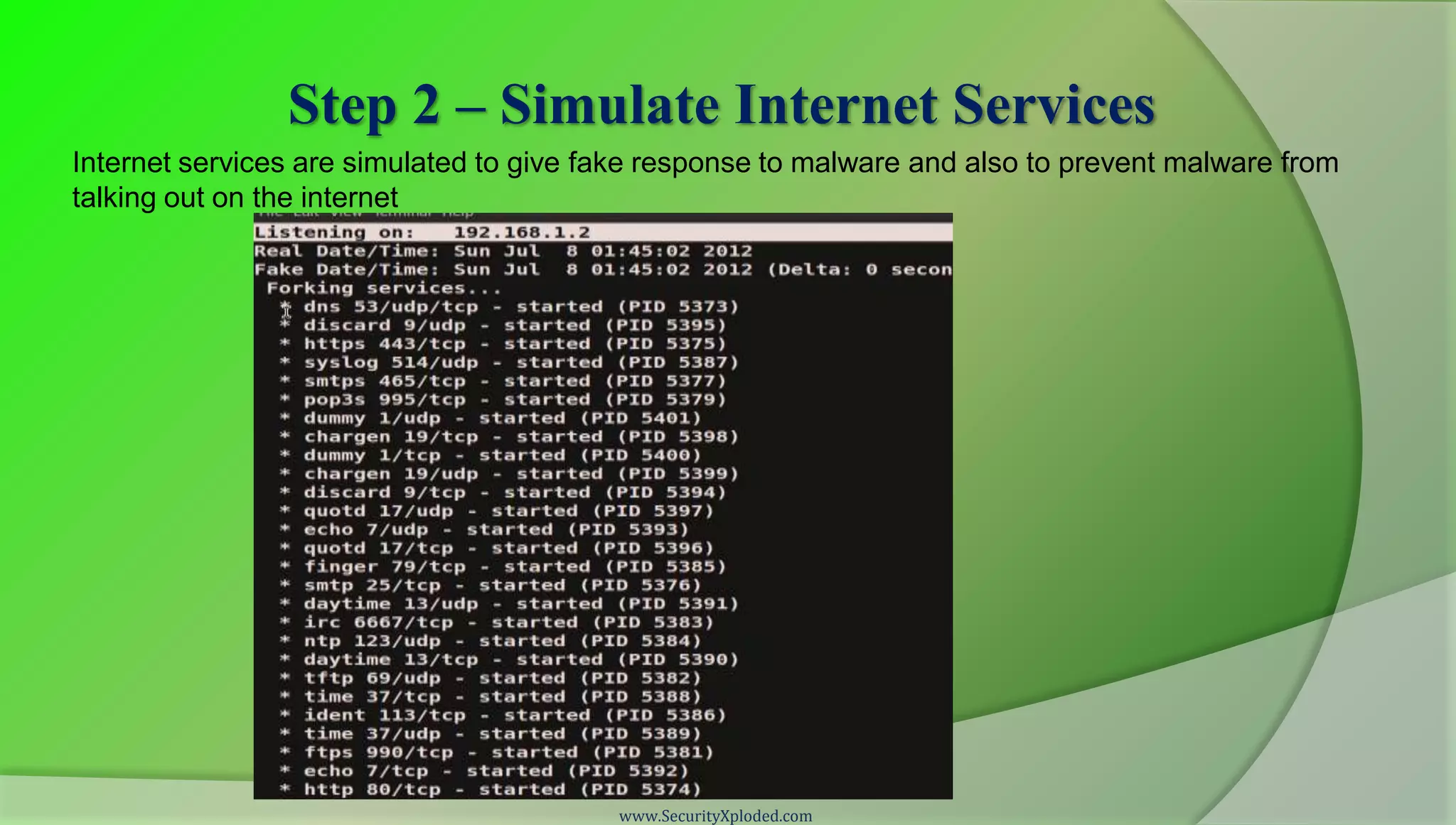
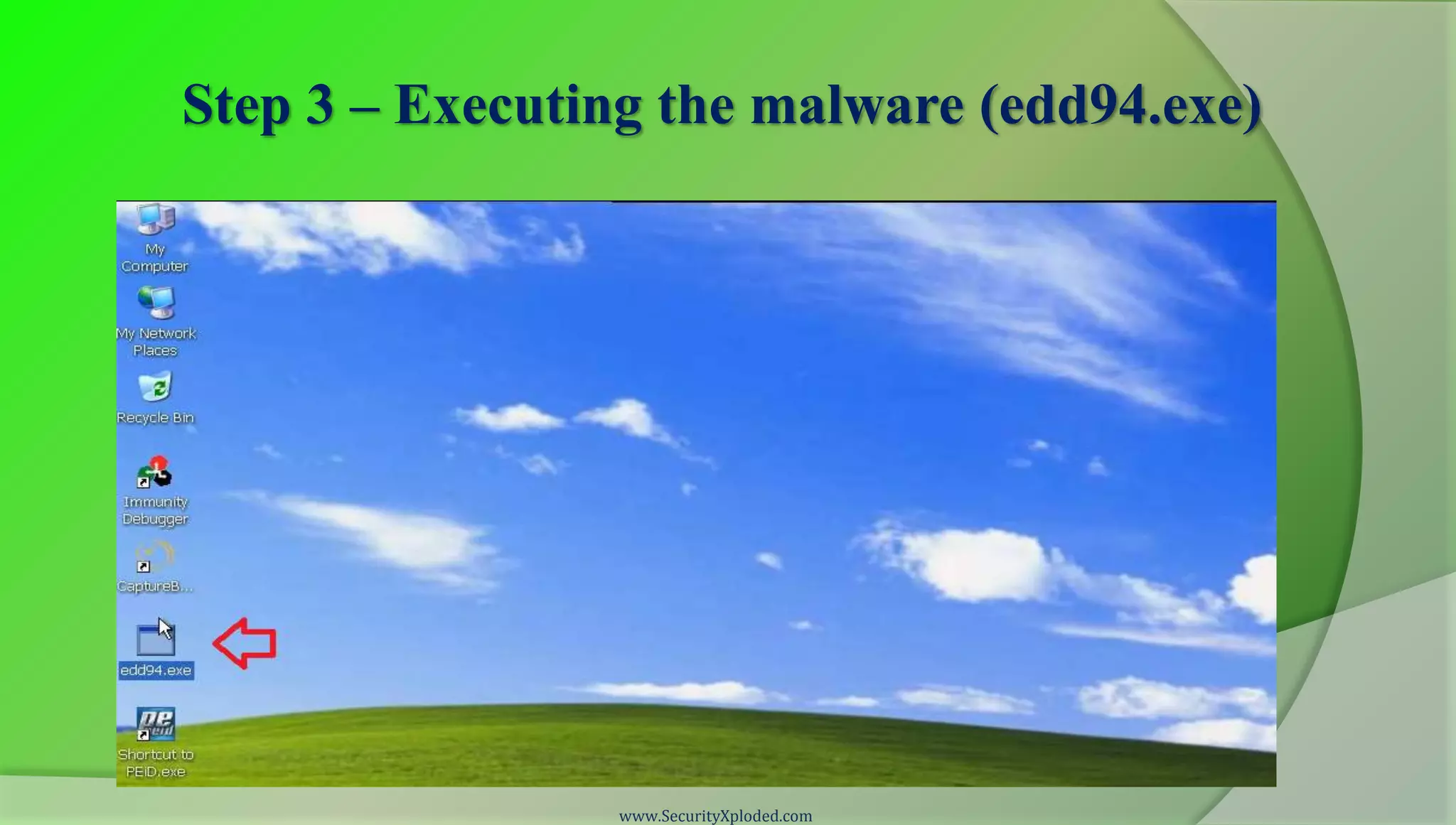
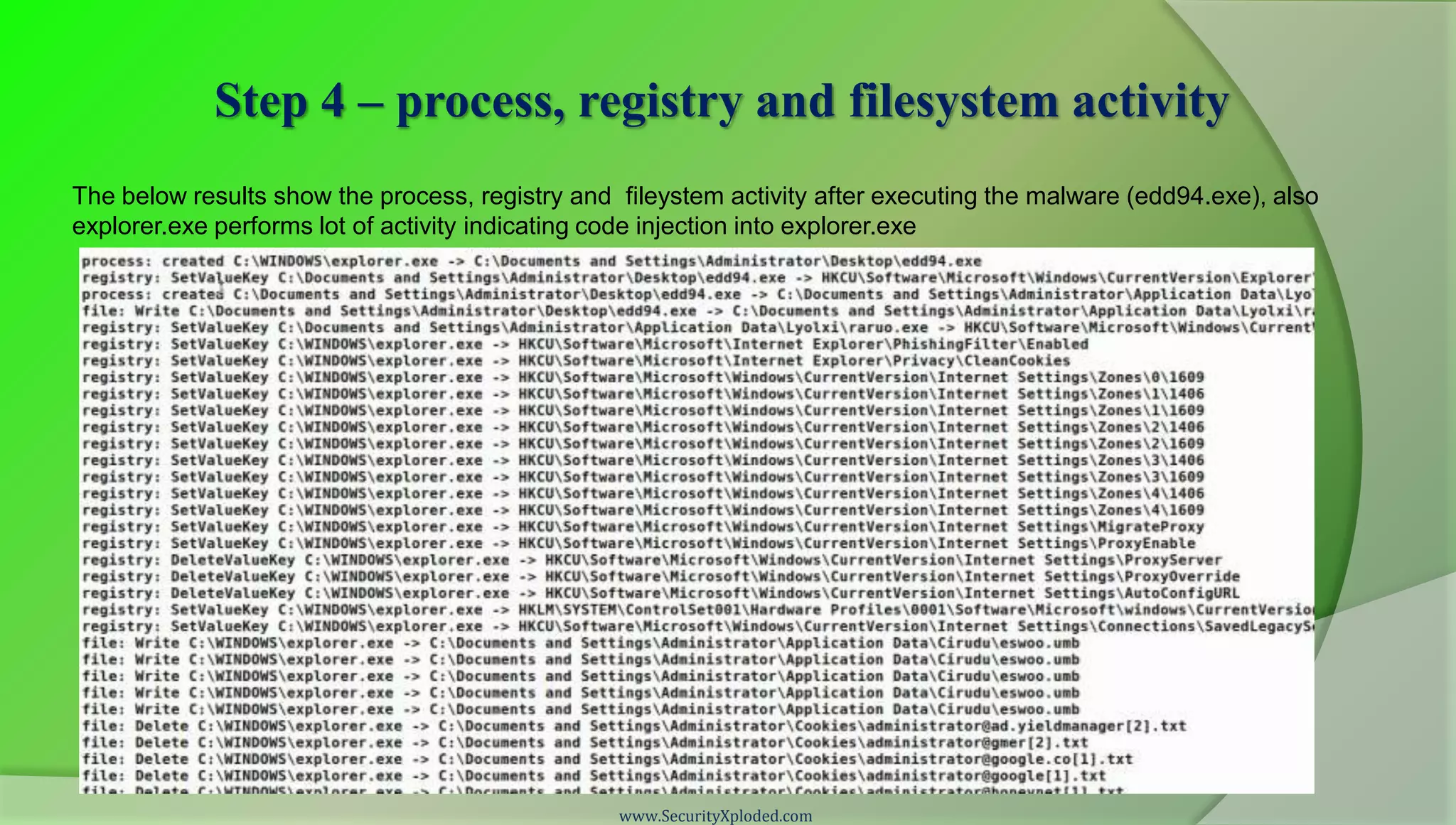
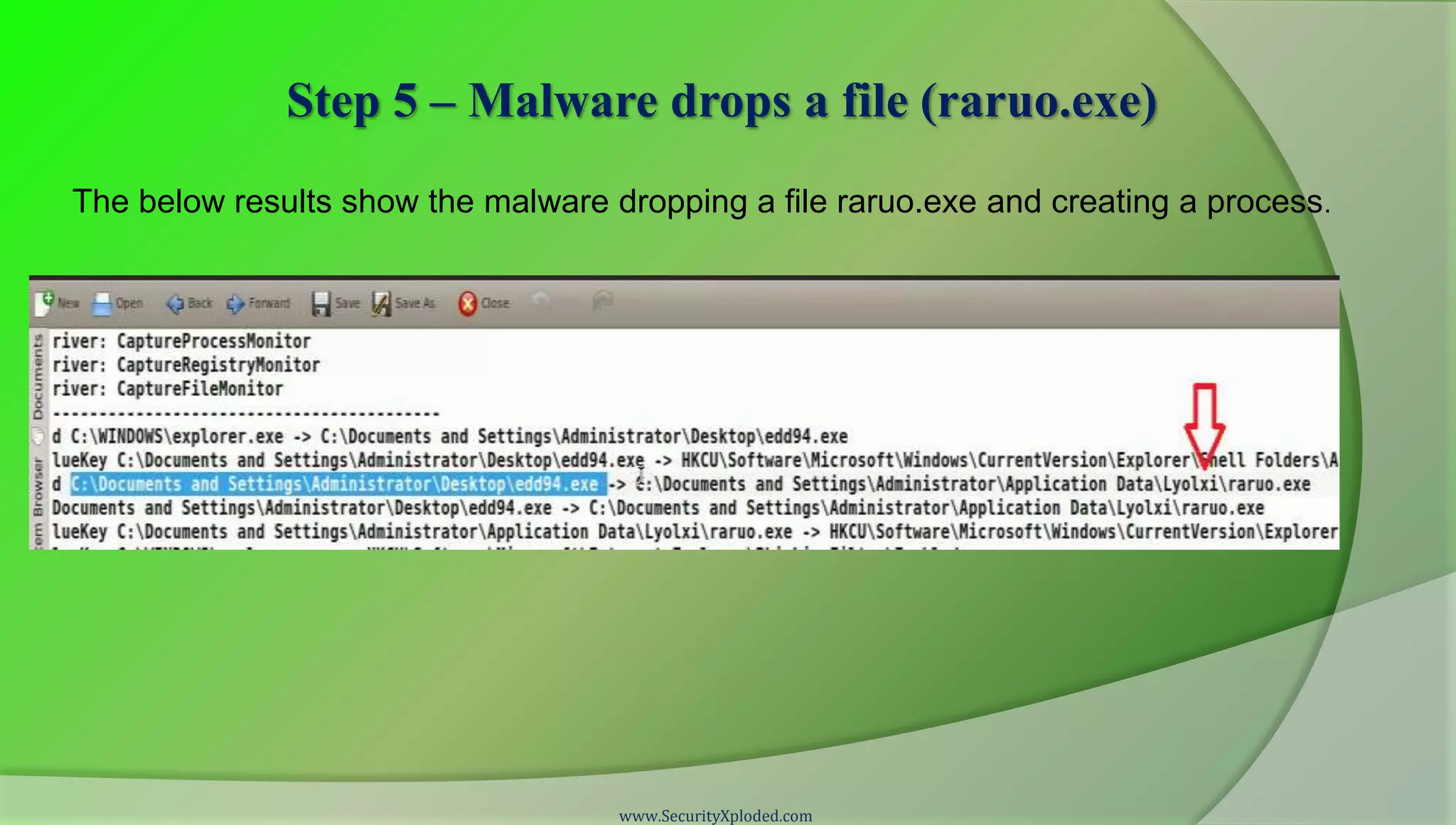
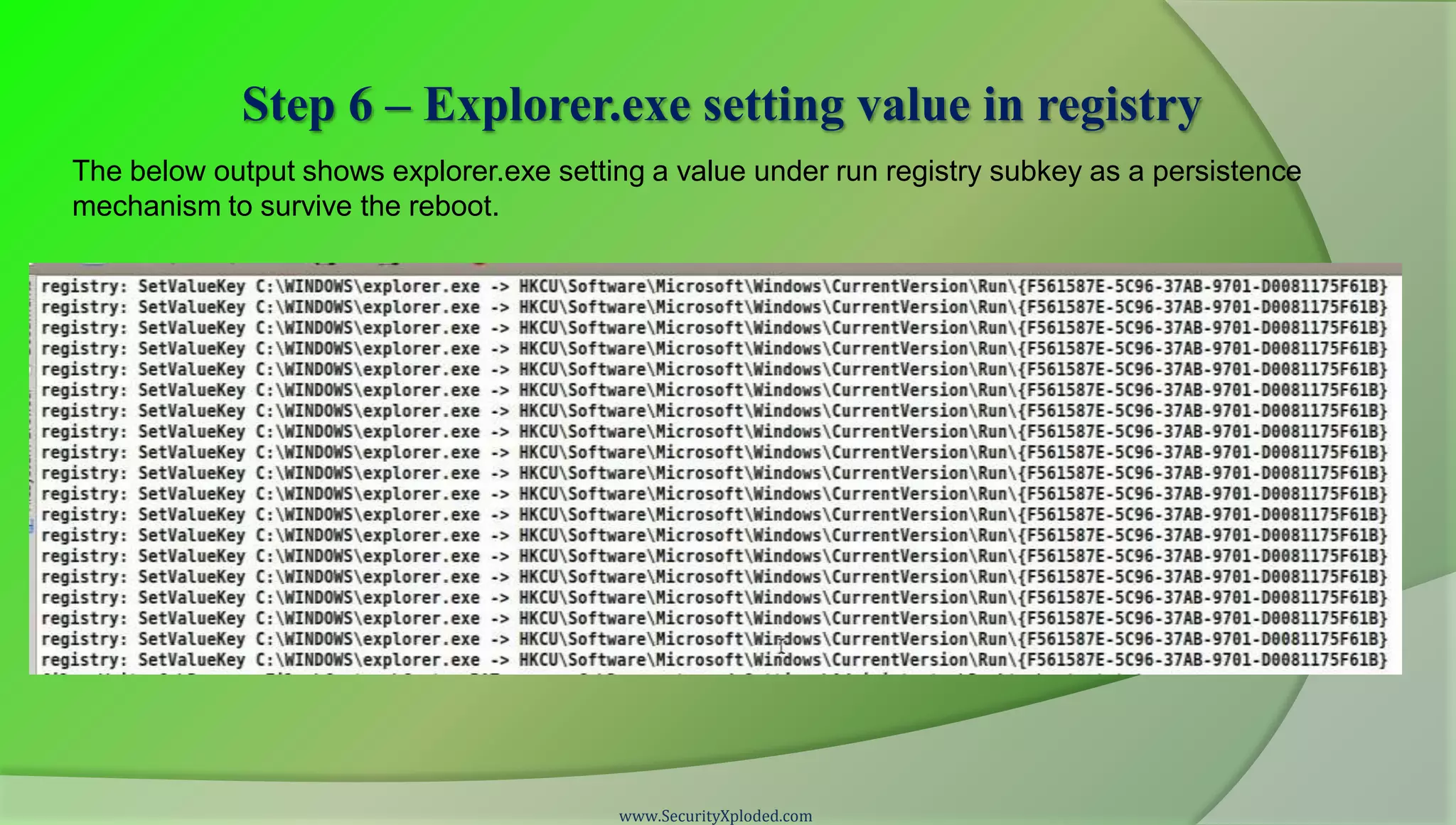
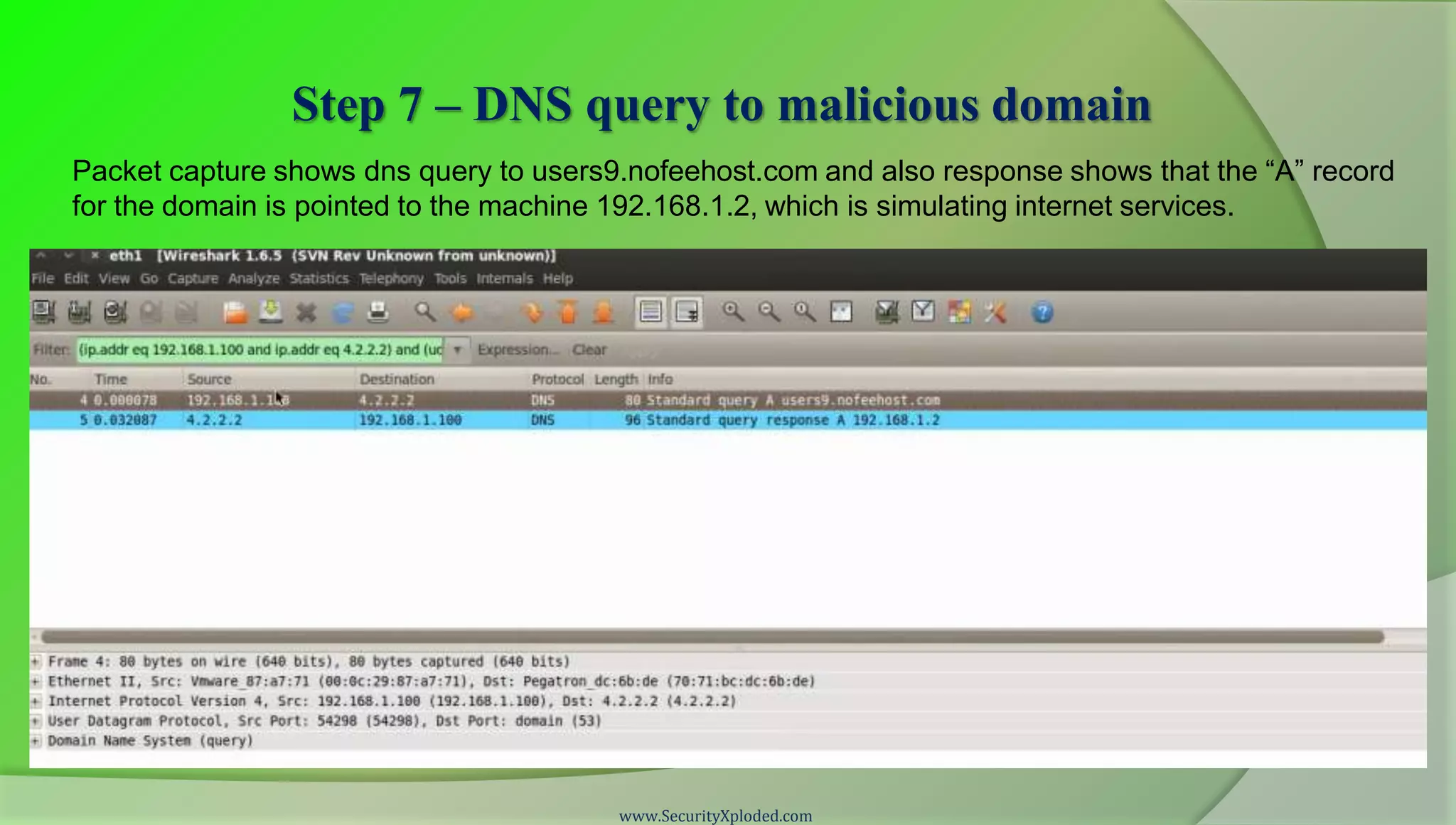
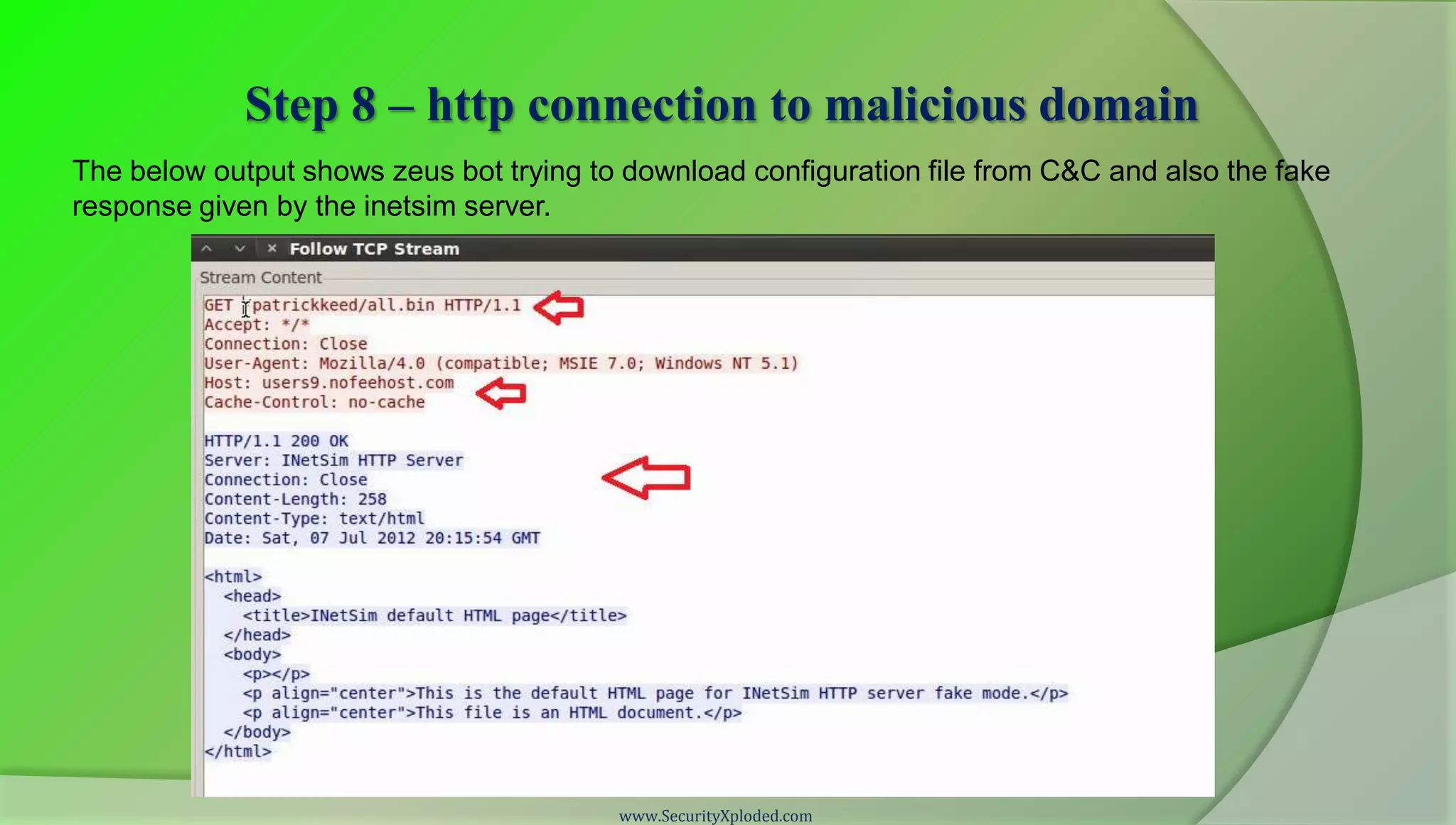
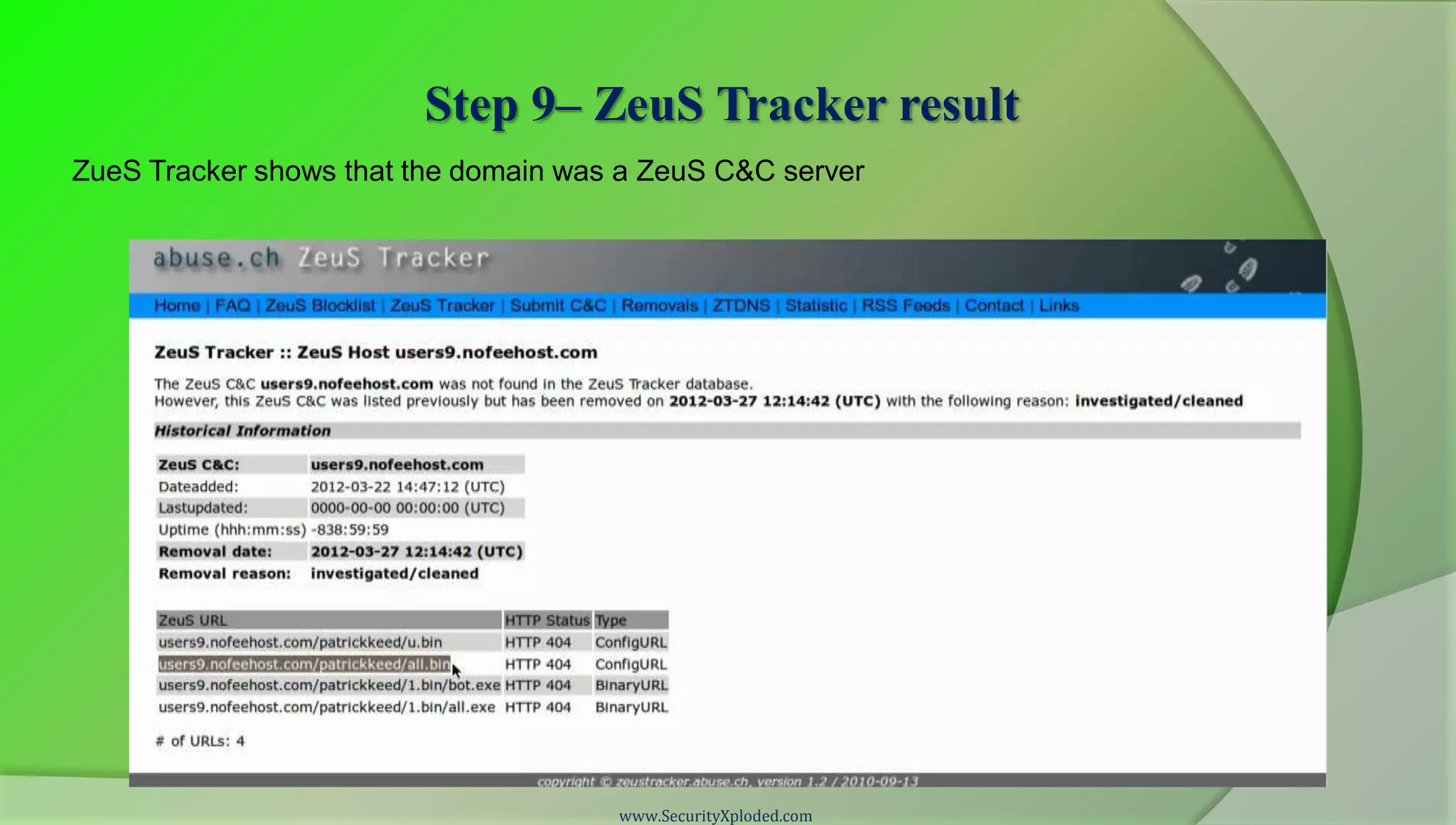
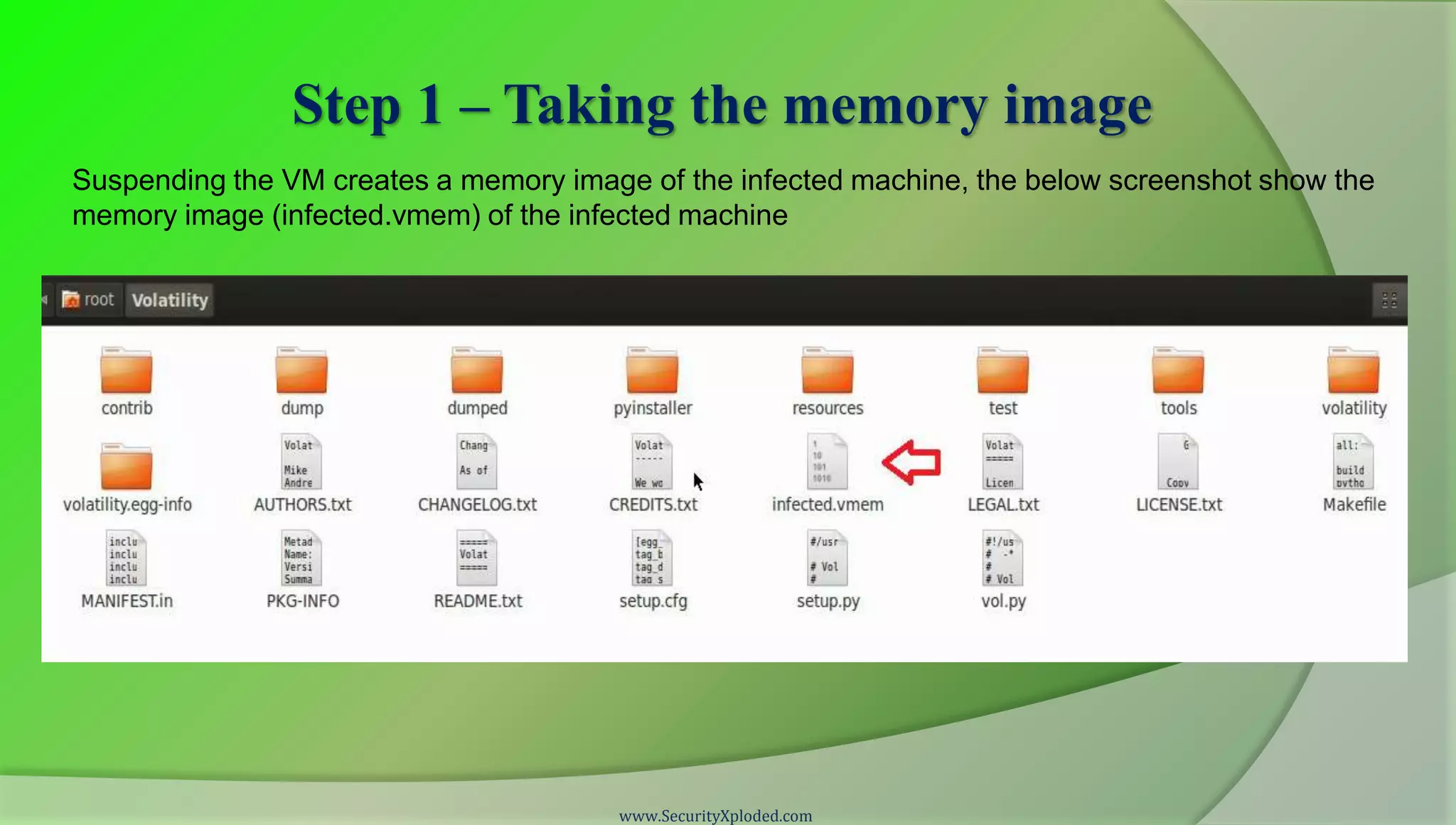
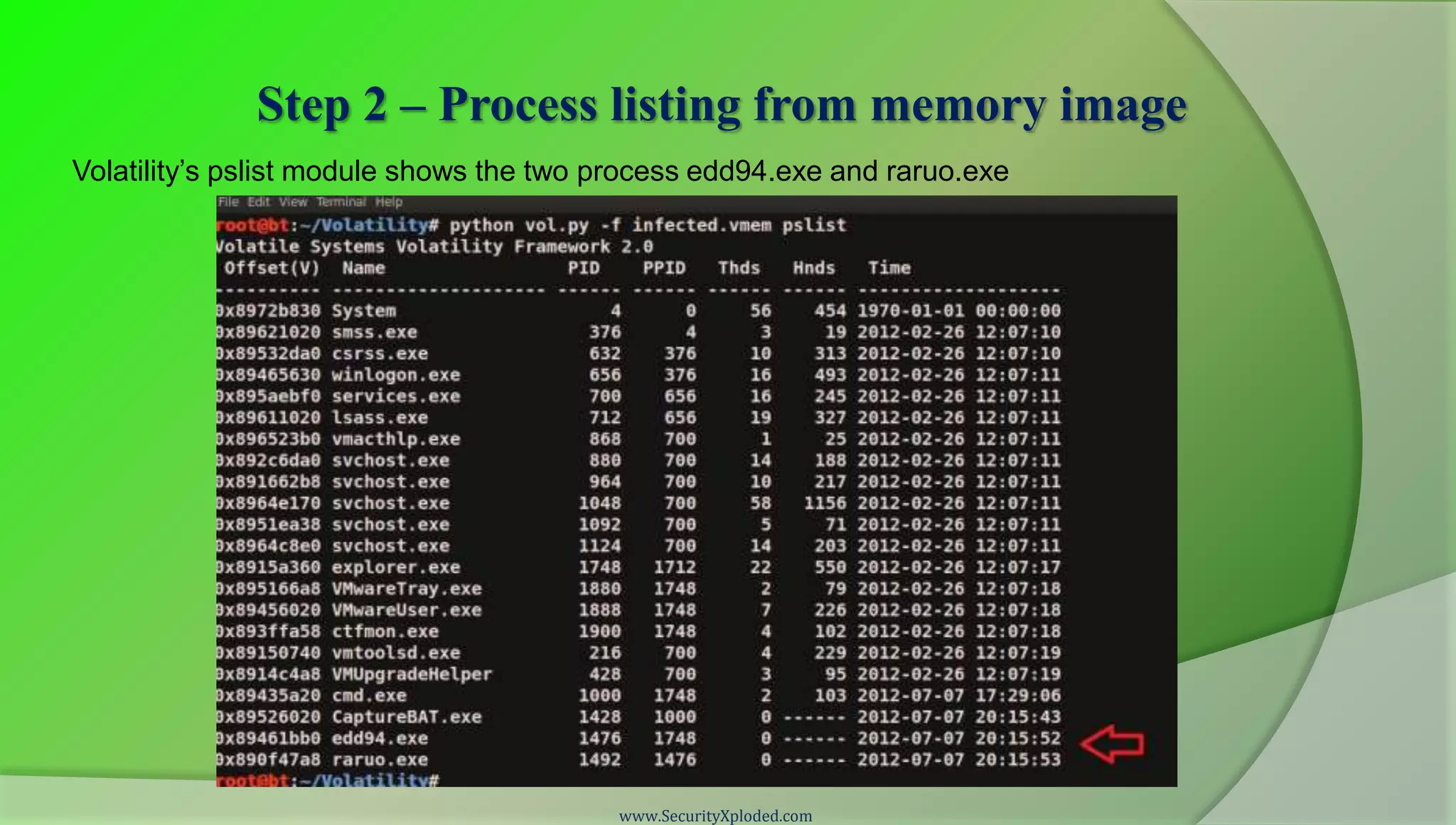
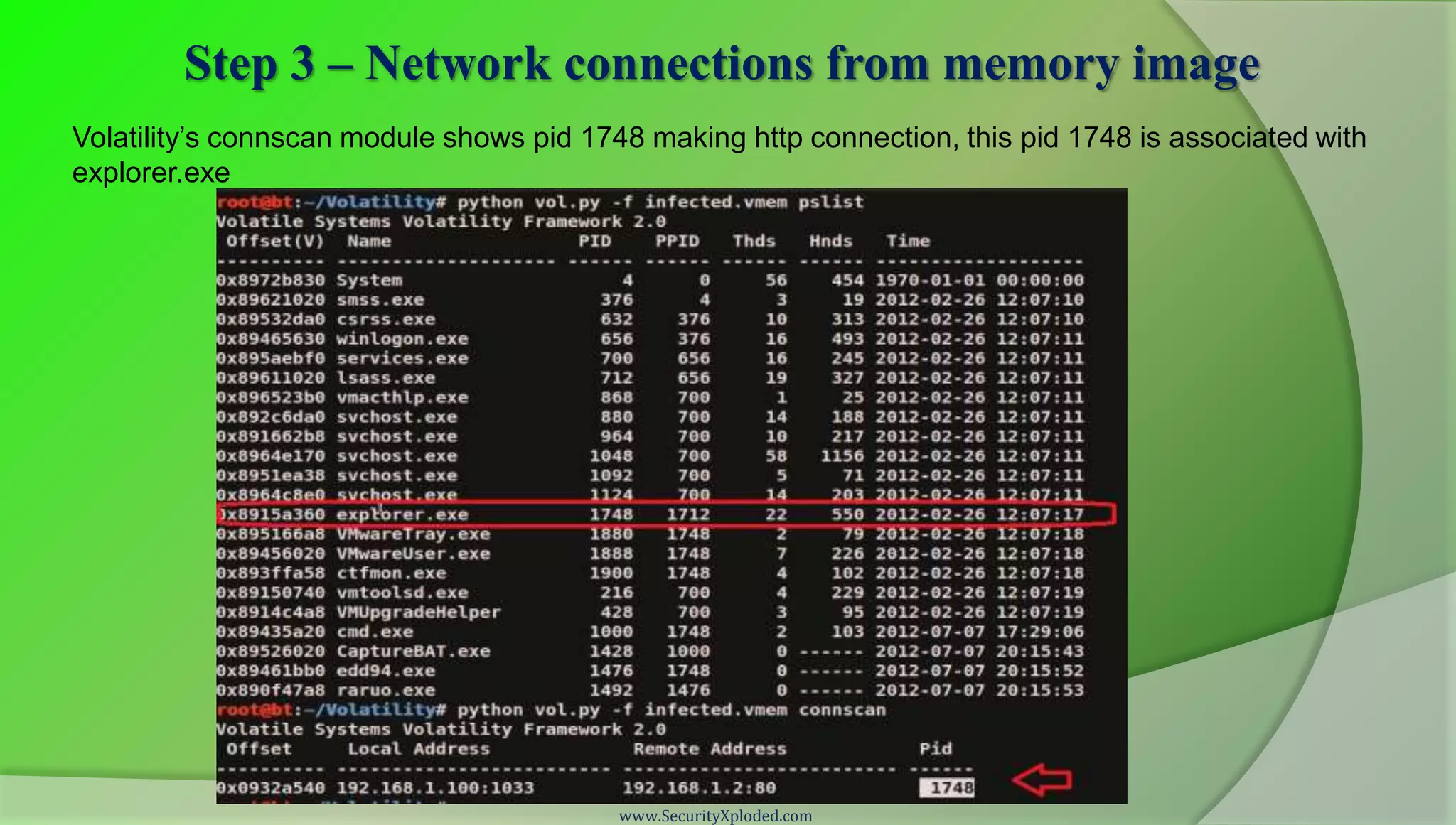
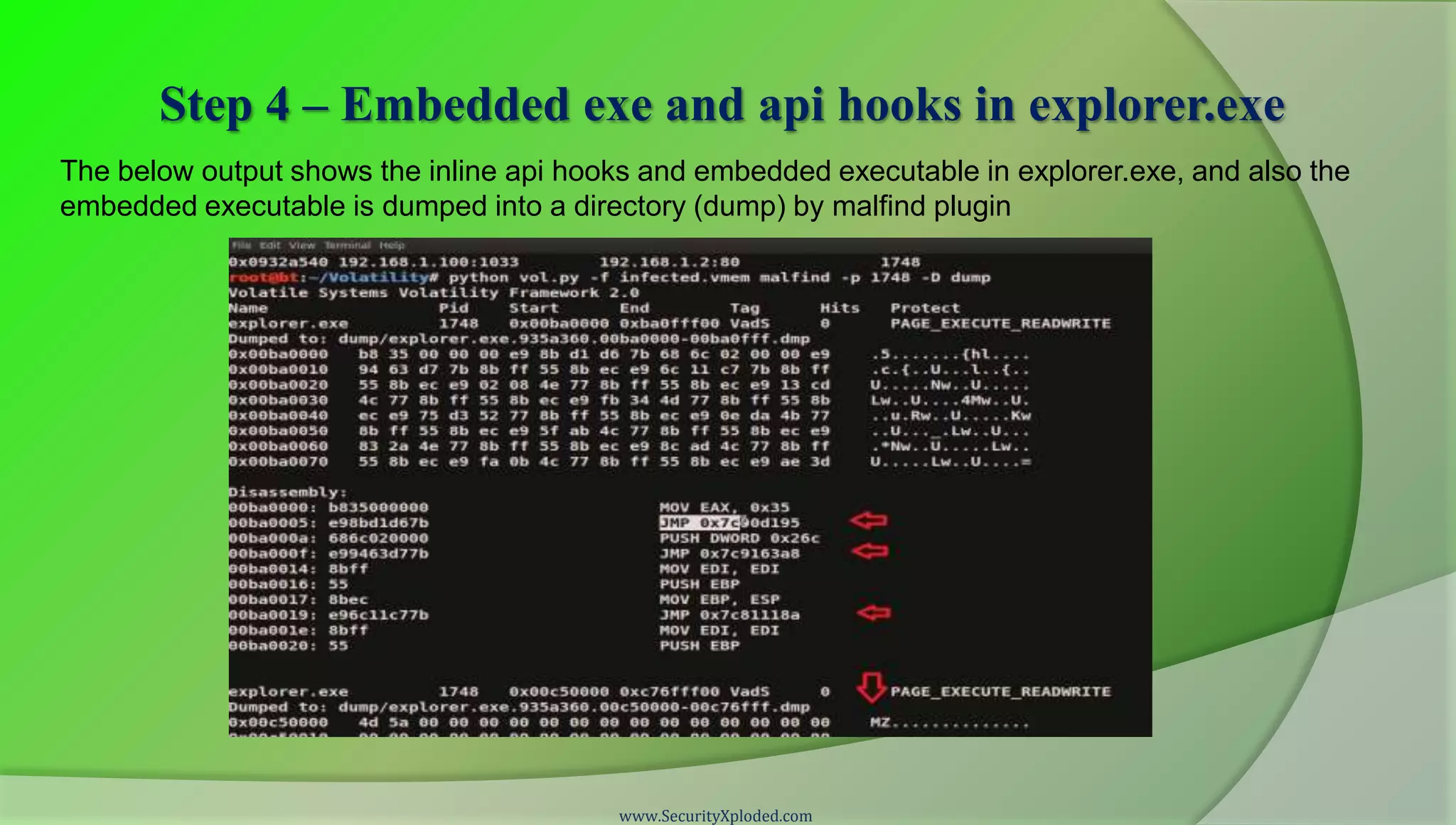
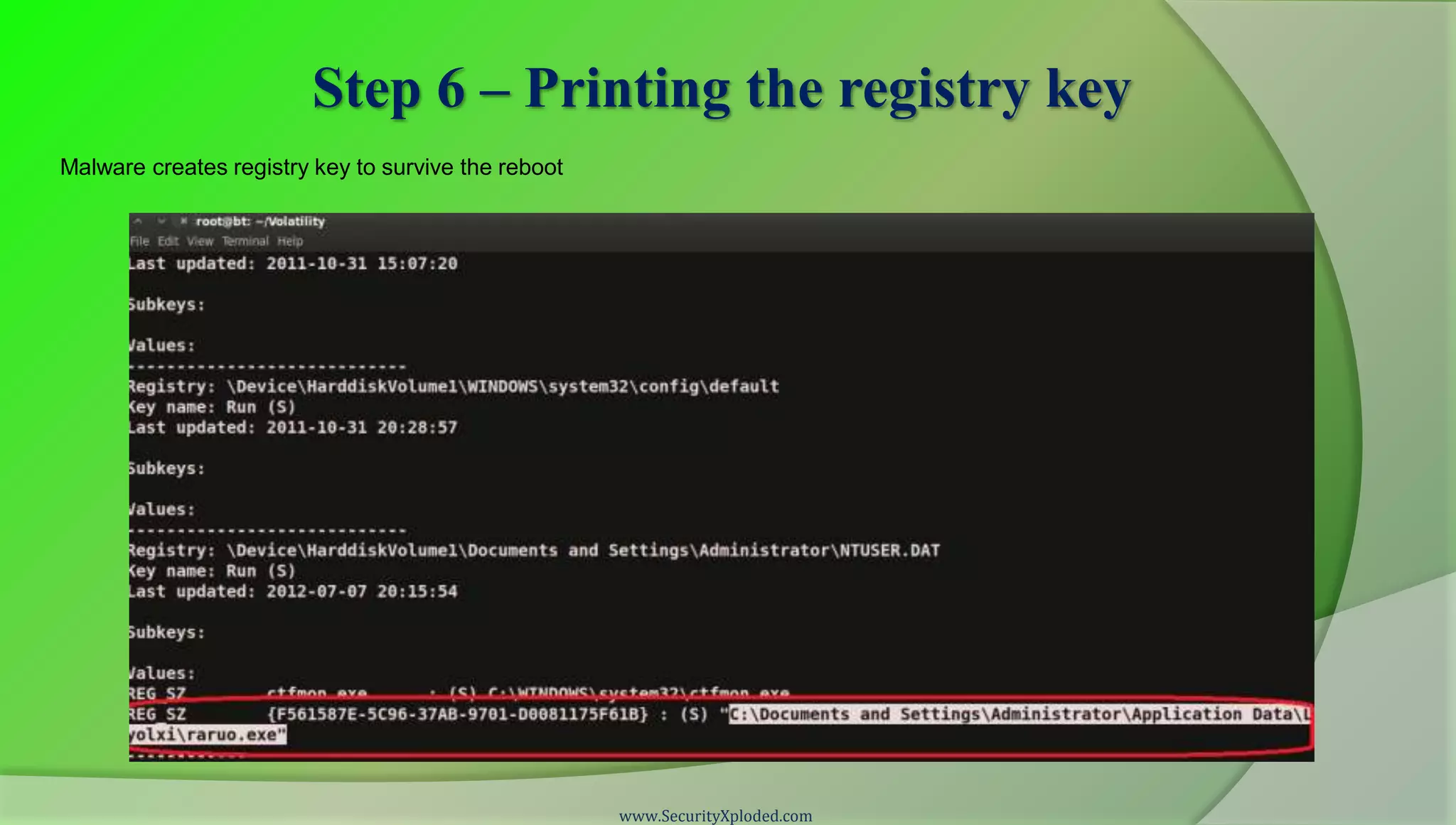
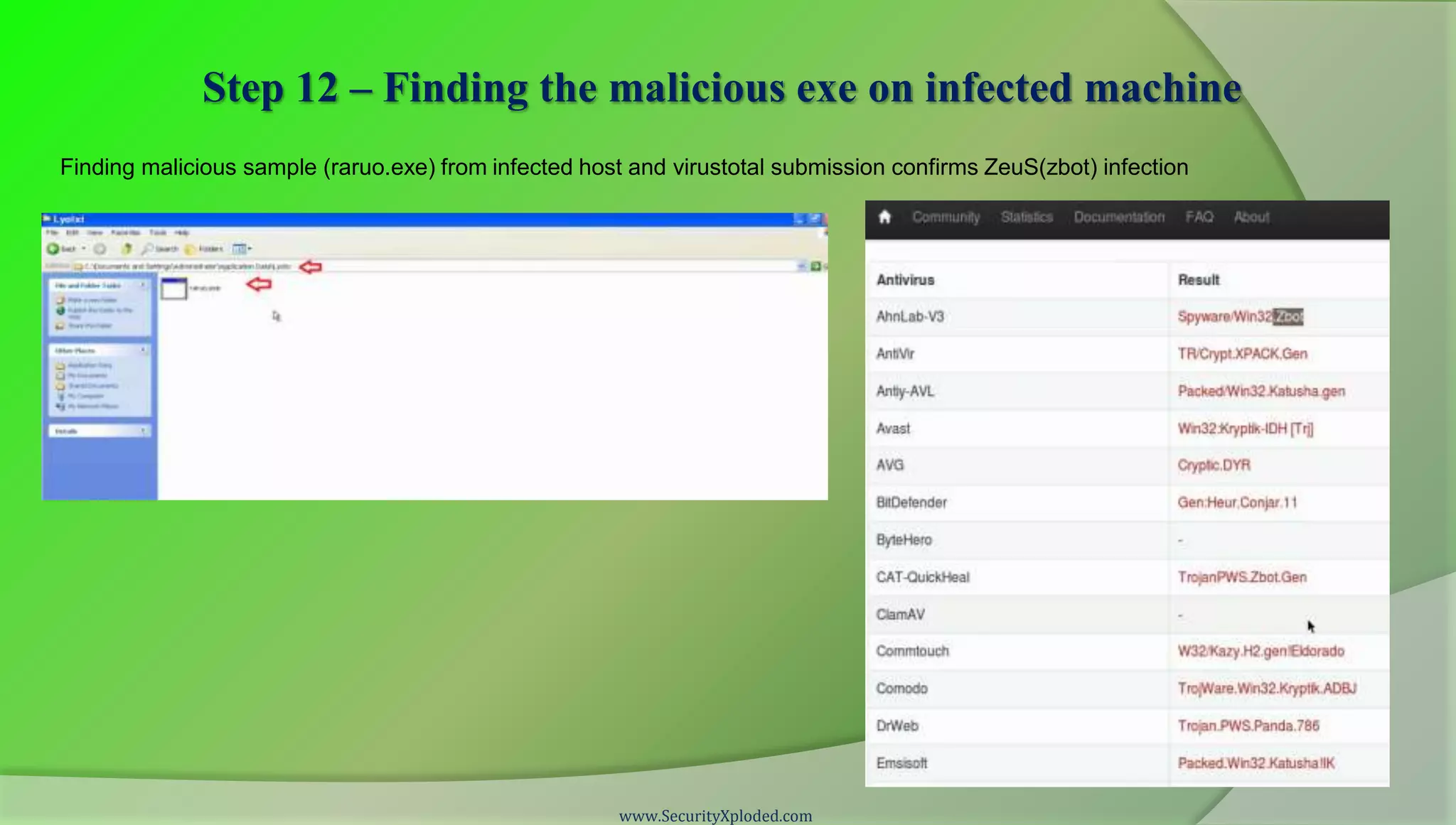
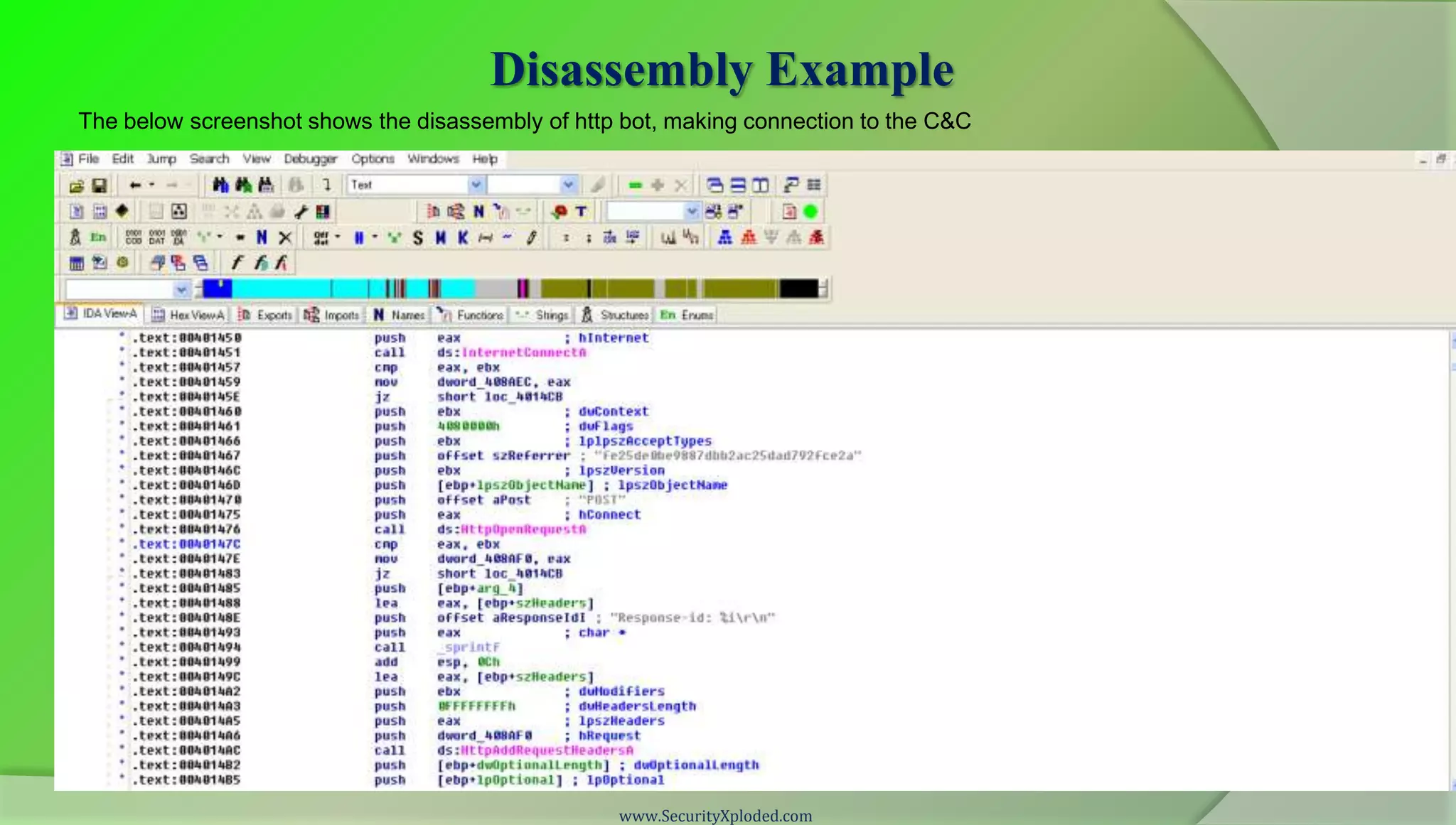
The document provides a disclaimer from SecurityXploded regarding the content and responsibility of the information presented in their malware analysis training program. It outlines various malware analysis techniques, including static, dynamic, and memory analysis, along with steps and tools for each method. The presentation also thanks contributors and provides a guide on how to analyze malware behavior through practical examples.