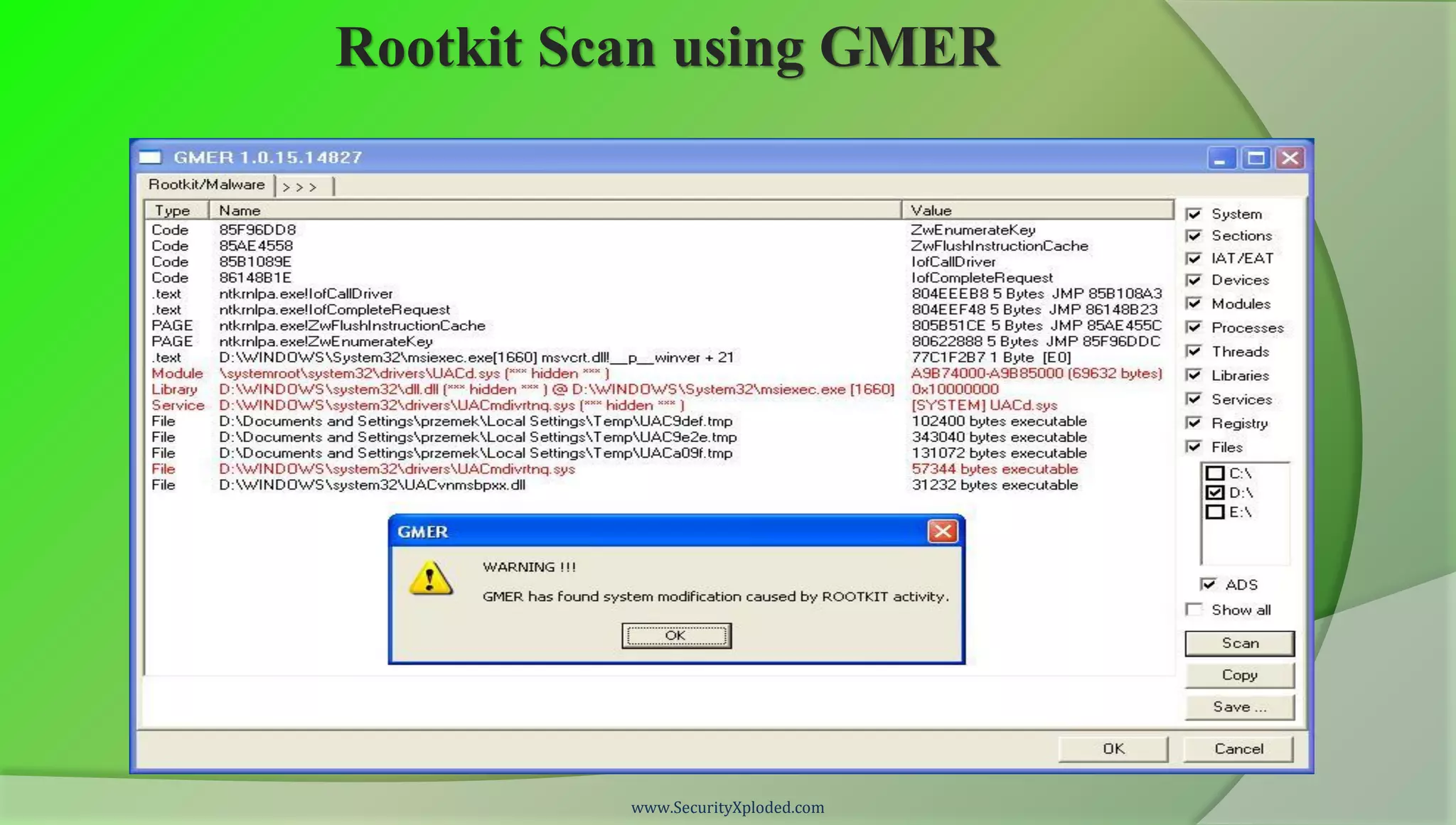
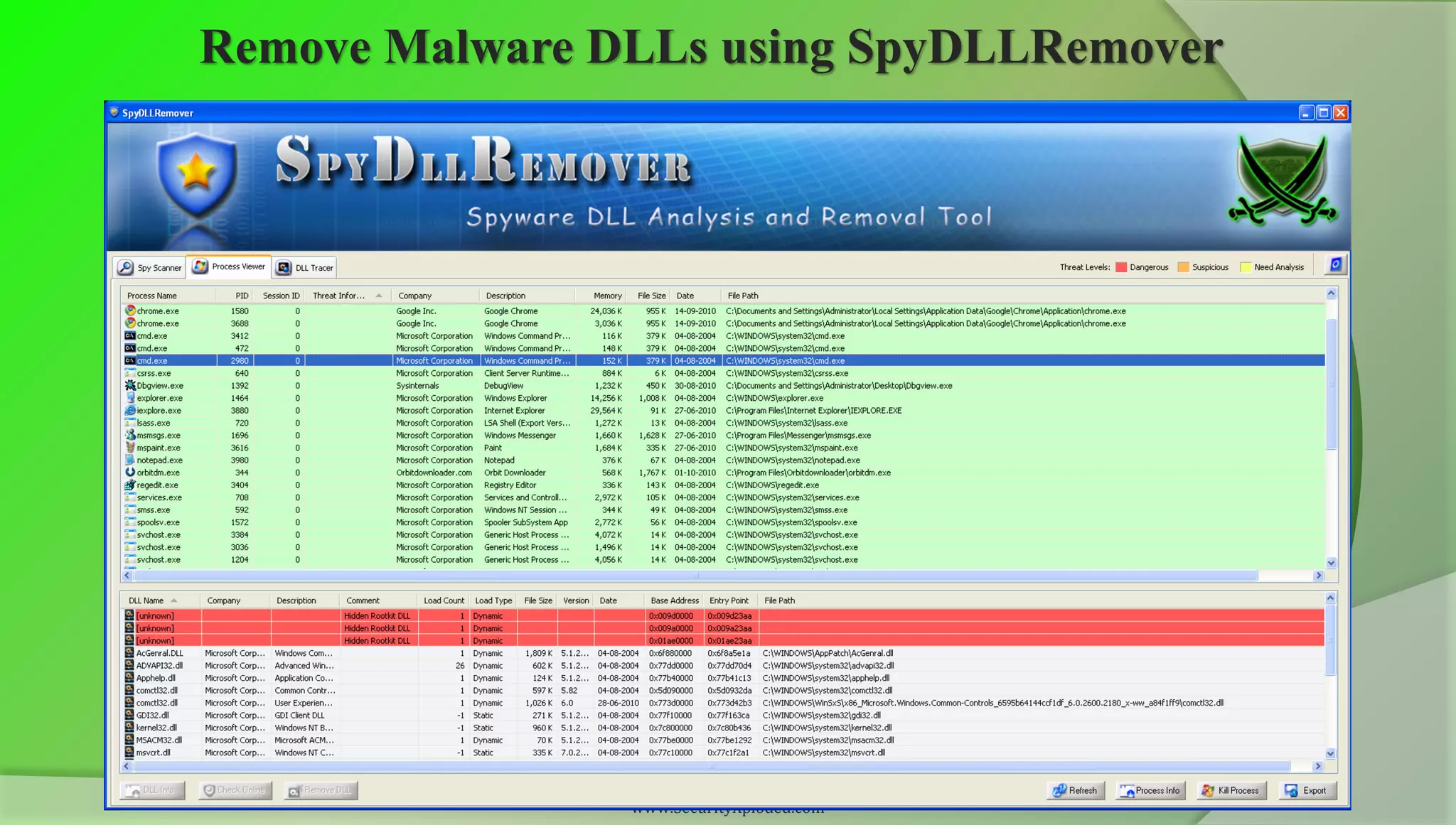
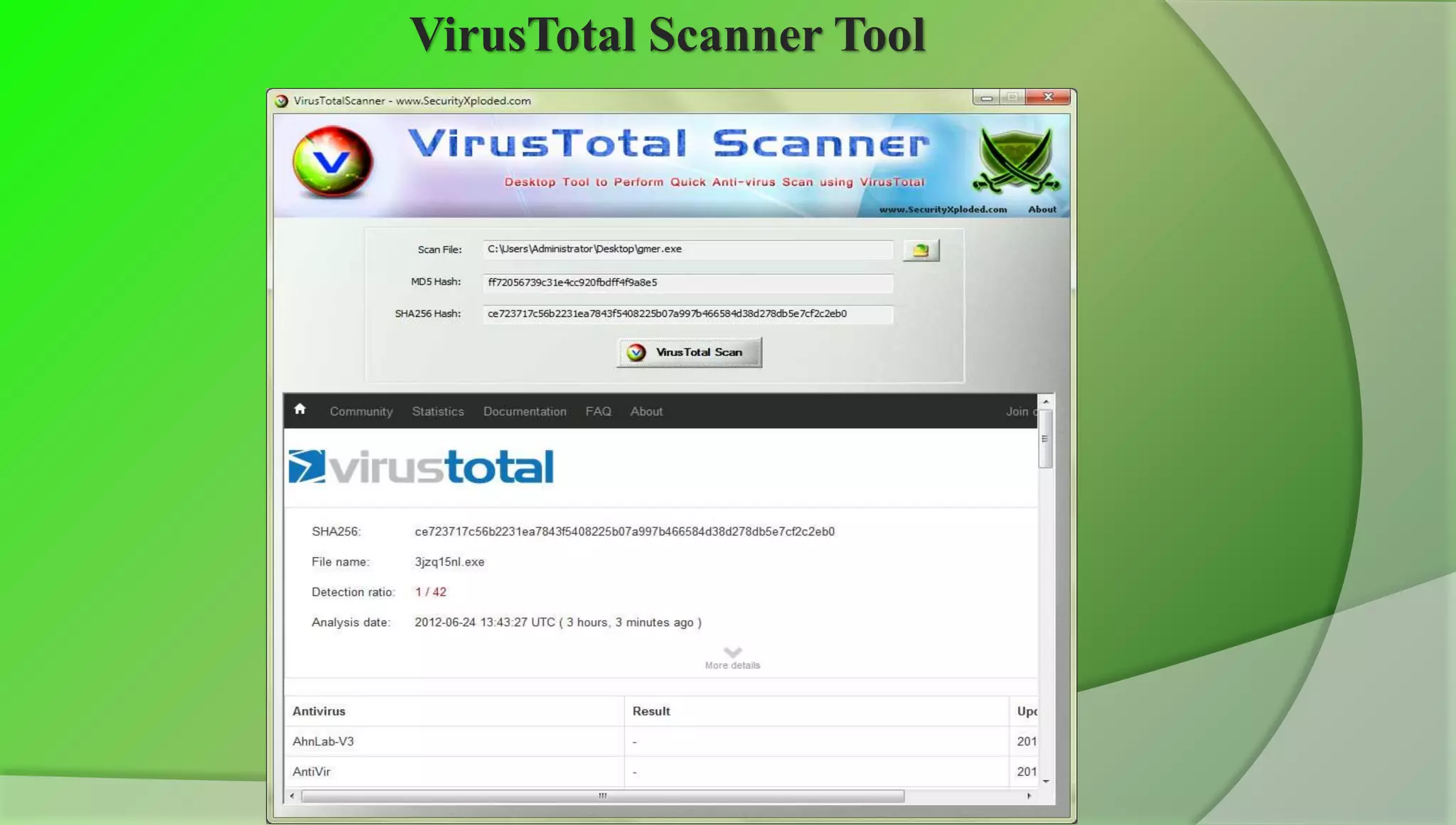
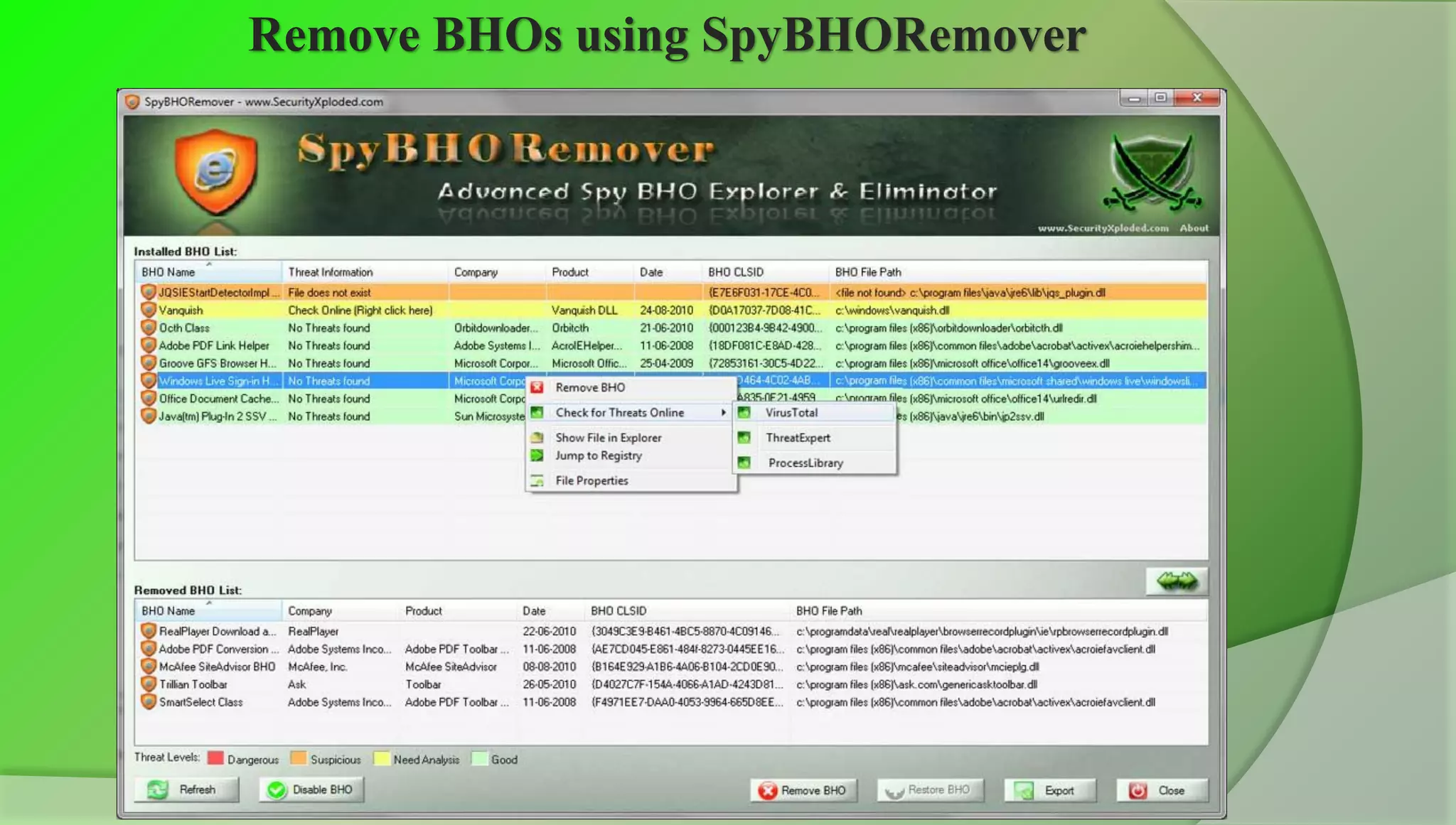
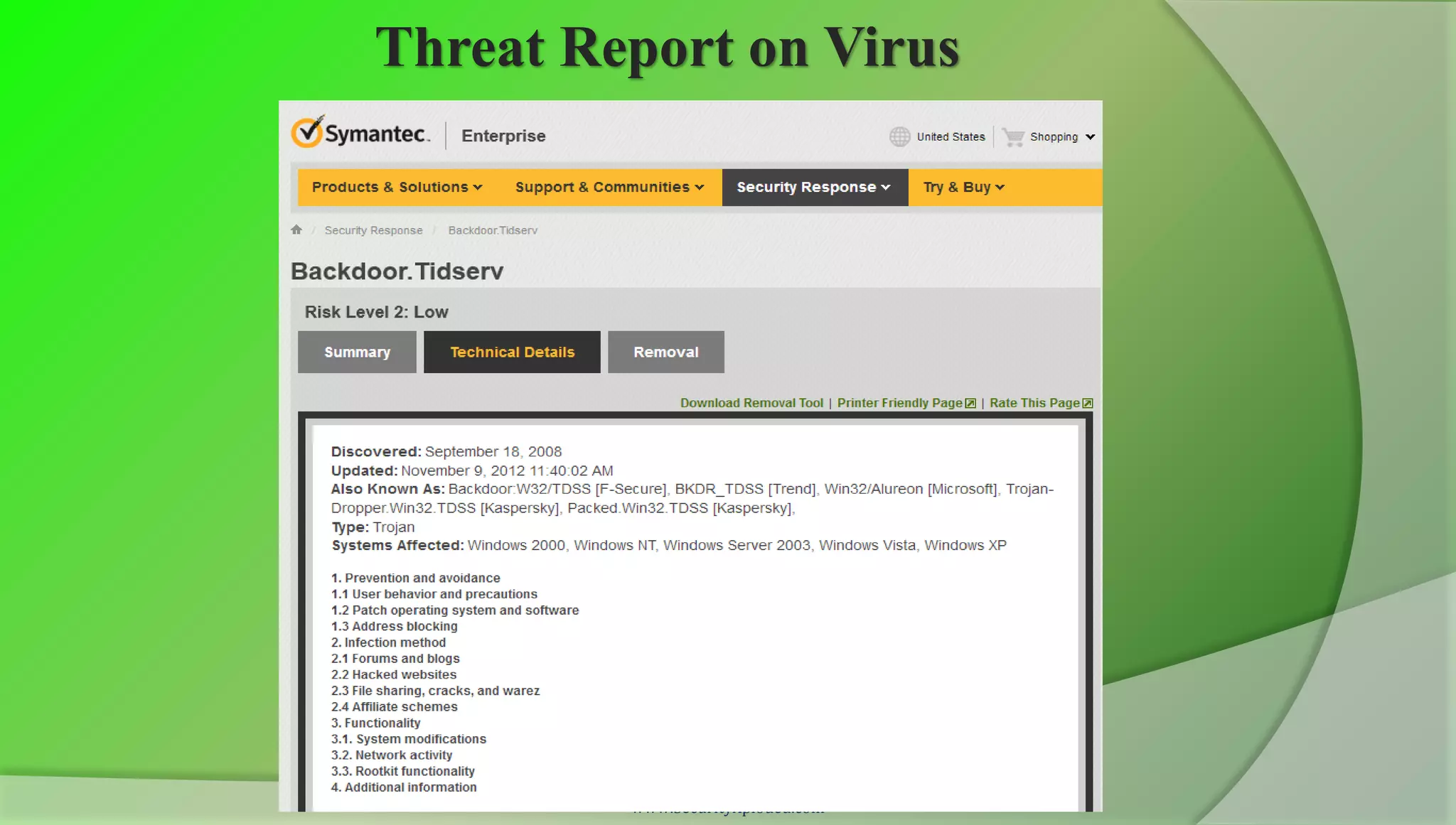
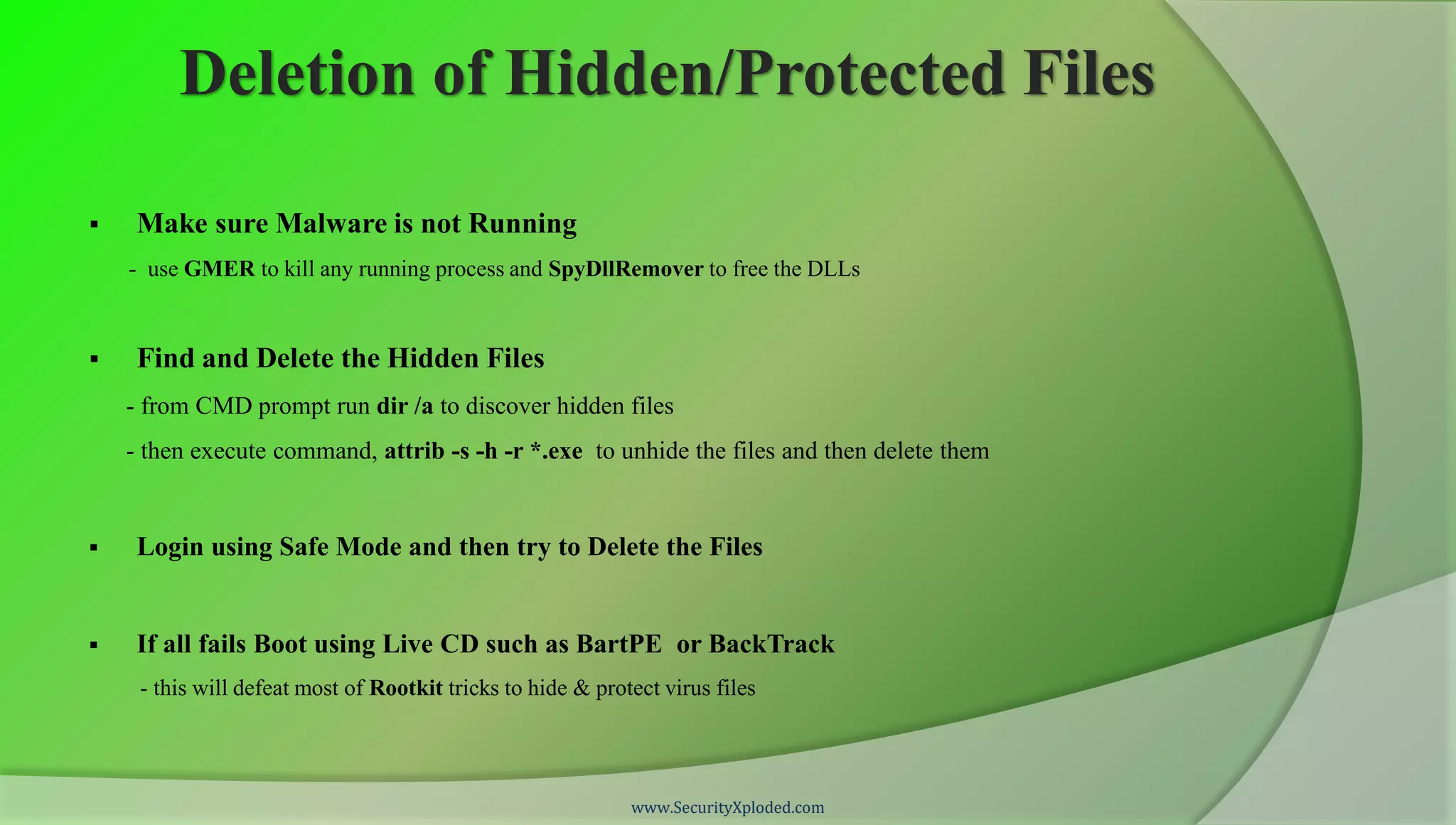
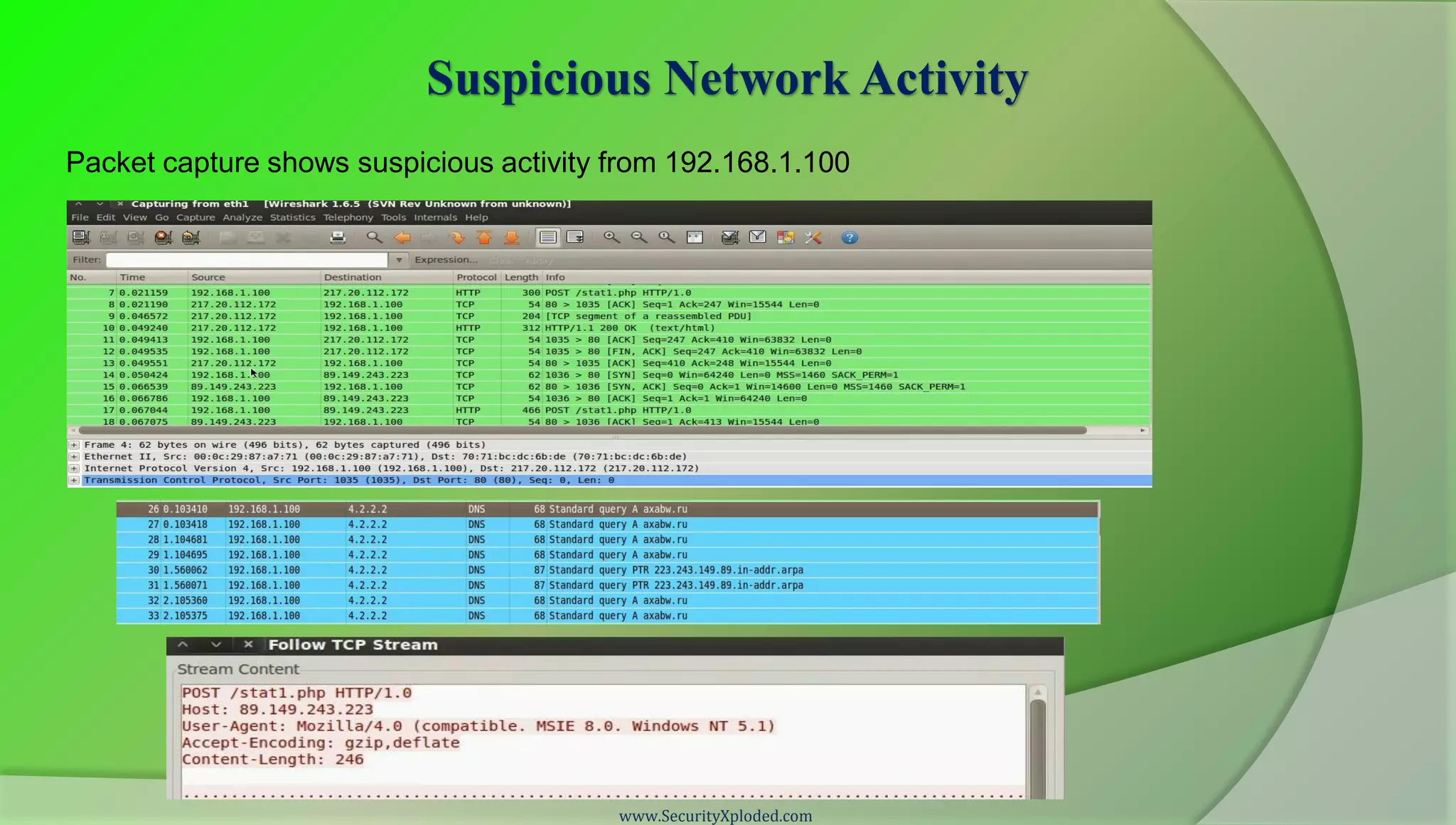
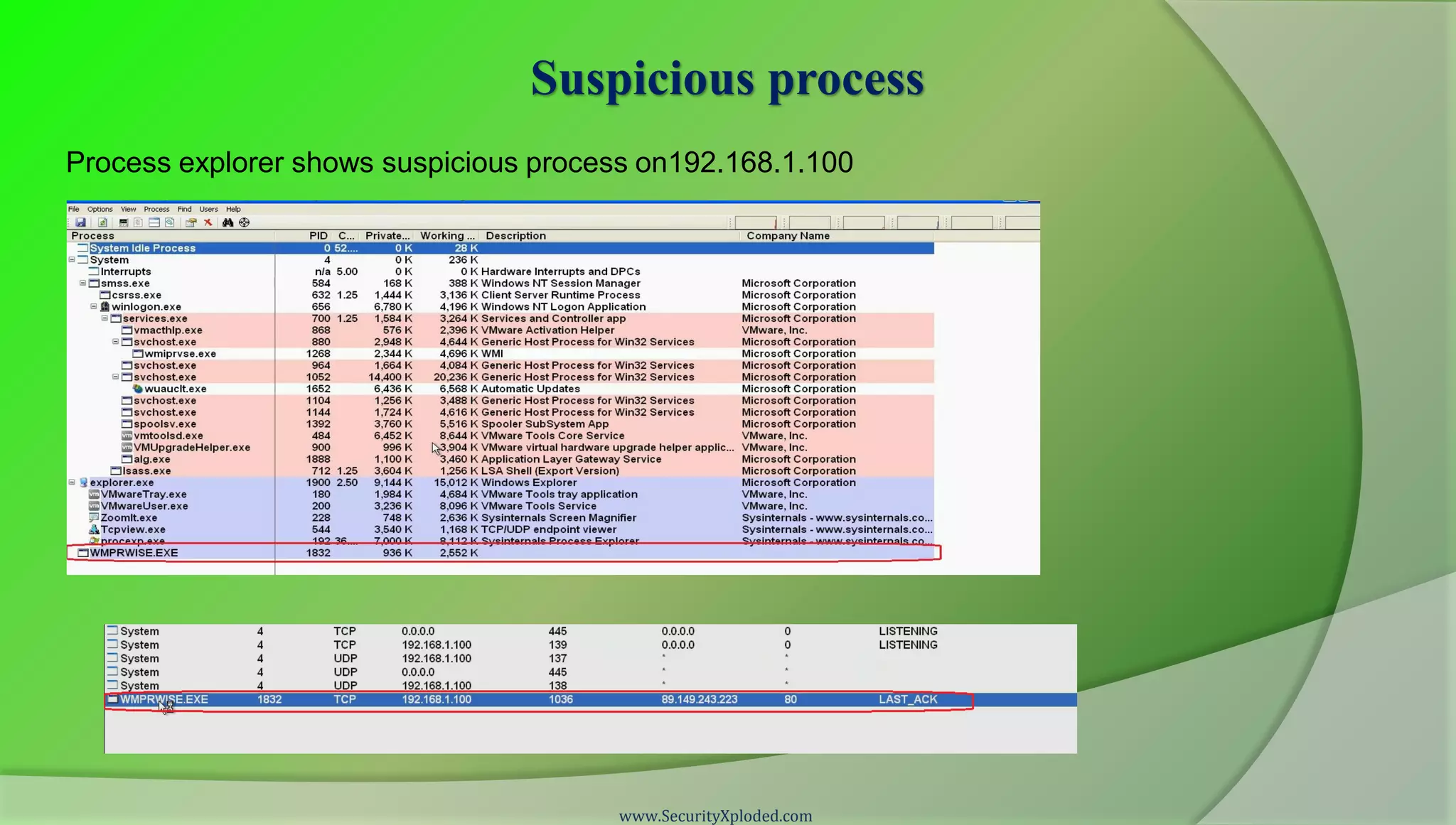
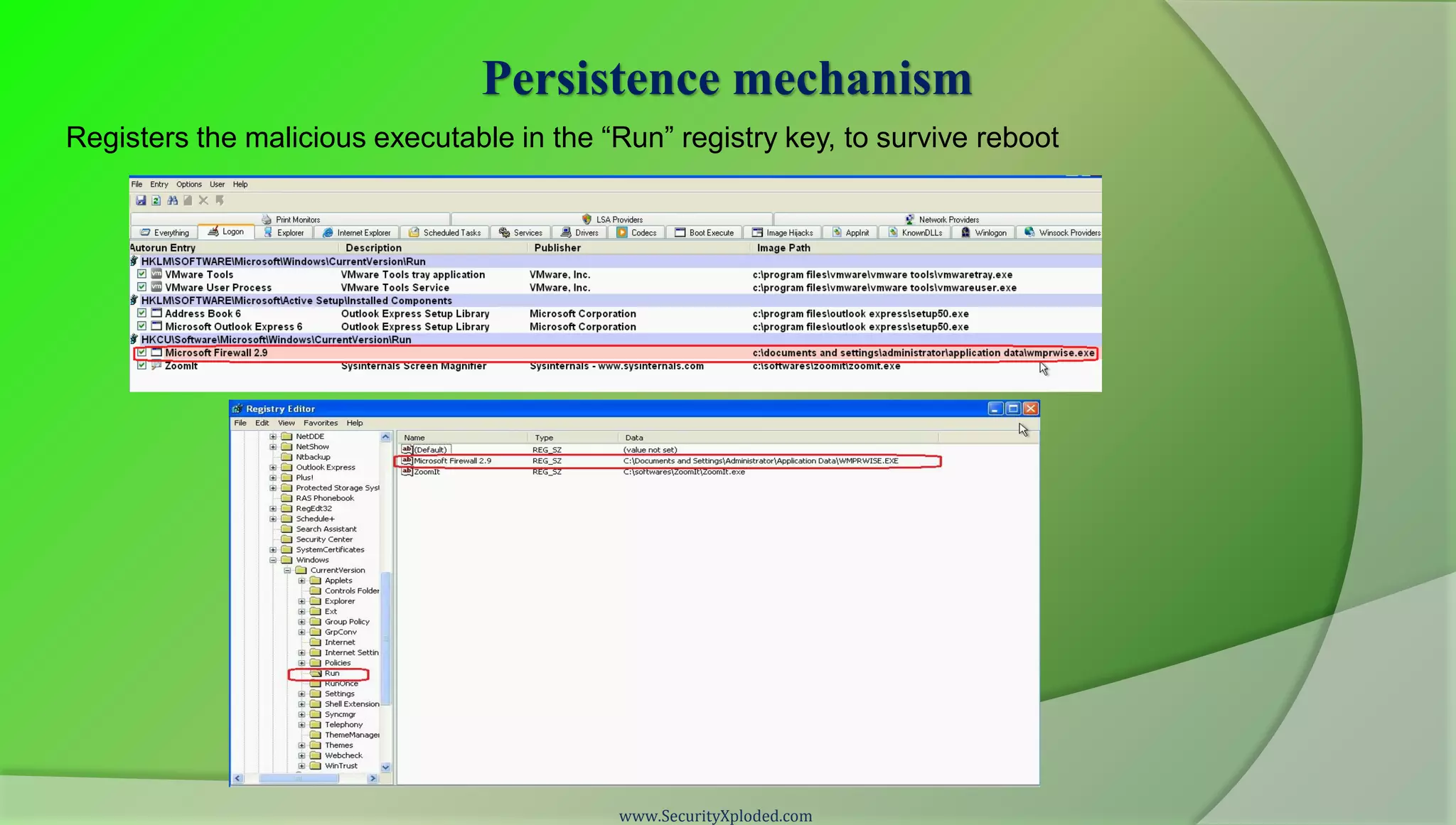
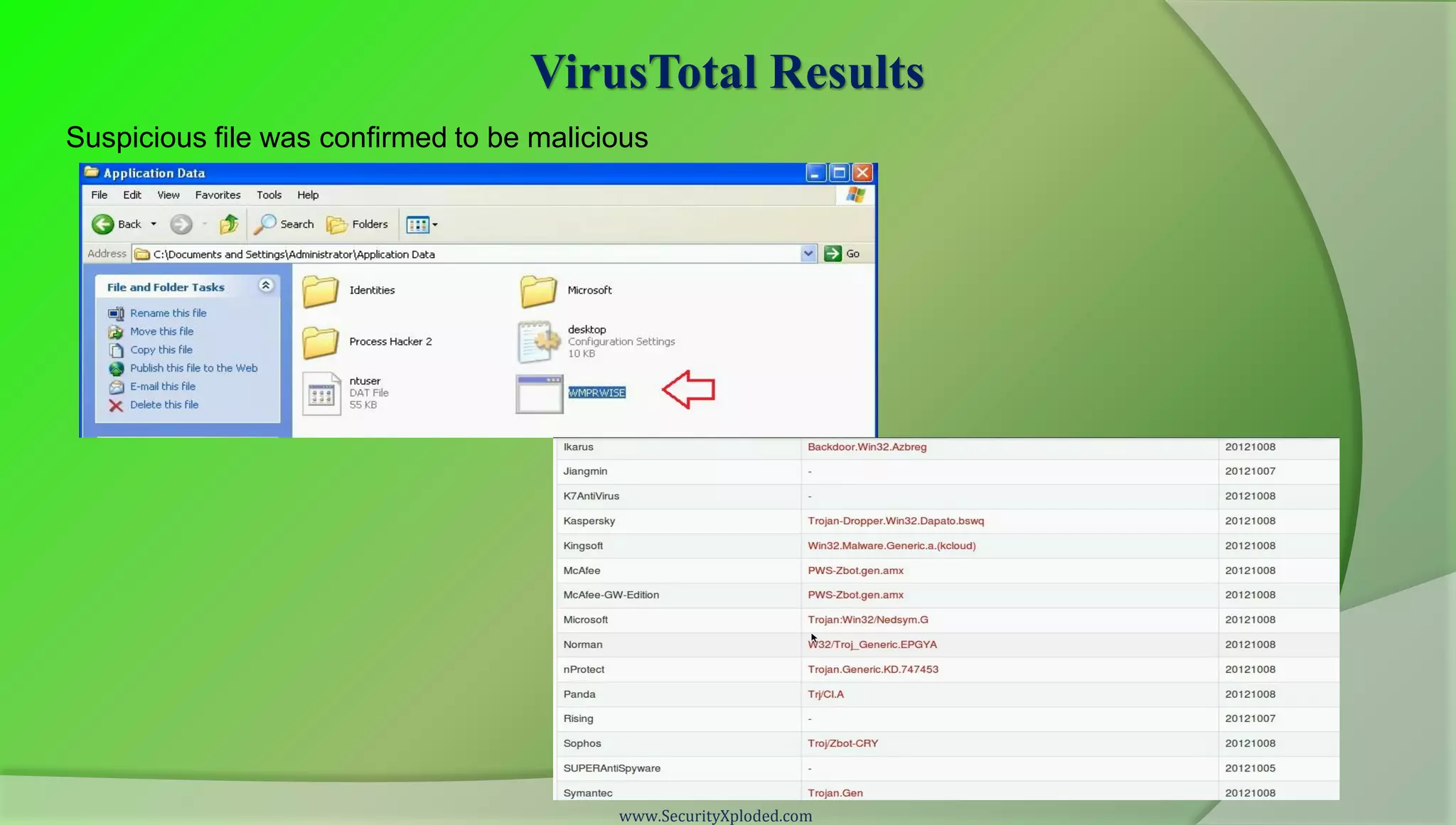
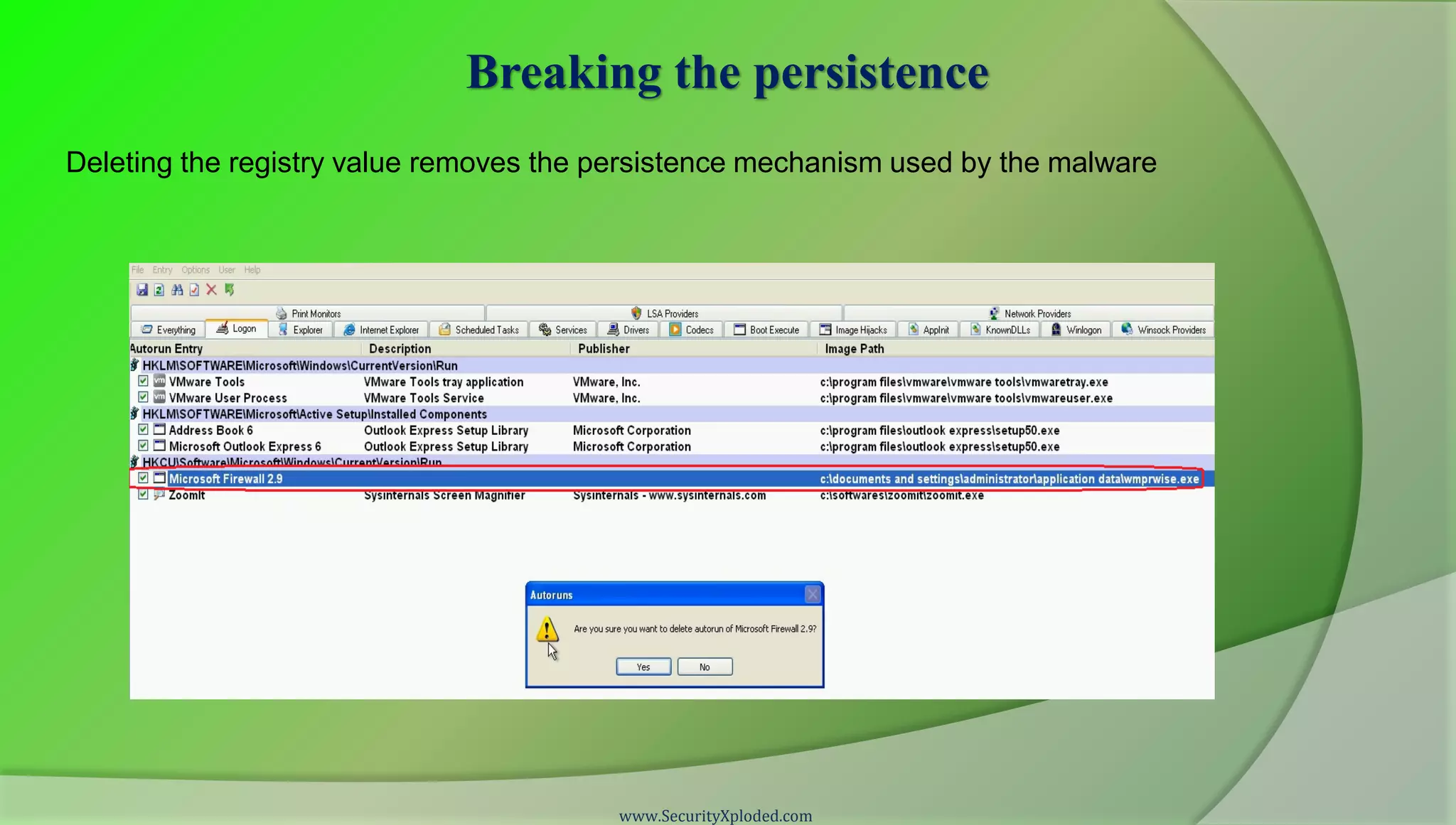
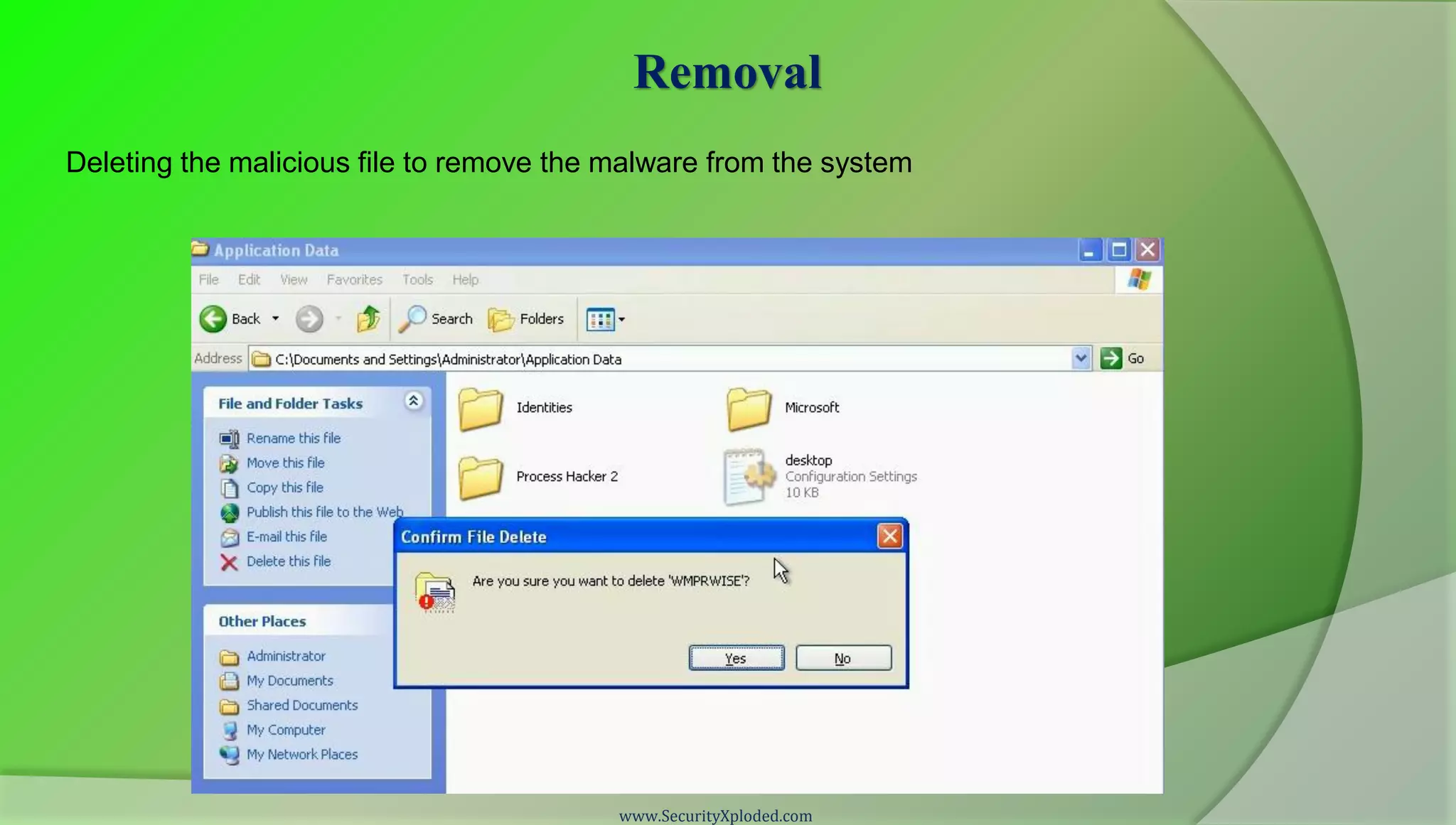
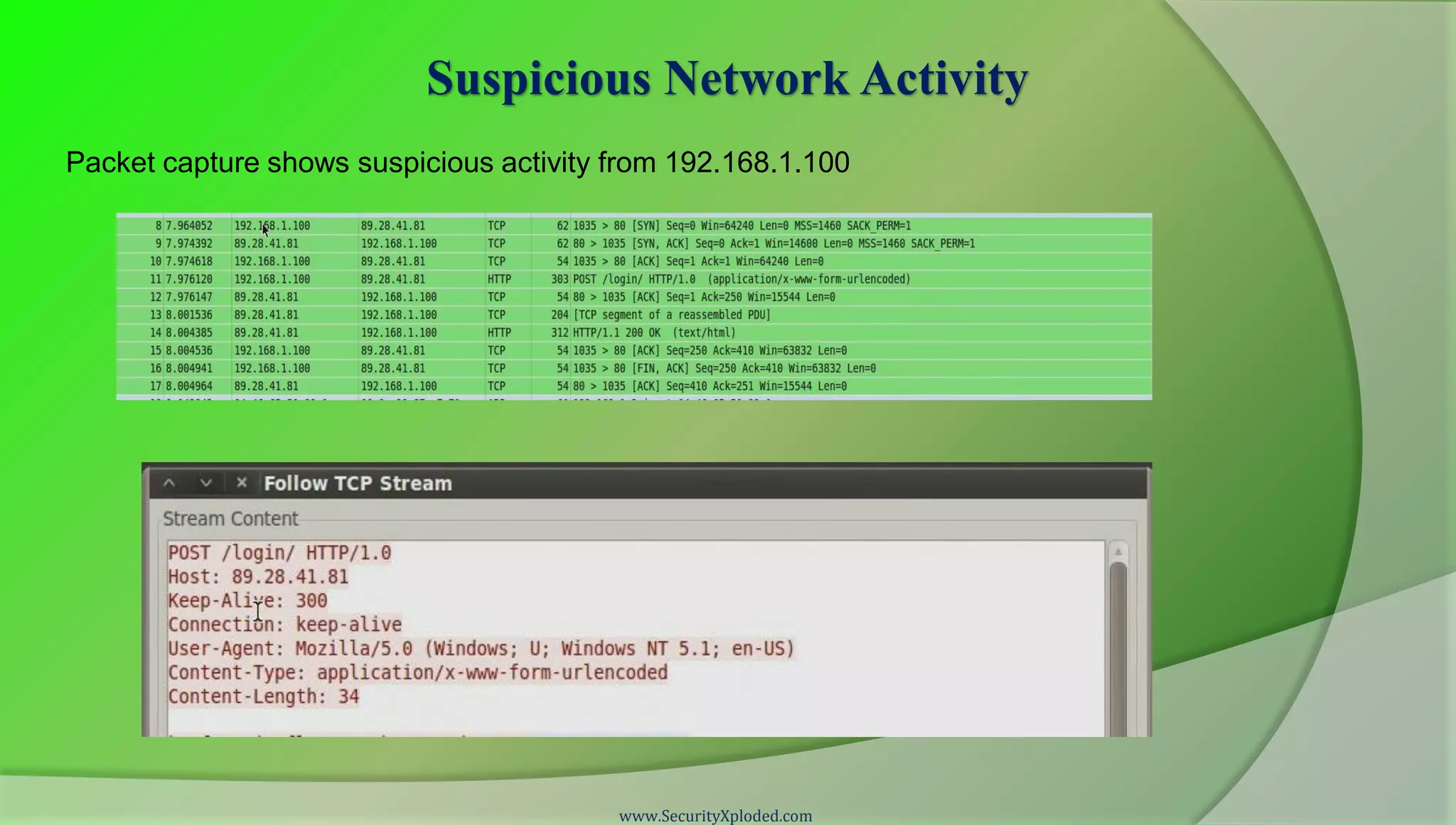
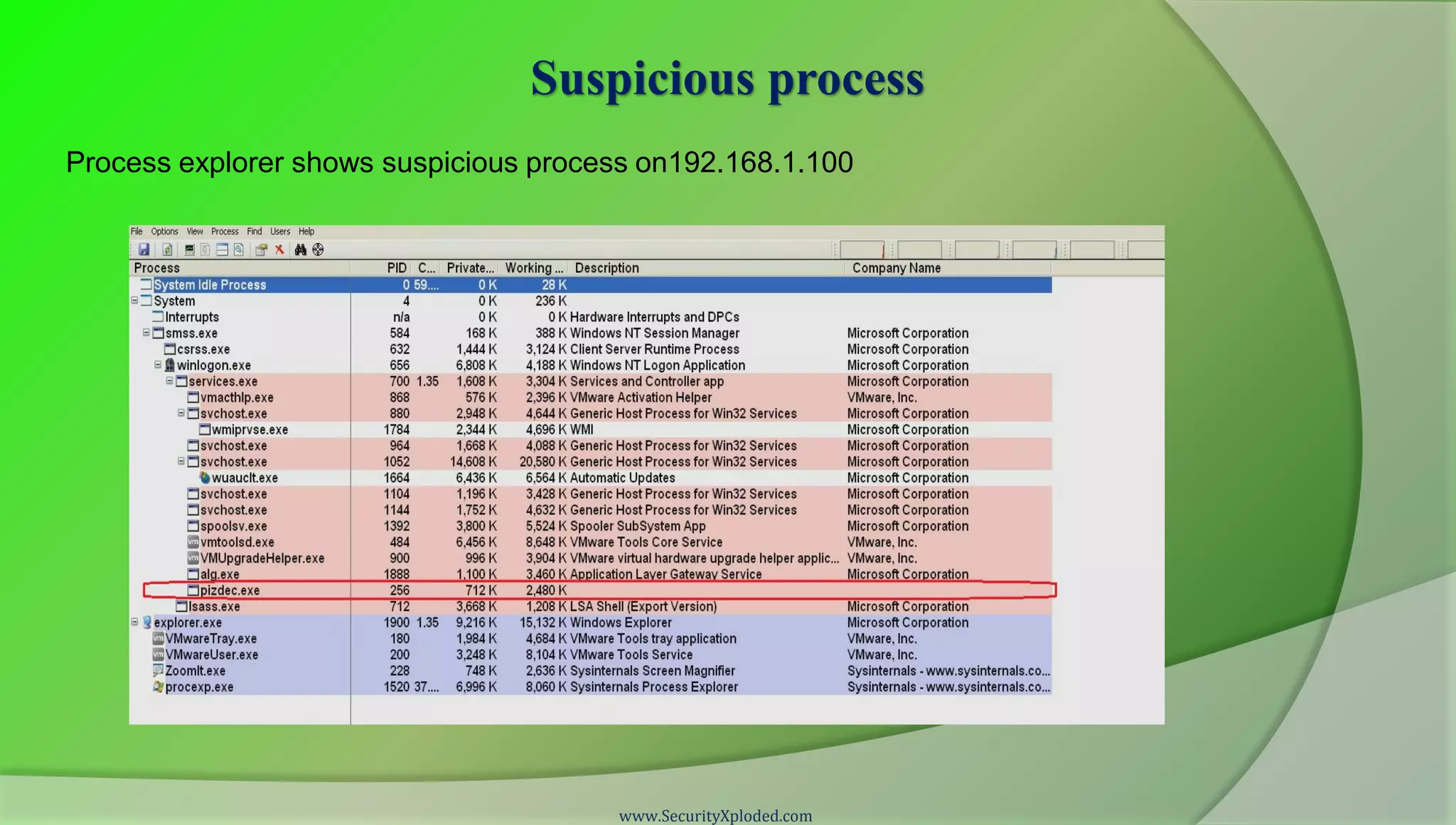
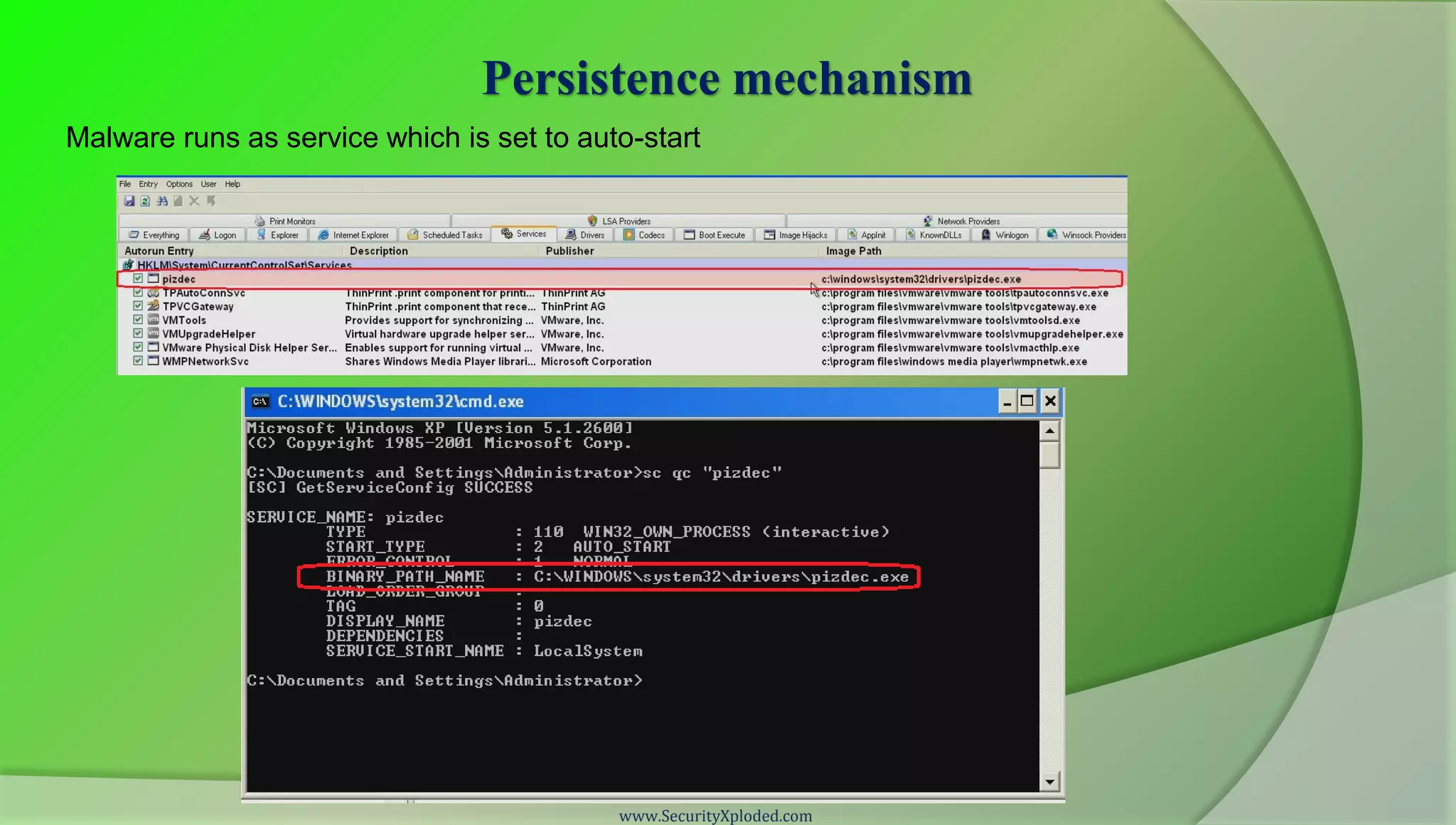
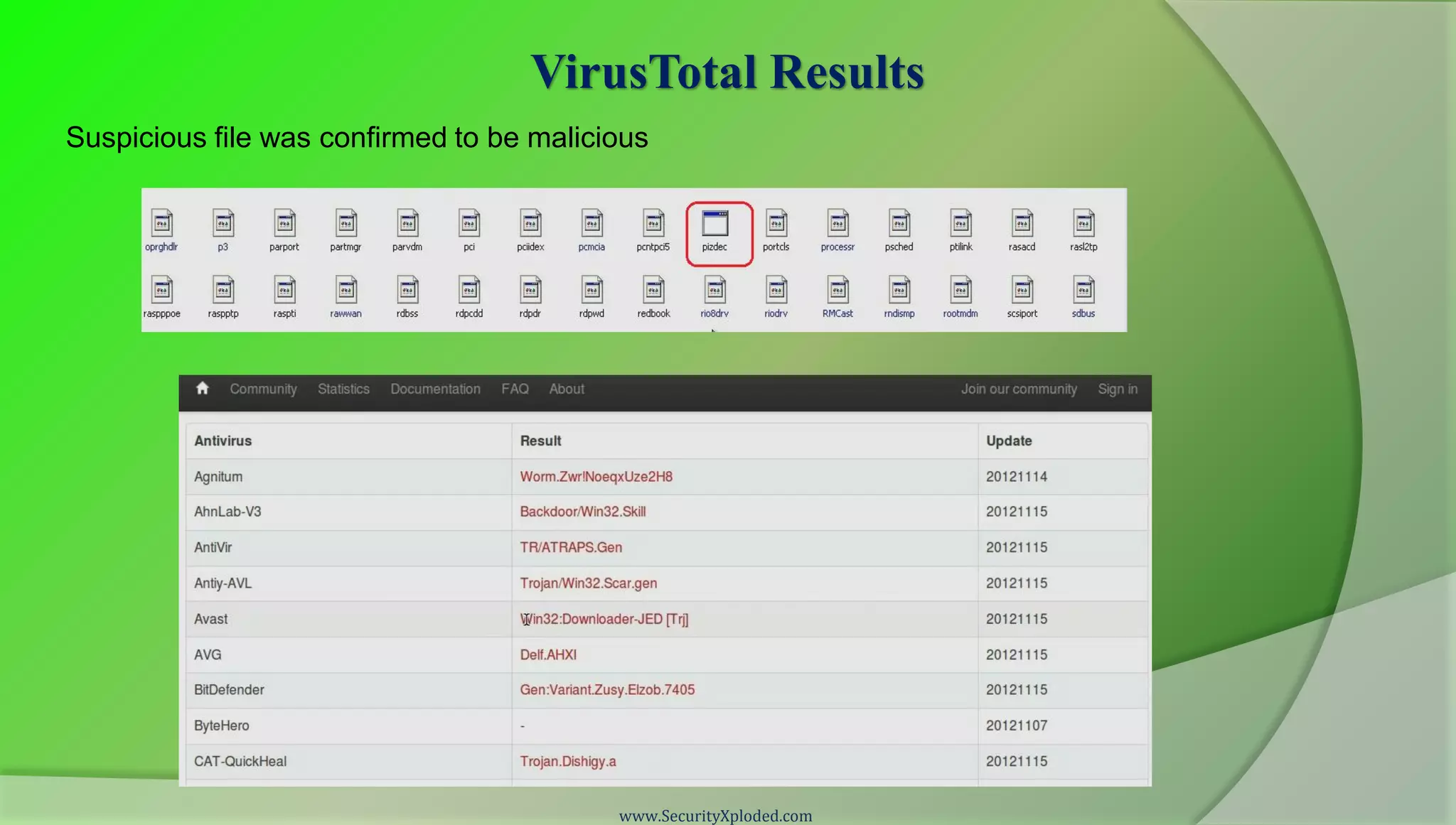
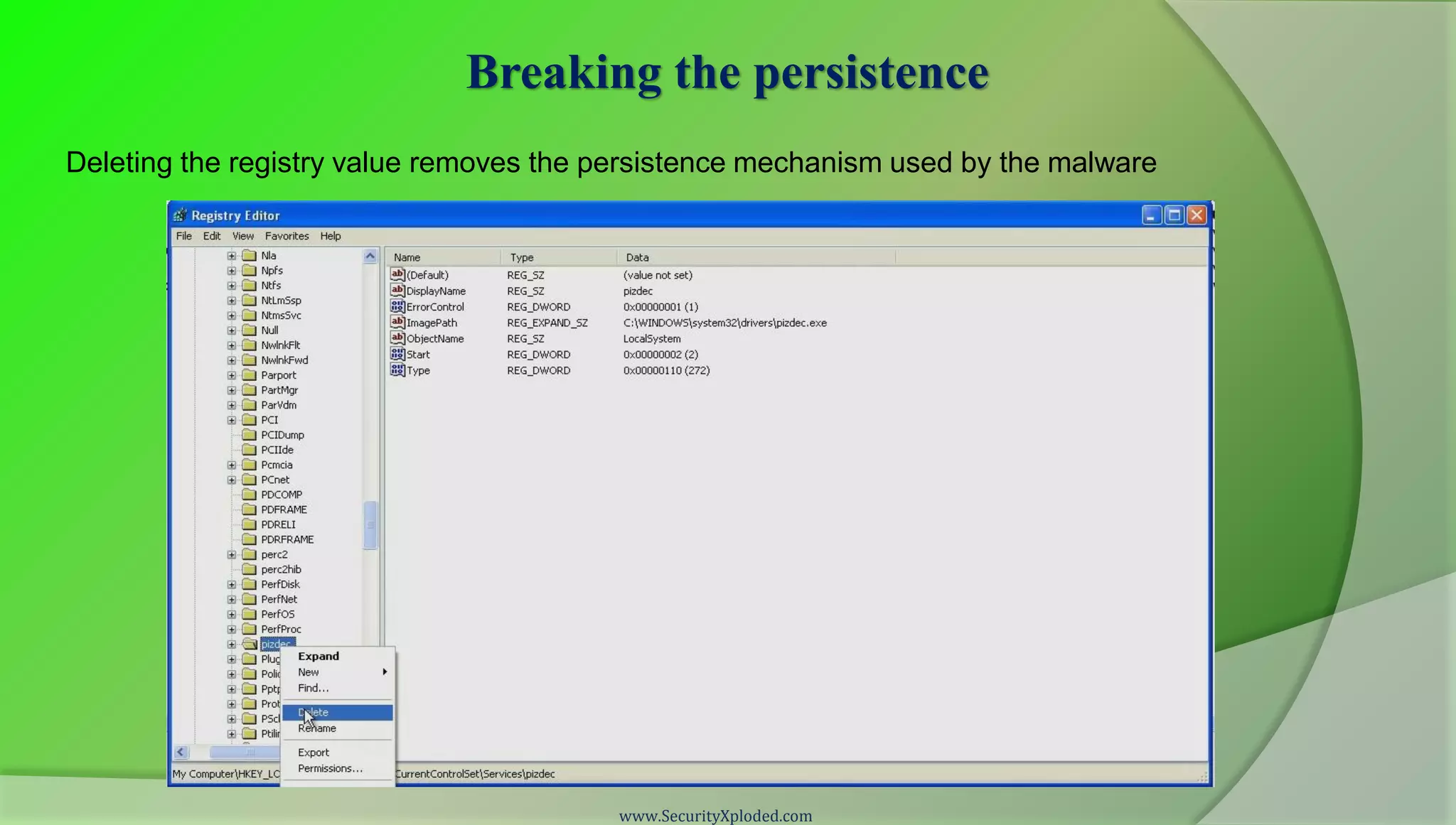
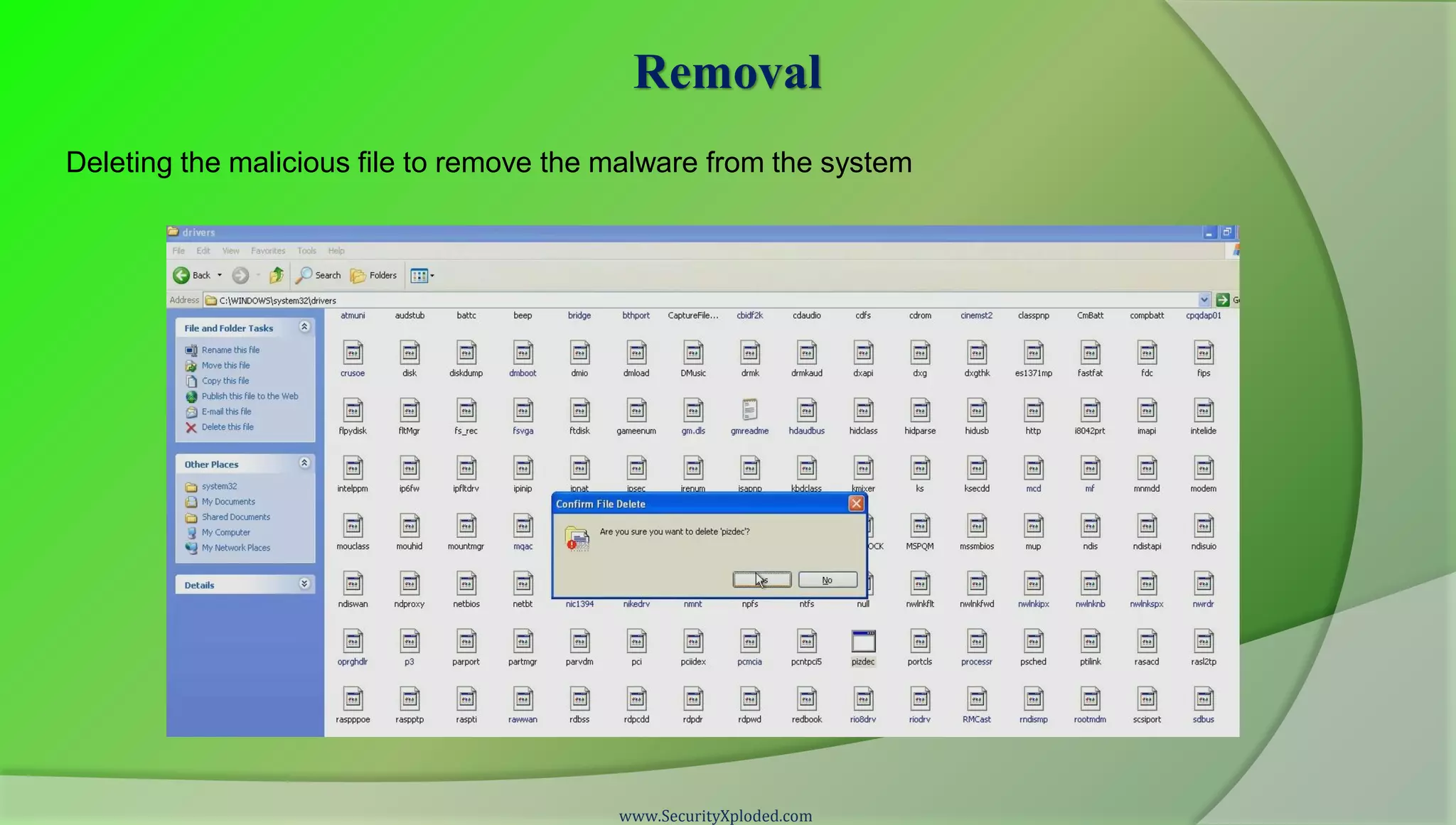
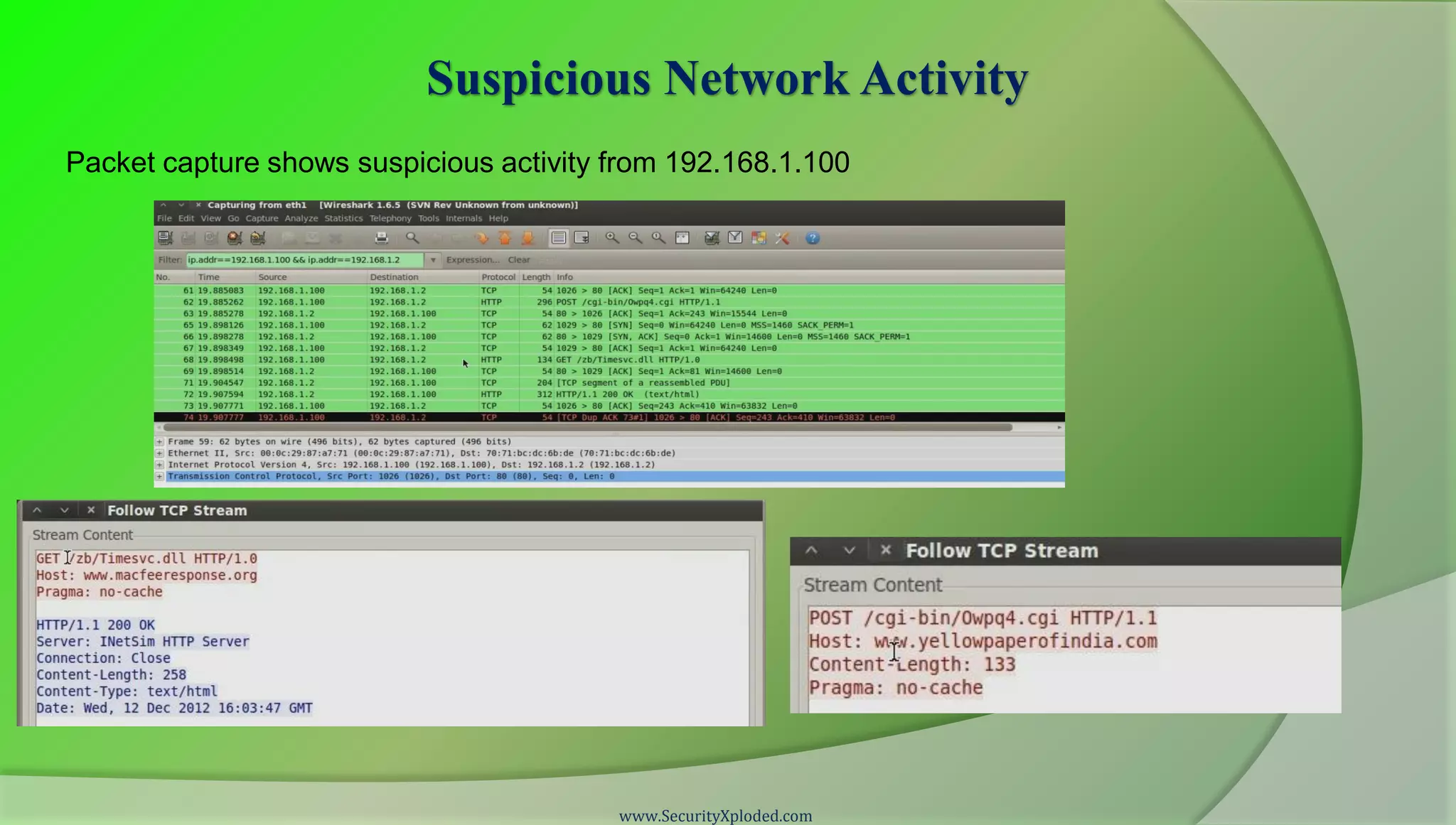
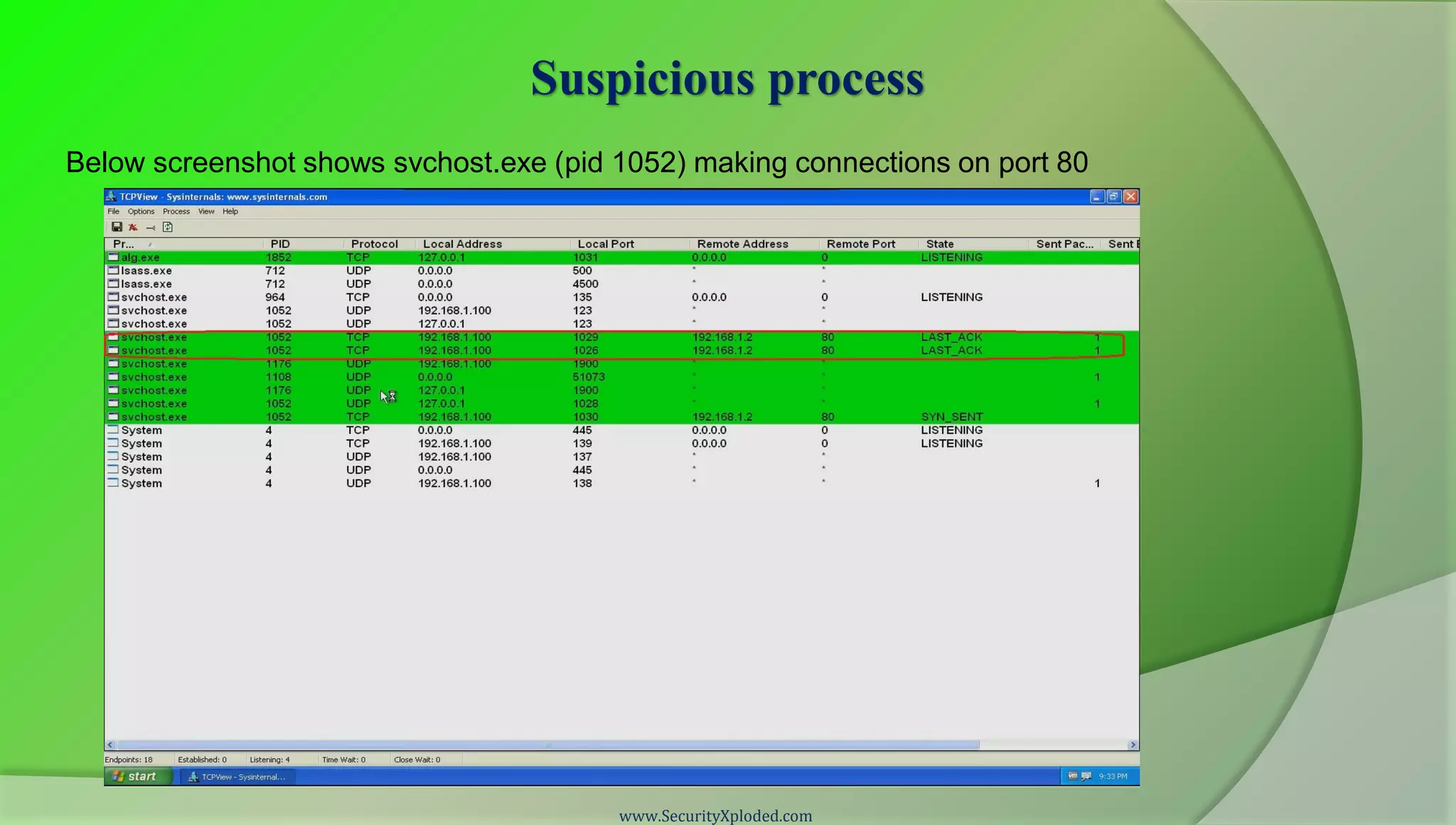
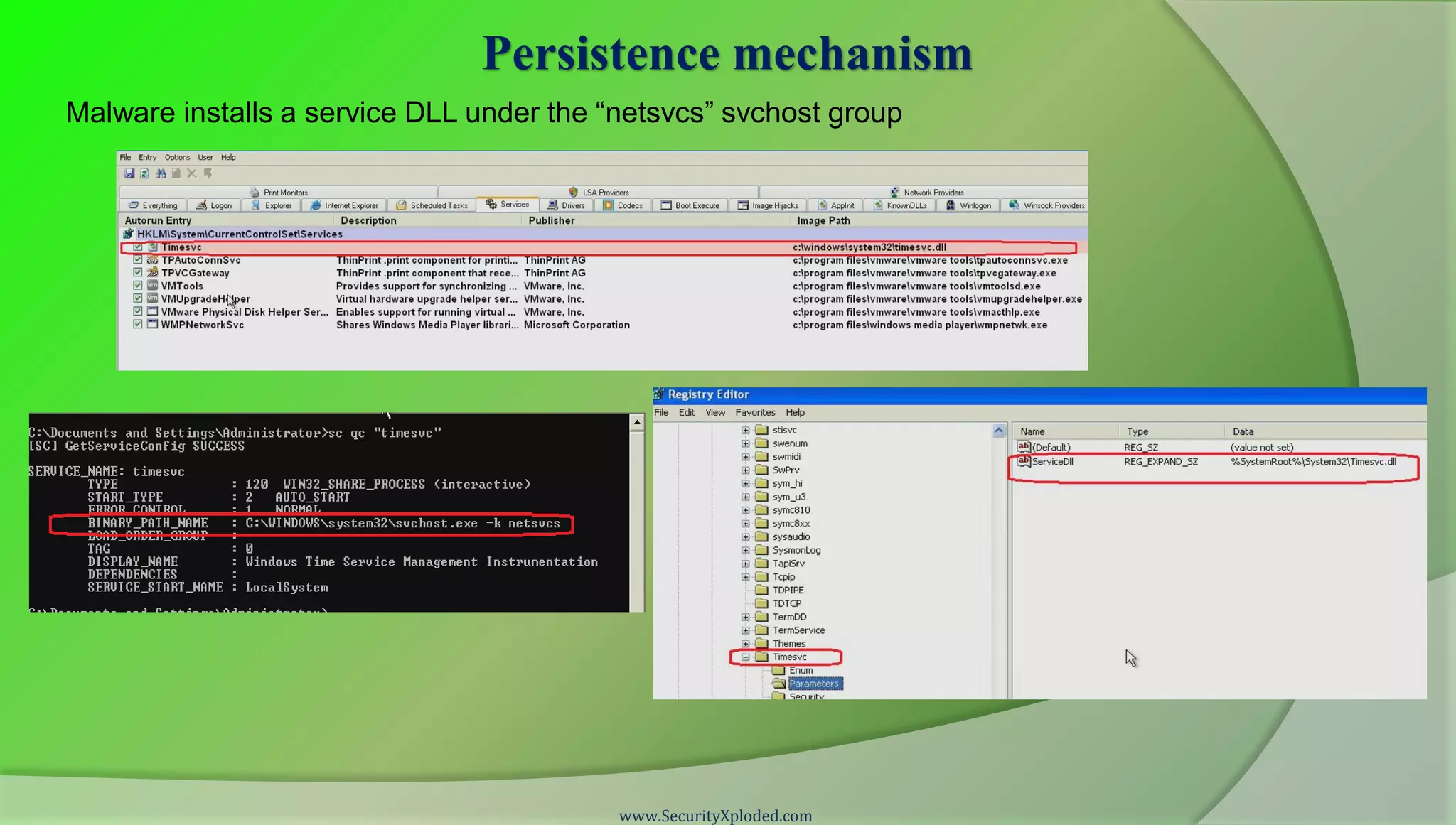
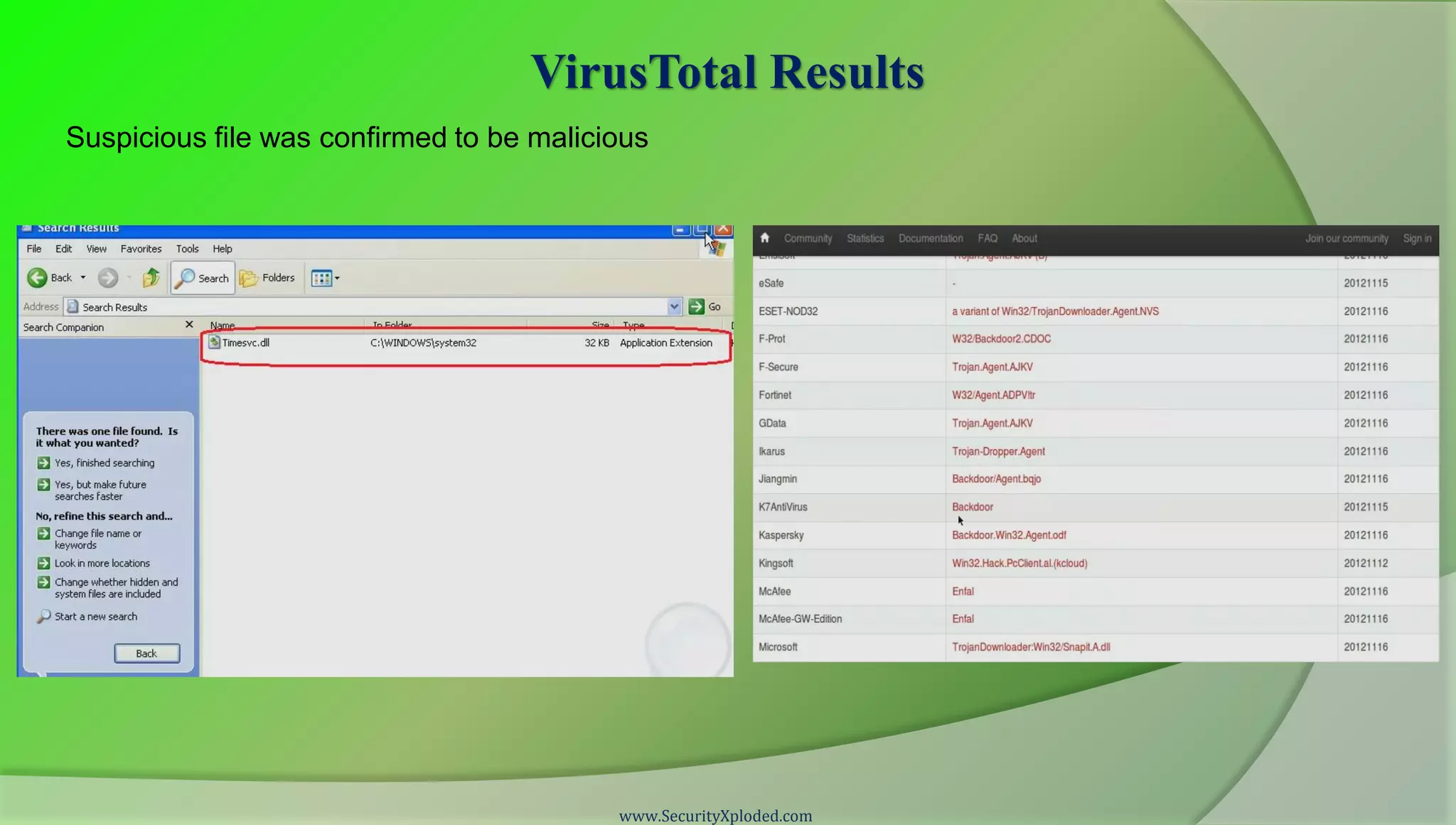
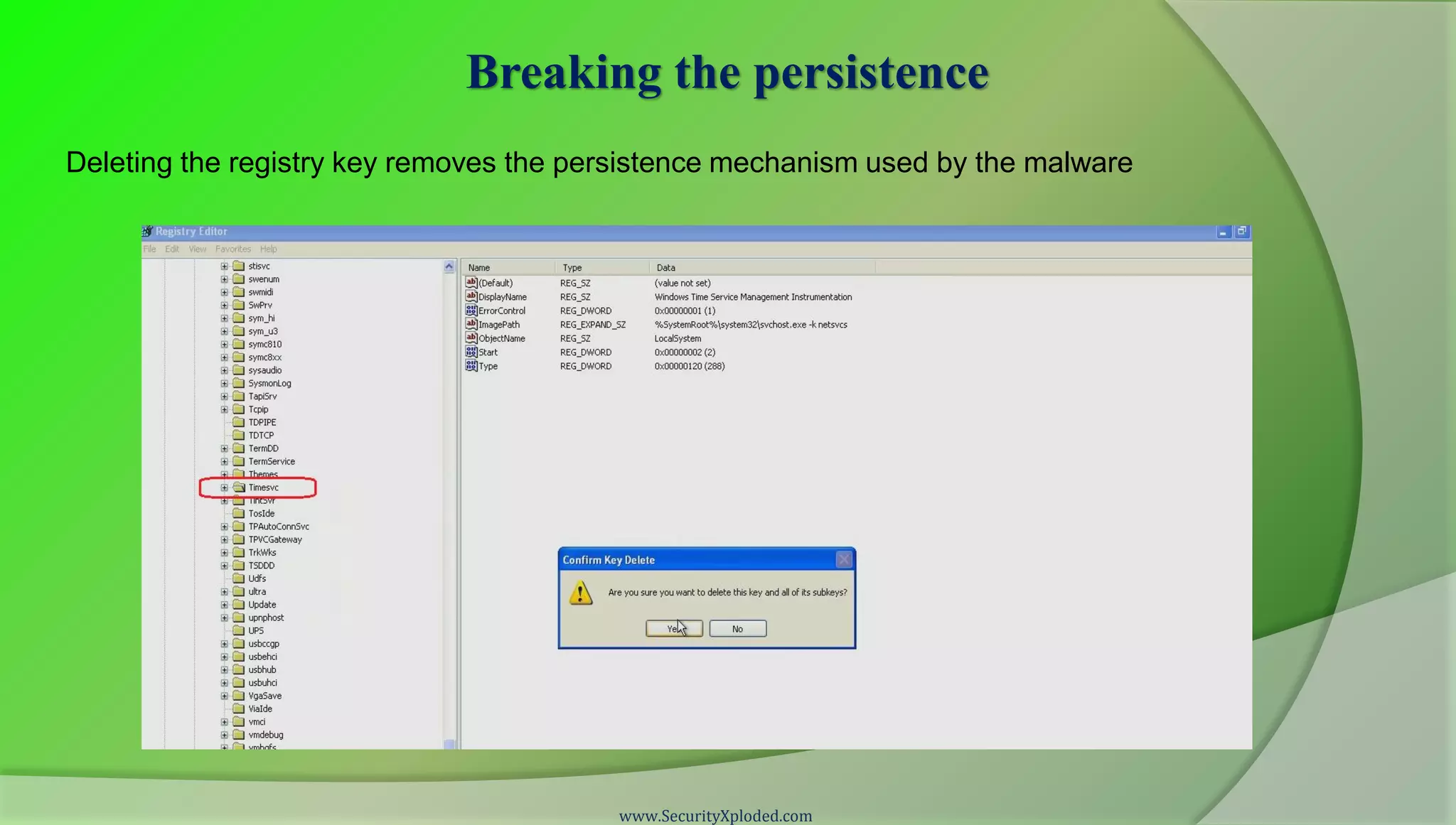
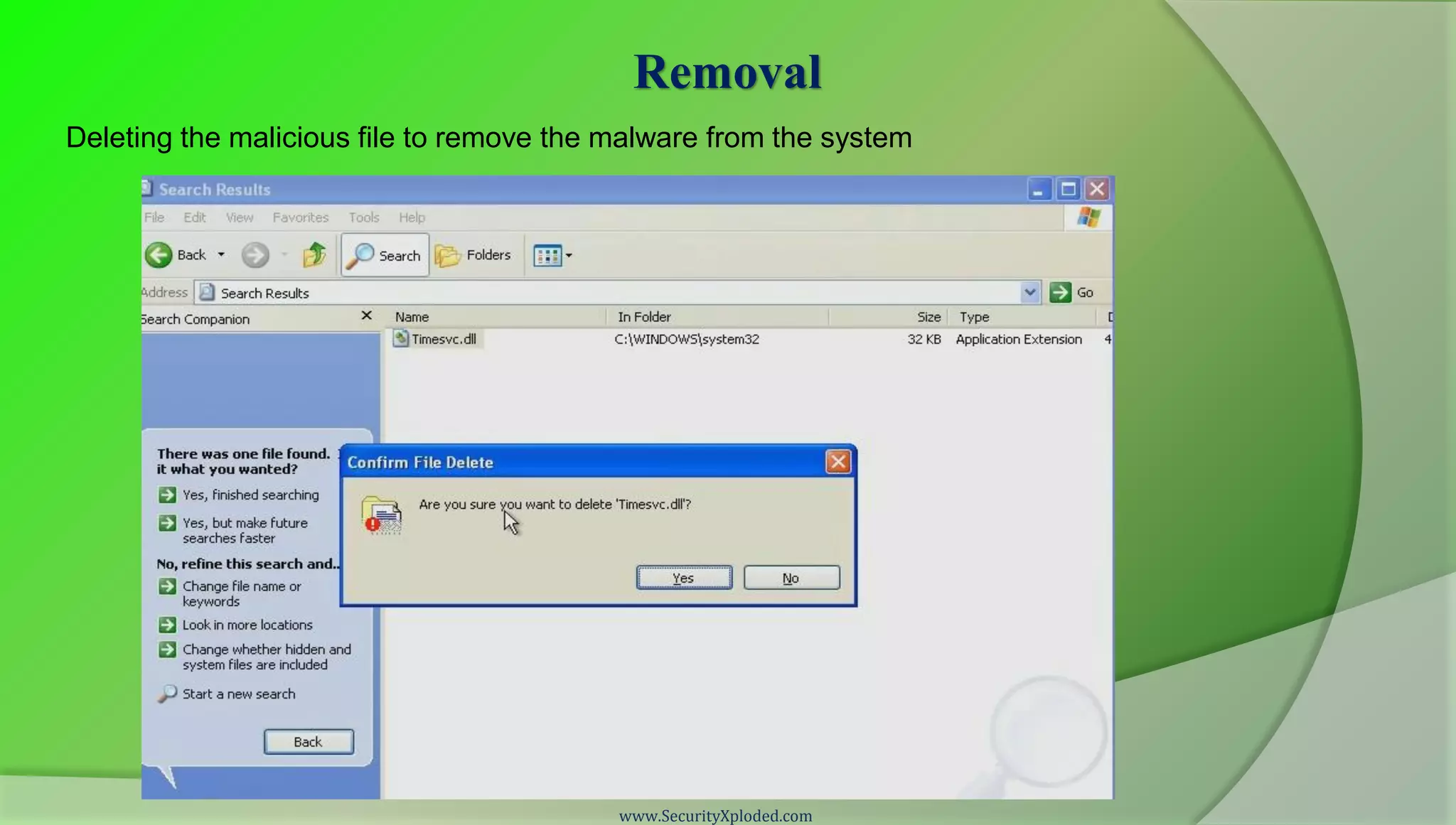
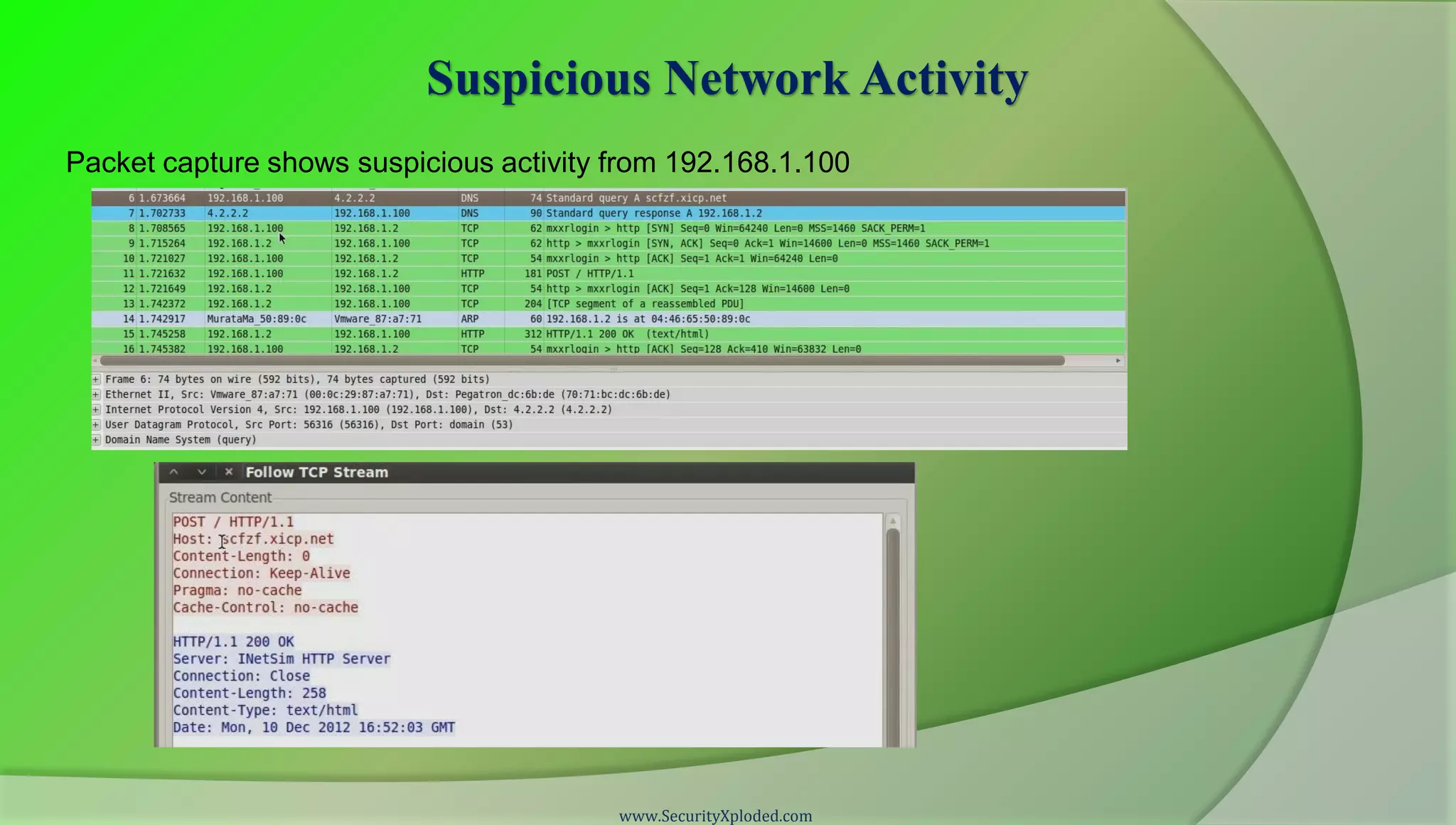
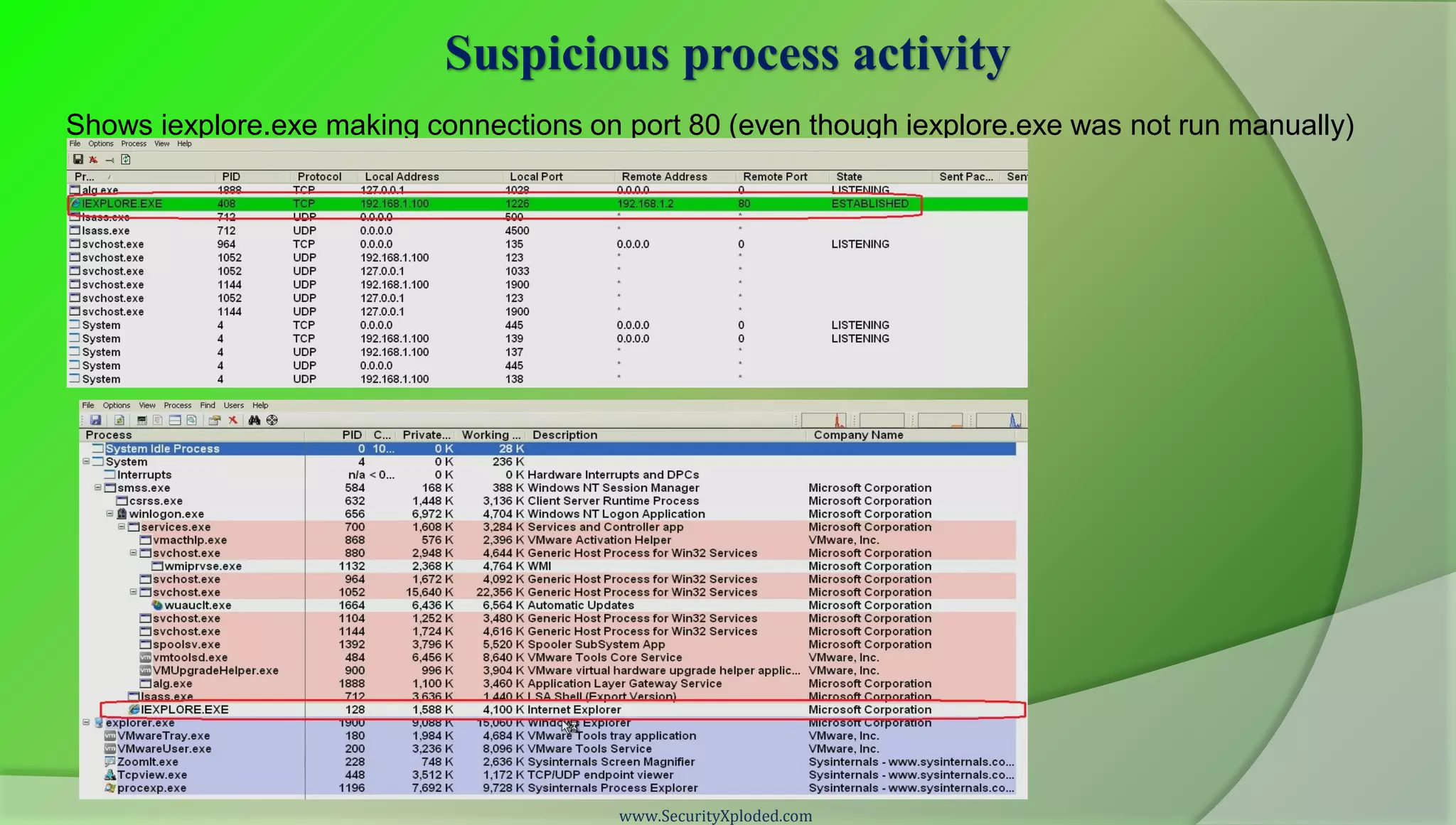
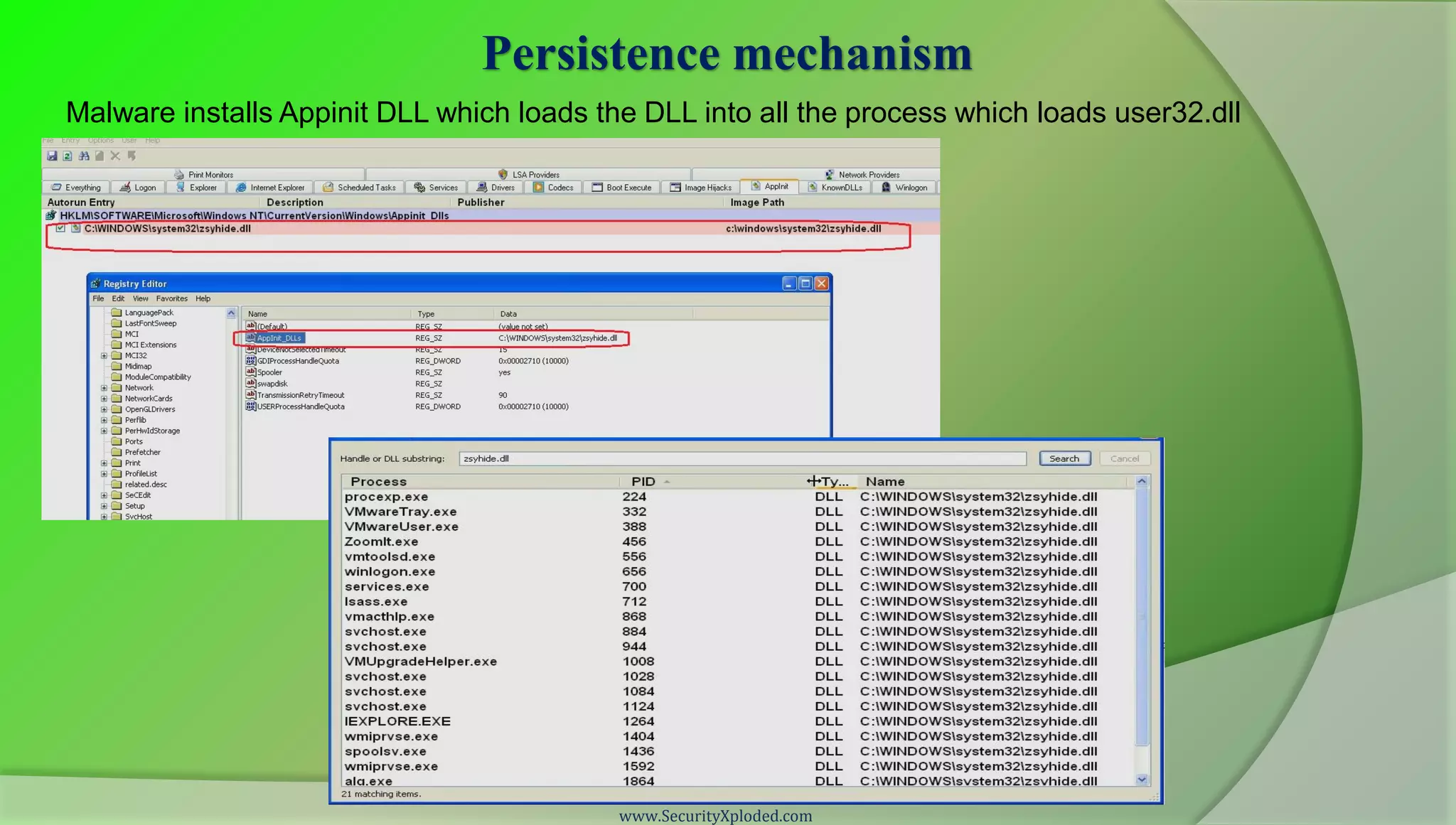
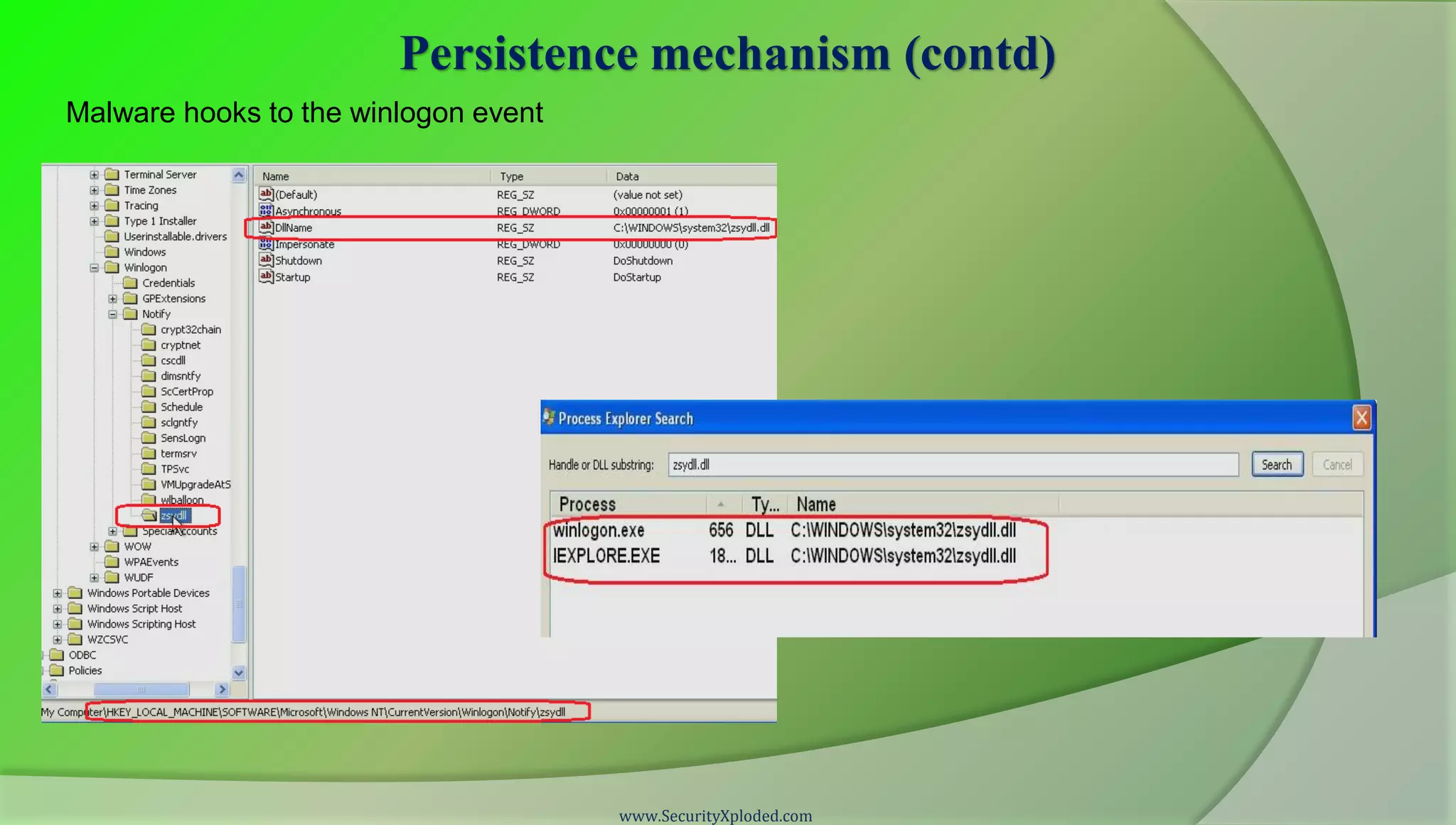
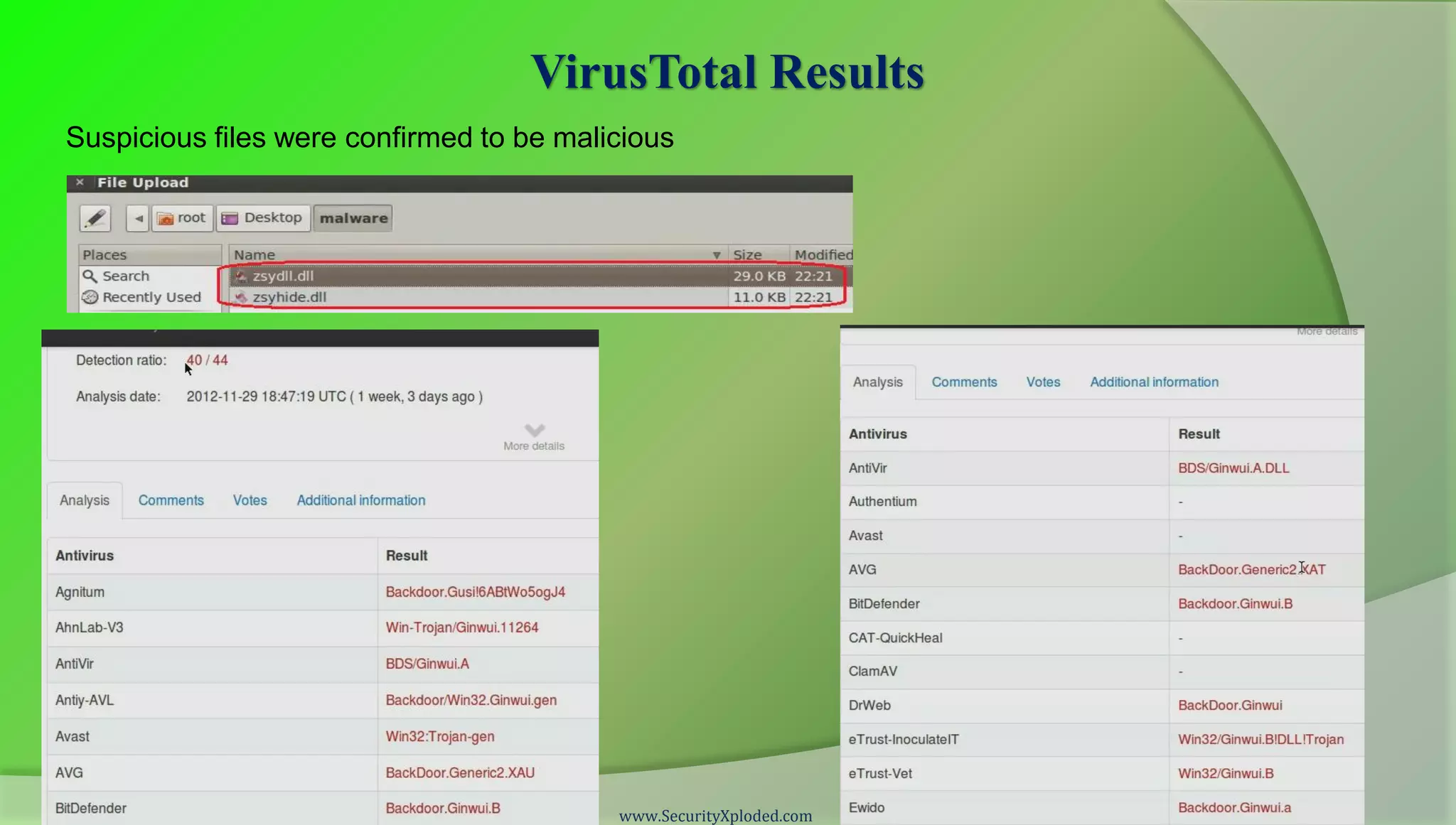
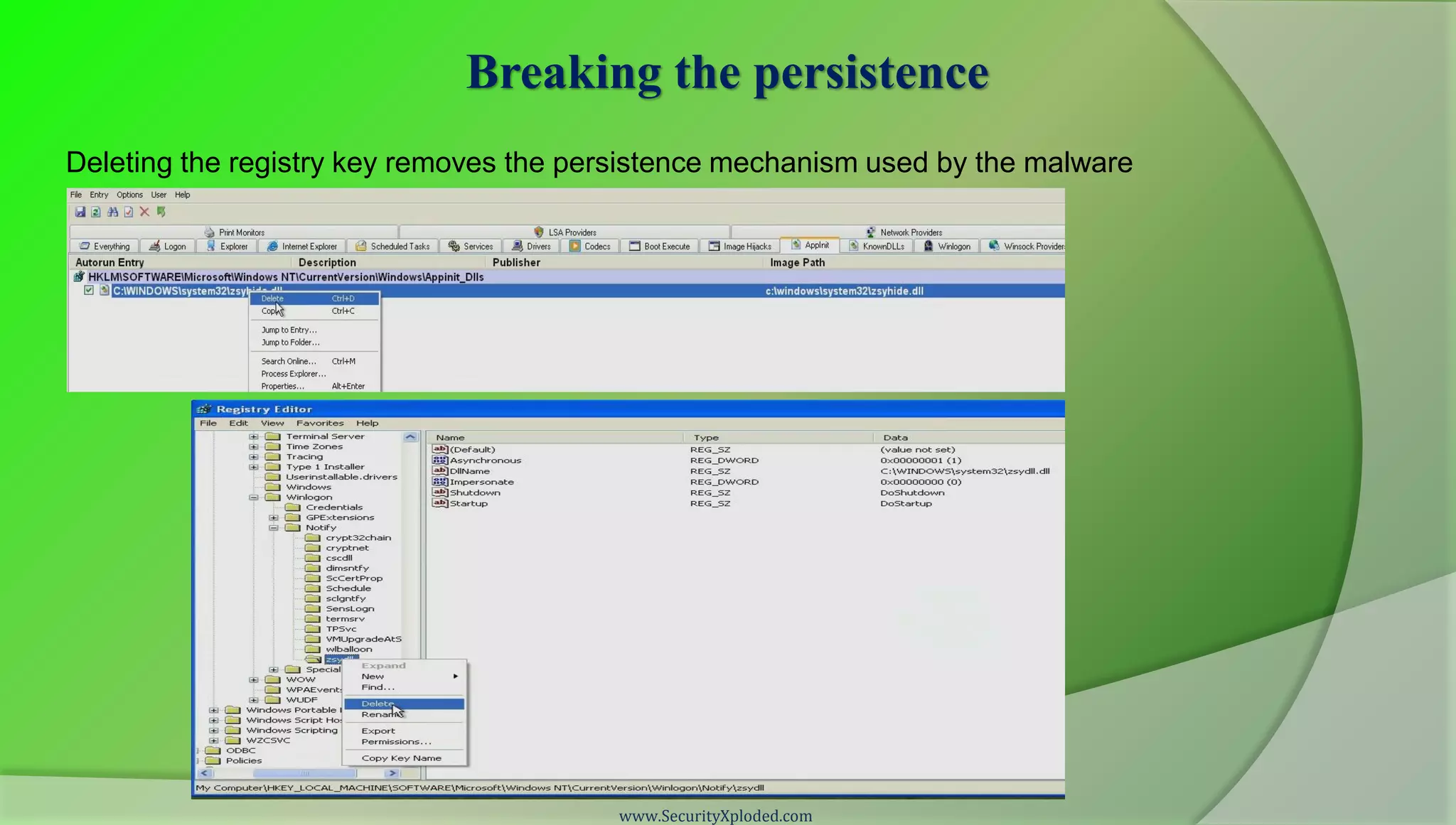
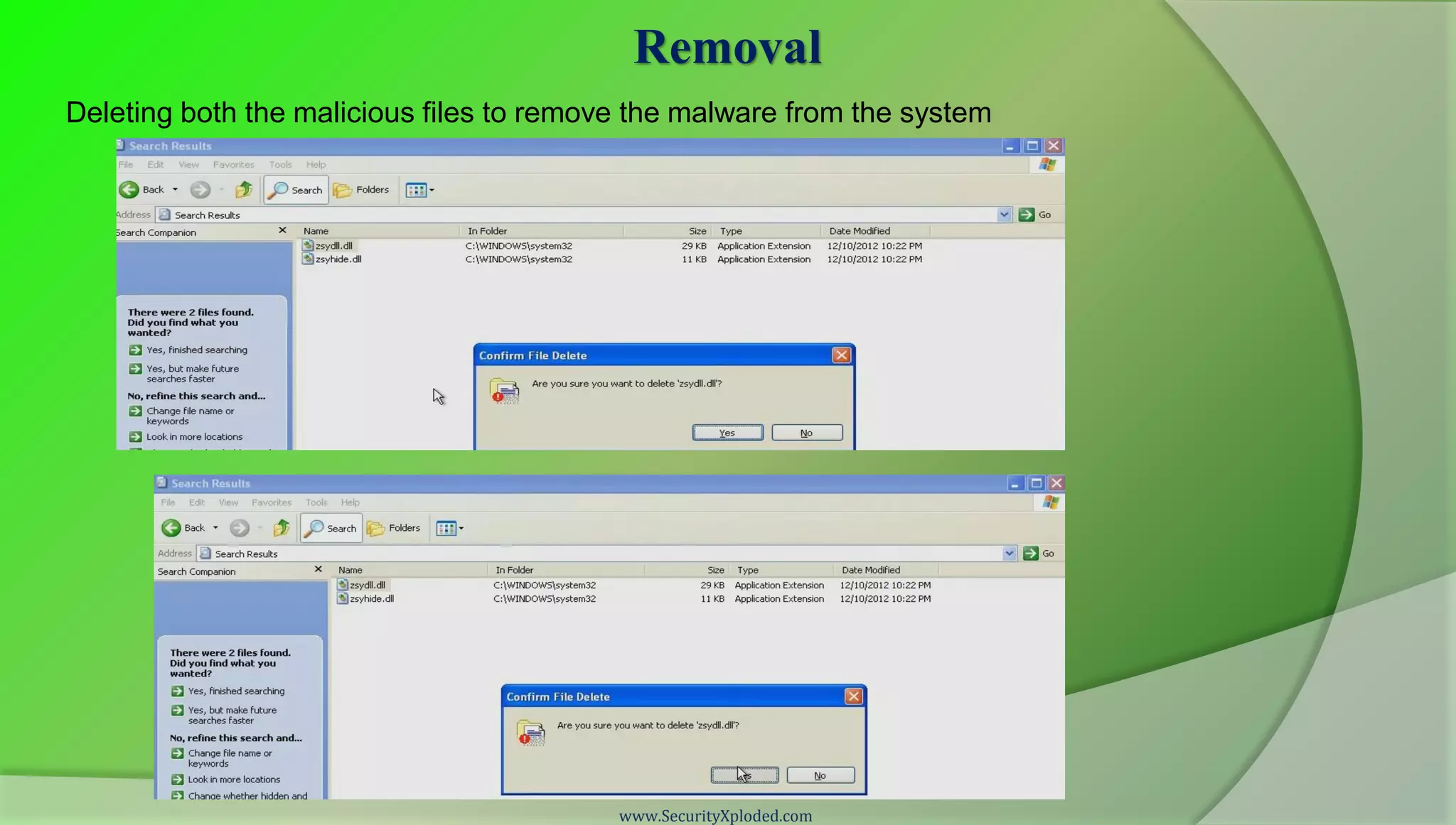
This document provides an overview of an advanced malware analysis training program. It begins with a disclaimer and acknowledgements. It then outlines the course contents, including detection and removal of malware, common persistence mechanisms, and four malware analysis demonstrations. The demonstrations show identifying suspicious network activity and processes, determining the persistence mechanism, using VirusTotal to validate files as malicious, breaking the persistence, and removing the malware from the system.