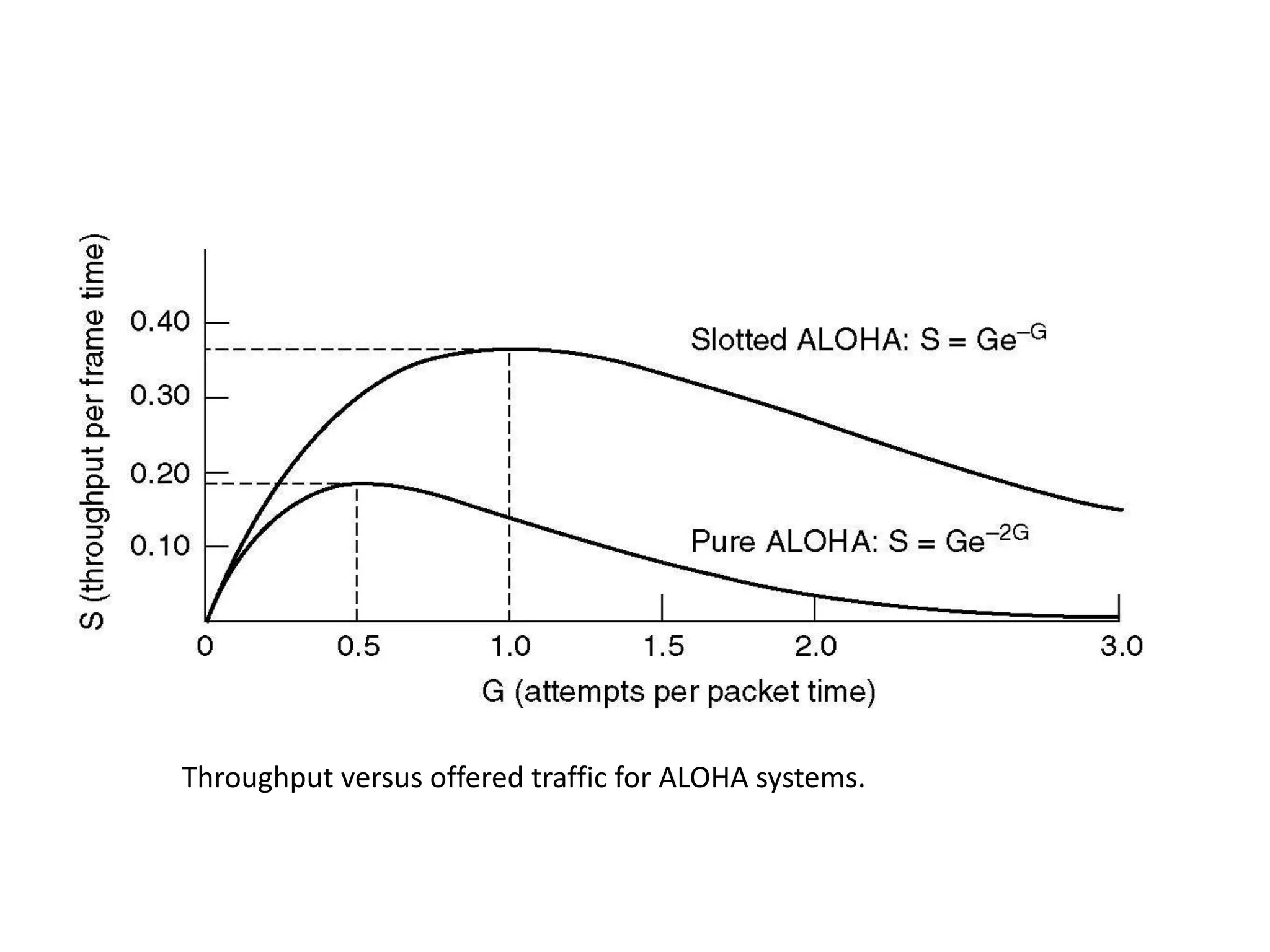
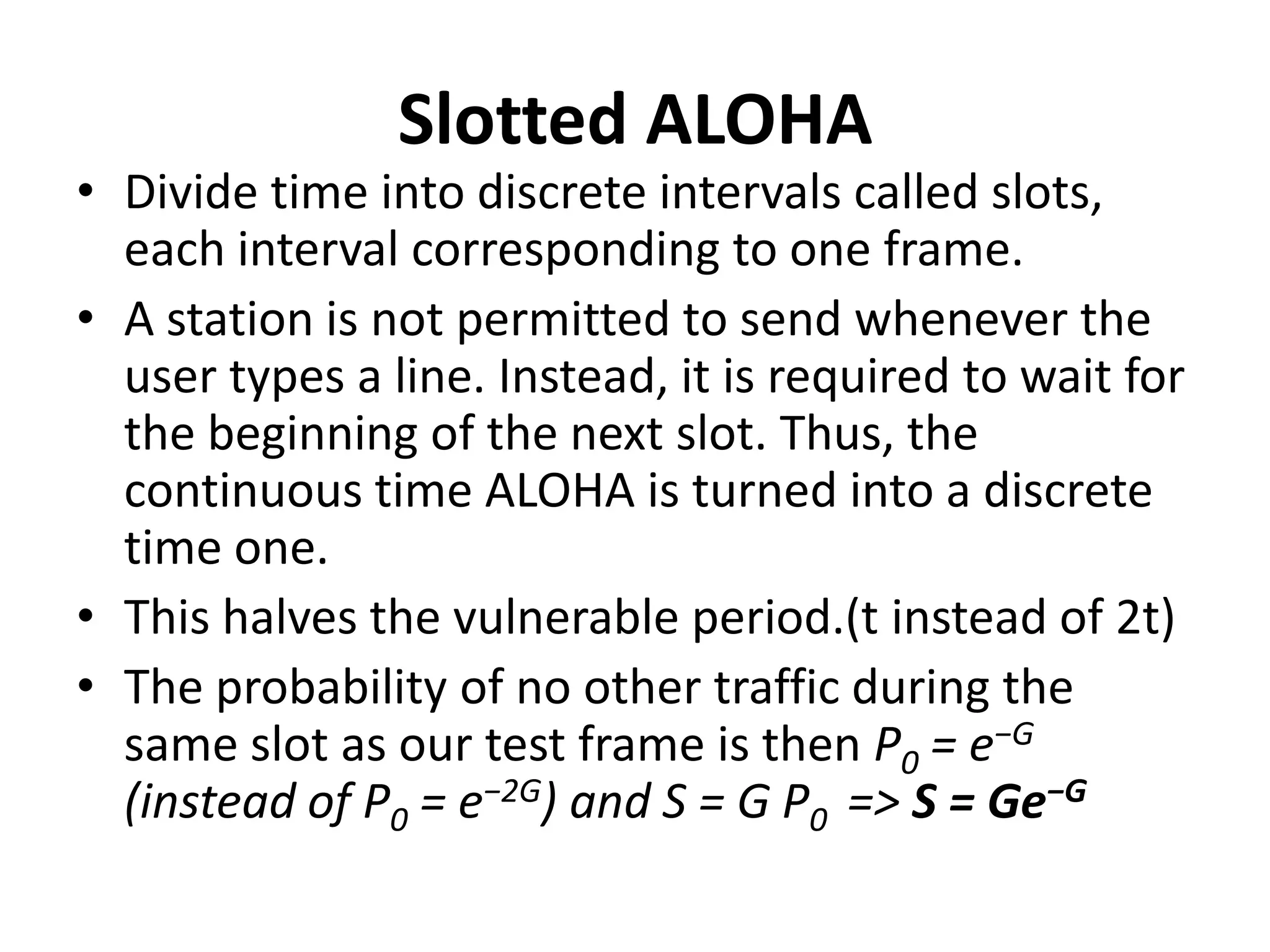
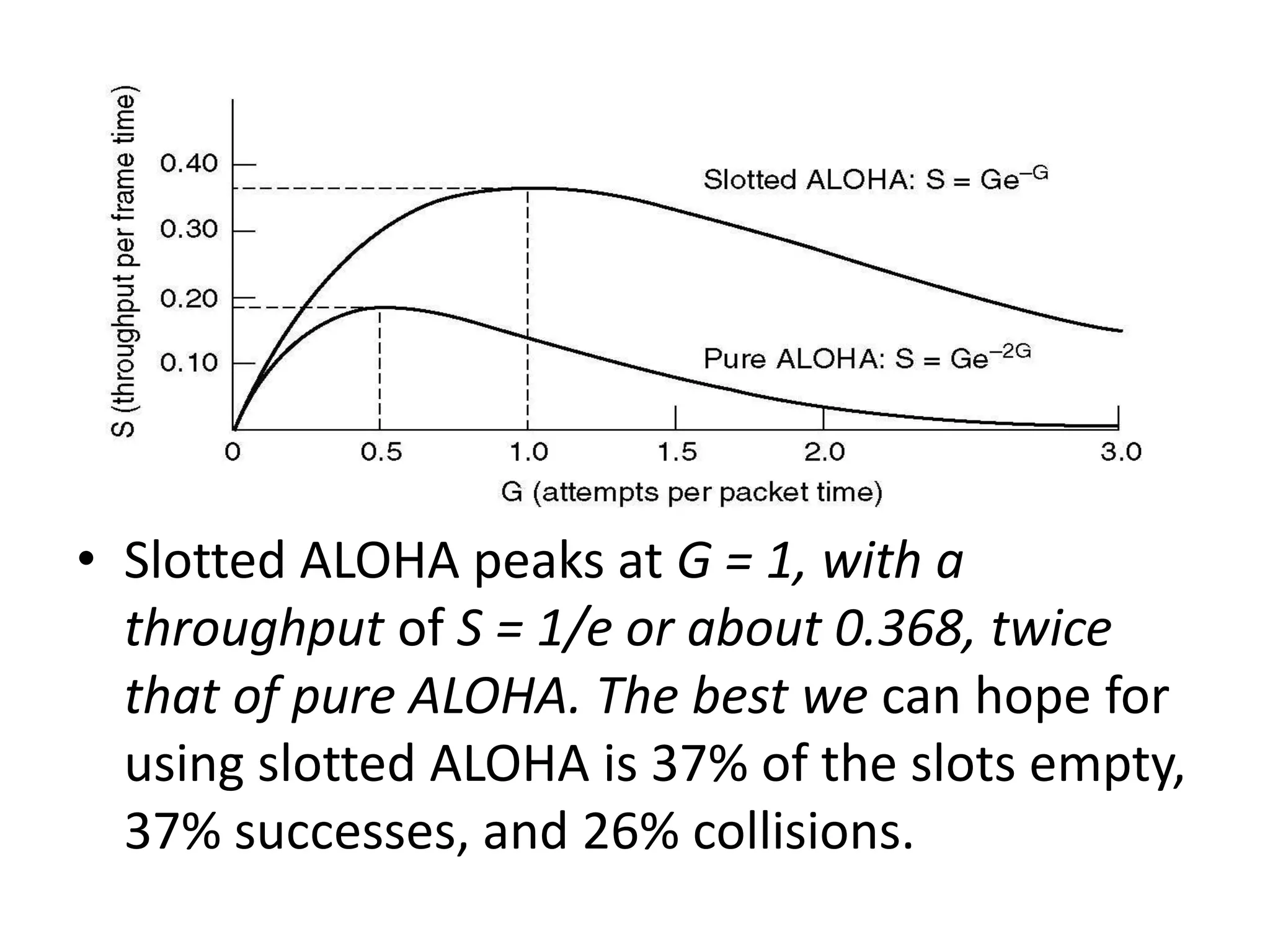
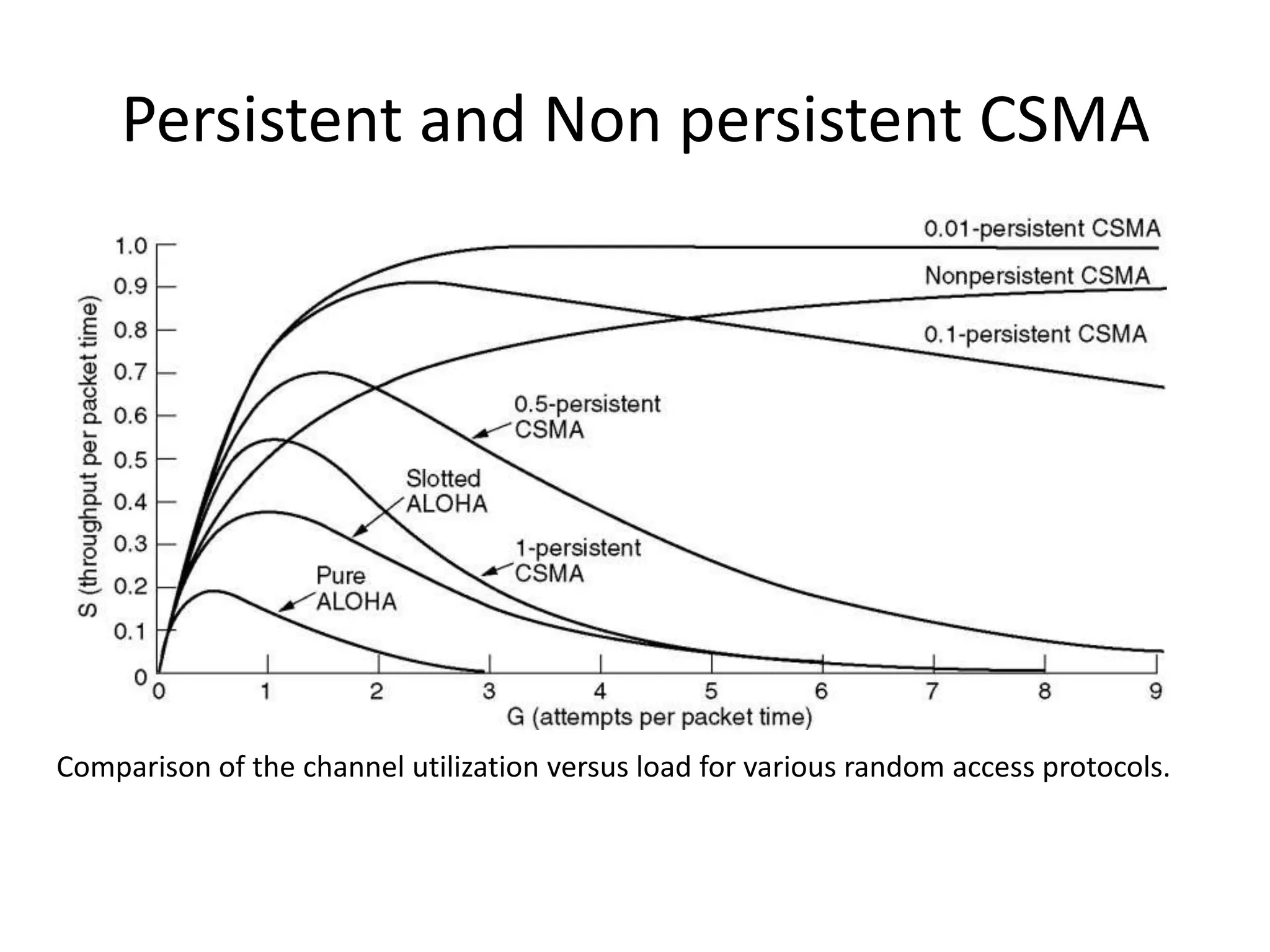
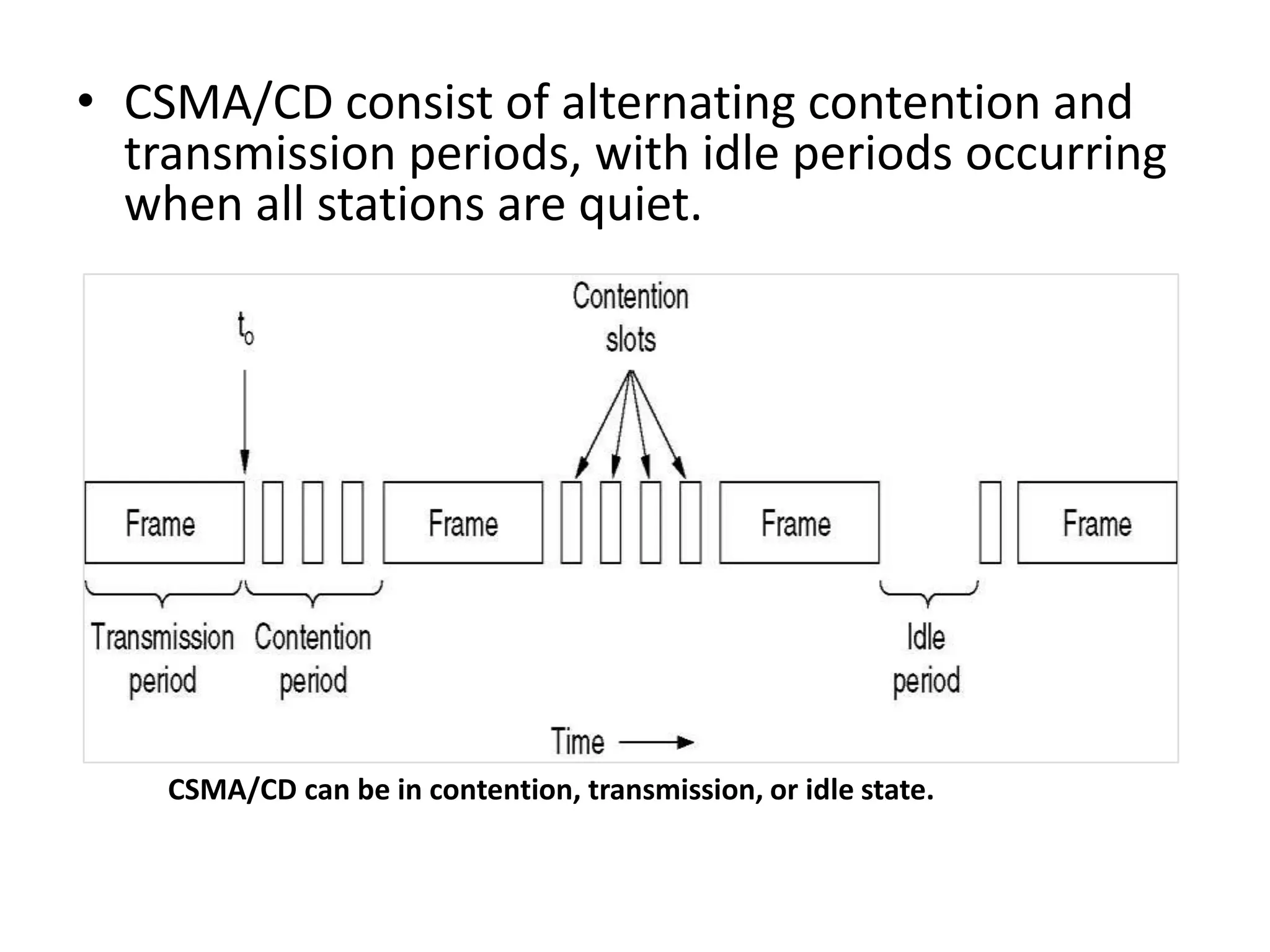
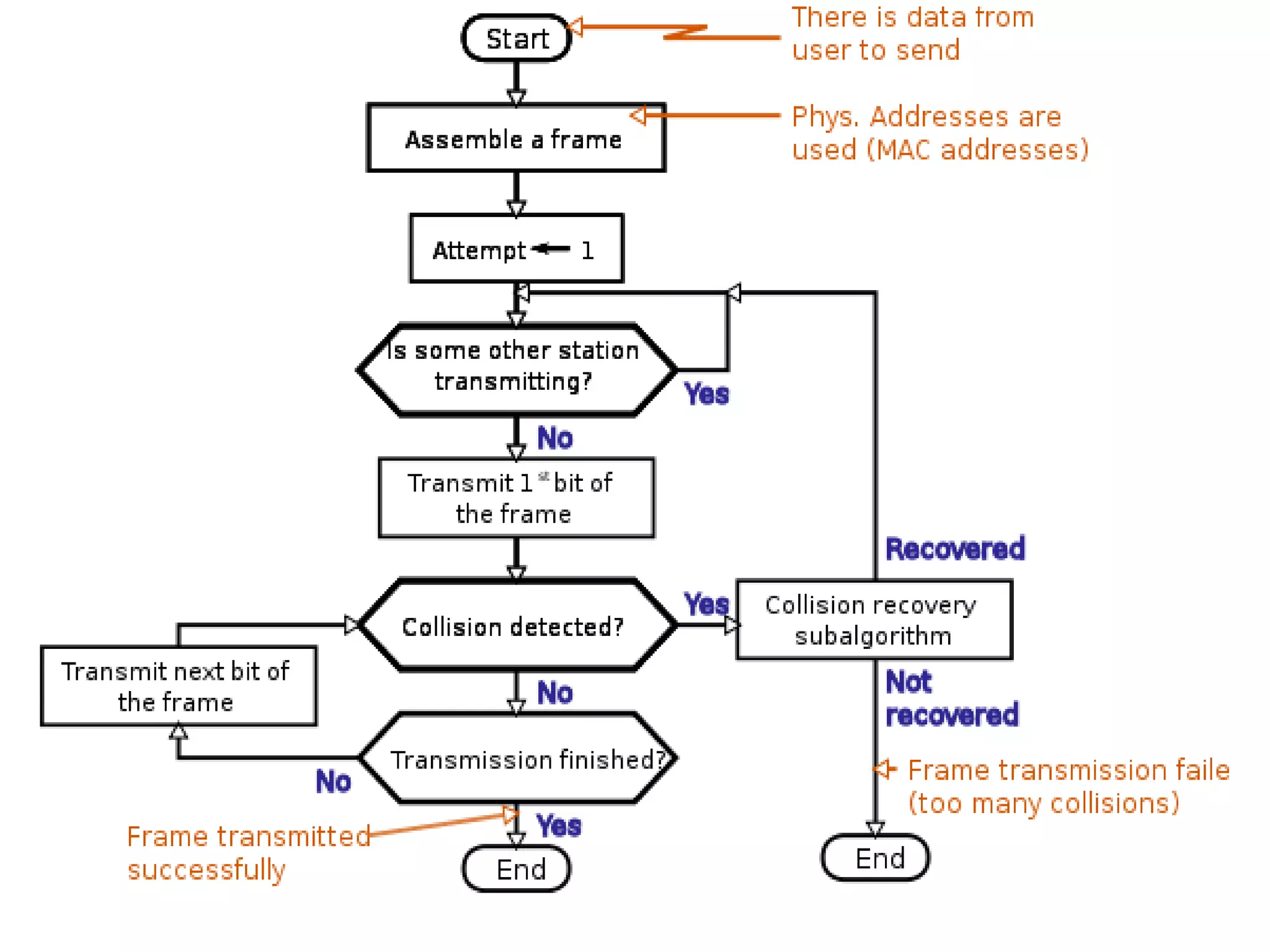
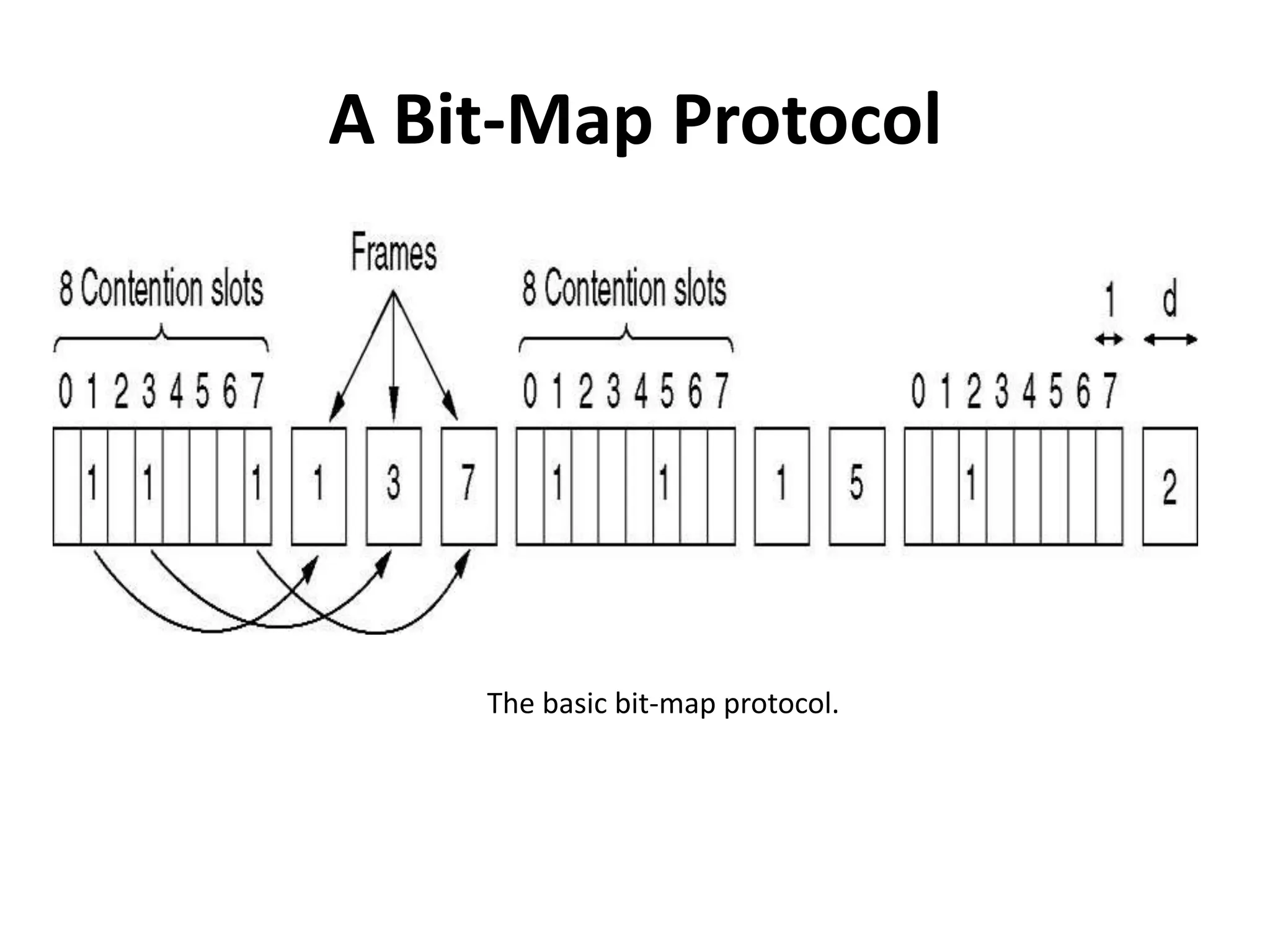
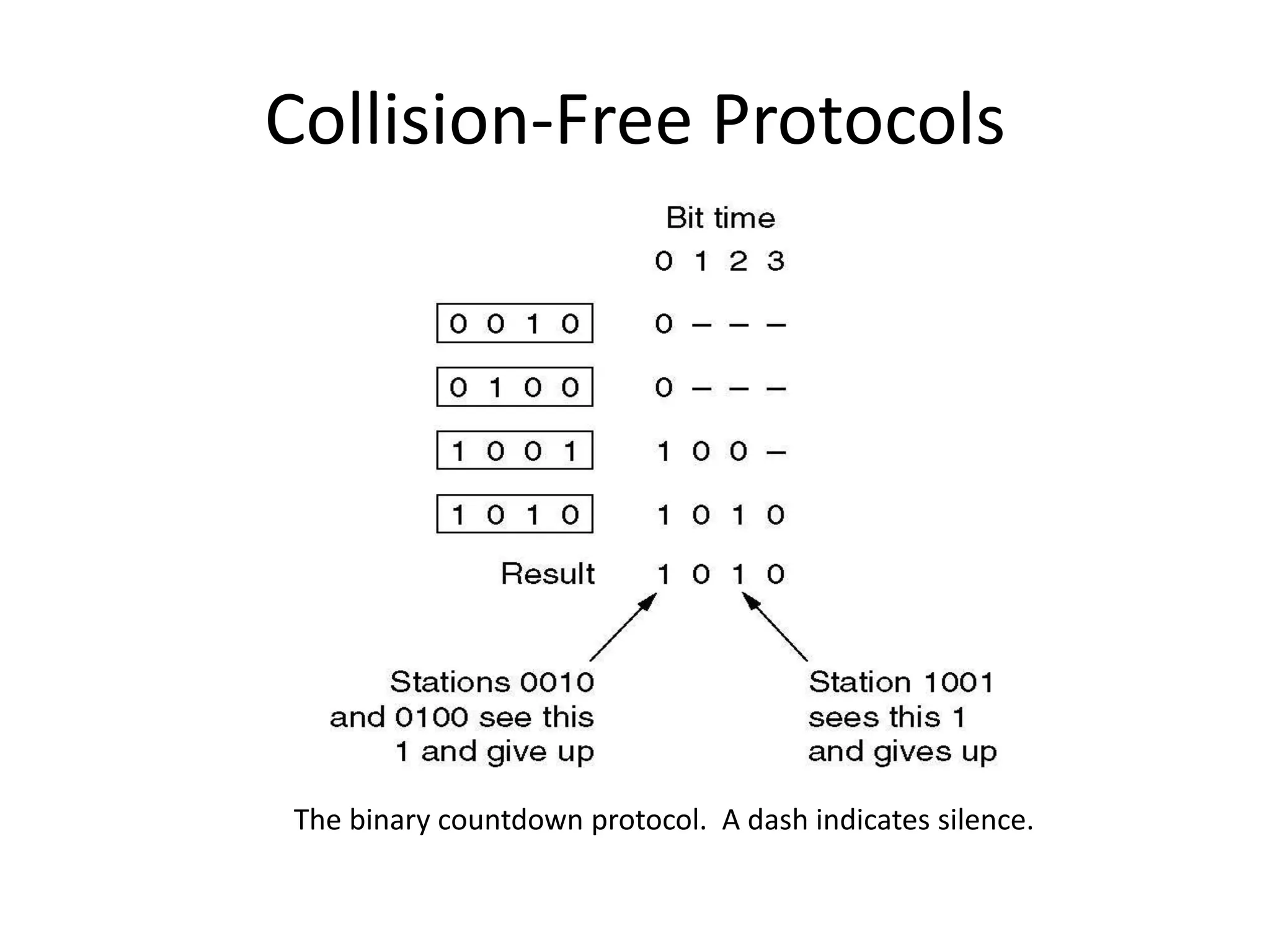
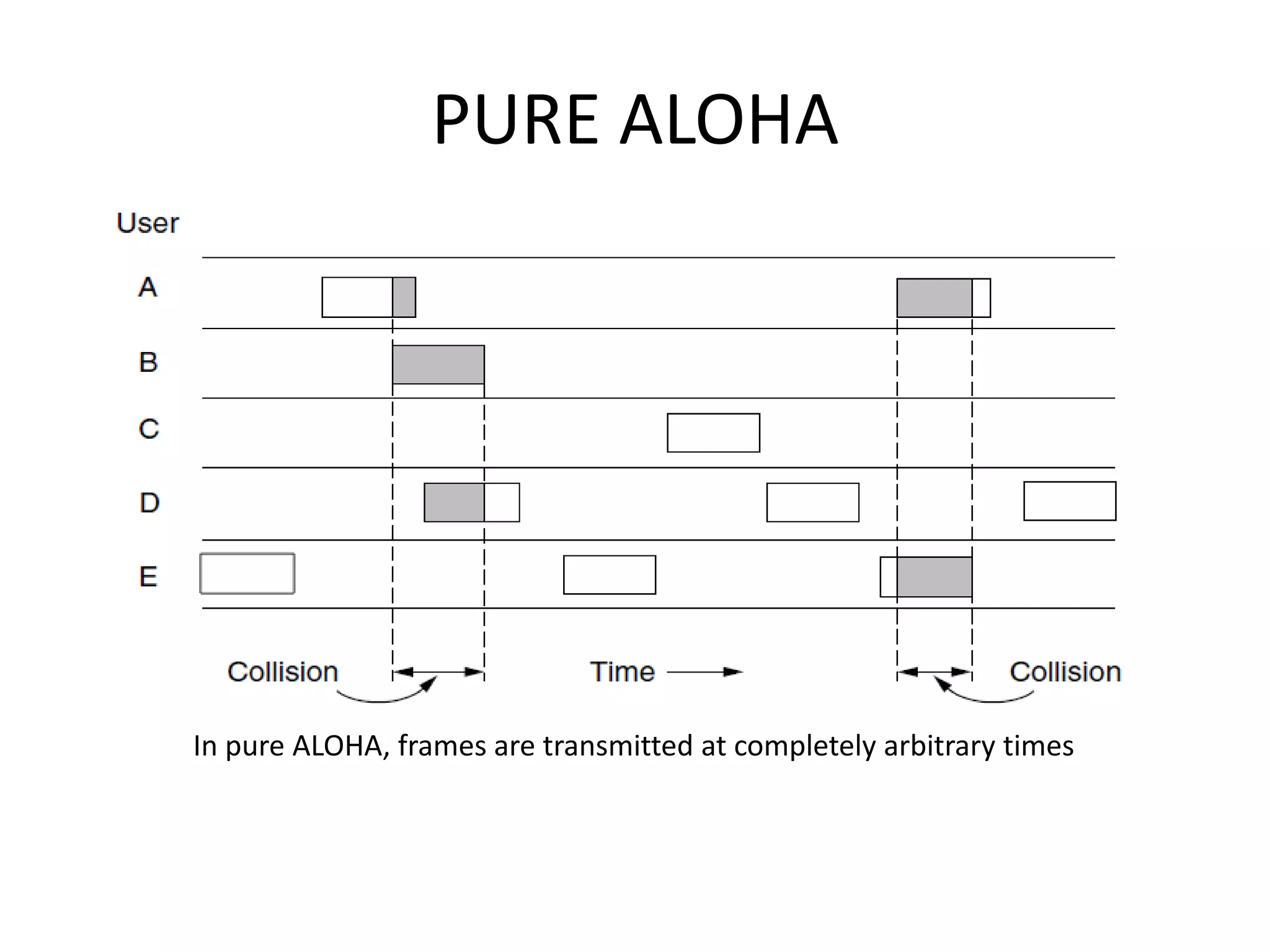
The document discusses the Medium Access Control (MAC) sublayer of the data link layer and various protocols for determining which device can access a shared communication channel. It focuses on static and dynamic channel allocation problems in local area networks (LANs) and wireless networks. Static allocation wastes bandwidth by assigning each user a fixed portion of the channel even when they are not transmitting. Dynamic protocols like ALOHA and carrier sense multiple access (CSMA) aim to improve channel utilization by allowing users to transmit only when the channel is idle.
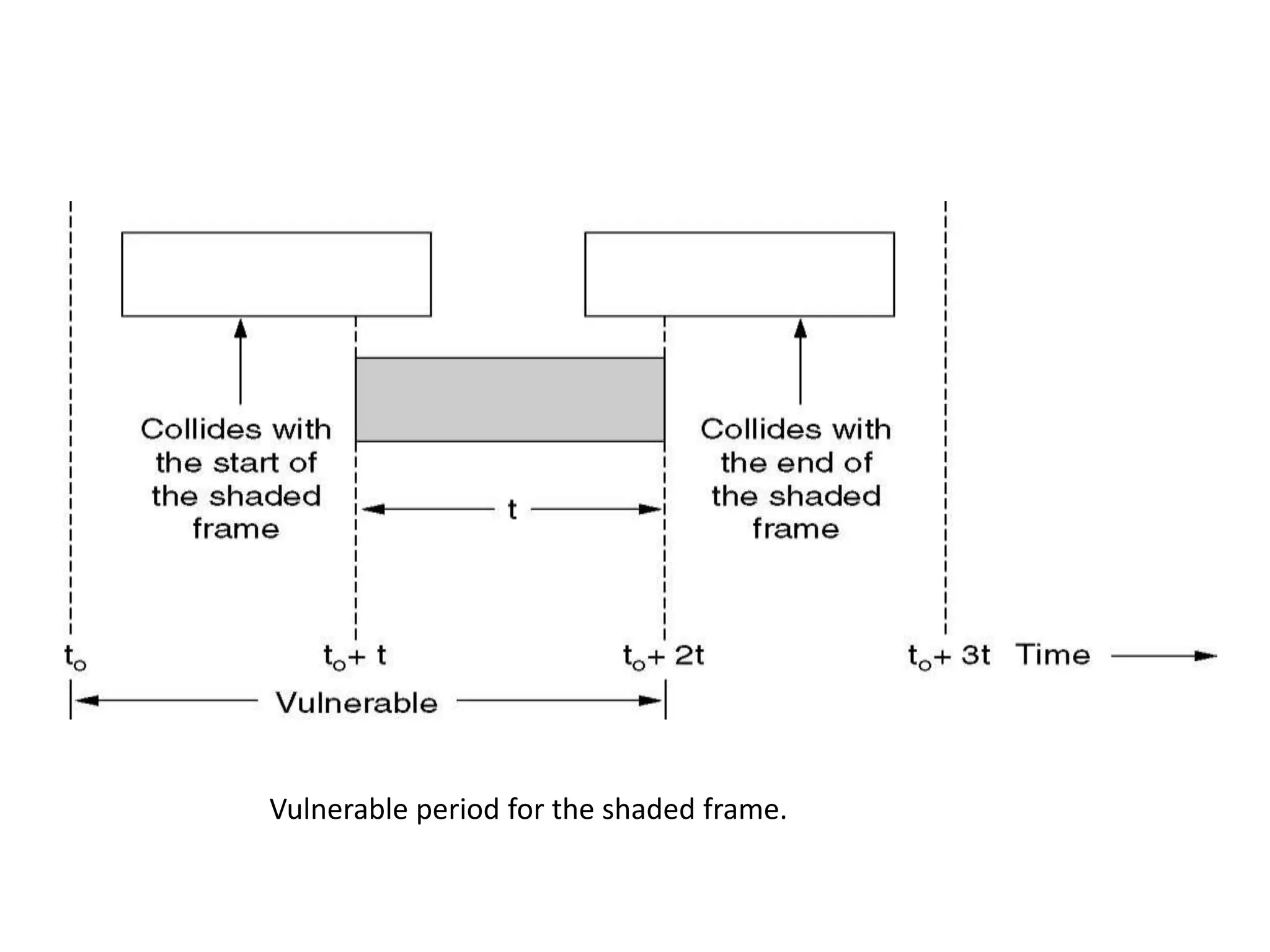
![• The probability that k frames are generated
during a given frame time, in which G frames
are expected, is given by the Poisson
distribution
Pr[k ] =Gk e−G /k!
• so the probability of zero frames is just e−G. In
an interval two frame times long, the mean
number of frames generated is 2G.
• The probability of no frames being initiated
during the entire vulnerable period is thus
given by P0 = e−2G. Using S = G P0, we get
S = Ge−2G](https://image.slidesharecdn.com/ch2themediumaccesssublayer-131117100553-phpapp01/75/The-medium-access-sublayer-19-2048.jpg)