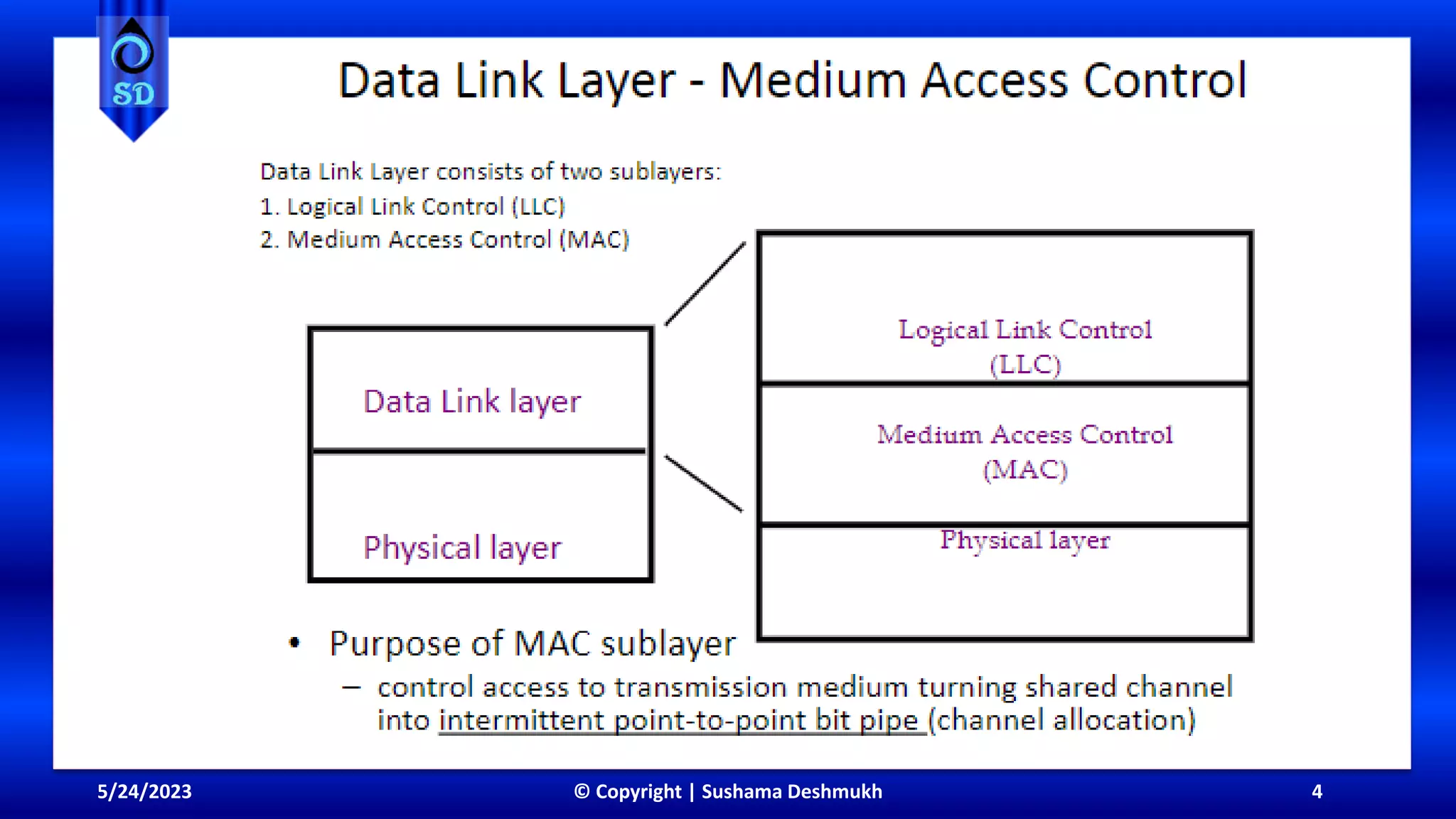
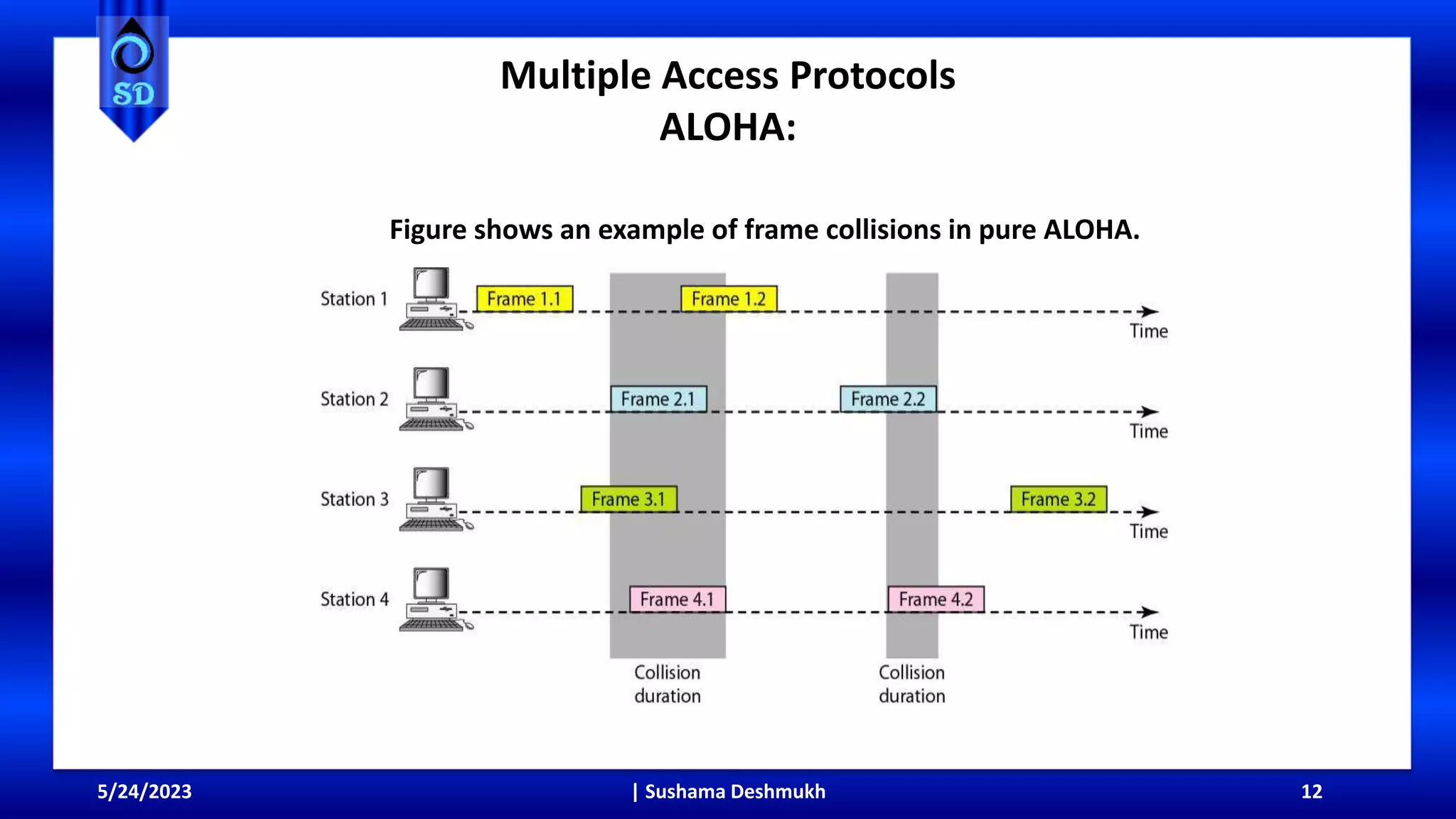
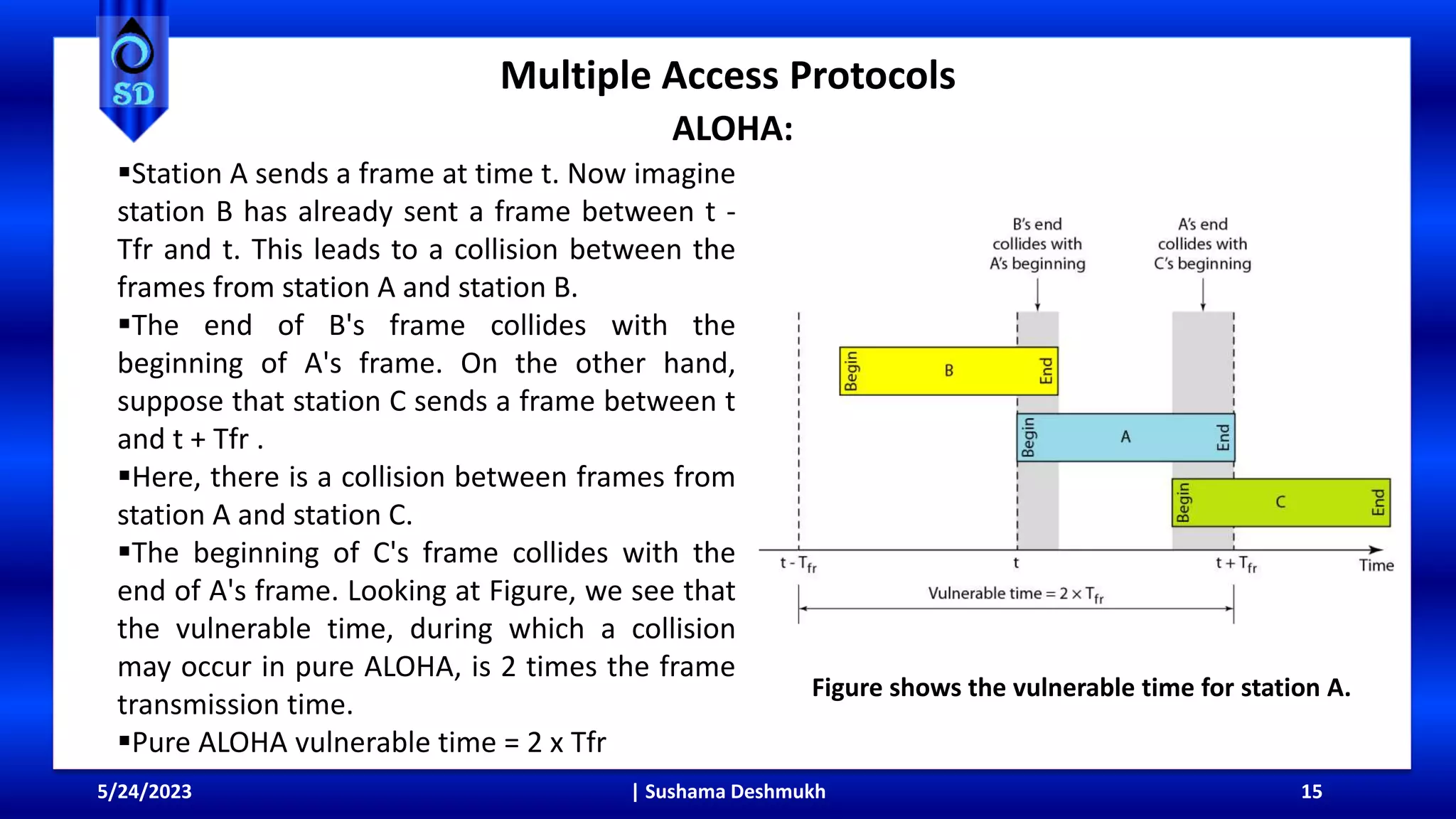
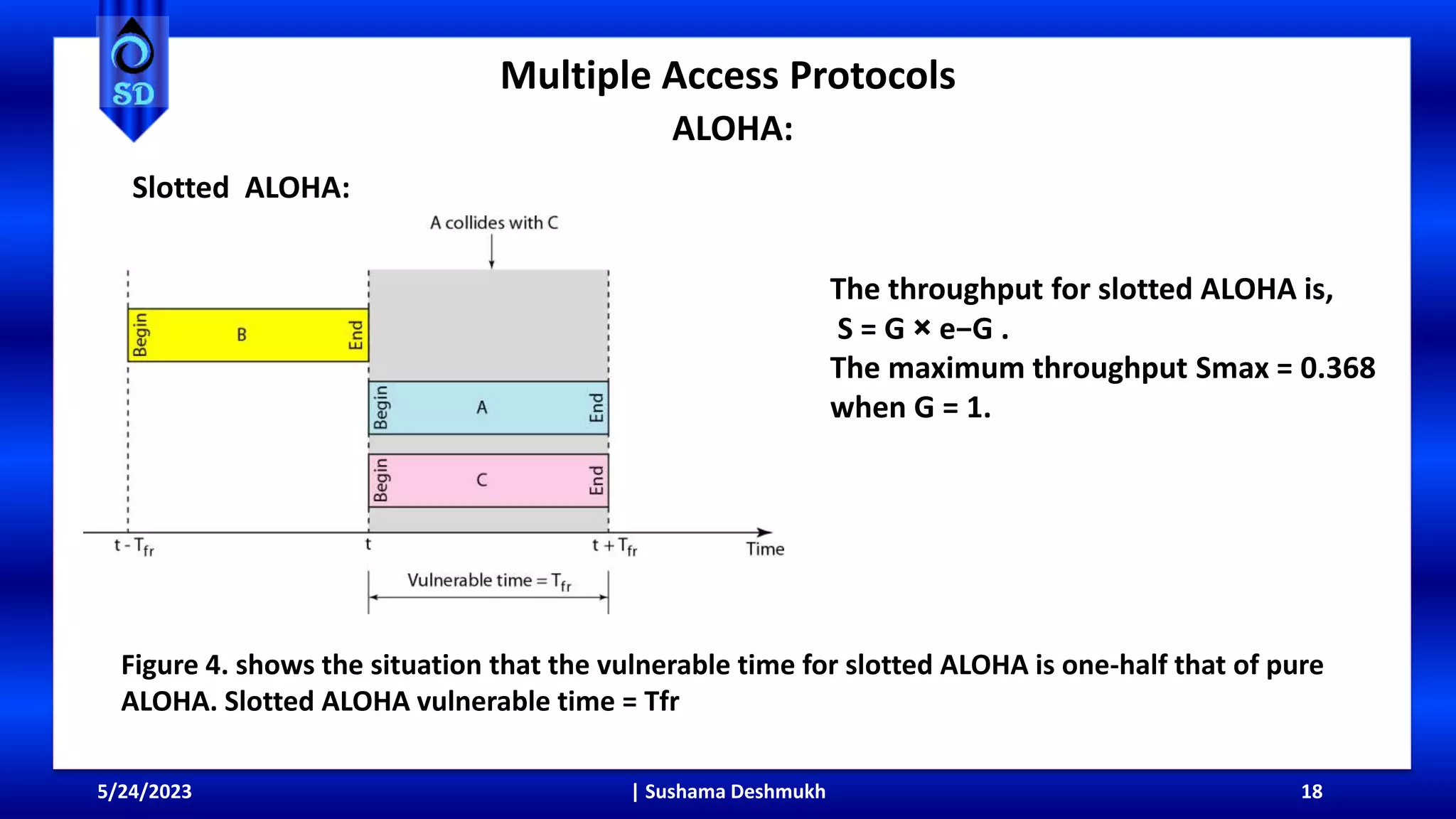
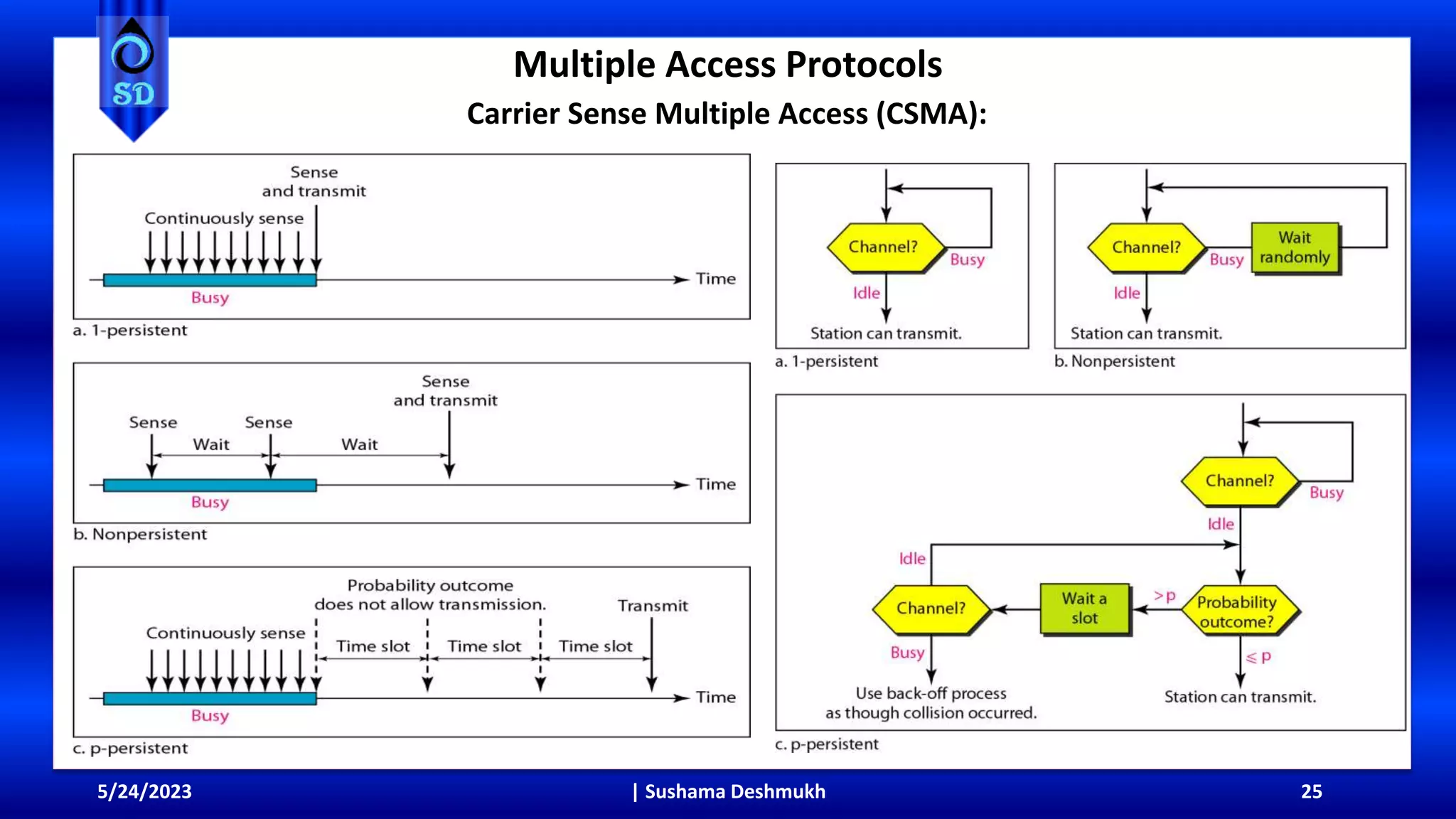
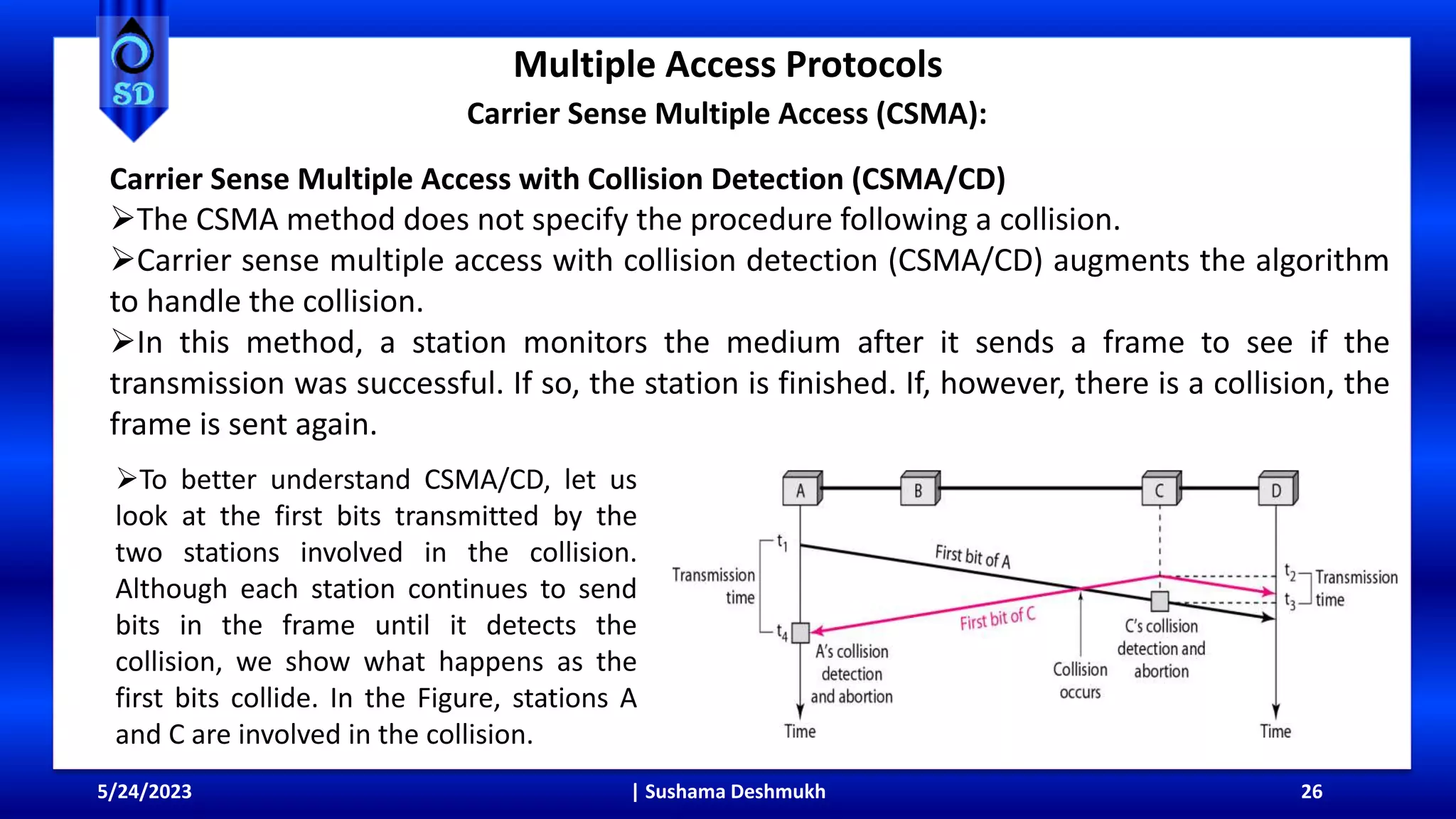
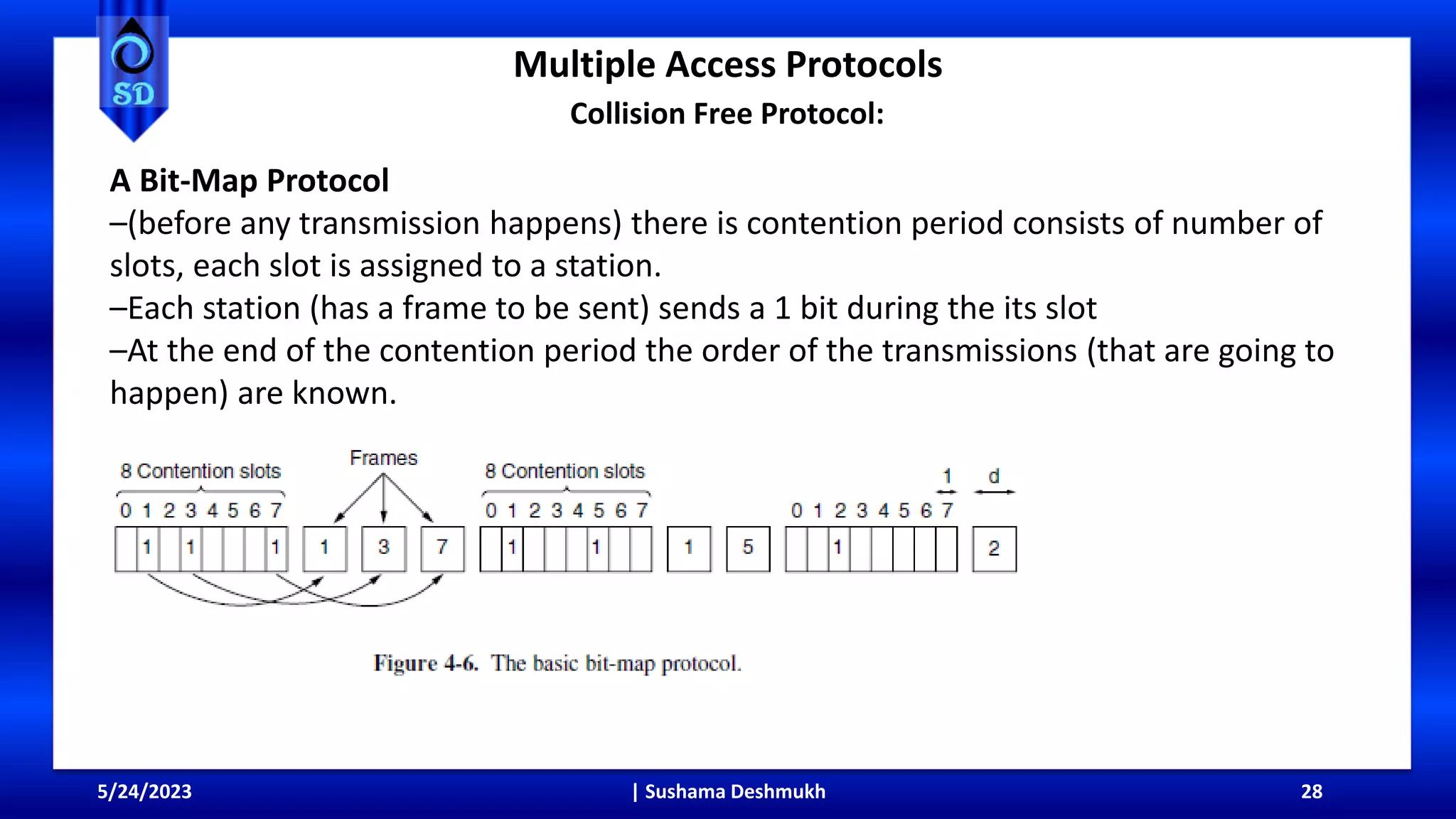
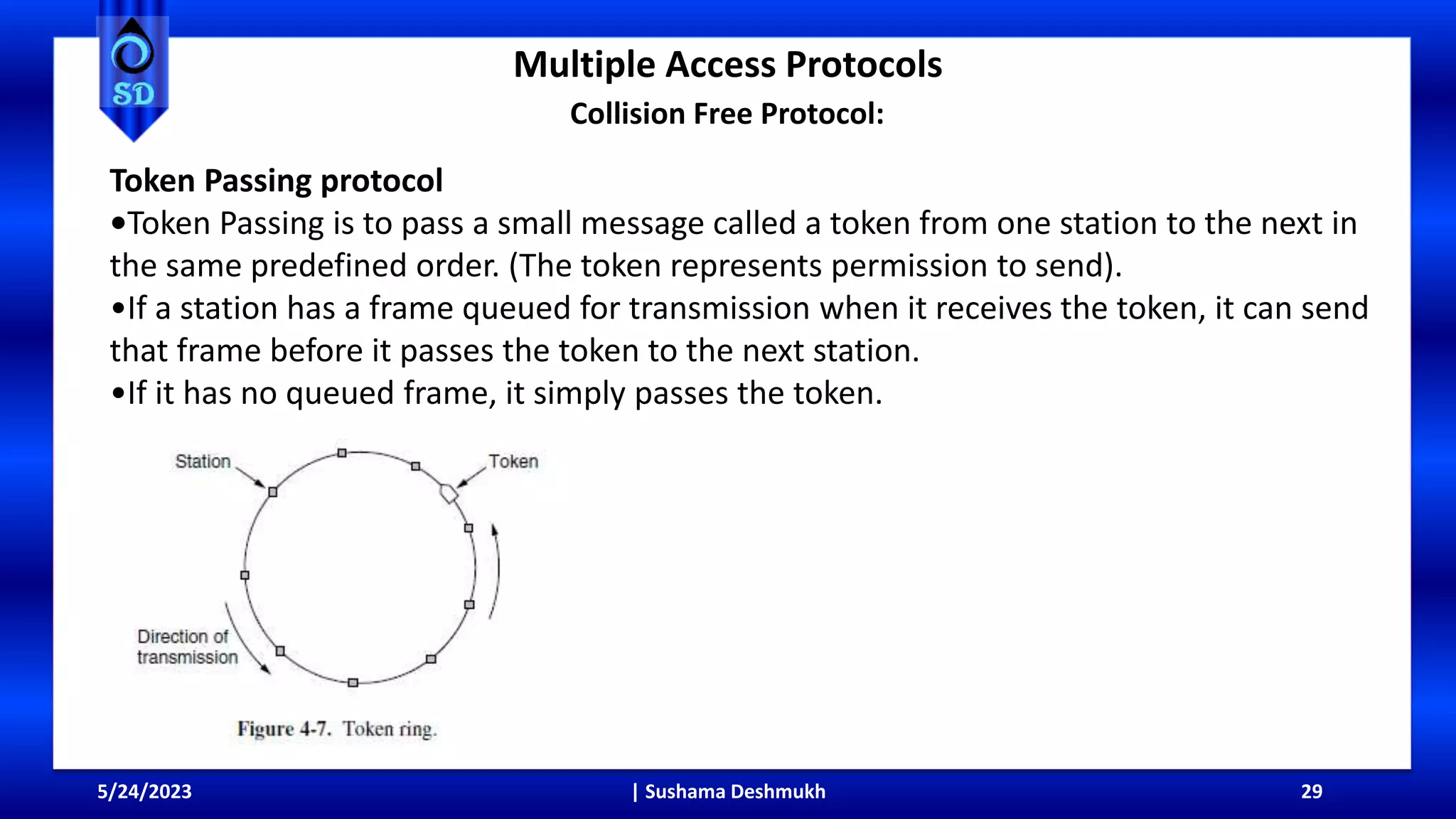
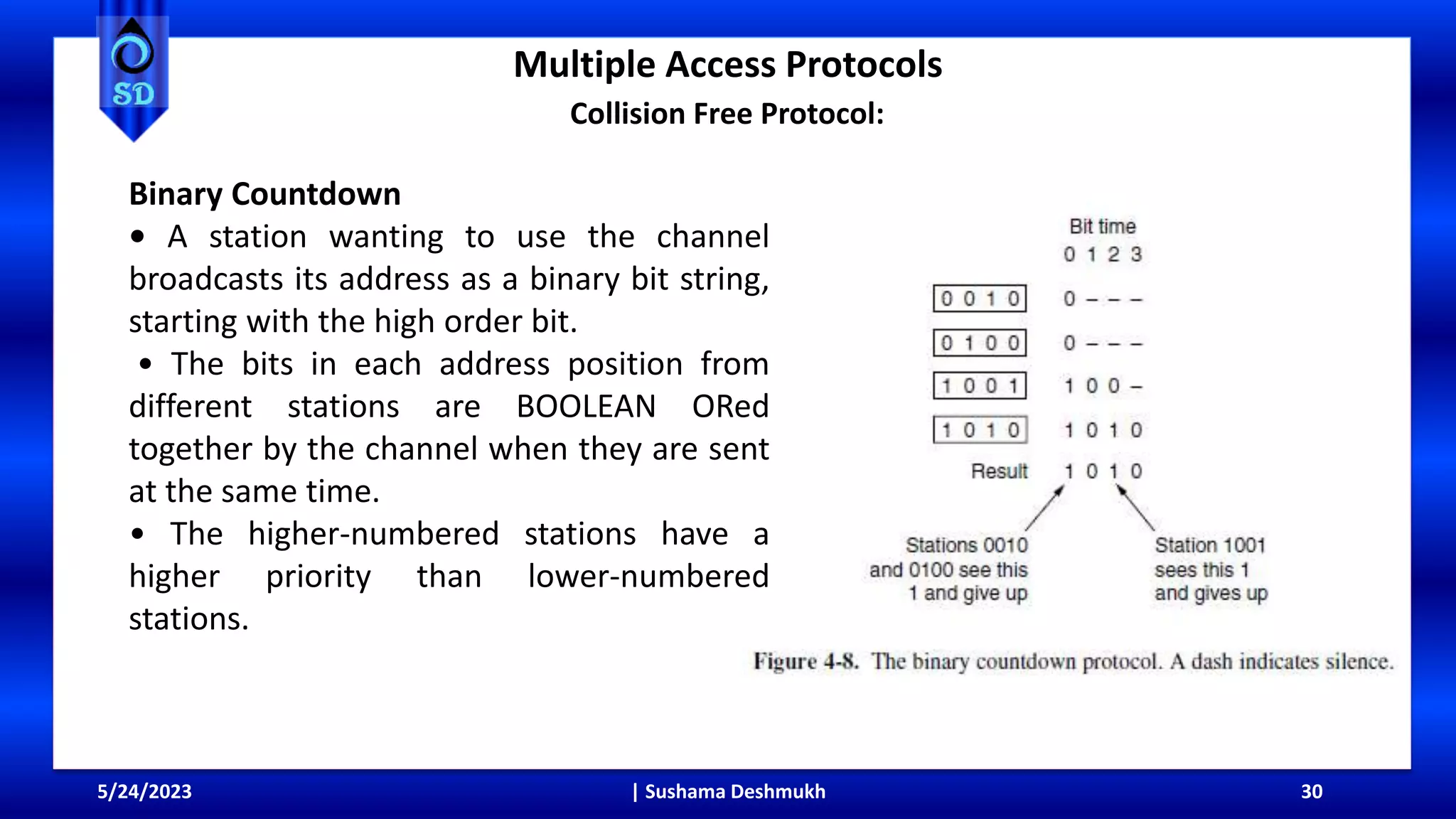
This document provides an overview of medium access control sublayer topics, including channel allocation, multiple access protocols, Ethernet, wireless LANs, and data link layer switching. It discusses static and dynamic channel allocation approaches. For multiple access protocols, it describes ALOHA, carrier sense multiple access, and collision-free protocols. It provides details on pure ALOHA, slotted ALOHA, 1-persistent CSMA, non-persistent CSMA, CSMA/CD, bit-map protocols, token passing, and binary countdown.