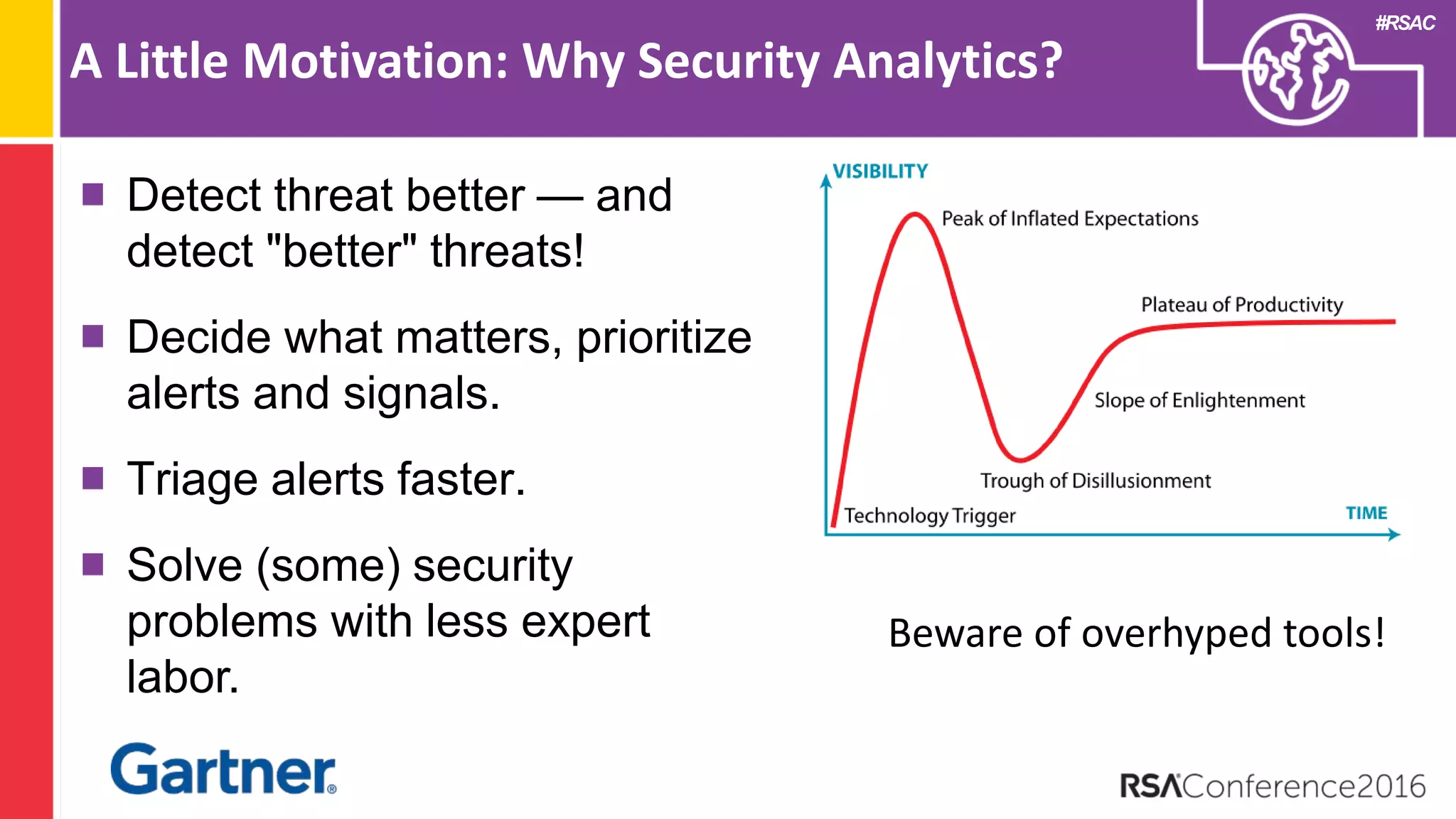
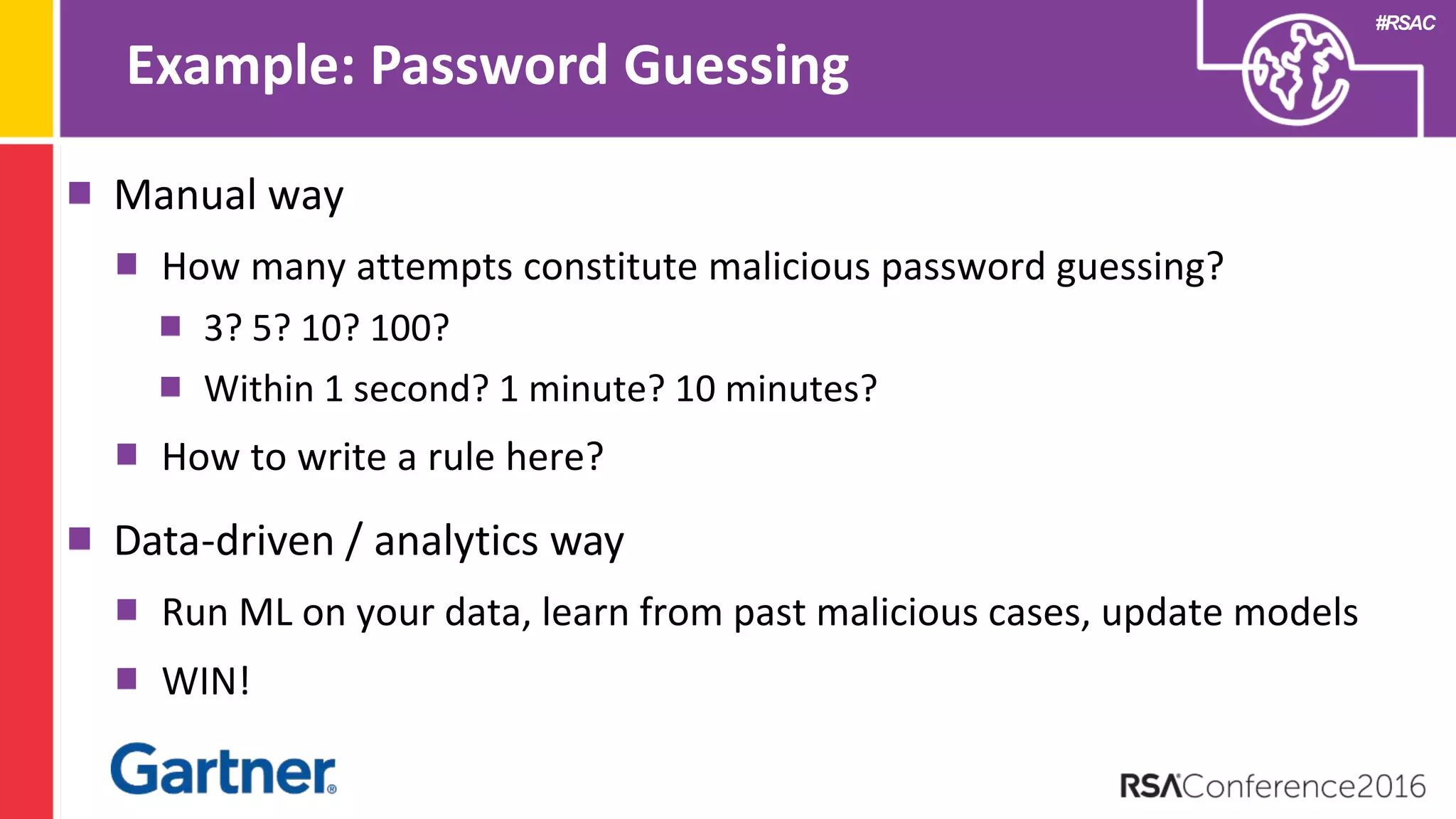
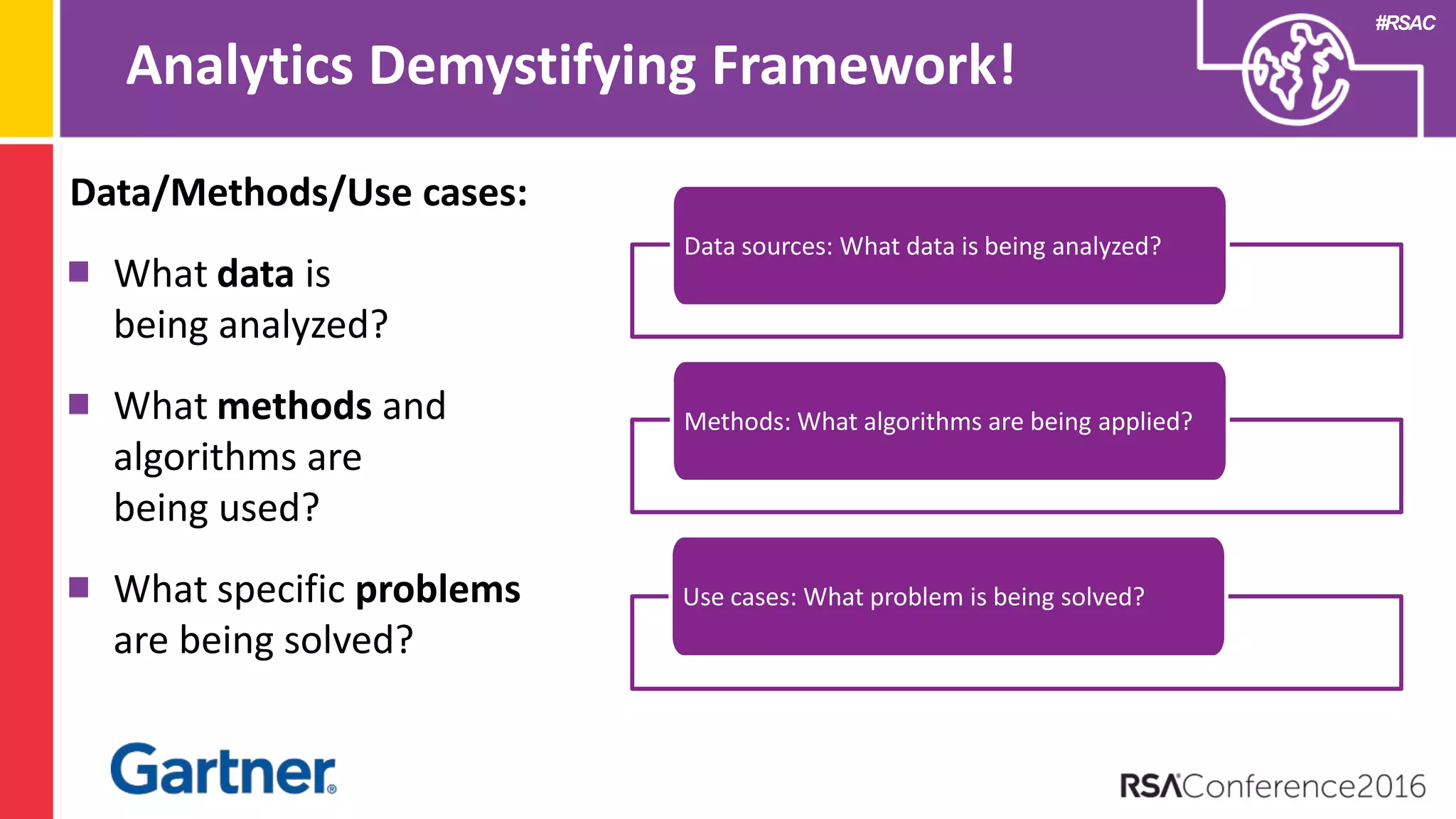
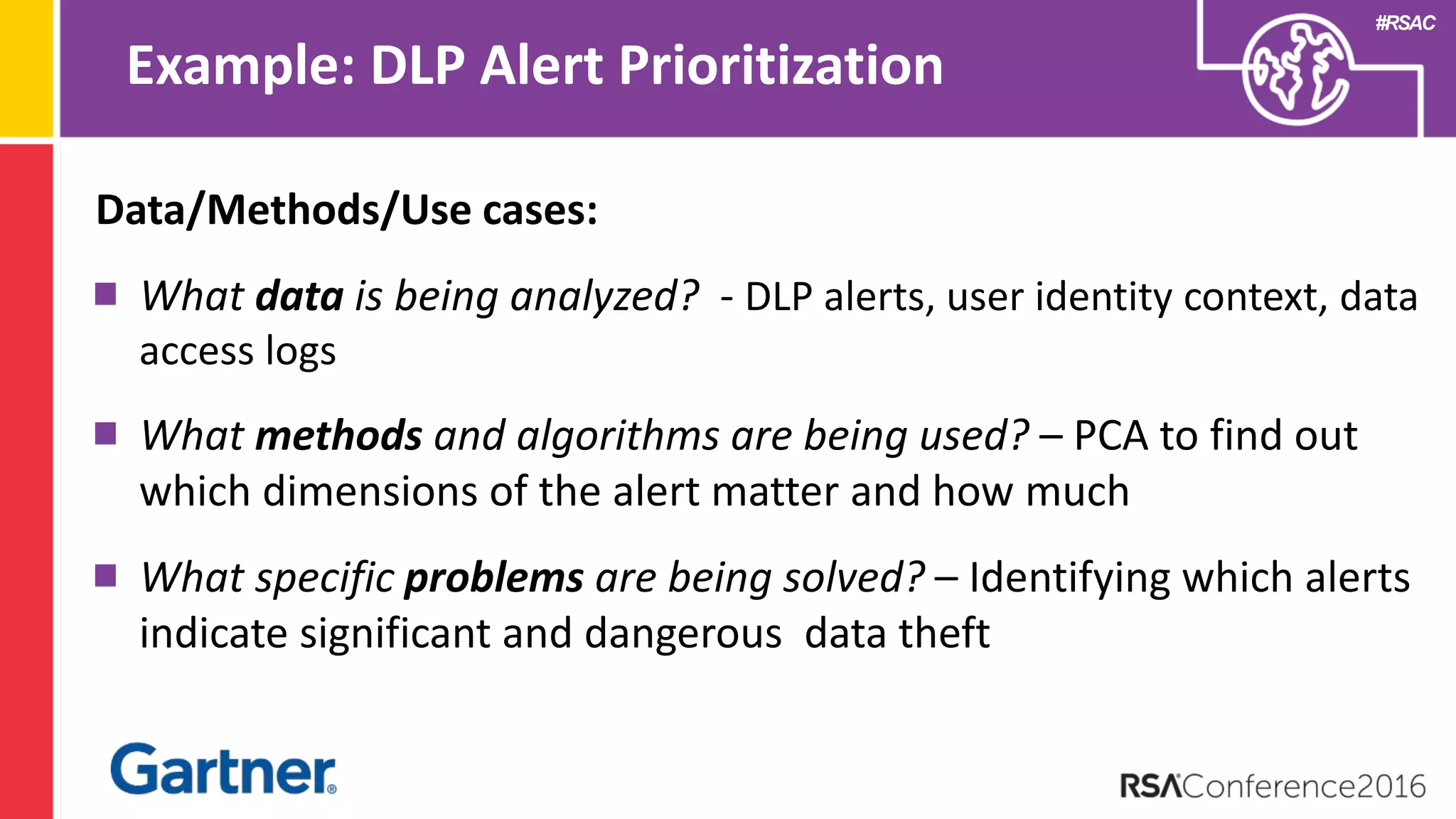
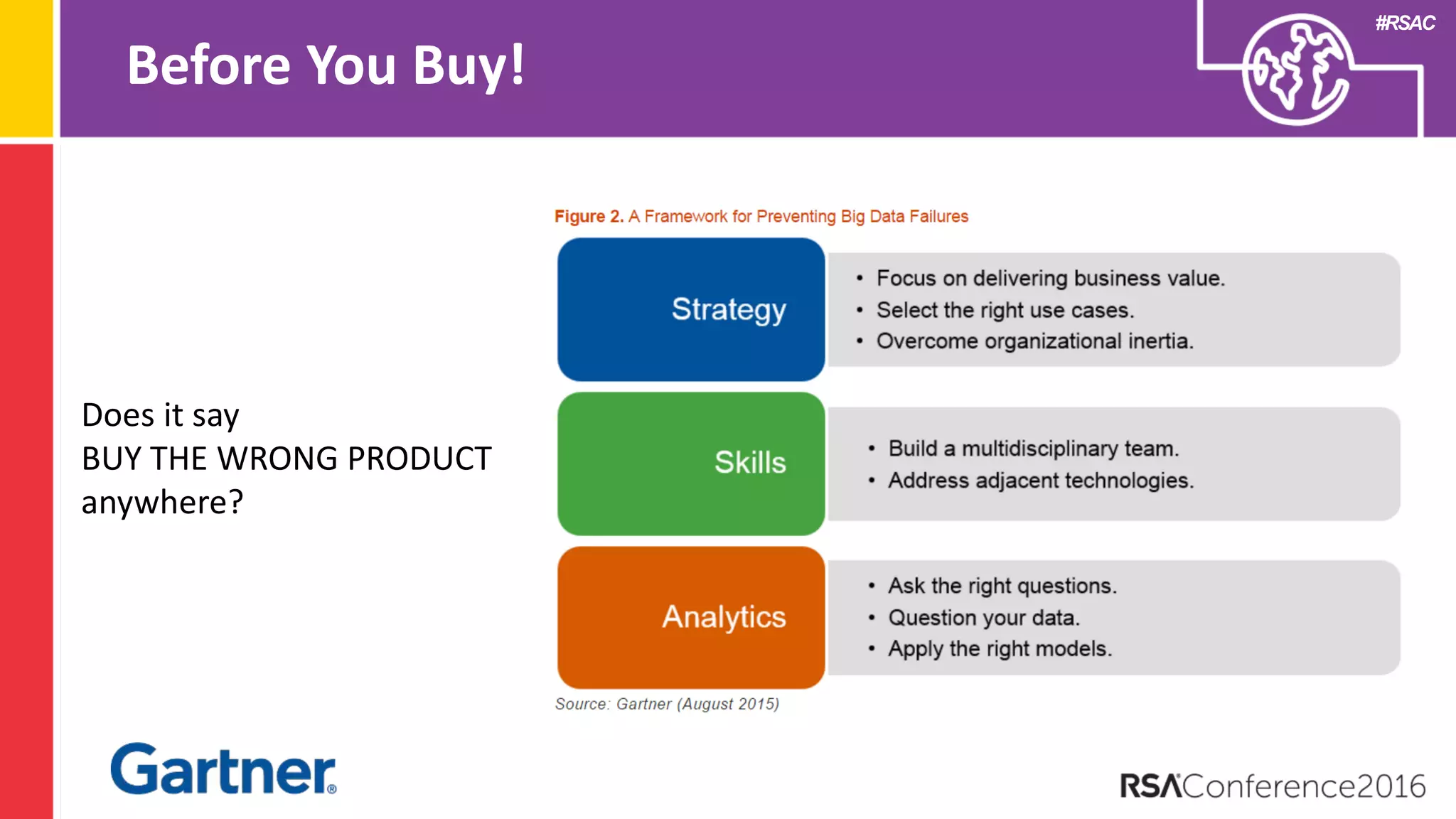
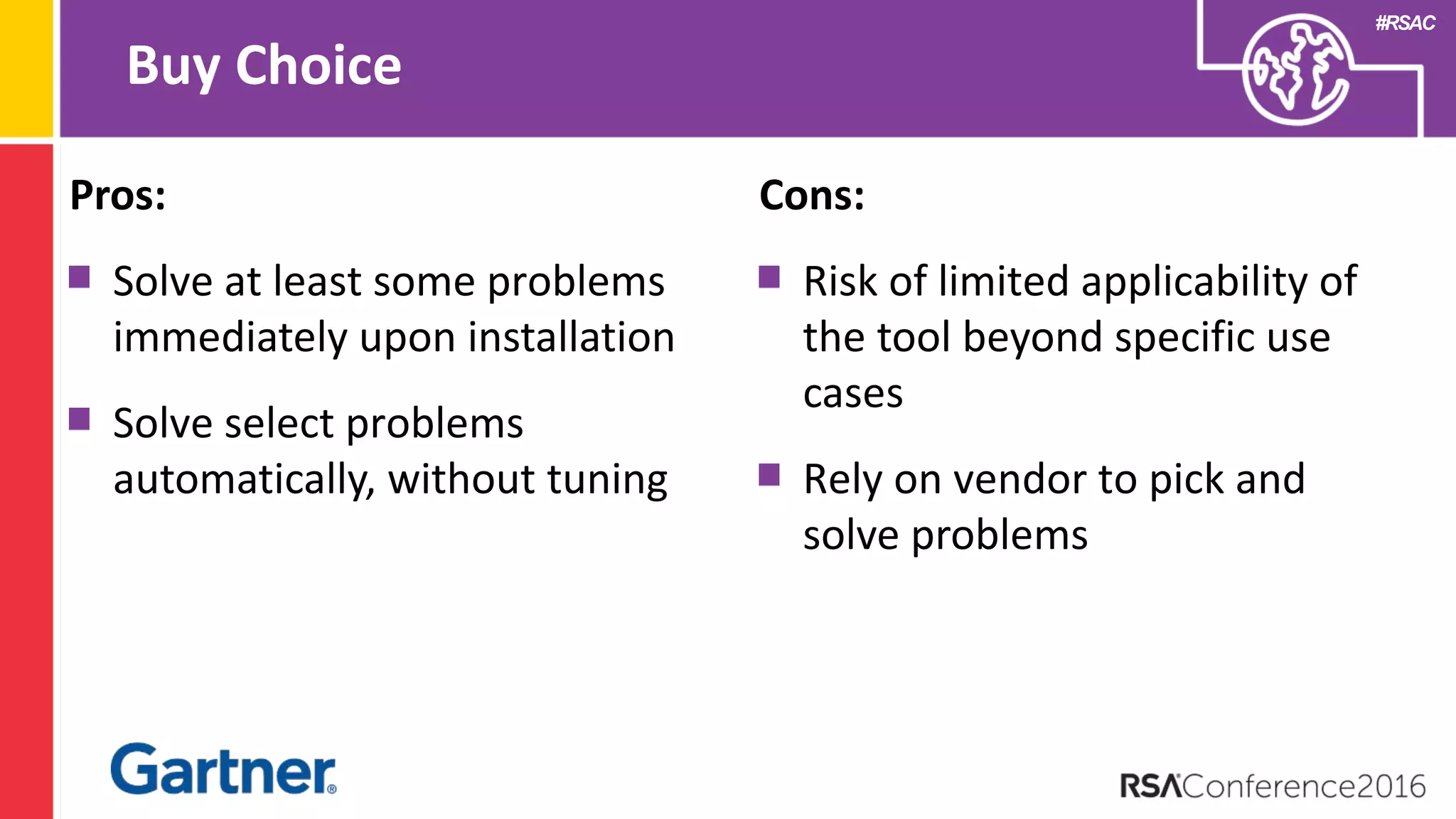
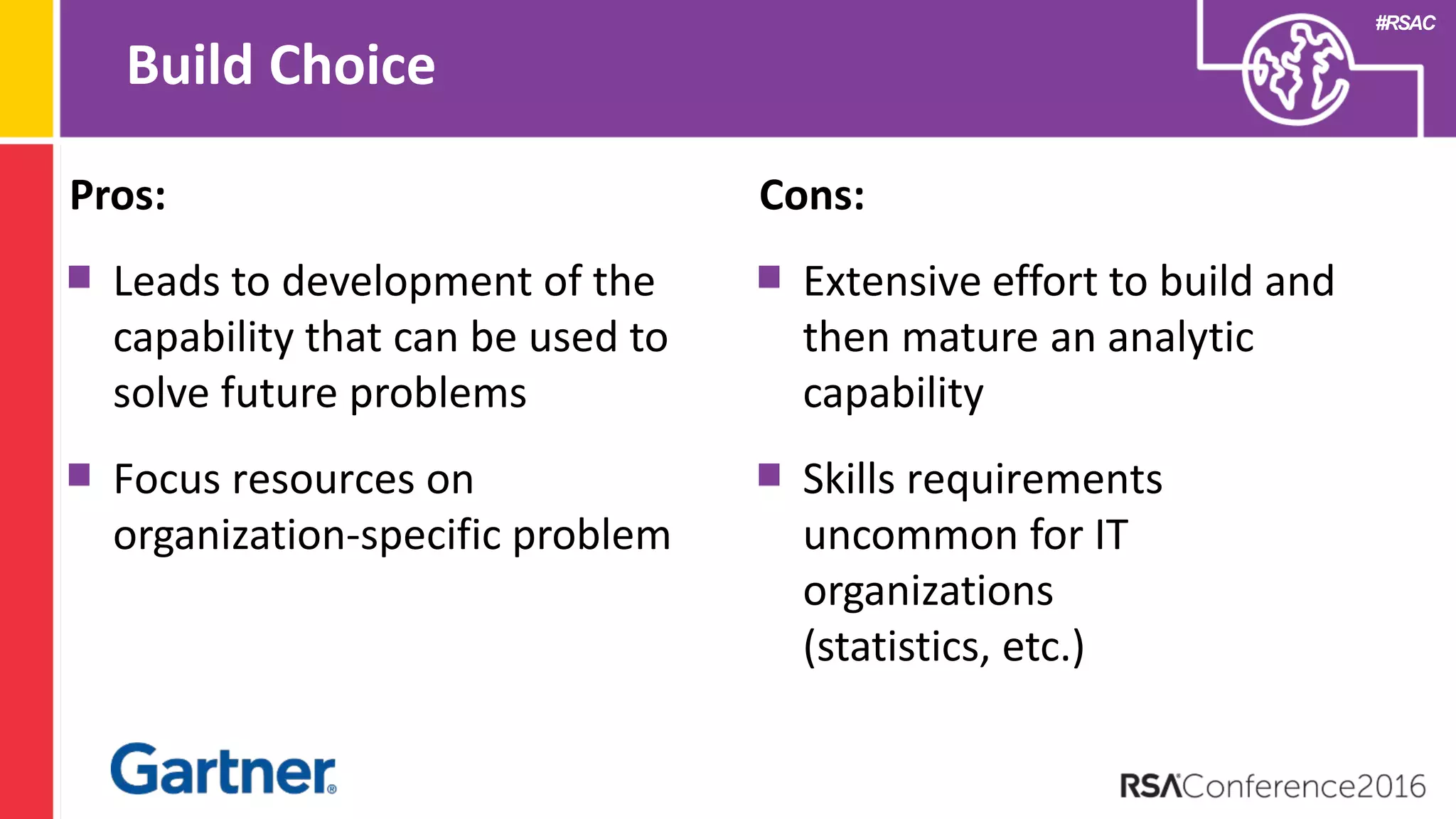
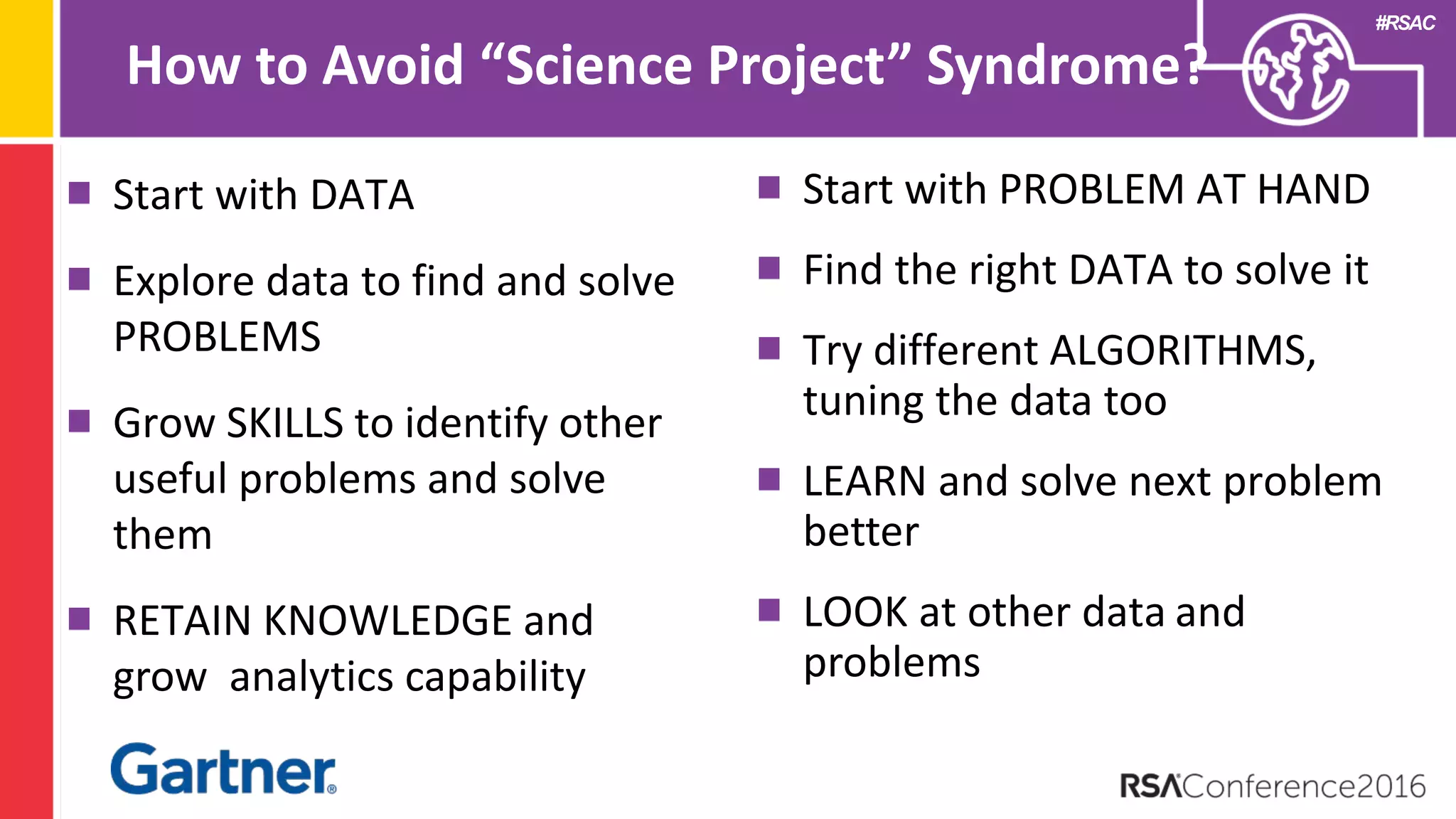
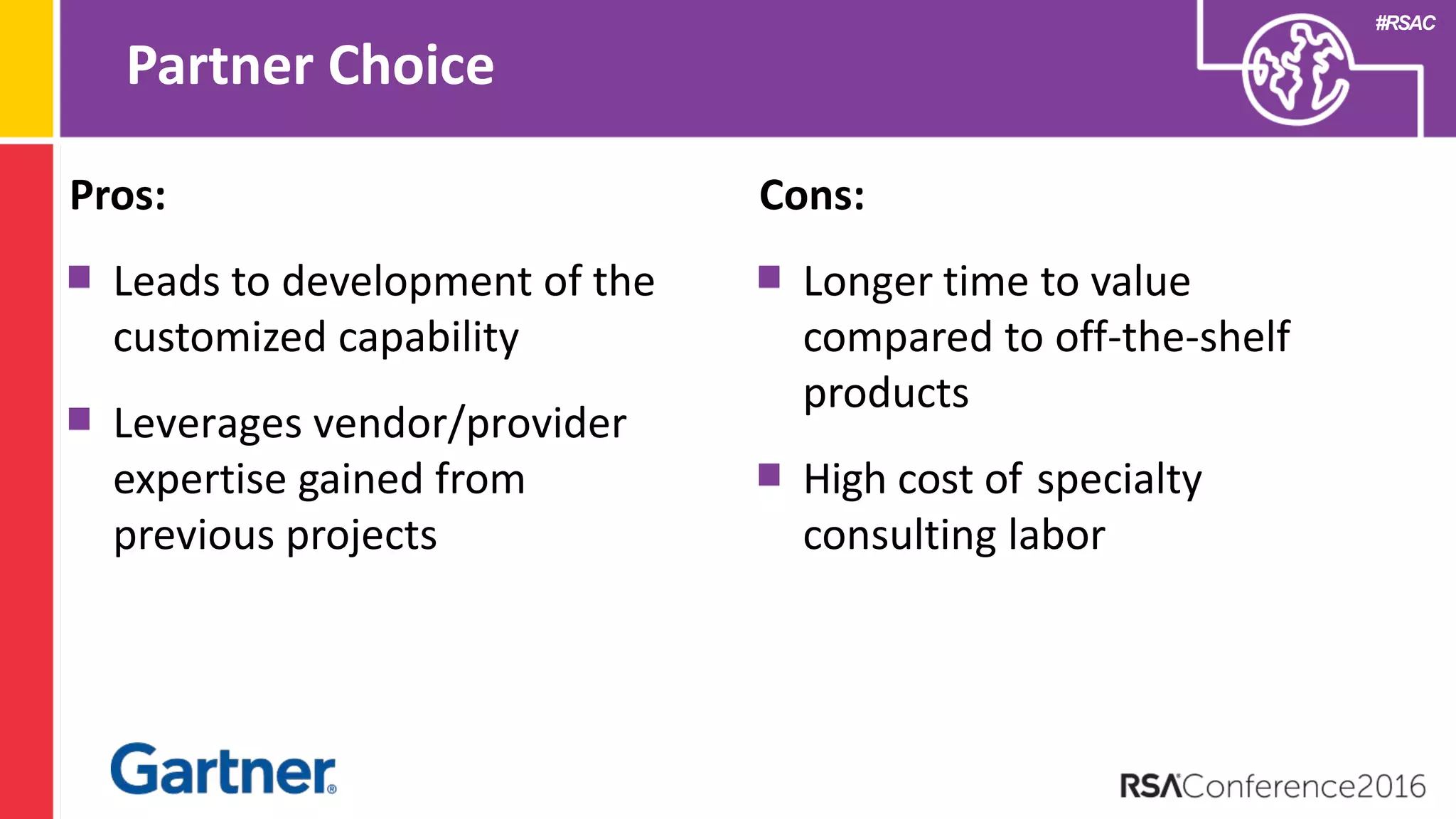
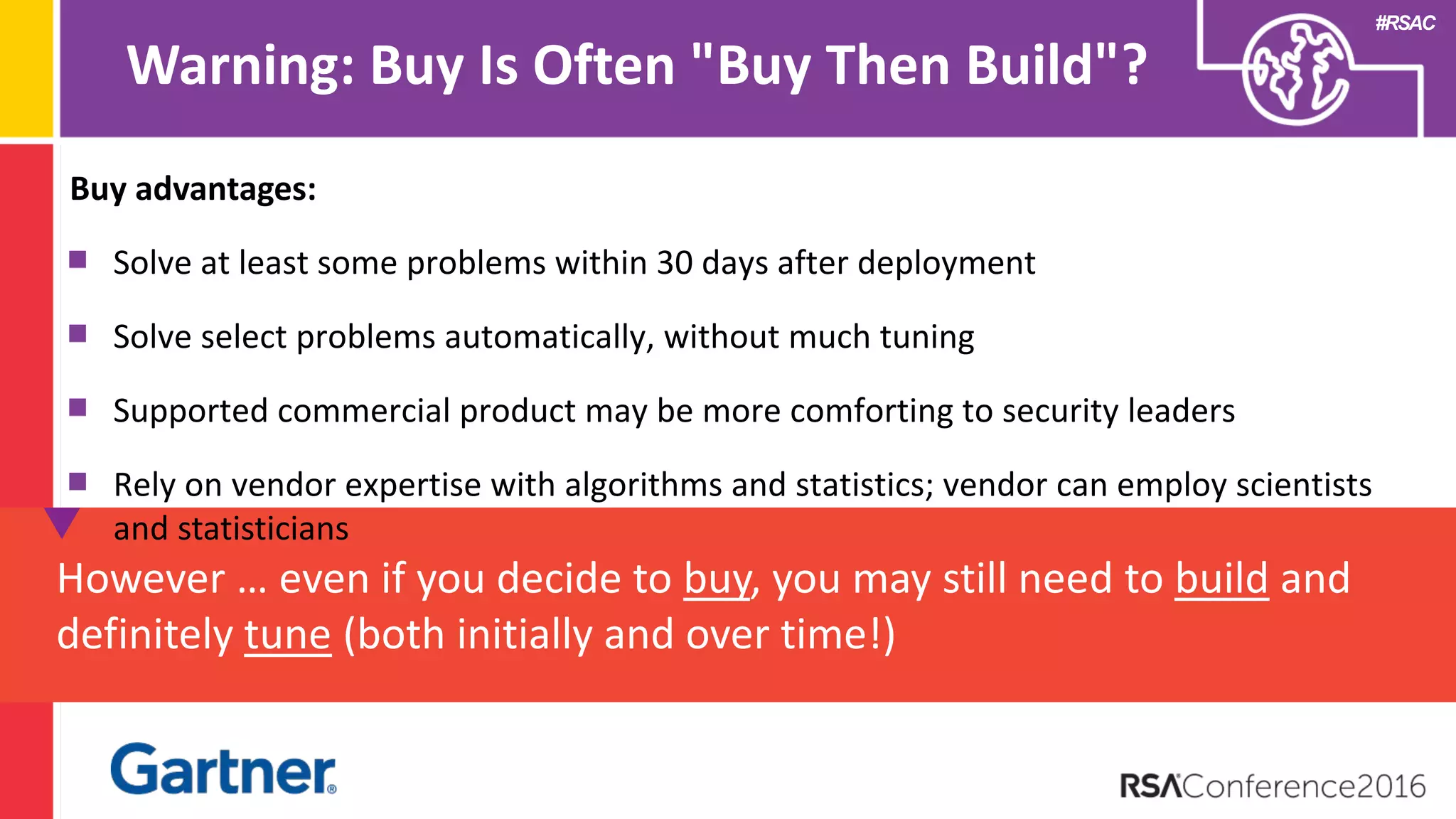
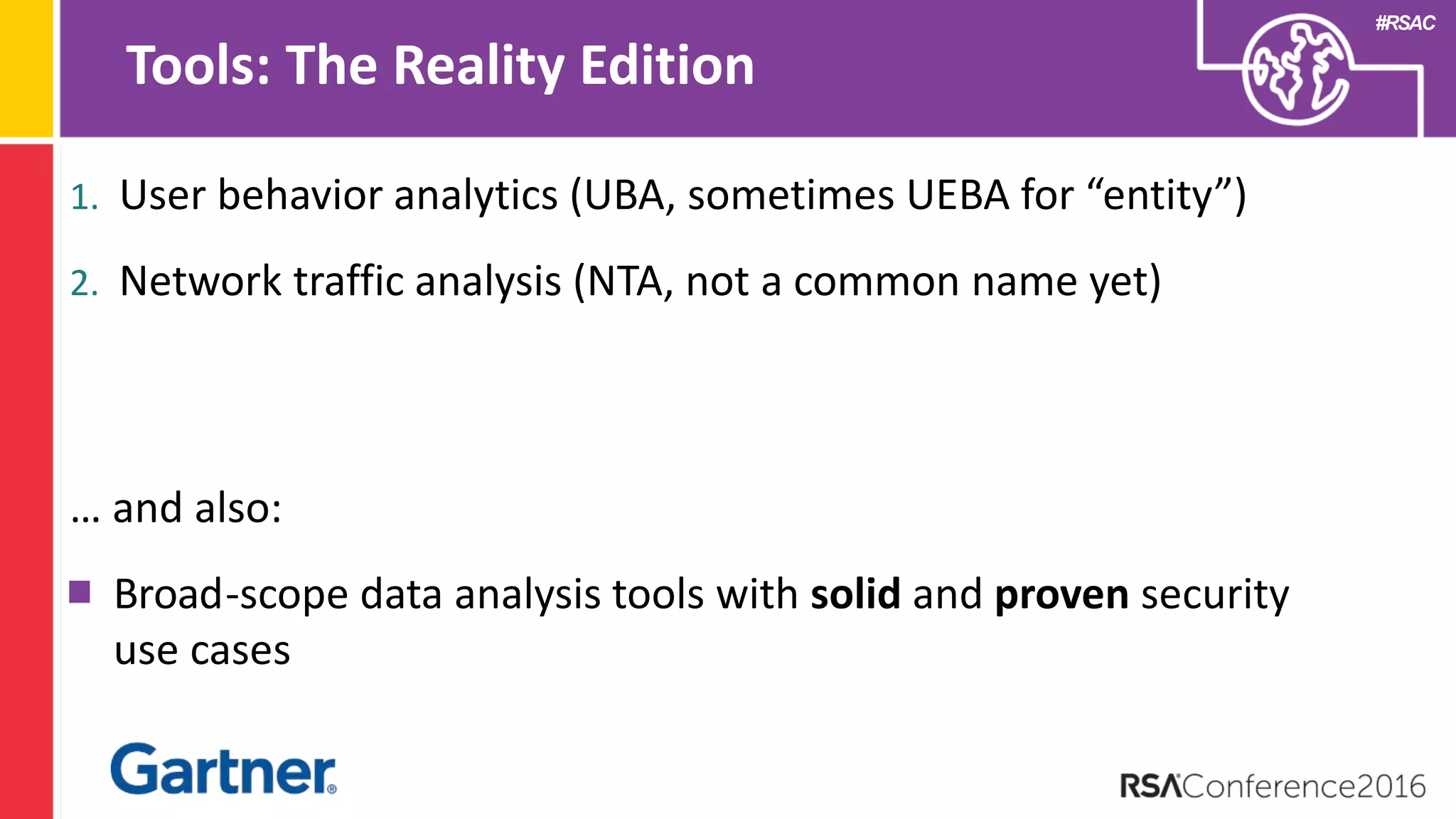
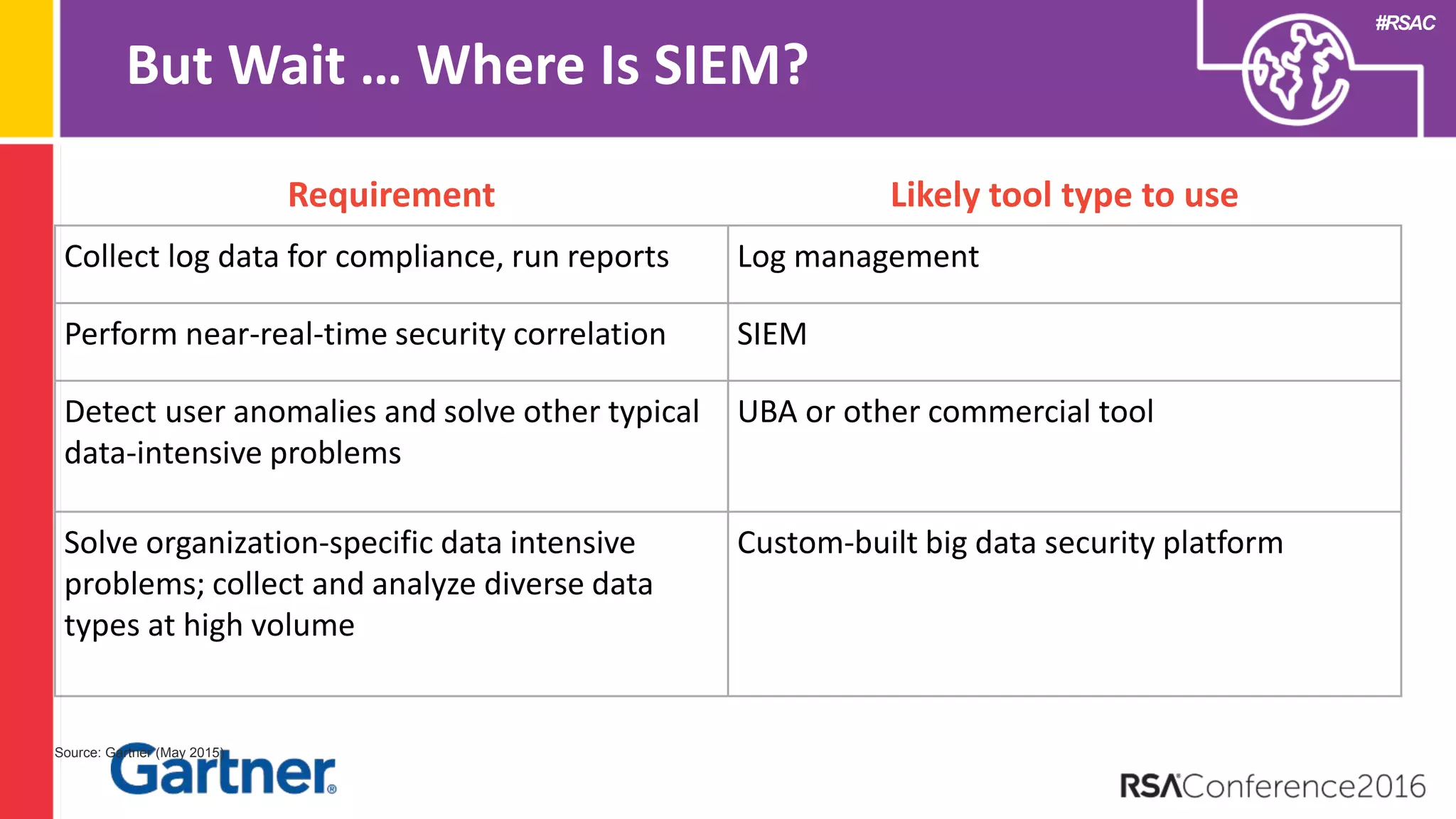
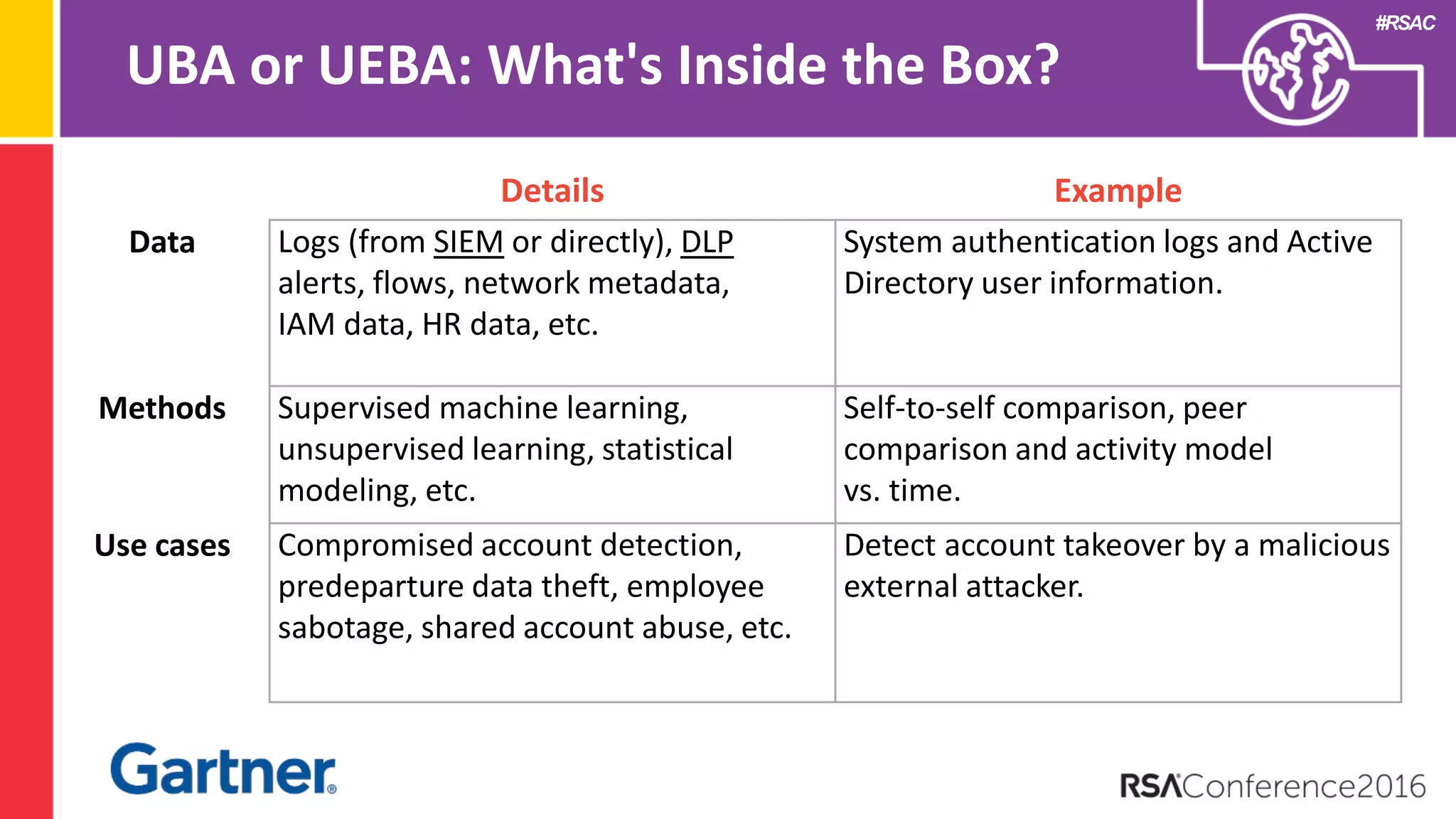
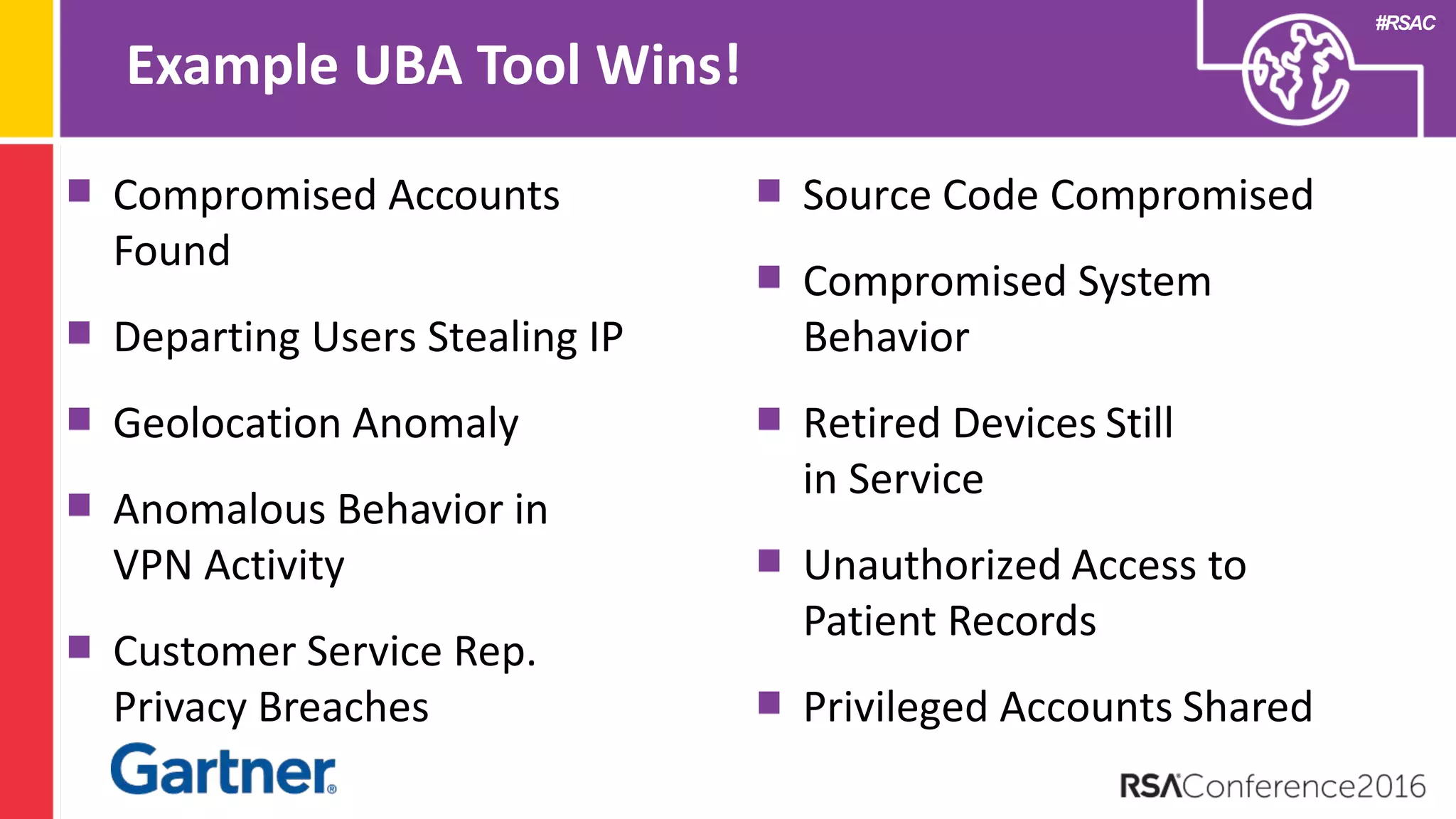
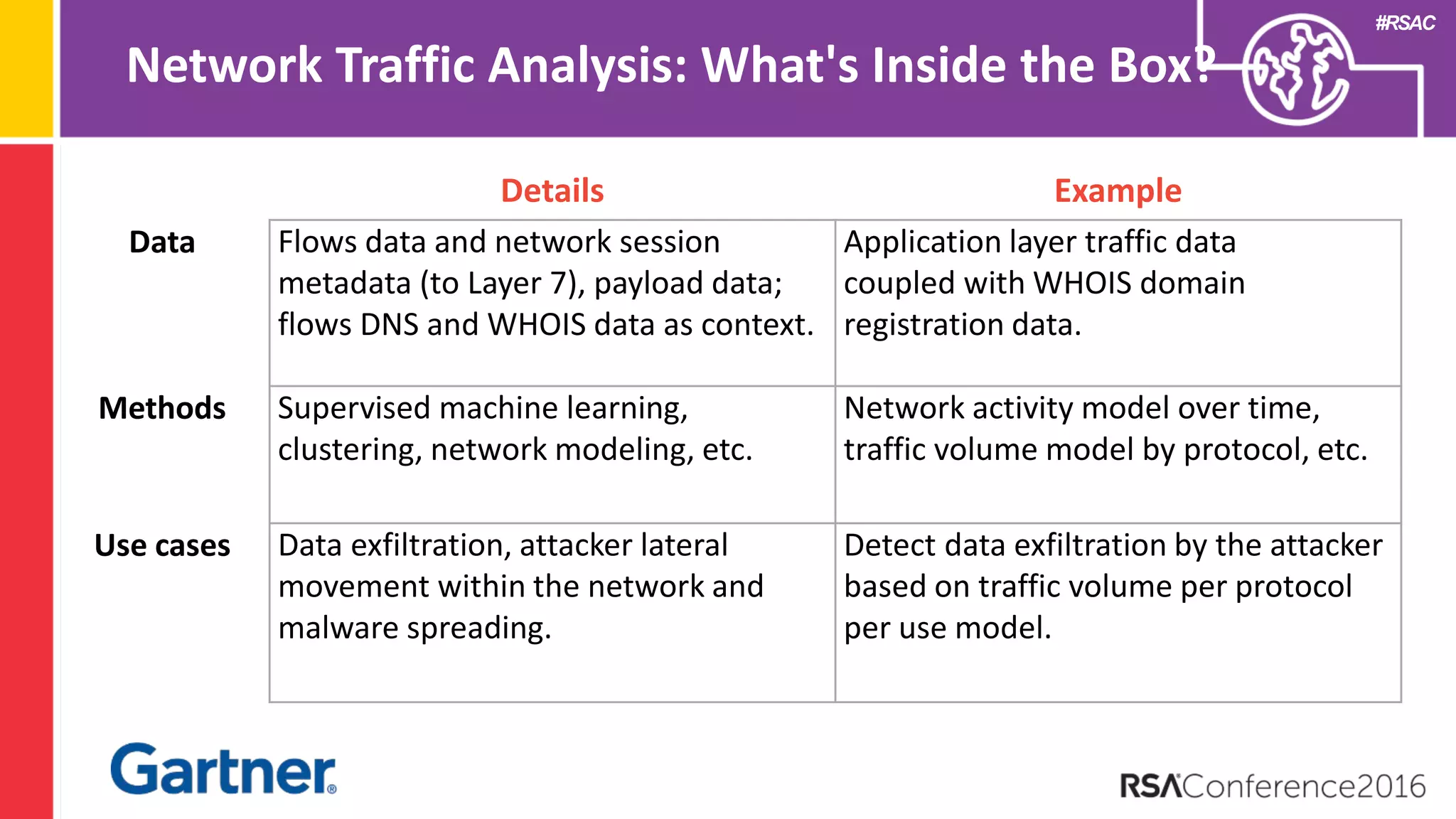
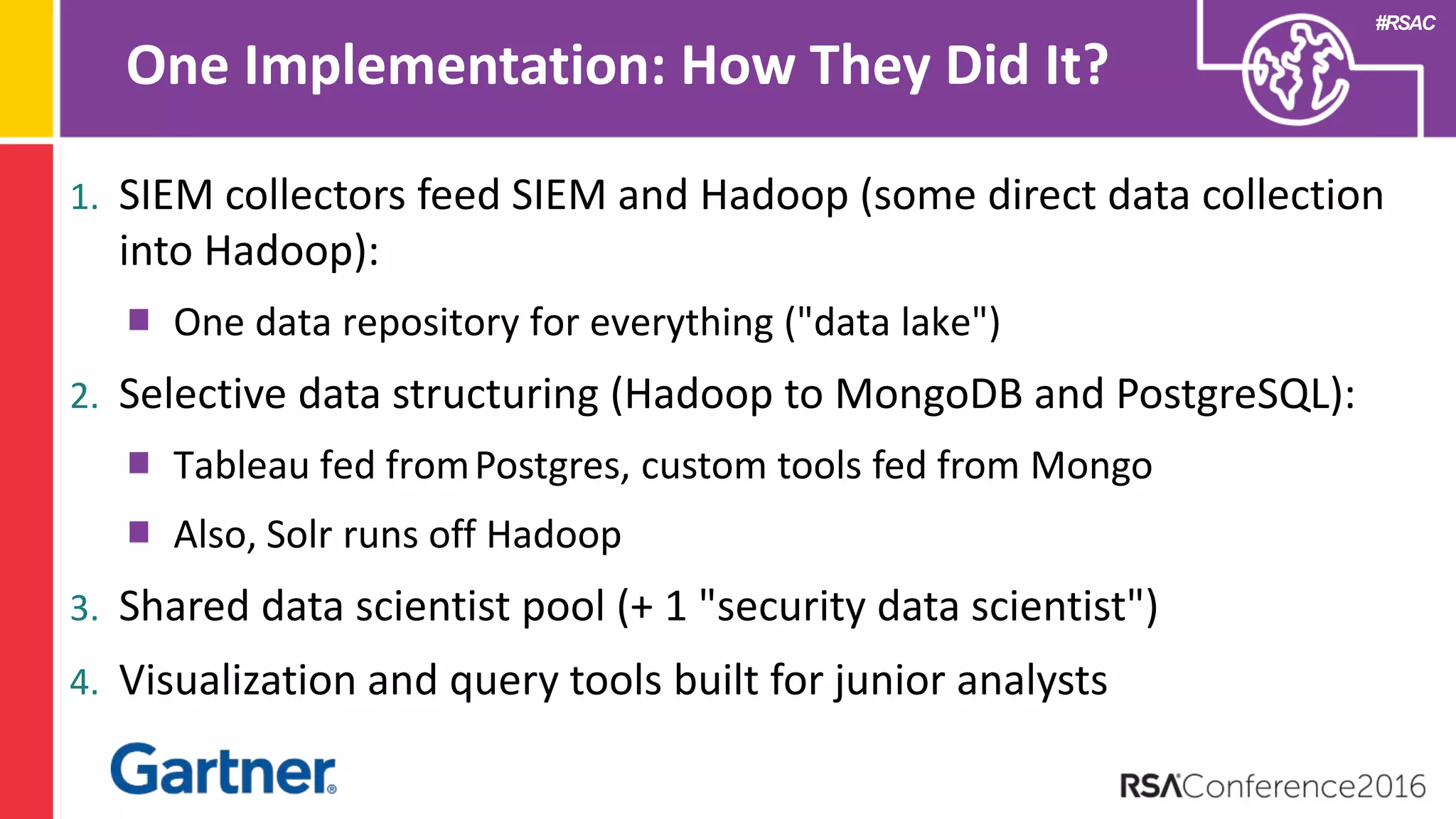
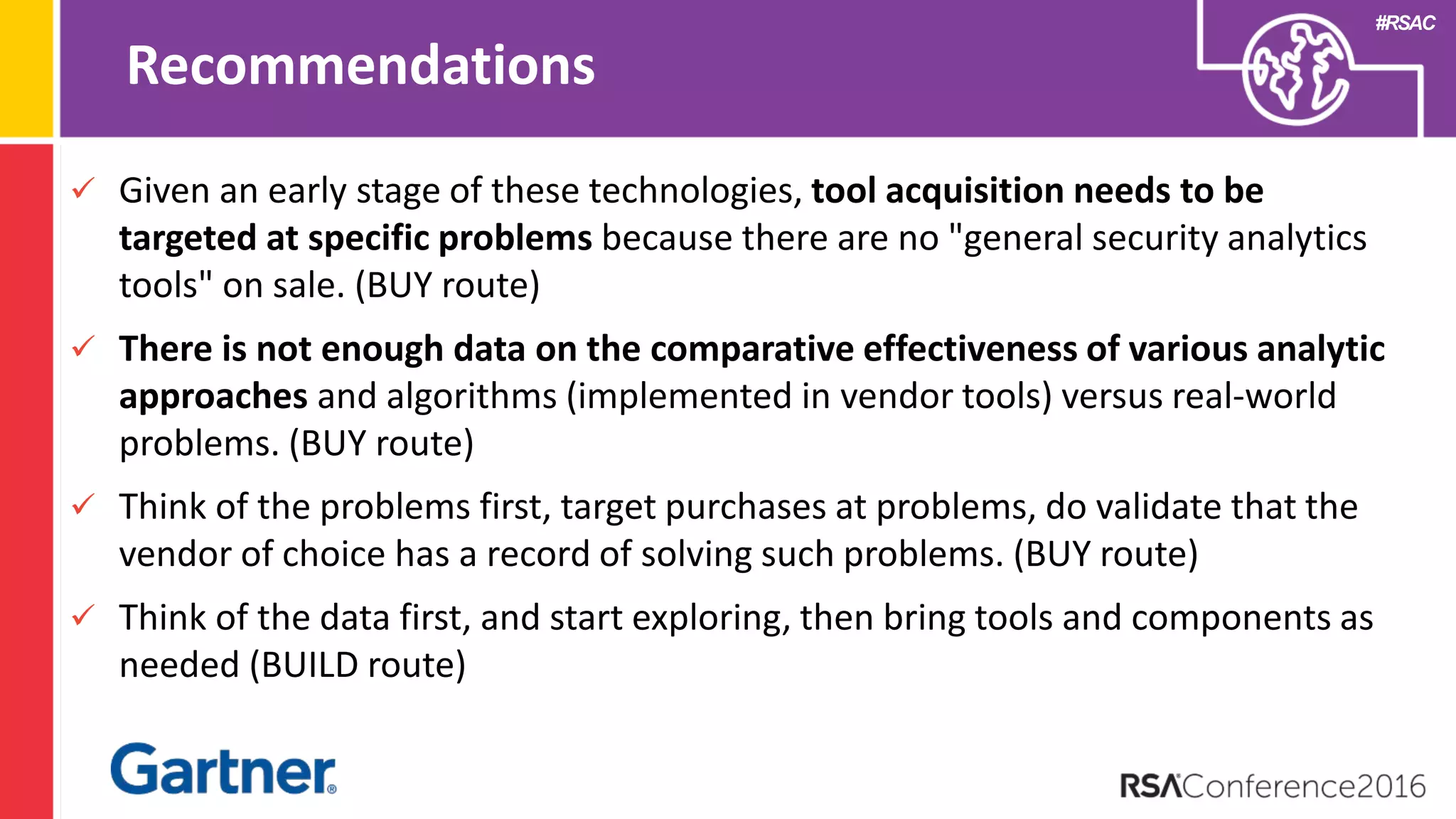
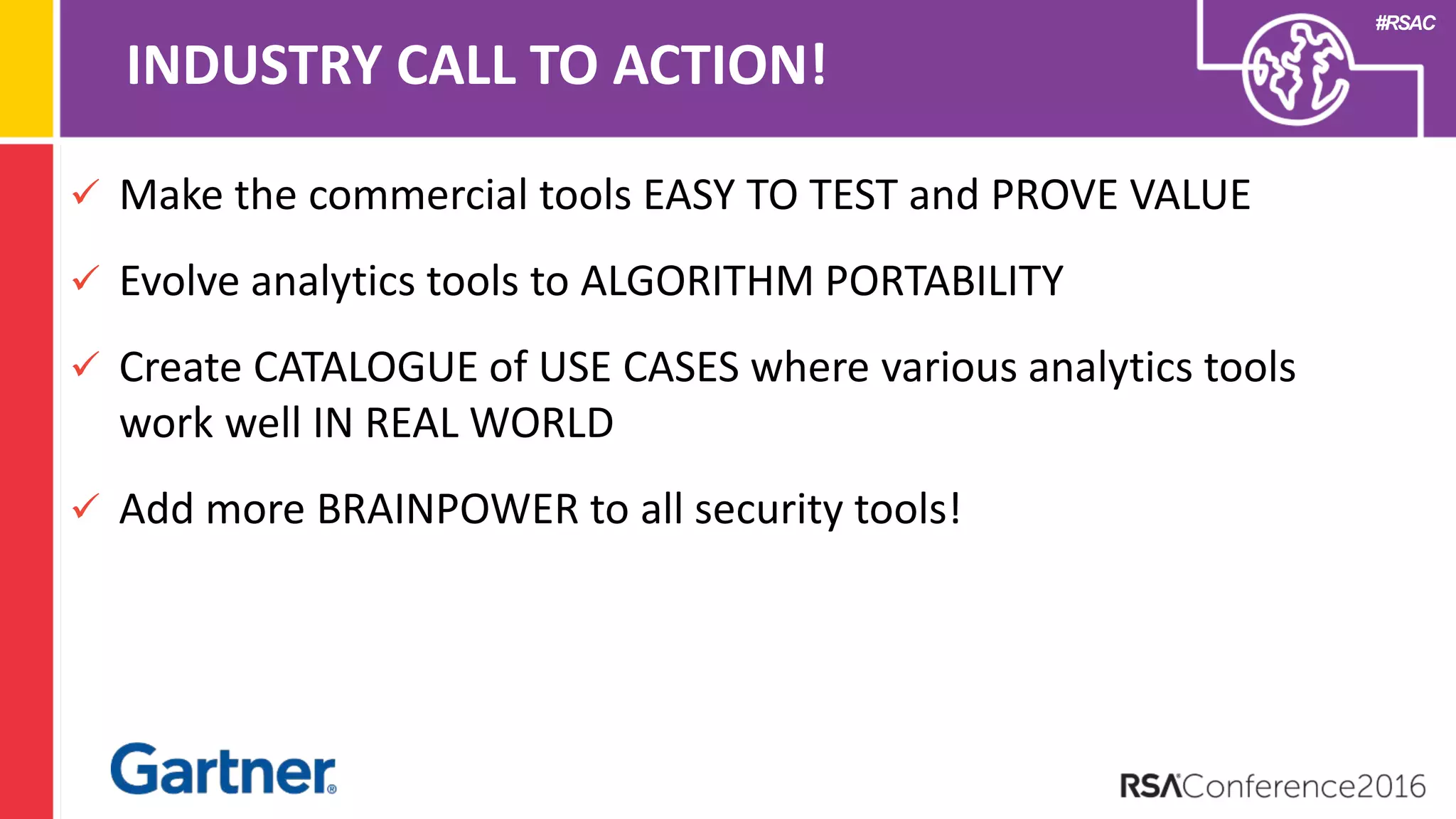
The document discusses the fundamentals of security analytics, emphasizing the importance of data collection, processing methods, and practical use cases to enhance threat detection and alert prioritization. It outlines key factors for success, such as adopting an analytic mindset, exploring data rather than relying solely on vendor solutions, and the necessity of building customized analytics capabilities for security problems. Additionally, it highlights the diverse tools available in the market and stresses the importance of targeted acquisition based on specific problems and data exploration.