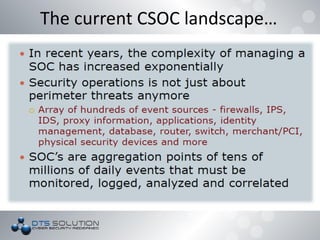
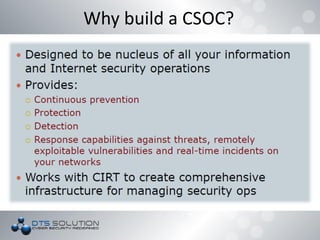
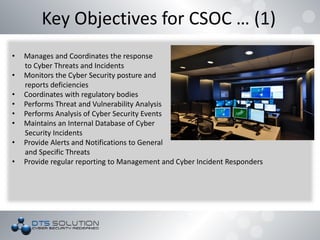
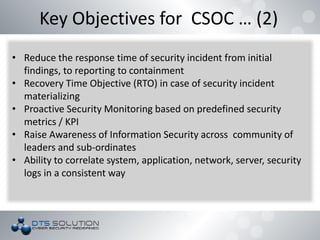
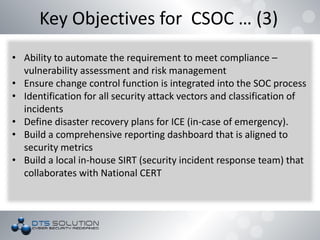
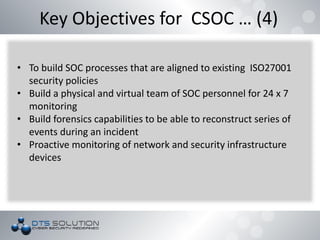
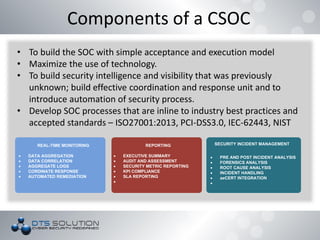
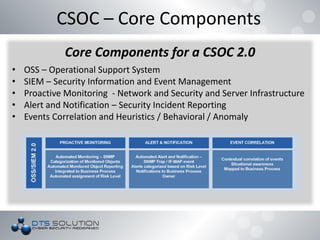
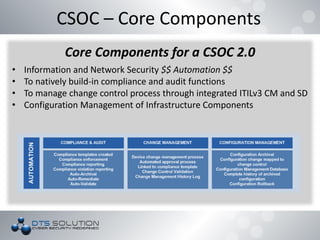
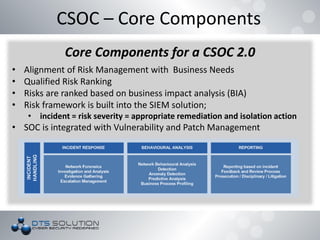
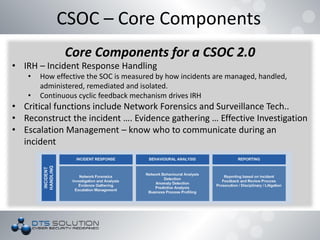
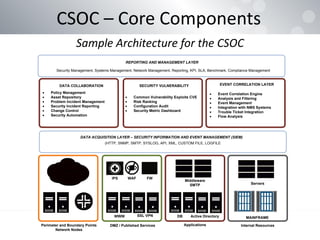
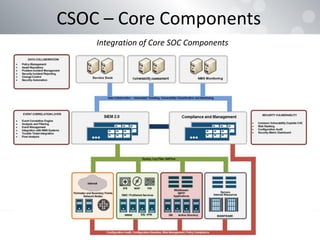
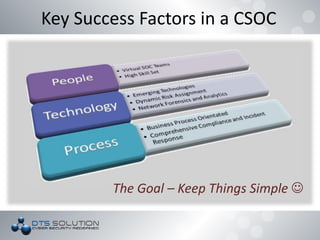
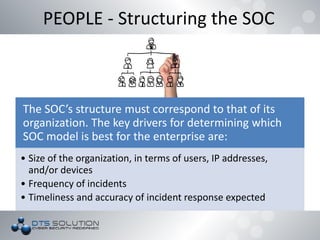
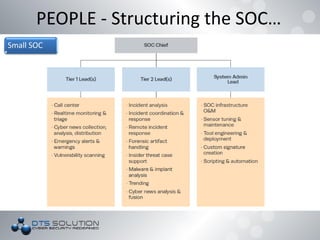
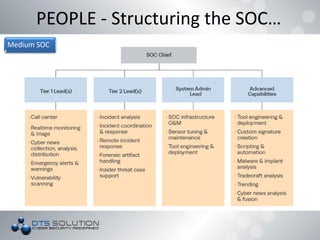
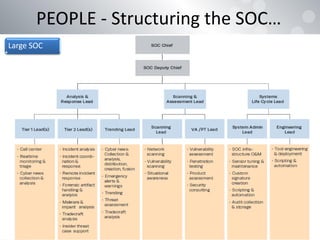
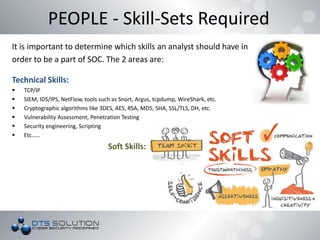
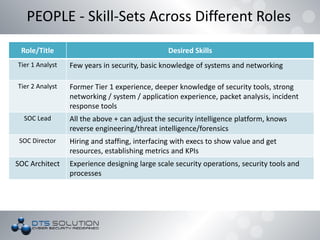
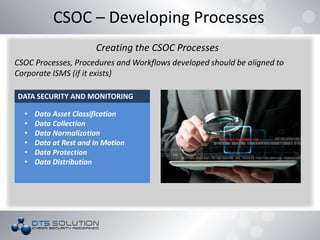
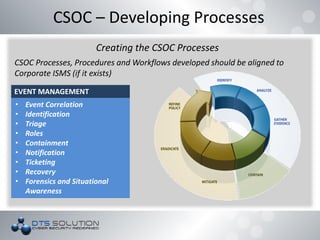
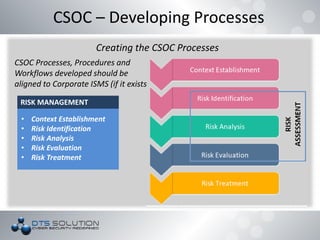
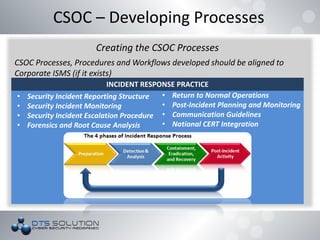
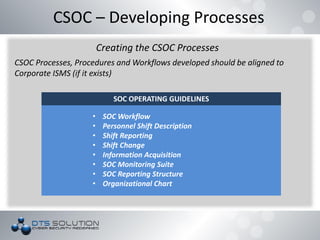
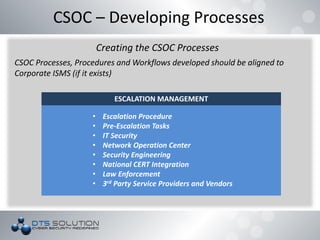
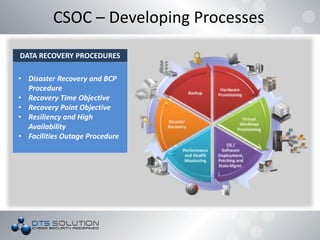
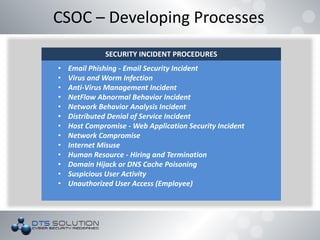
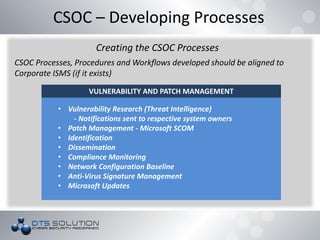
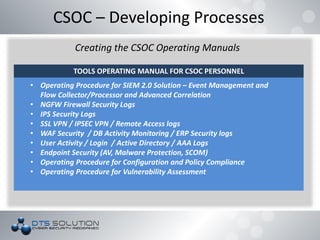
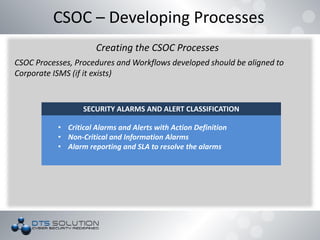
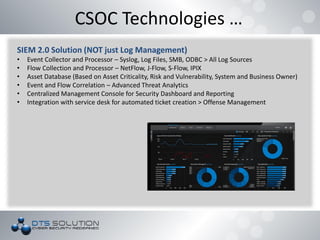
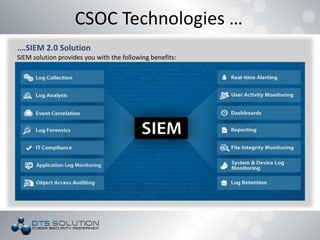
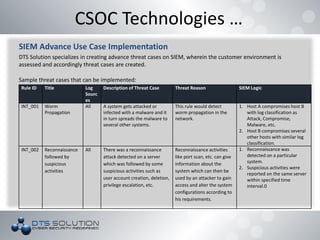
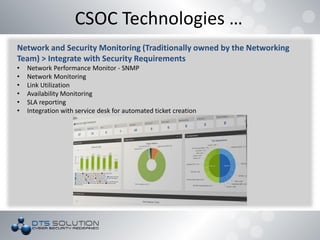
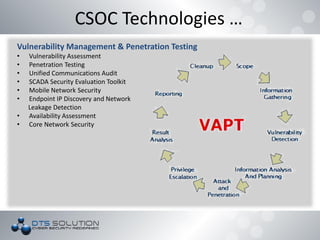
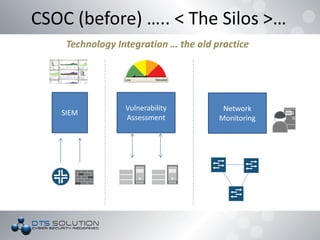
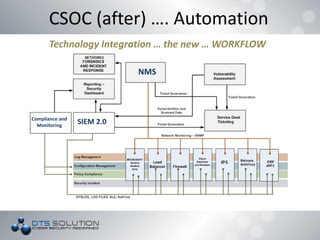
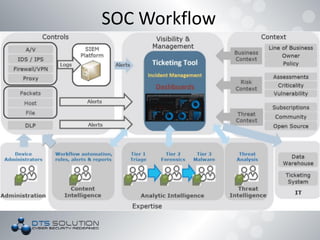
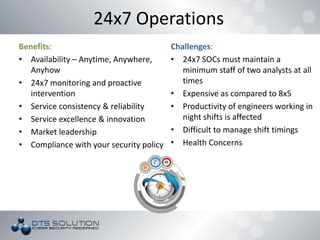
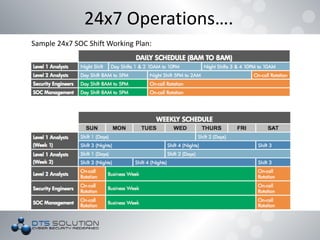
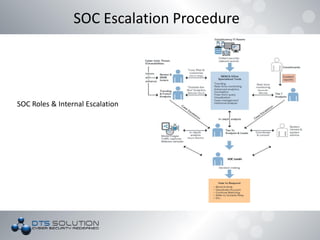
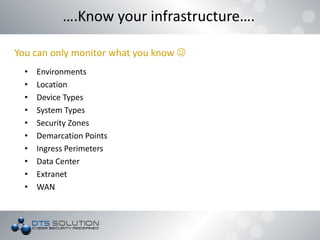
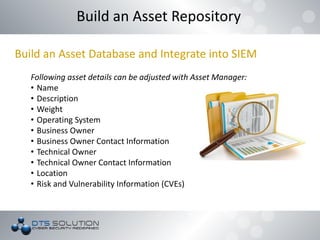
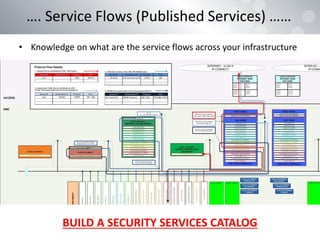
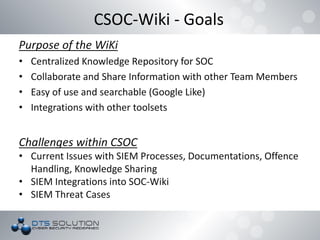
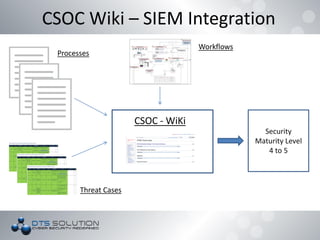
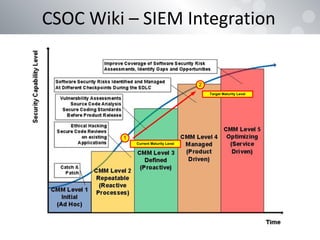
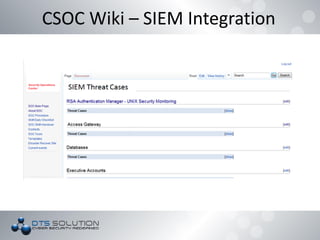
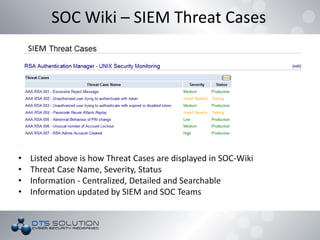
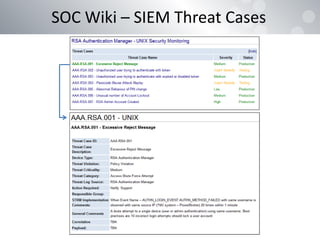
This document discusses building a cyber security operations center (CSOC). It covers the need for a CSOC, its core components including security information and event management (SIEM), and integrating components like monitoring, alerting, and reporting. Key aspects that are important for a successful CSOC are people, processes, and technology. The roles and skills required for people in the CSOC and training needs are outlined. Developing standardized processes, procedures and workflows that align with frameworks like ISO are also discussed.