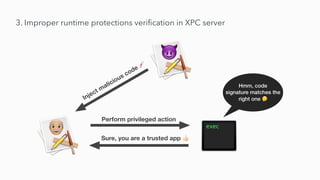
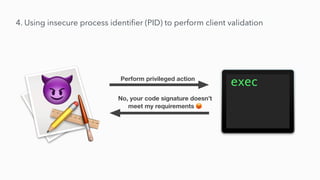
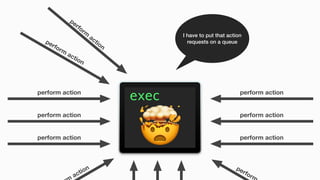
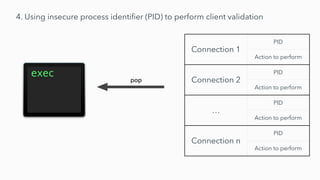
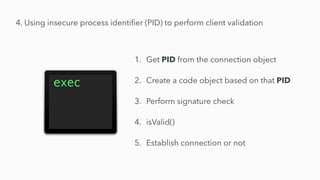
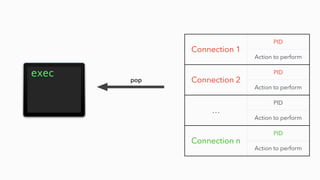
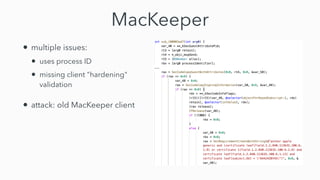
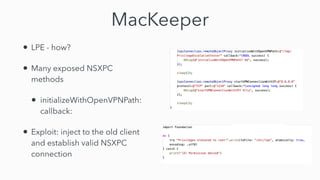
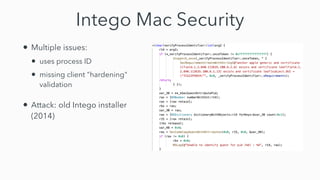
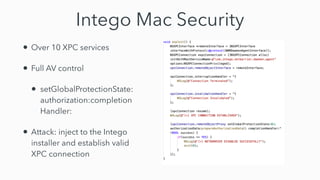
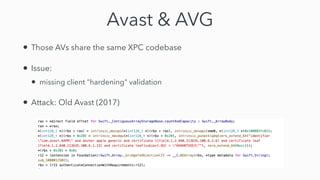
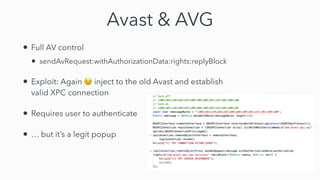
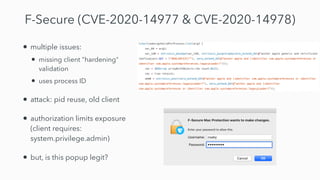
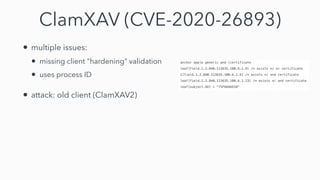
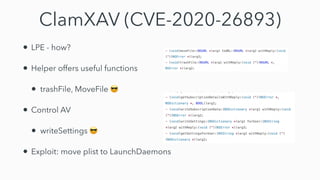
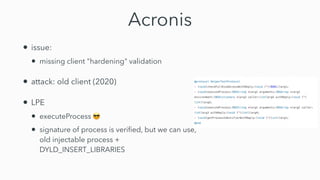
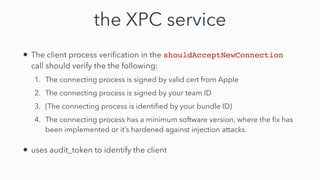
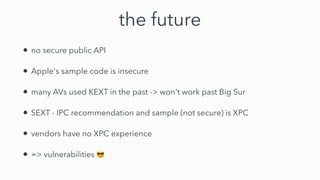
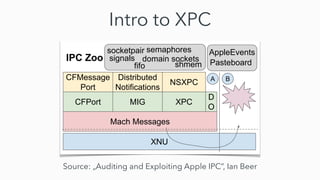
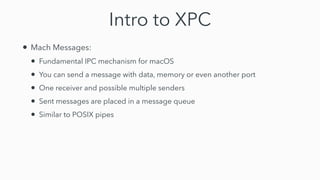
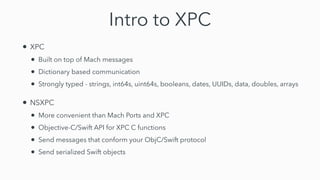
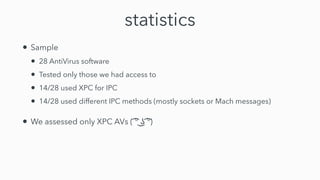
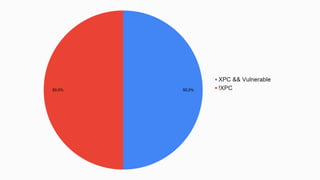
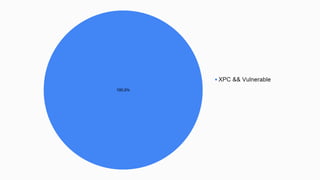
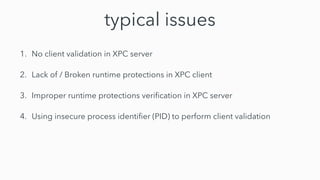
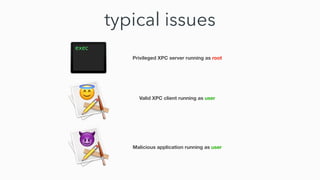
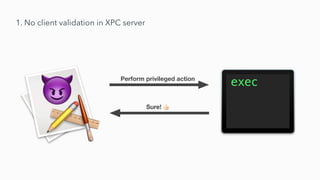
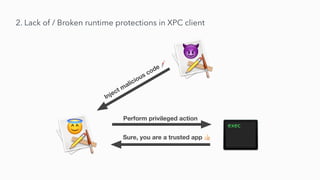
The document discusses the exploitation of XPC (cross-process communication) in antivirus software, highlighting various issues such as lacking client validation and runtime protections across 28 antivirus solutions. It provides statistics and examples of vulnerable applications like MacKeeper and Intego, illustrating potential attacks and weaknesses in their design. Recommendations for developers include proper client verification and utilizing hardened runtimes to mitigate these vulnerabilities.








![3. Improper runtime protections veri
fi
cation in XPC server
SecRequirement = “anchor apple generic and identi
fi
er
‘com.yourcompany.app’ and certi
fi
cate leaf[subject.OU] =
‘ABCDEFG’”
SecRequirement = “anchor apple generic and identi
fi
er
‘com.yourcompany.app’ and certi
fi
cate leaf[subject.OU] =
‘ABCDEFG’”
==](https://image.slidesharecdn.com/exploitingxpcinantivirus-210305070506/85/Exploiting-XPC-in-AntiVirus-21-320.jpg)