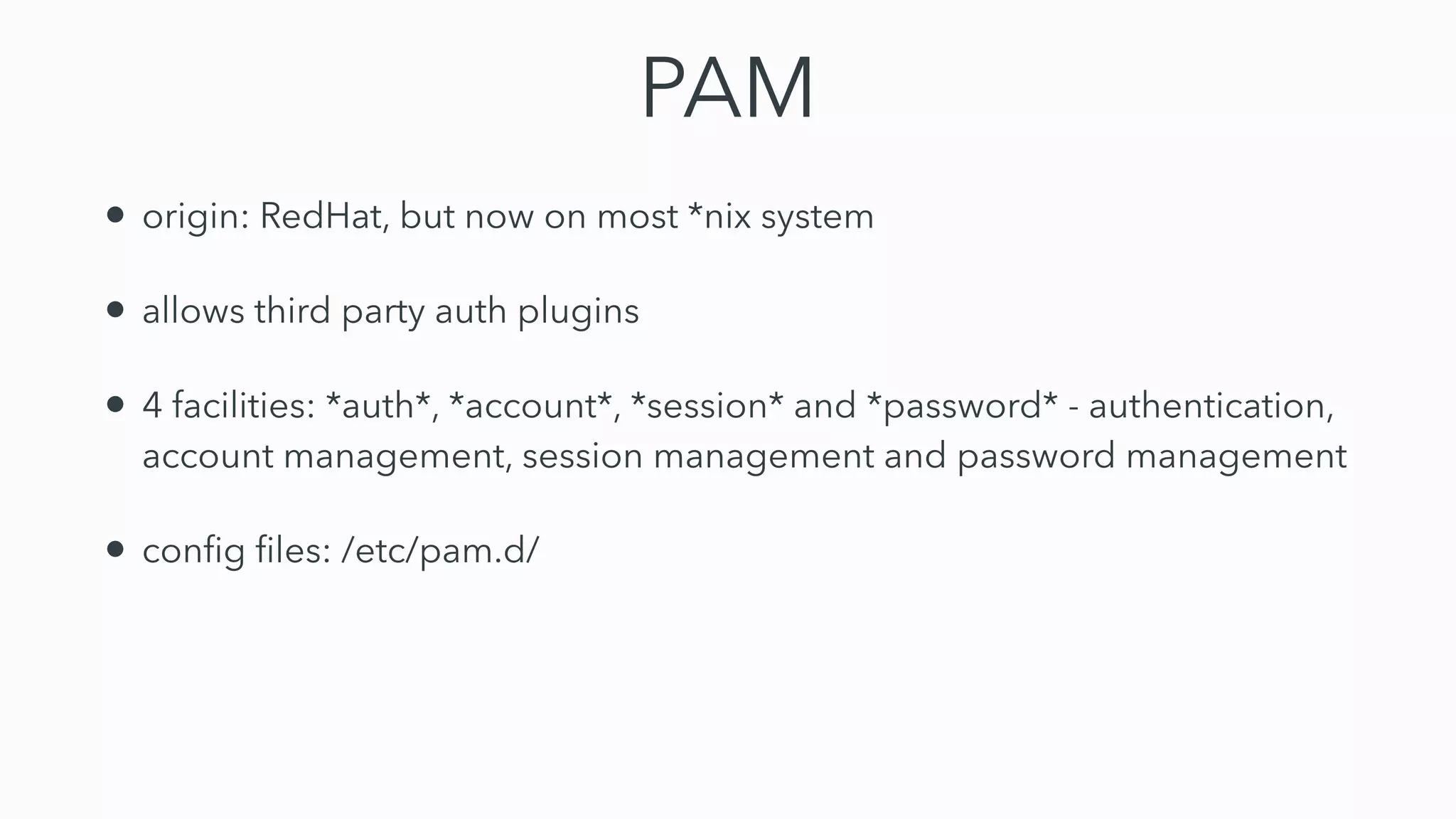
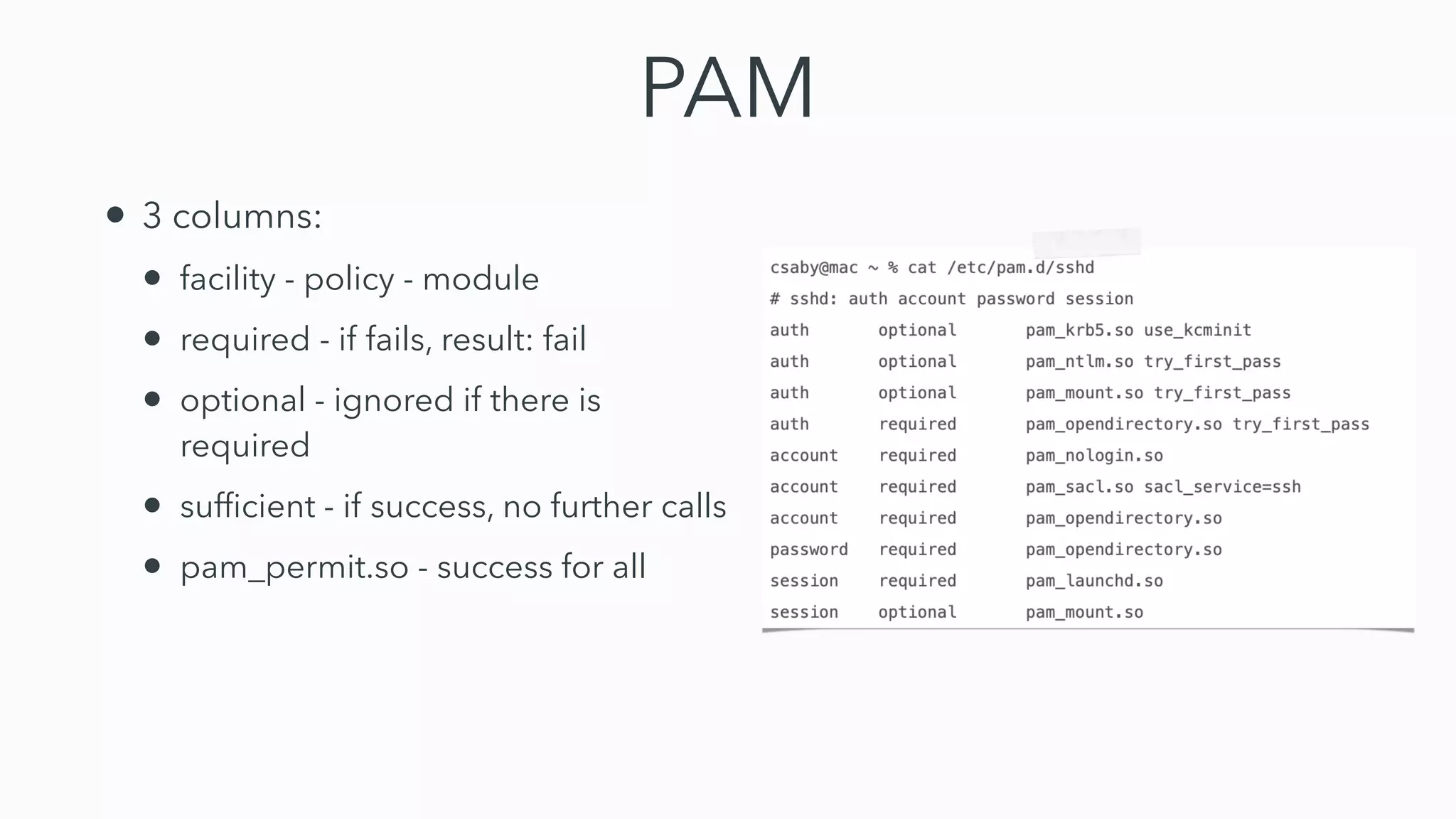
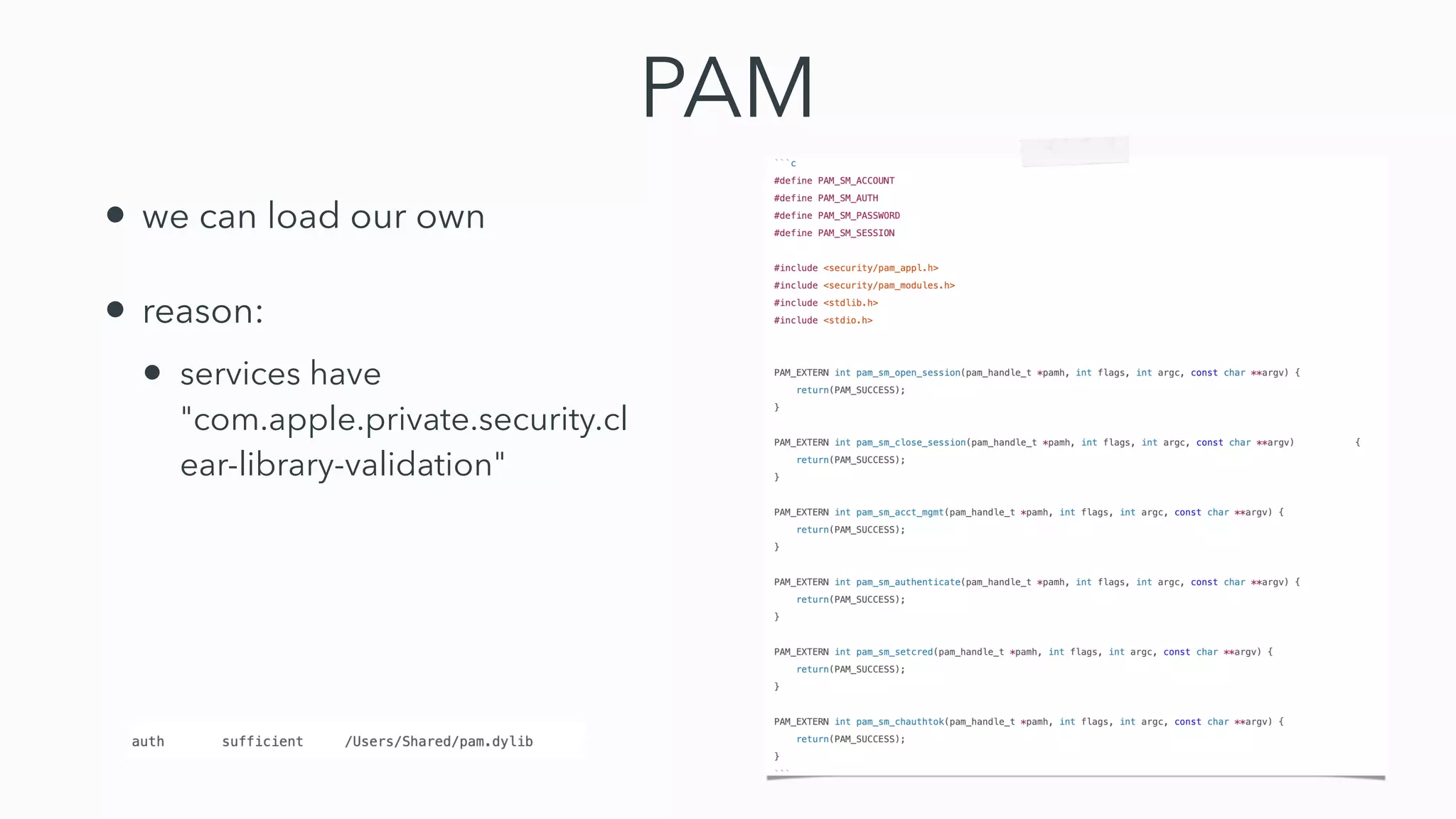
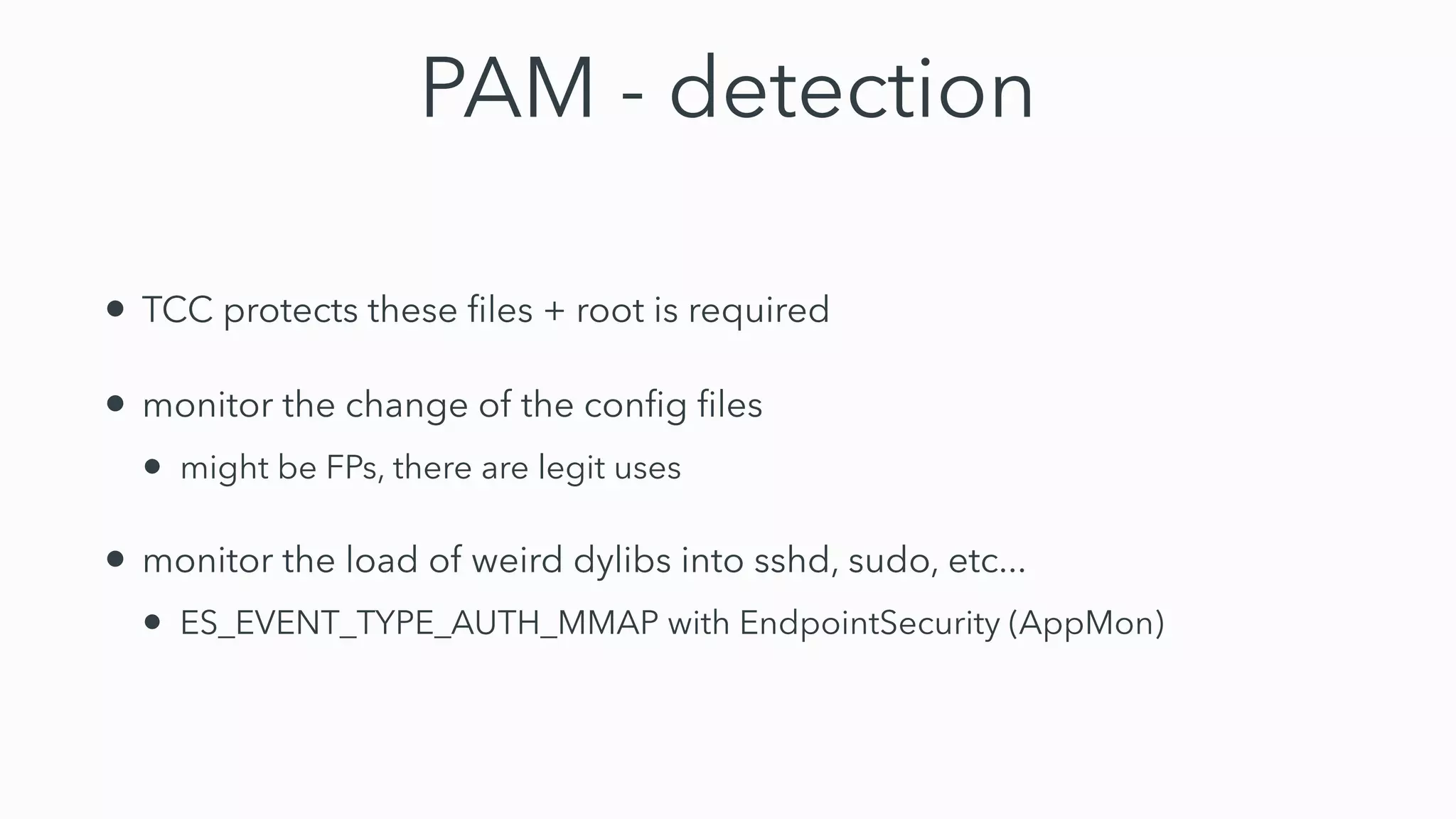
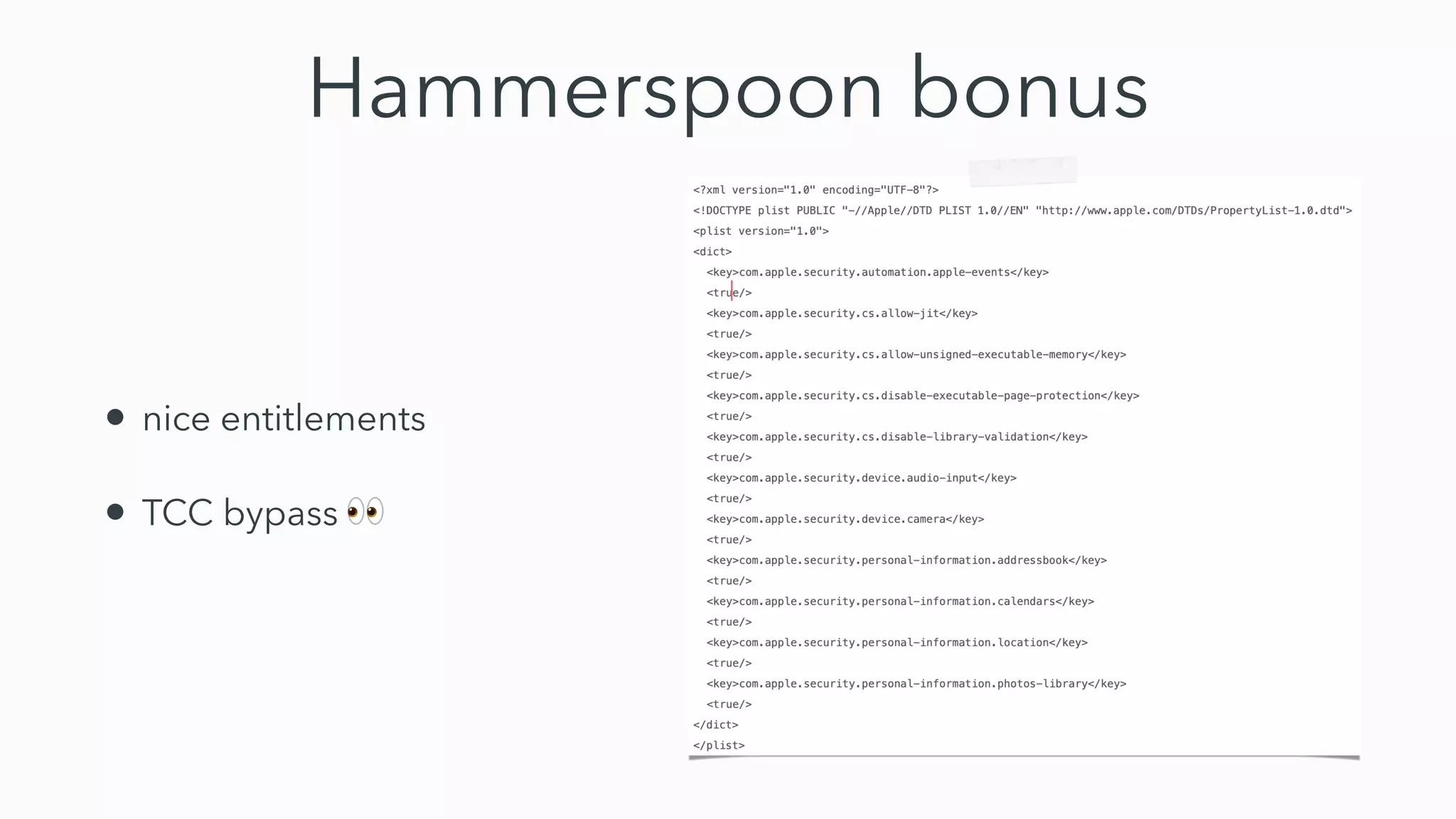
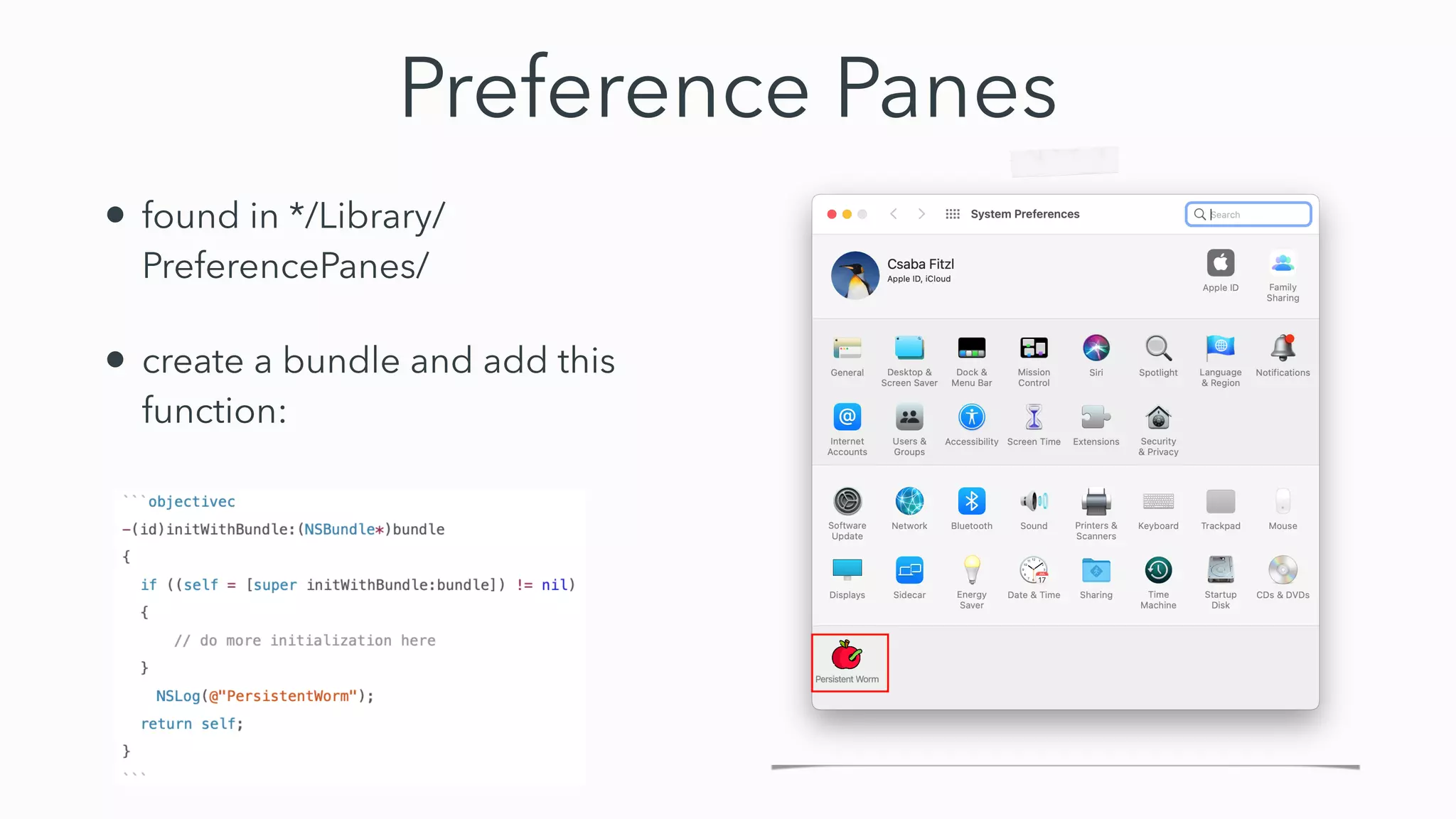
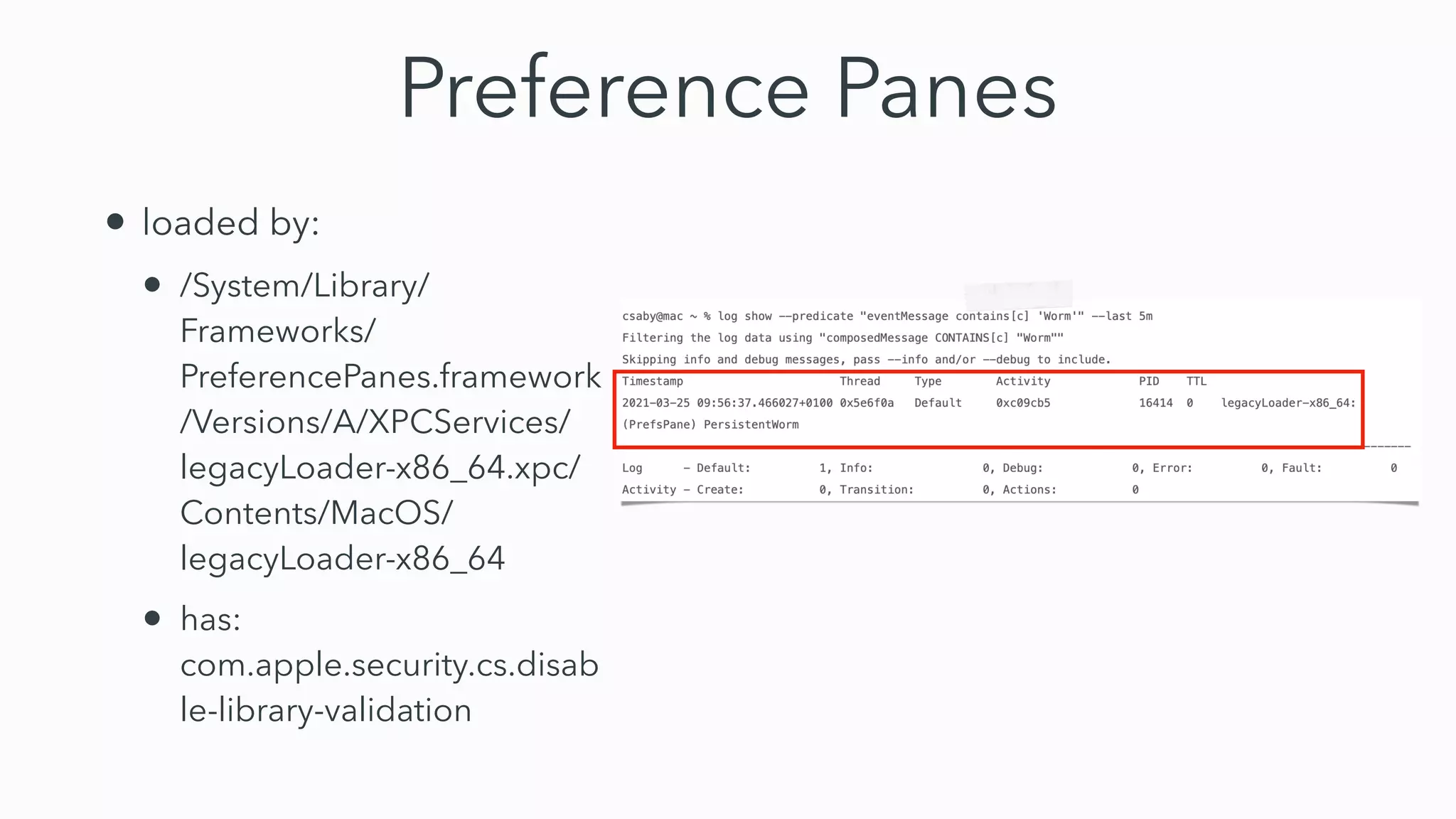
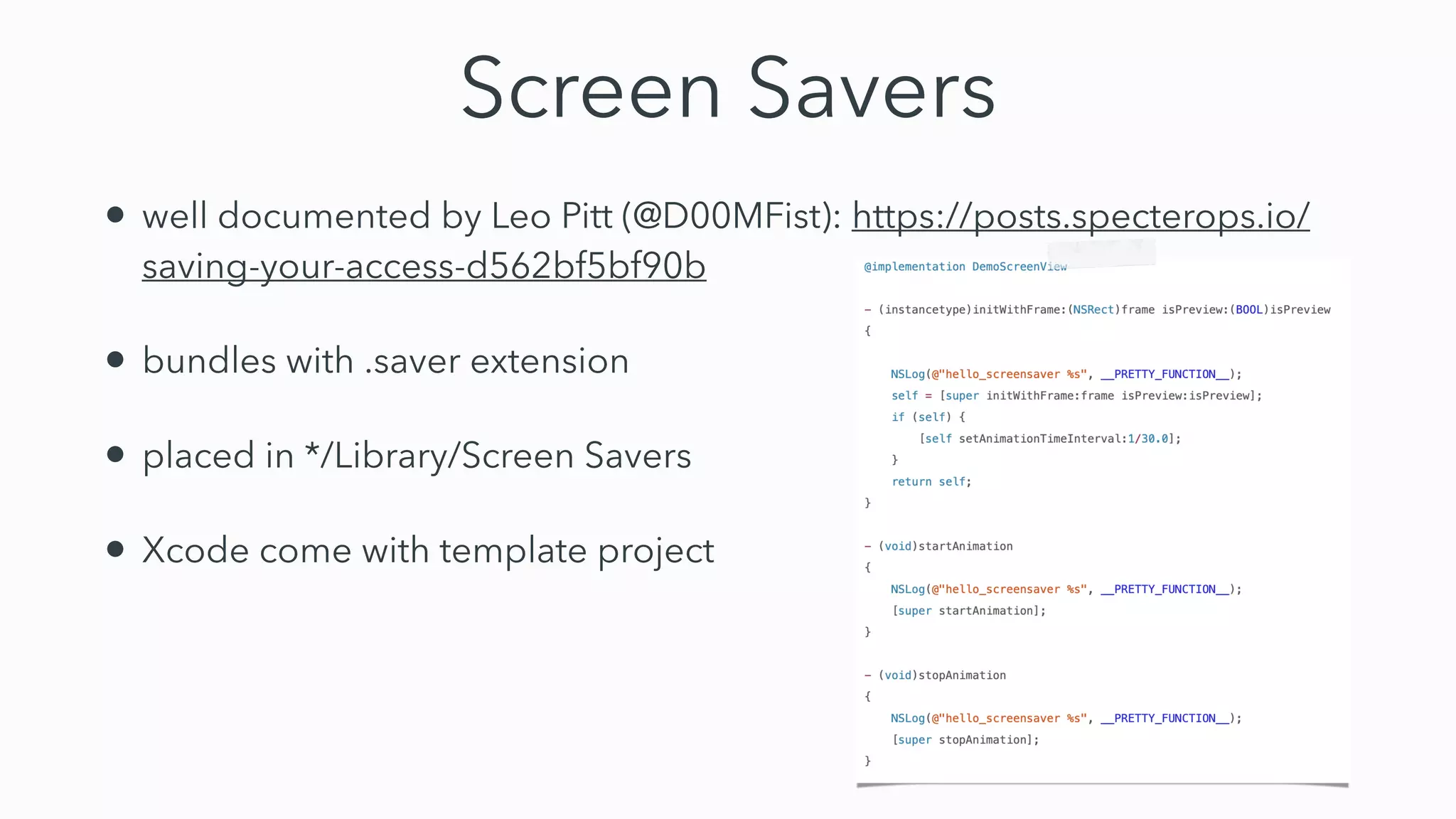
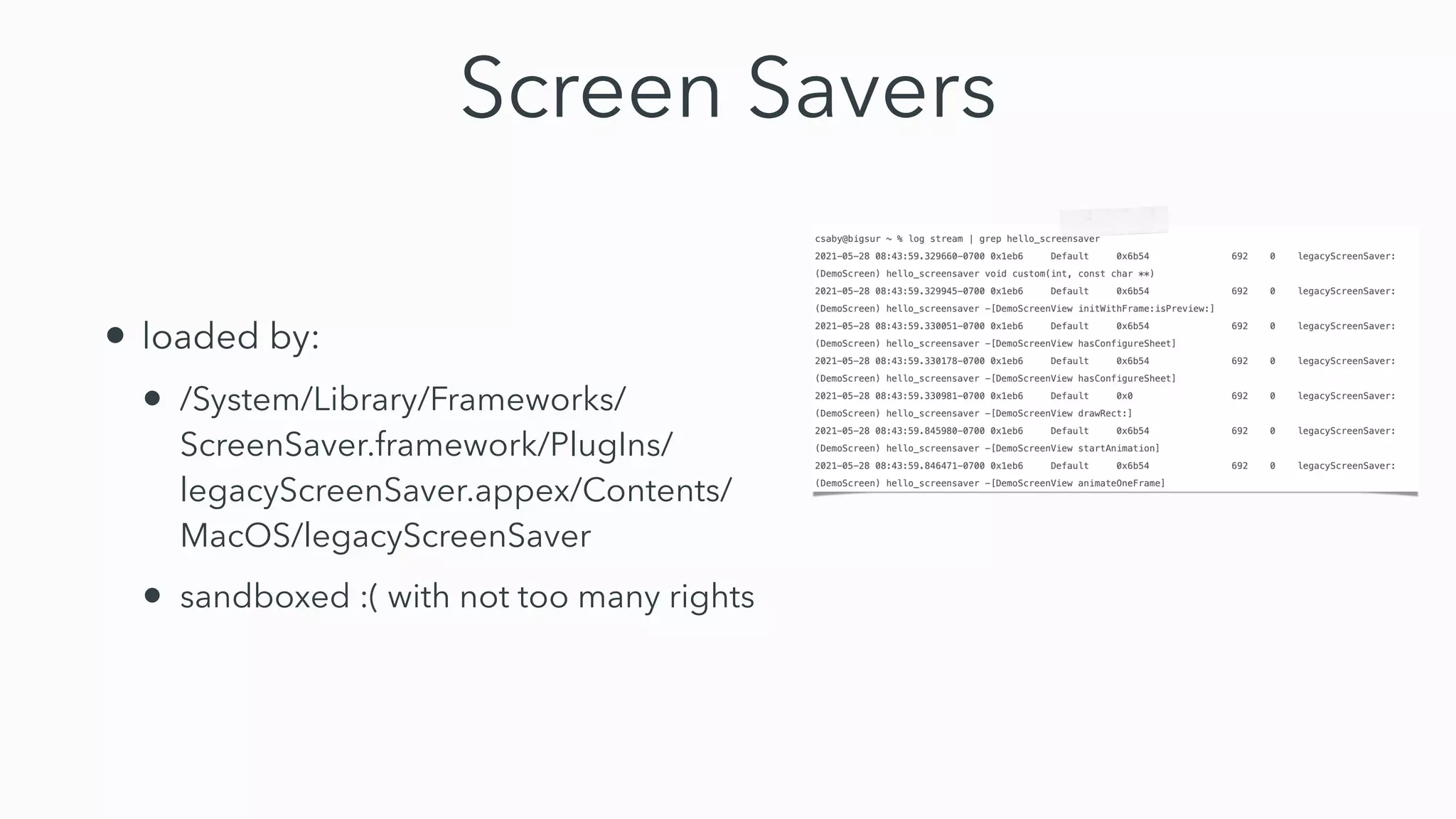
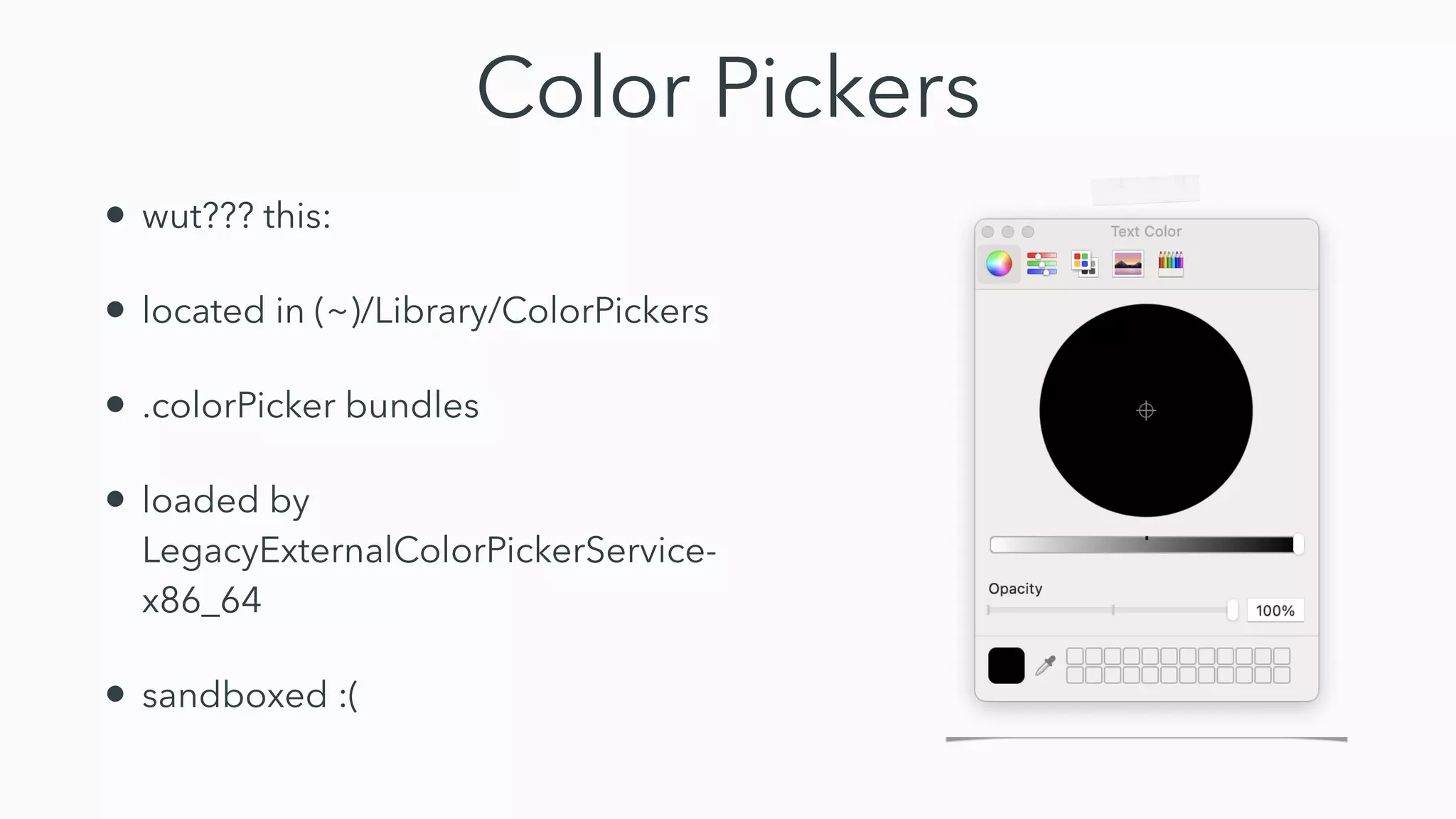
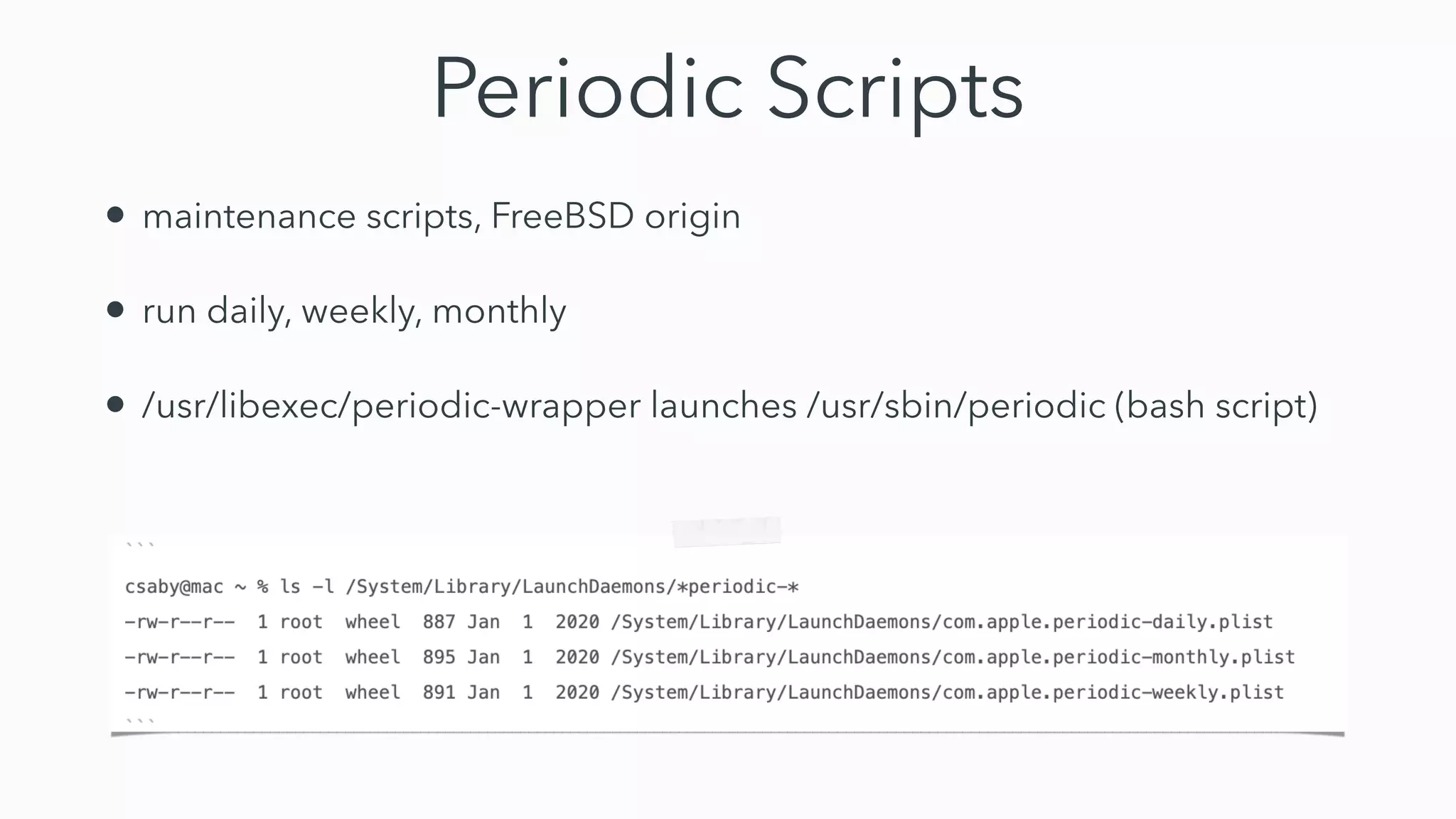
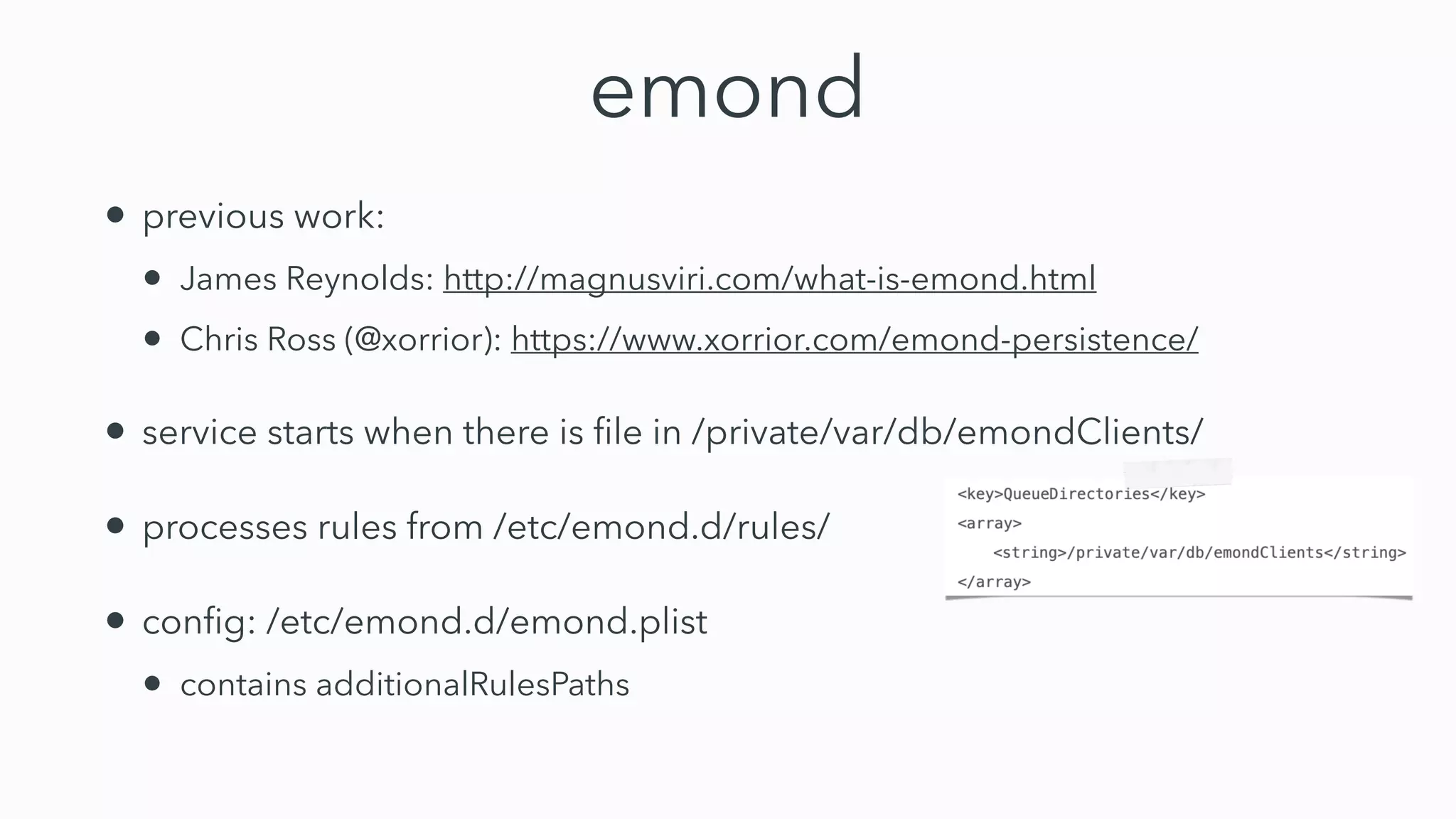
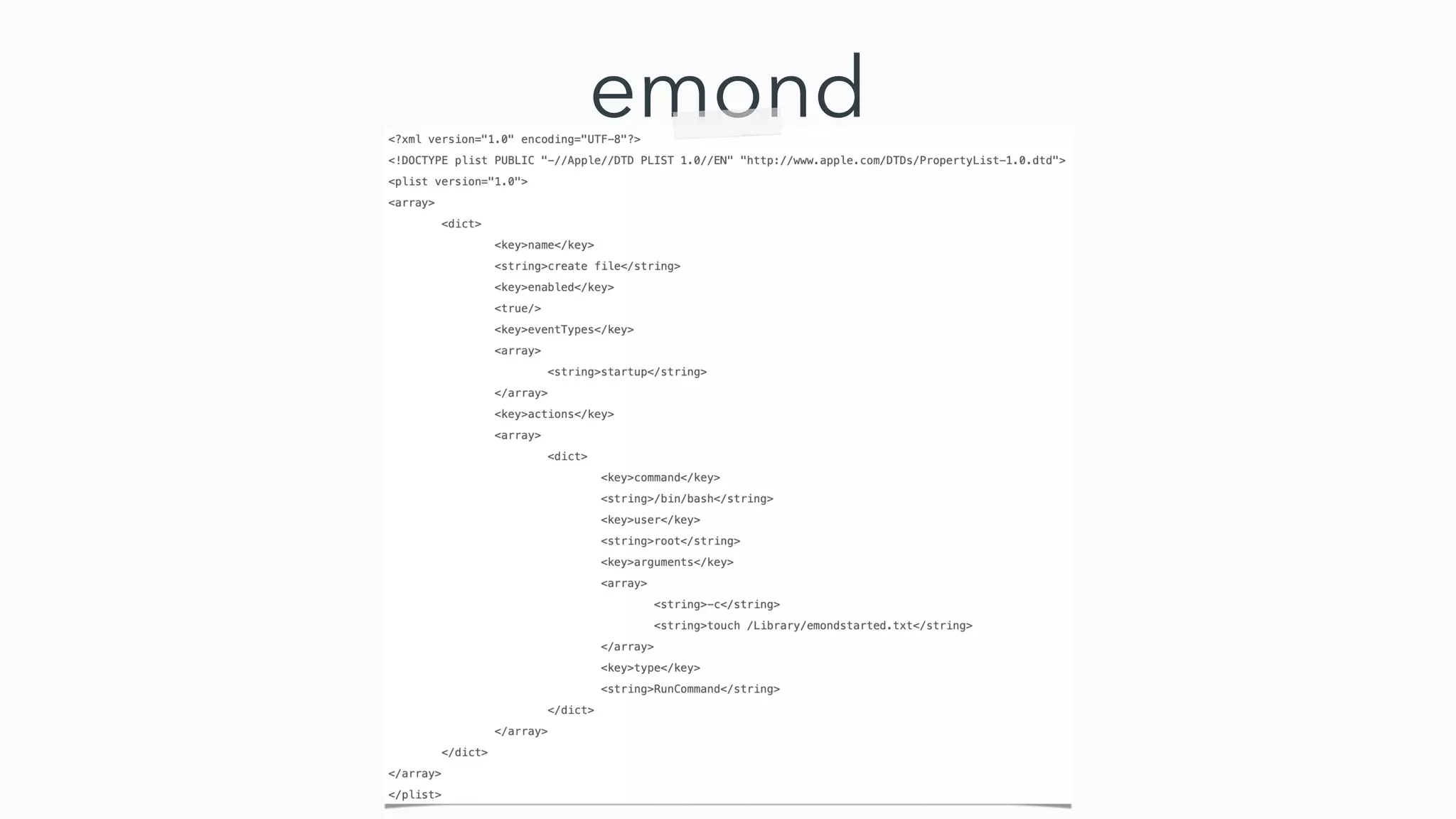
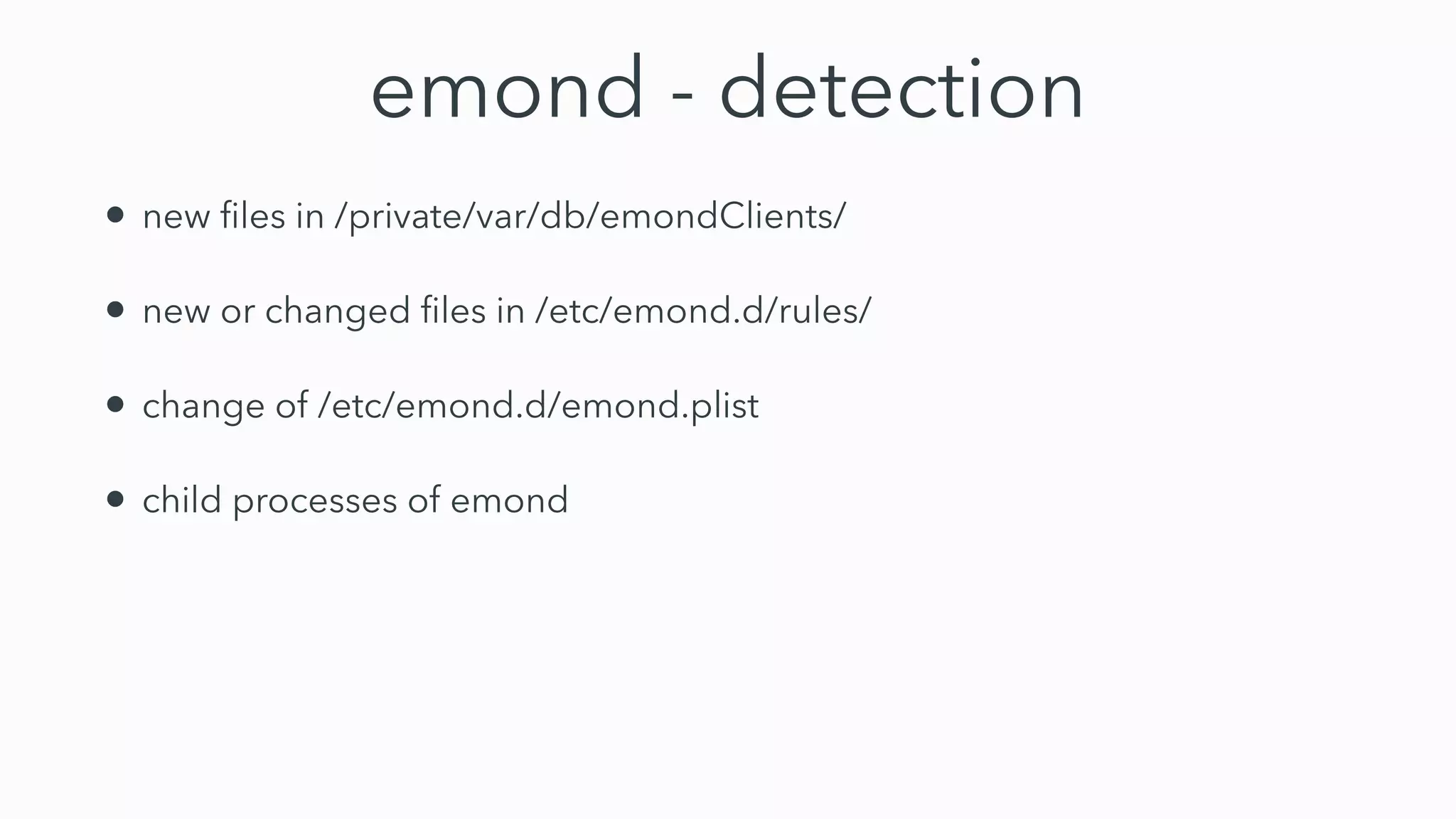
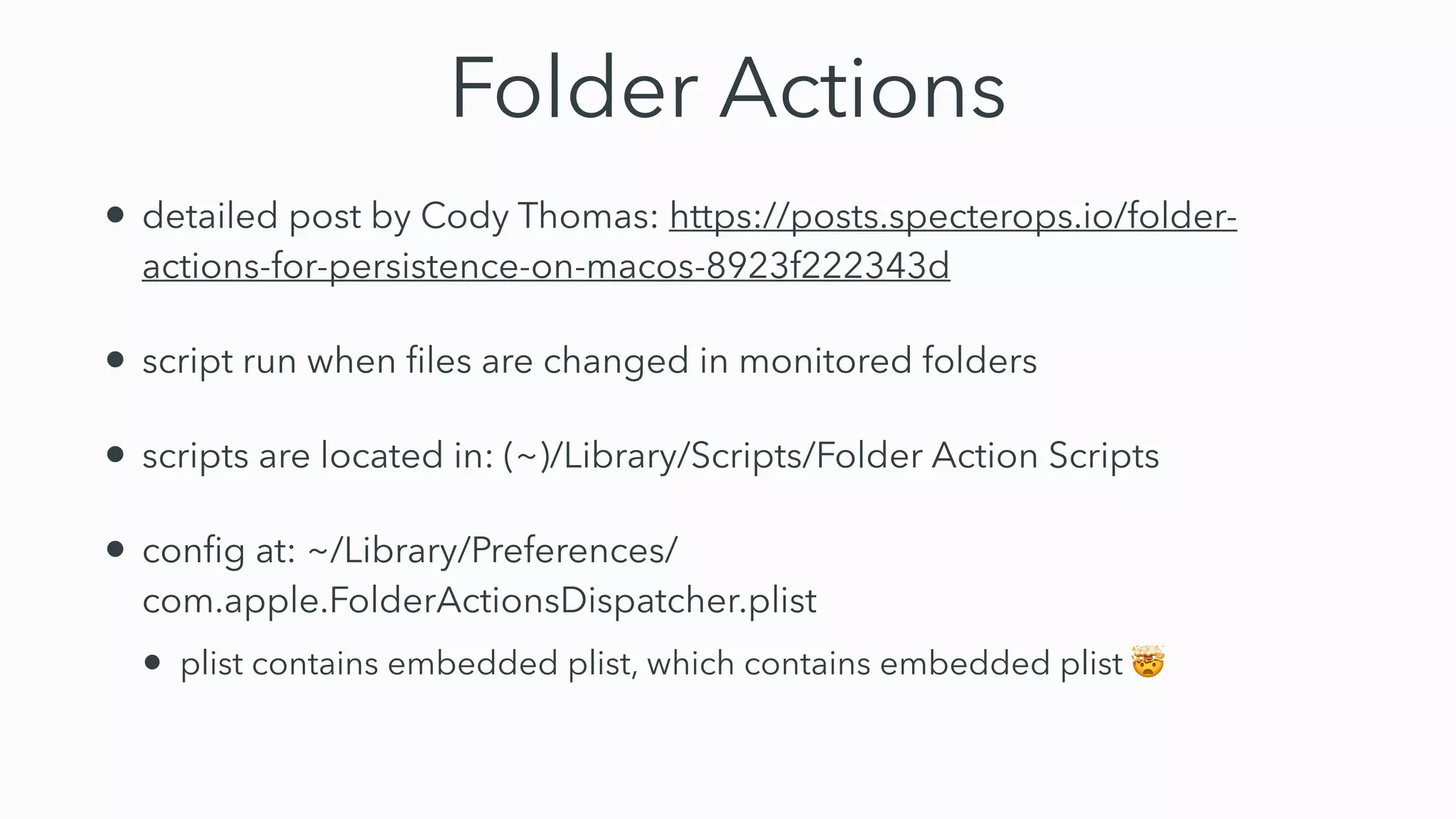
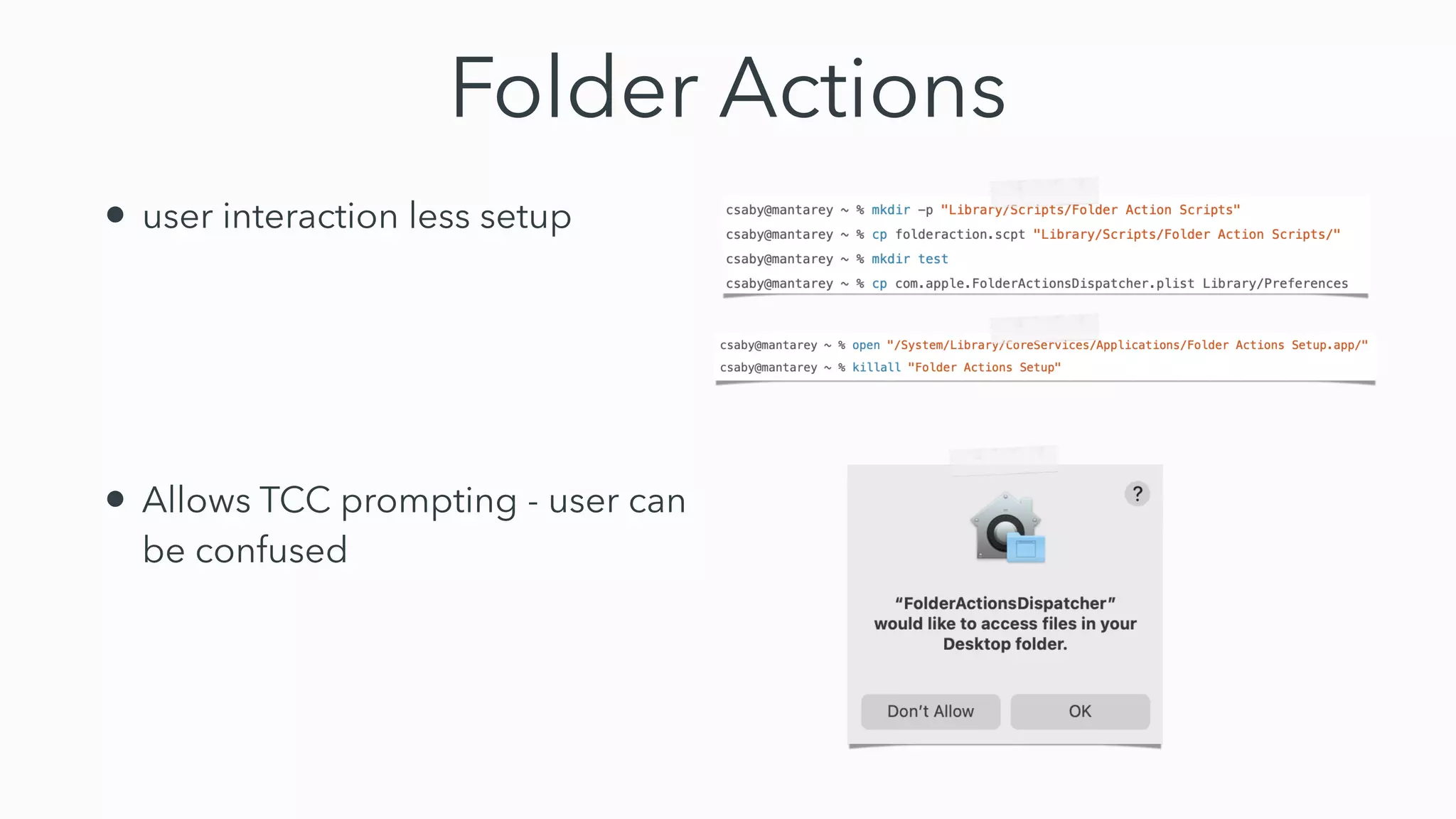
This document discusses 10 techniques for persistence on macOS beyond using LaunchAgents. It provides an overview of techniques such as modifying shell startup files, using Pluggable Authentication Modules (PAM), Hammerspoon, preference panes, screen savers, color pickers, periodic scripts, Terminal preferences, emond (the event monitor daemon), and folder actions. For each technique, it describes how it works and how it could be detected and monitored for malicious use. The conclusion is that while malware most commonly uses LaunchAgents, there are many unexplored persistence options that blue teams need to prepare for.


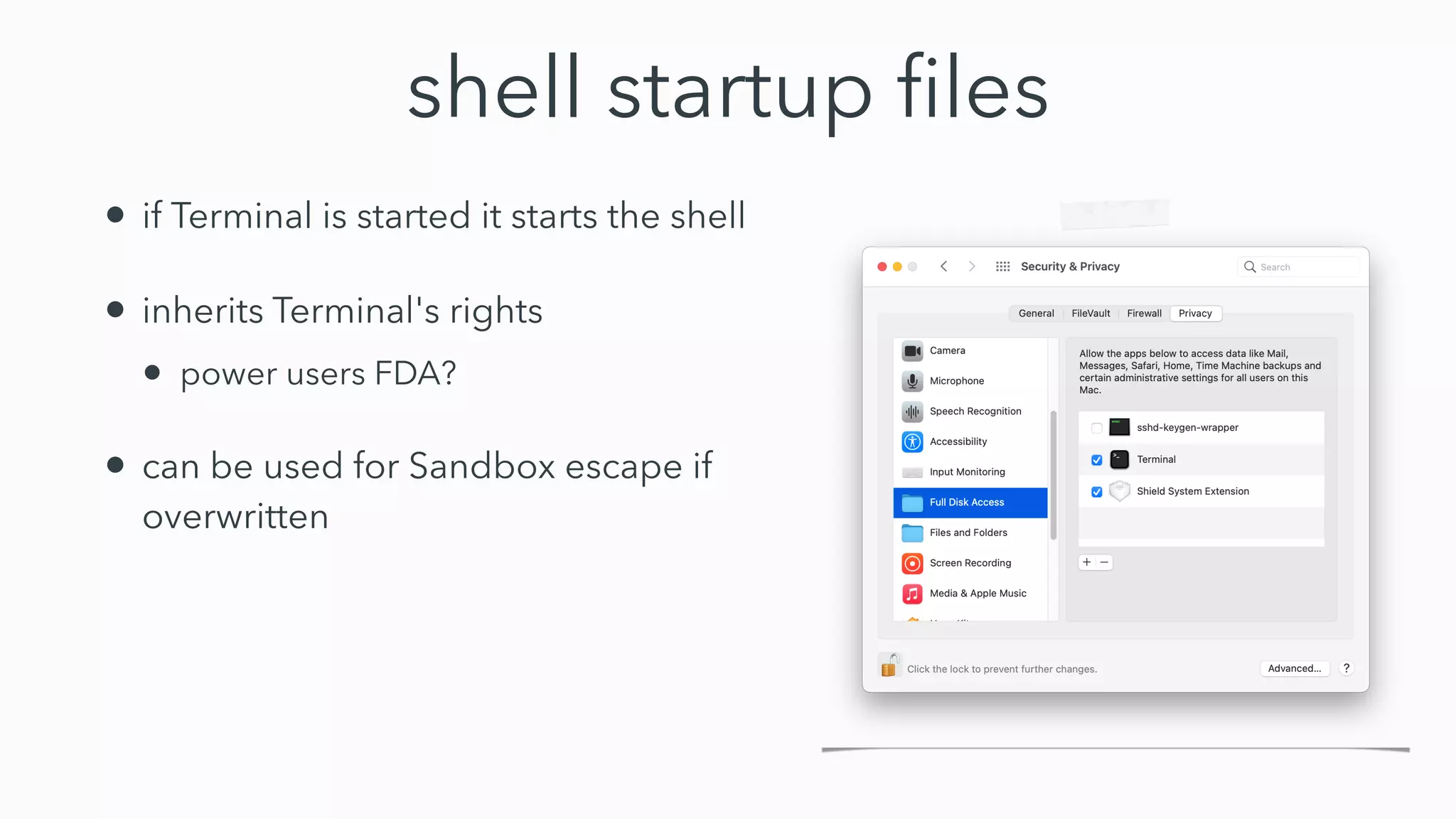
![shell startup
fi
les - detection?
• monitor for change of these
fi
les
• might be many FP, especially with power users
• chsh -s [new shell]
• changes default shell ()
• chpass
• can change multiple user attributes](https://image.slidesharecdn.com/securityfest-22-fitzl-beyond-220602113736-1e5926e2/75/SecurityFest-22-Fitzl-beyond-pdf-8-2048.jpg)