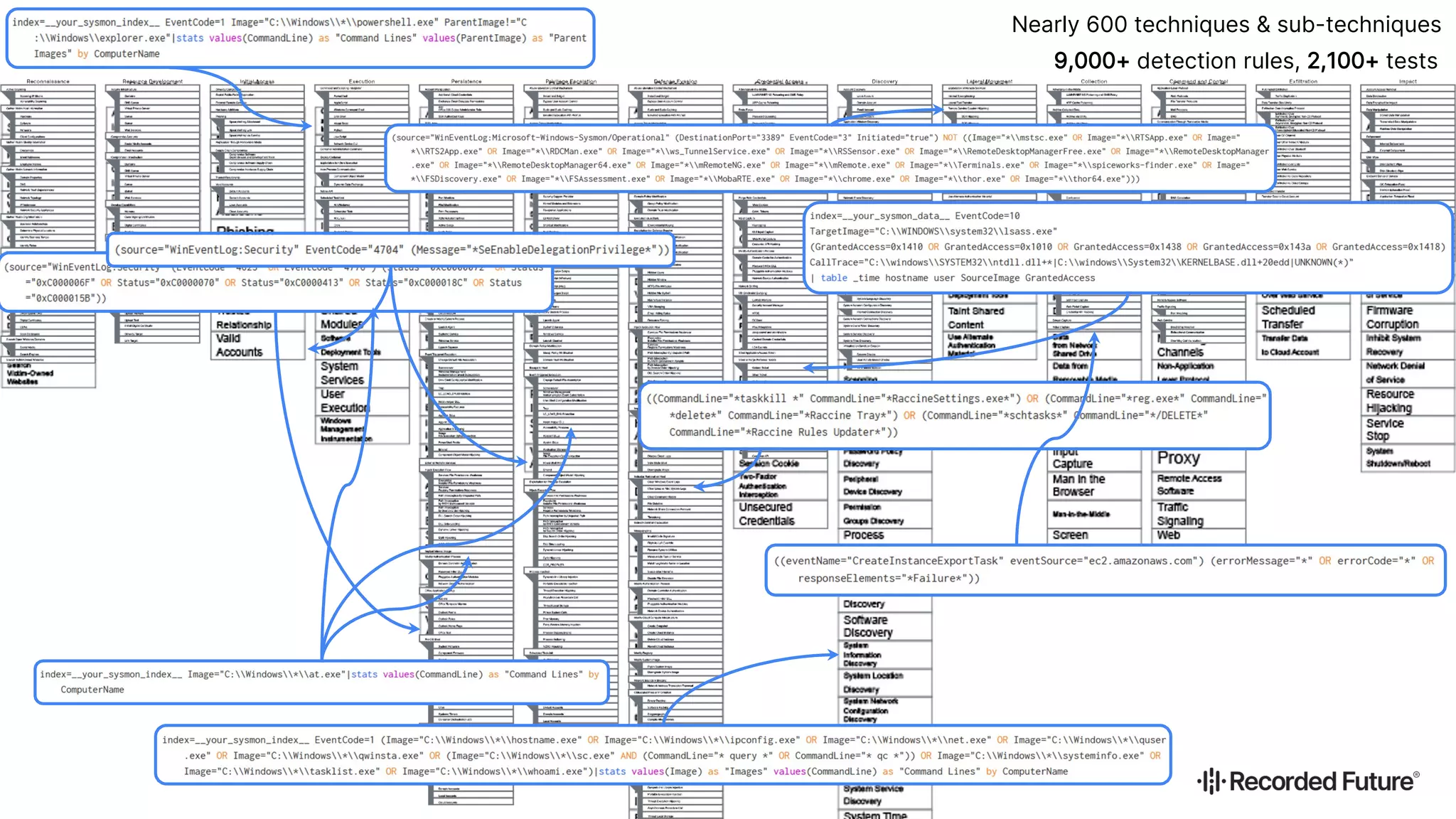
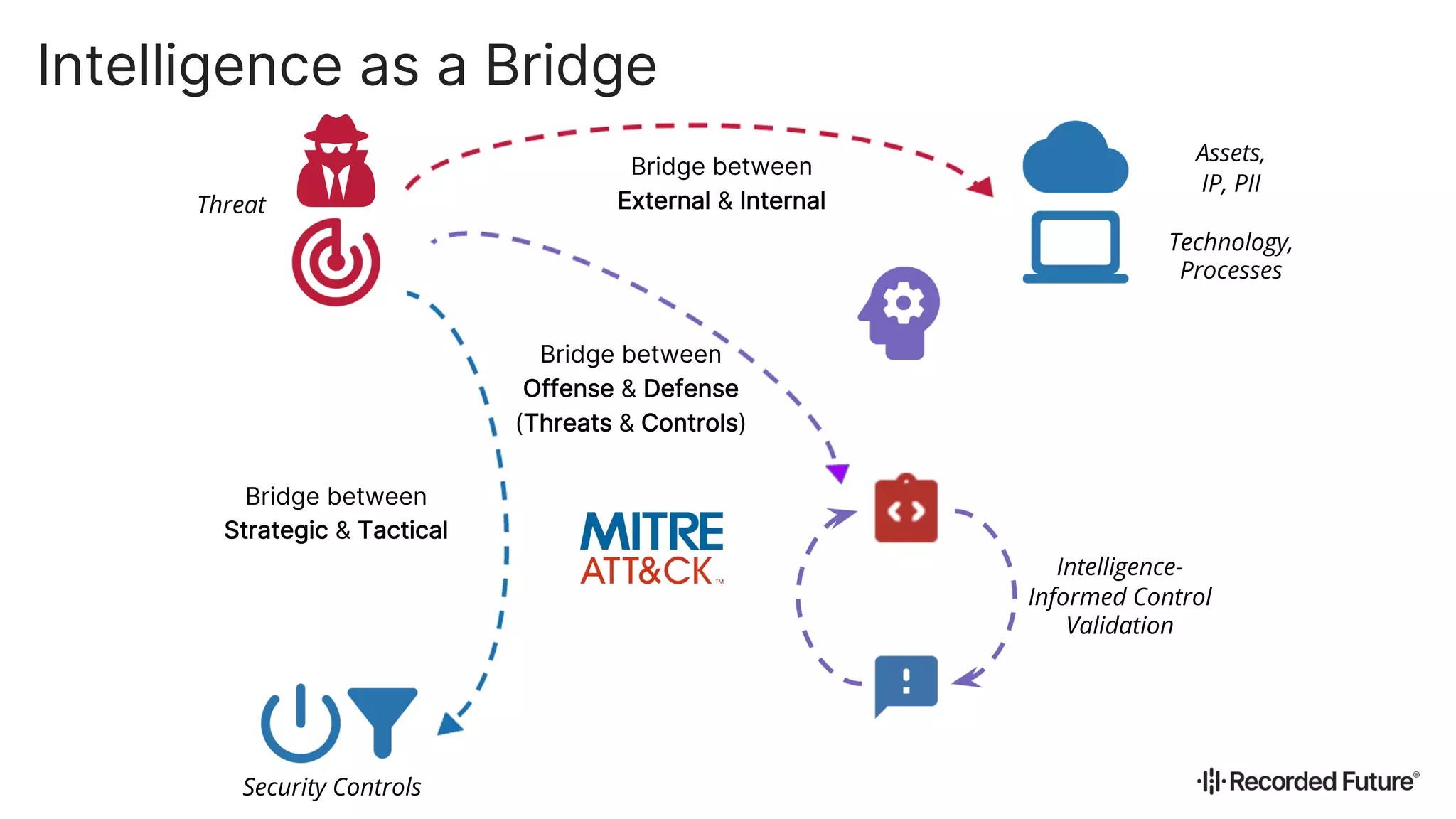
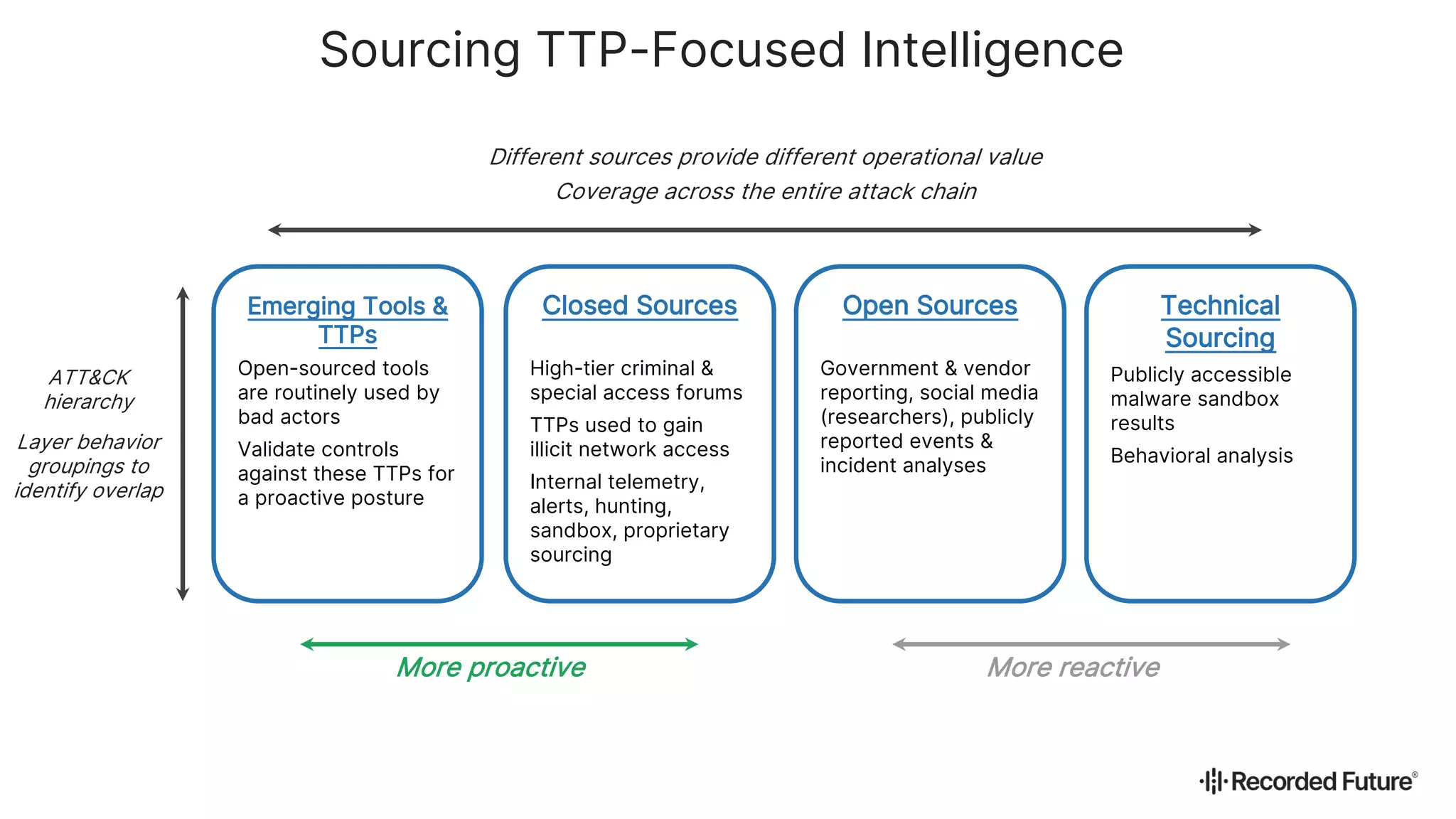
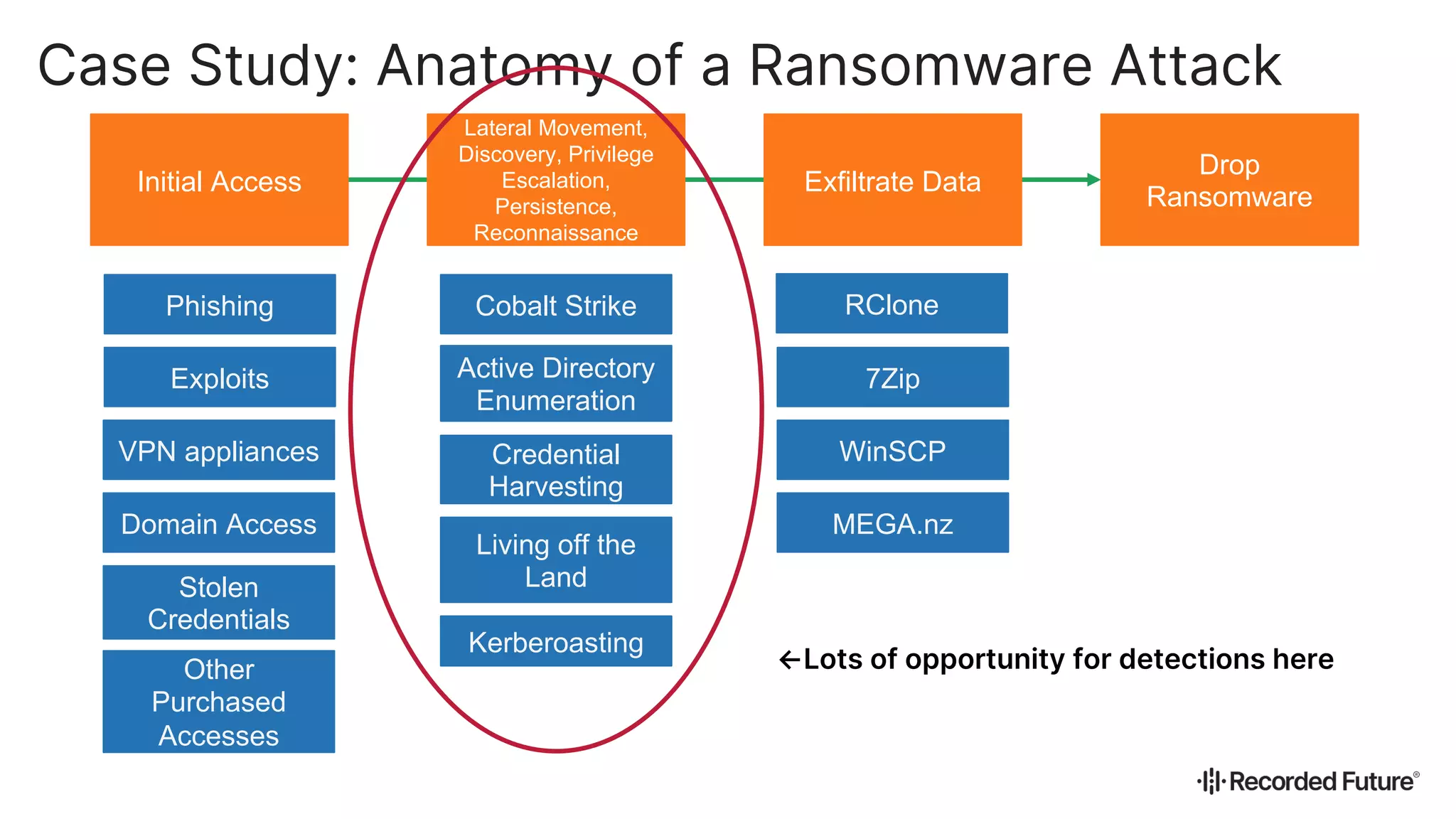
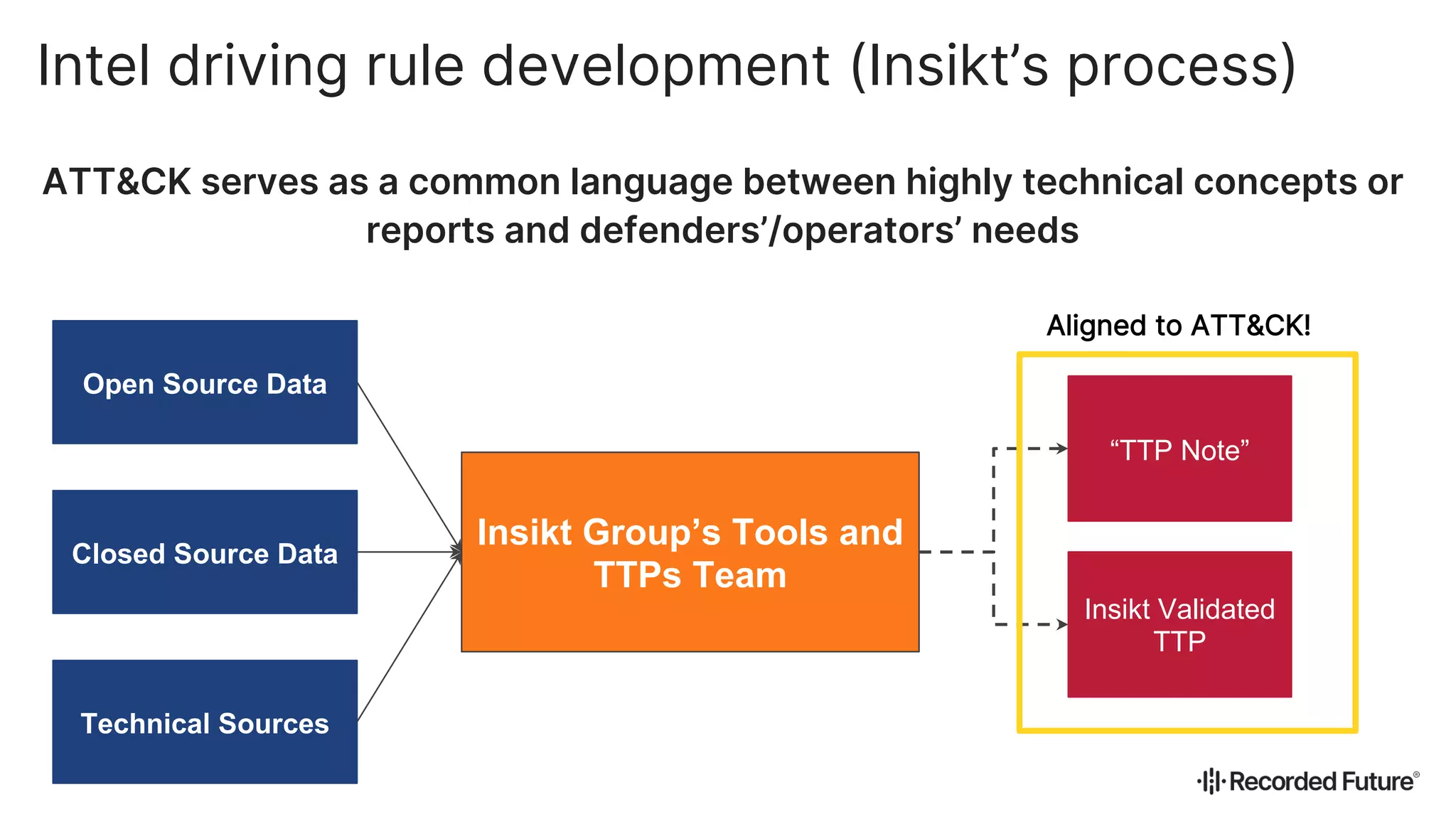
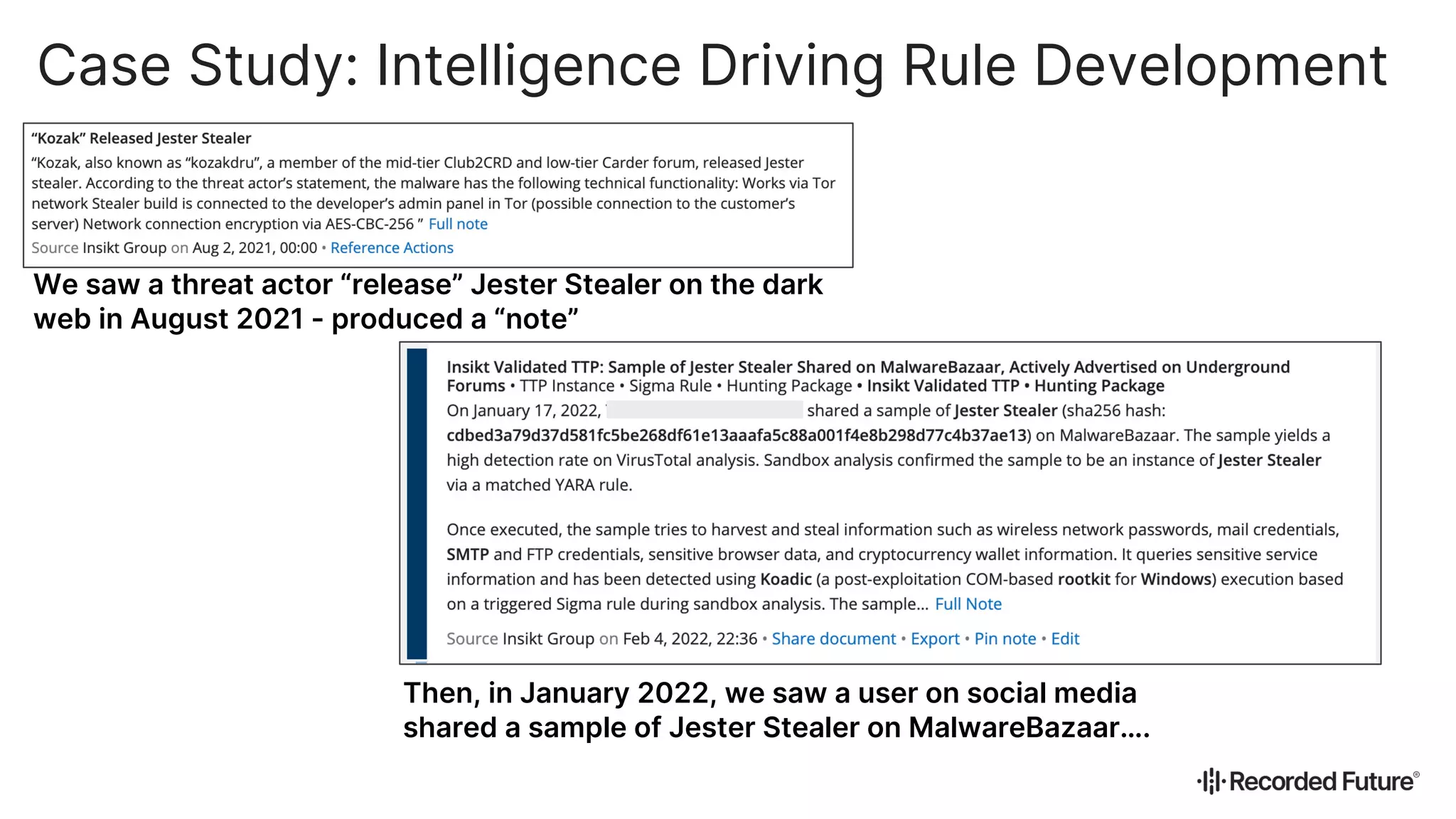
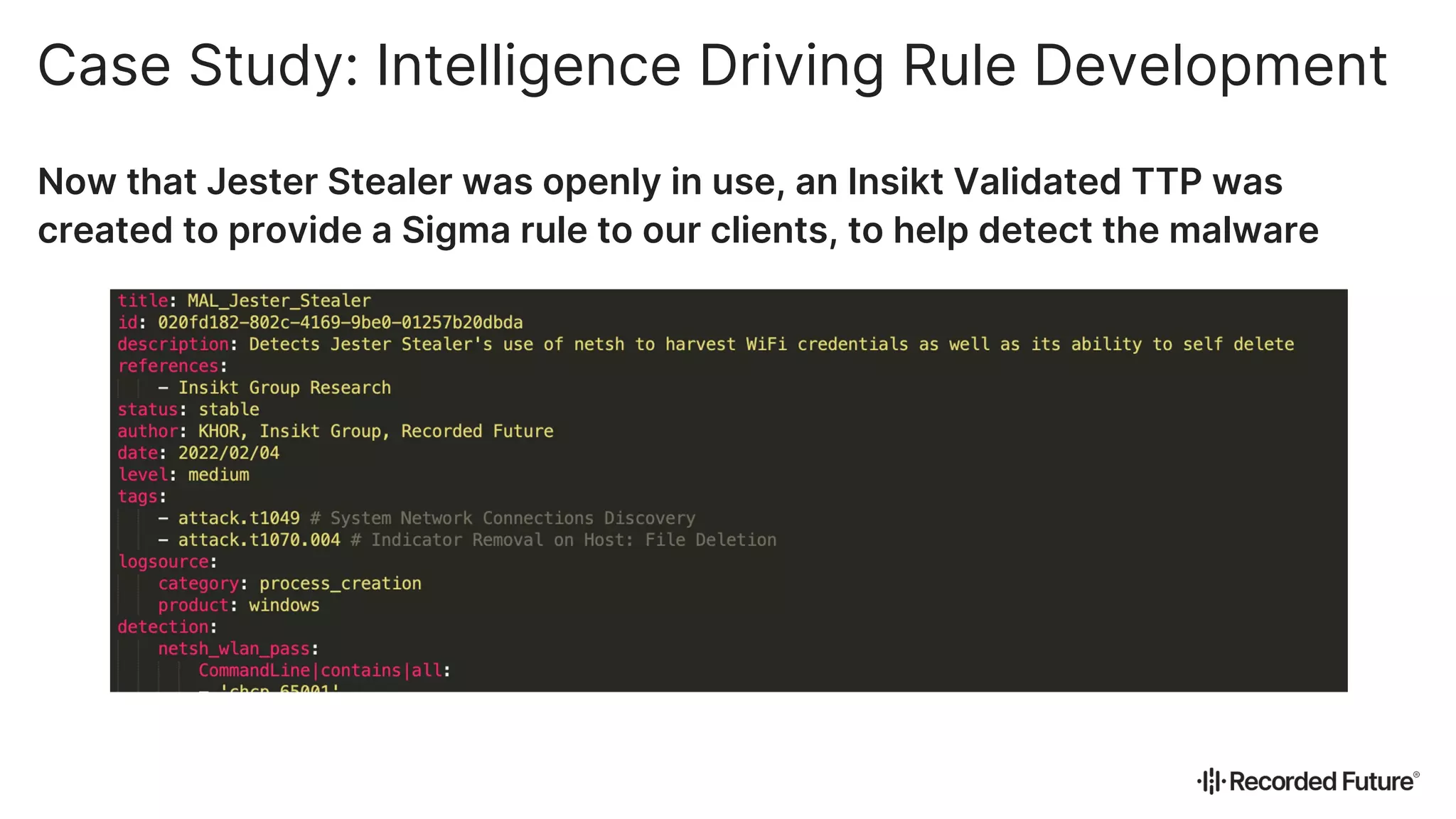
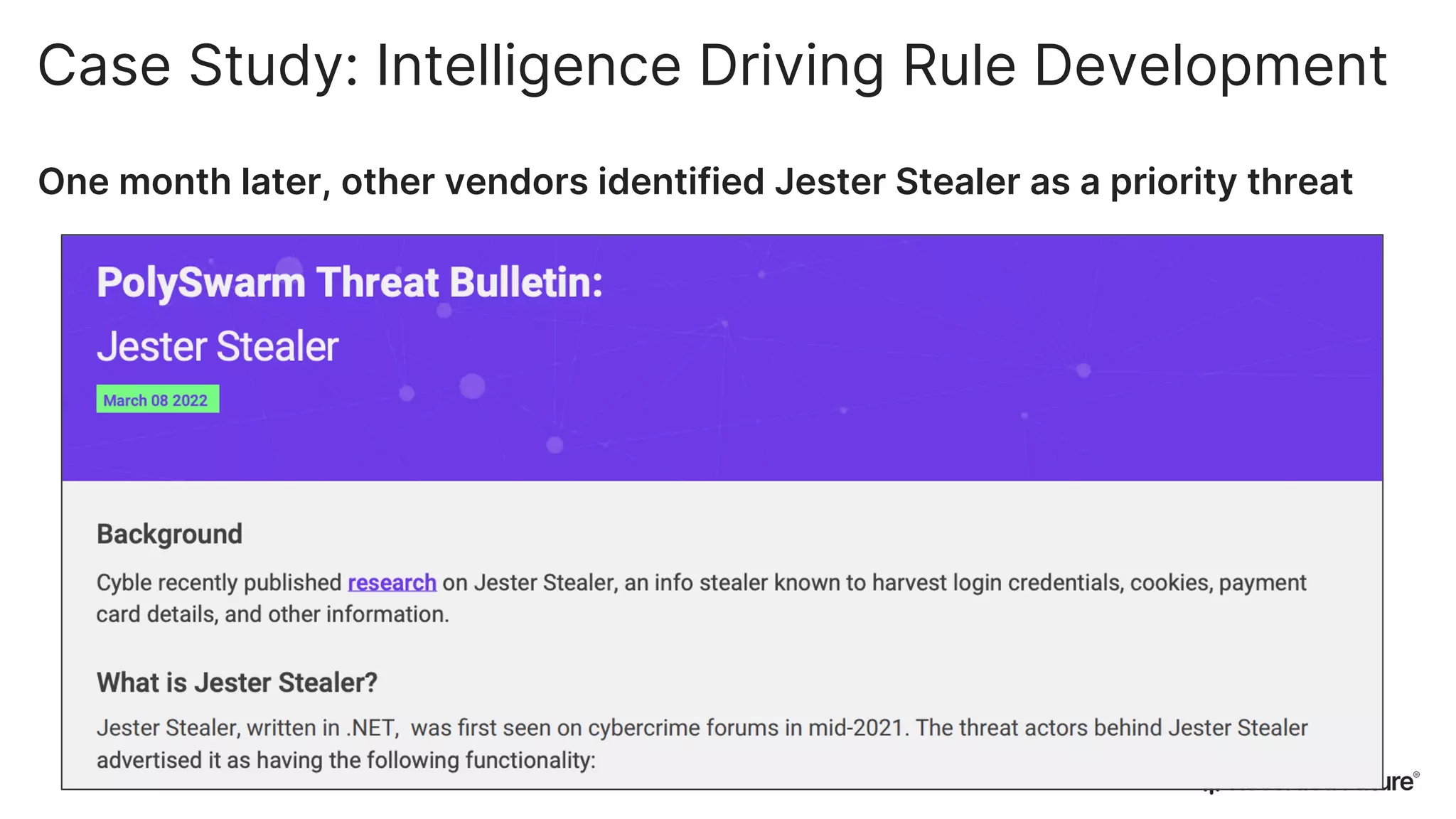
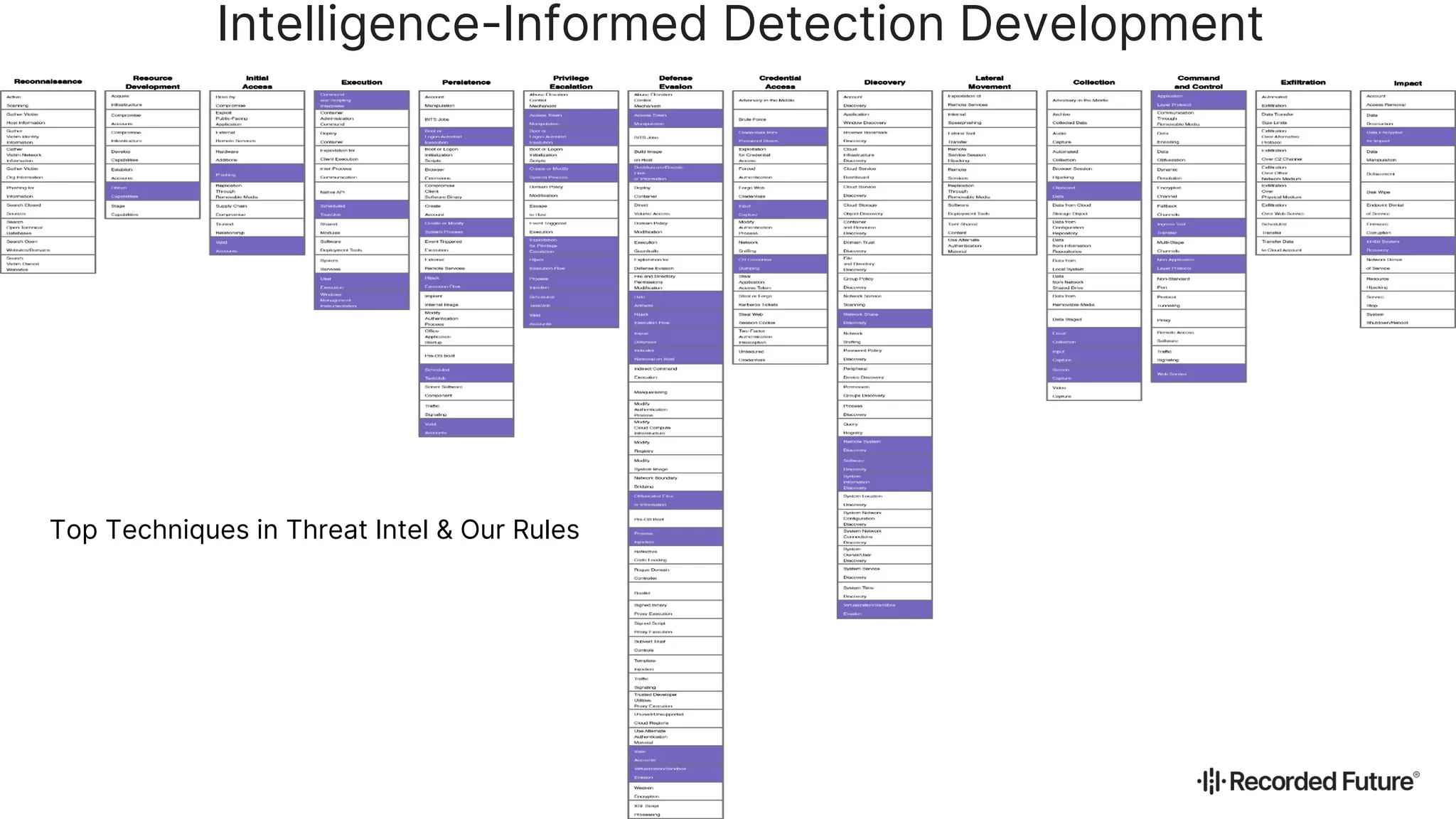
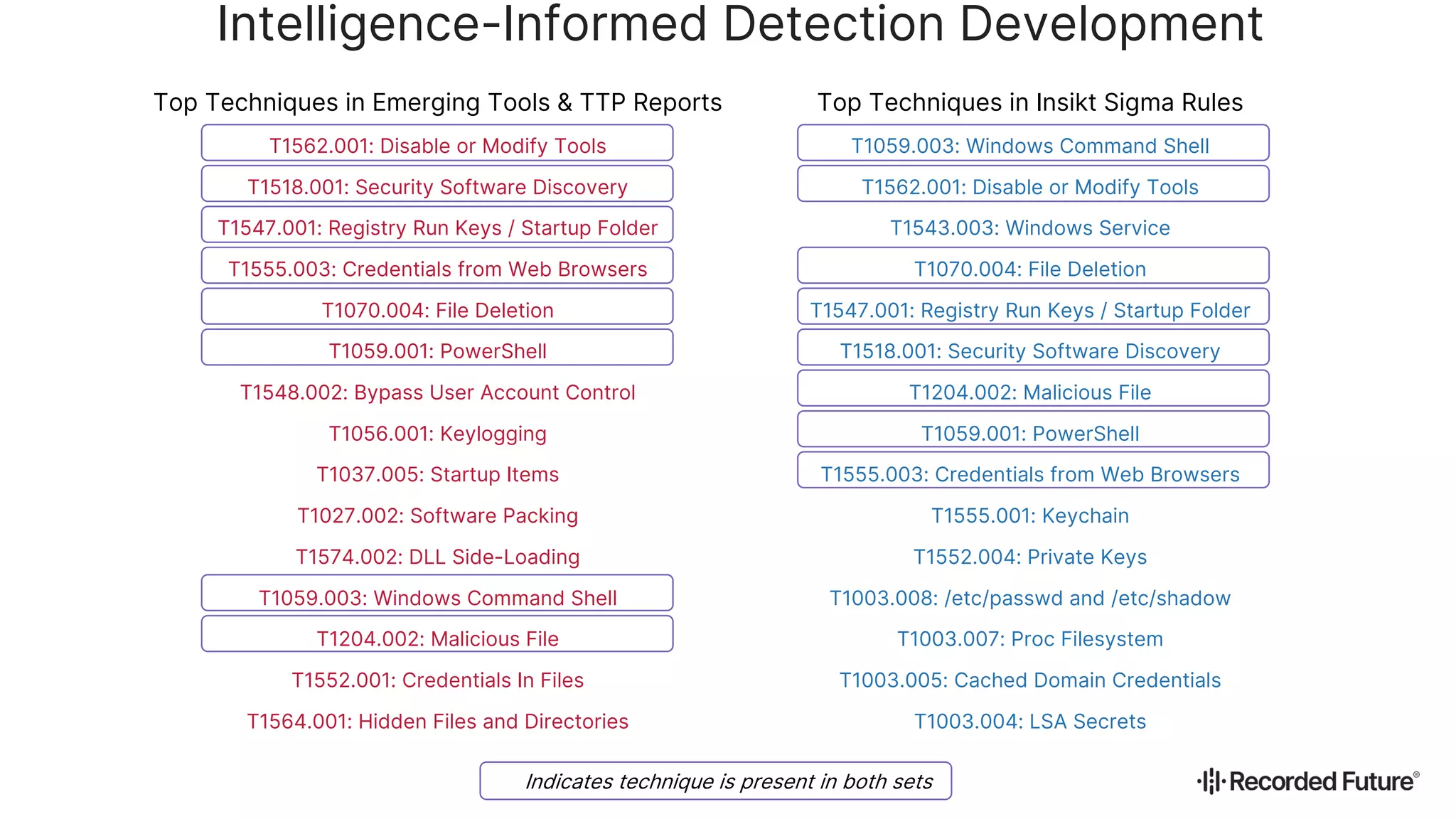
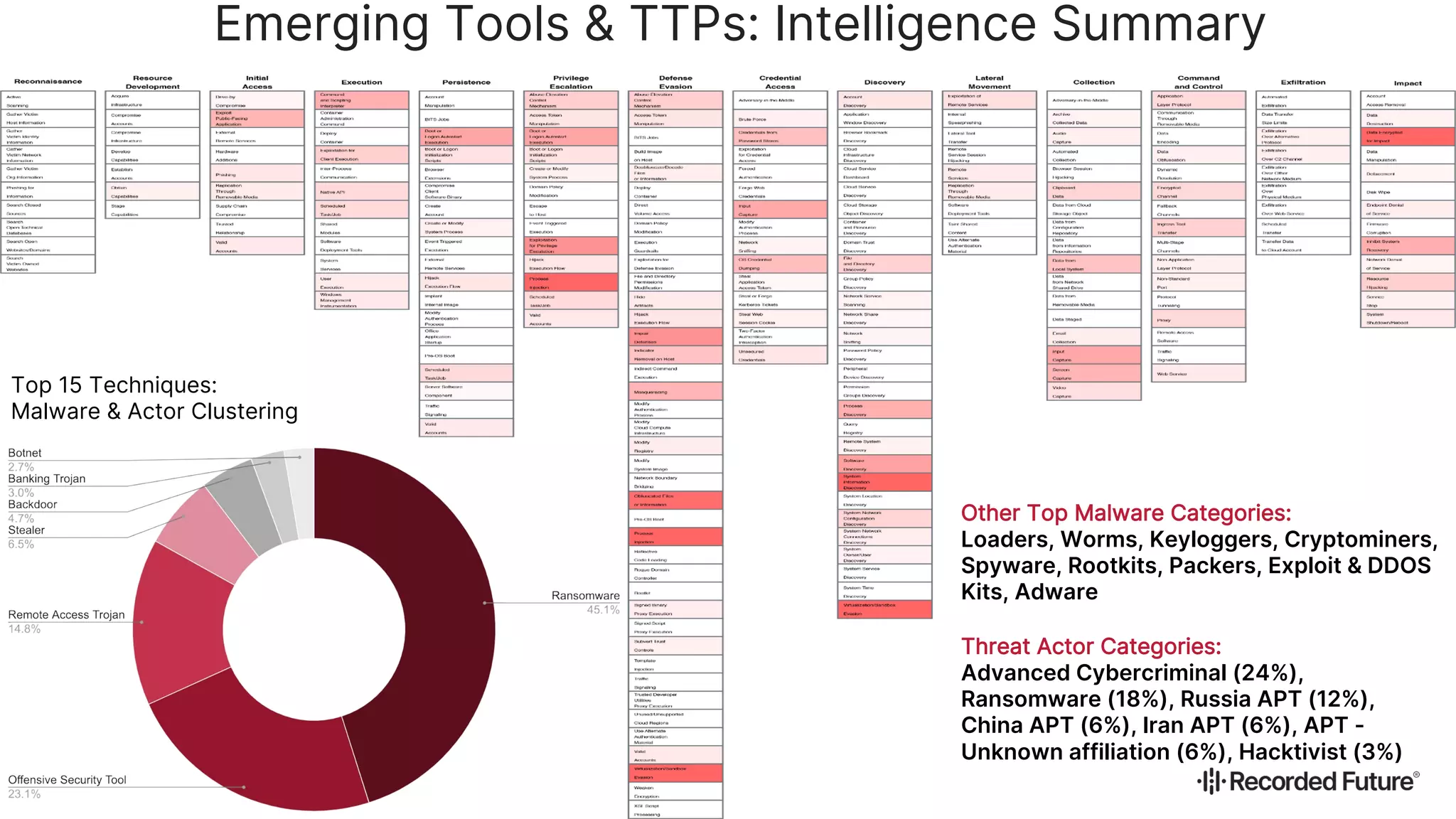
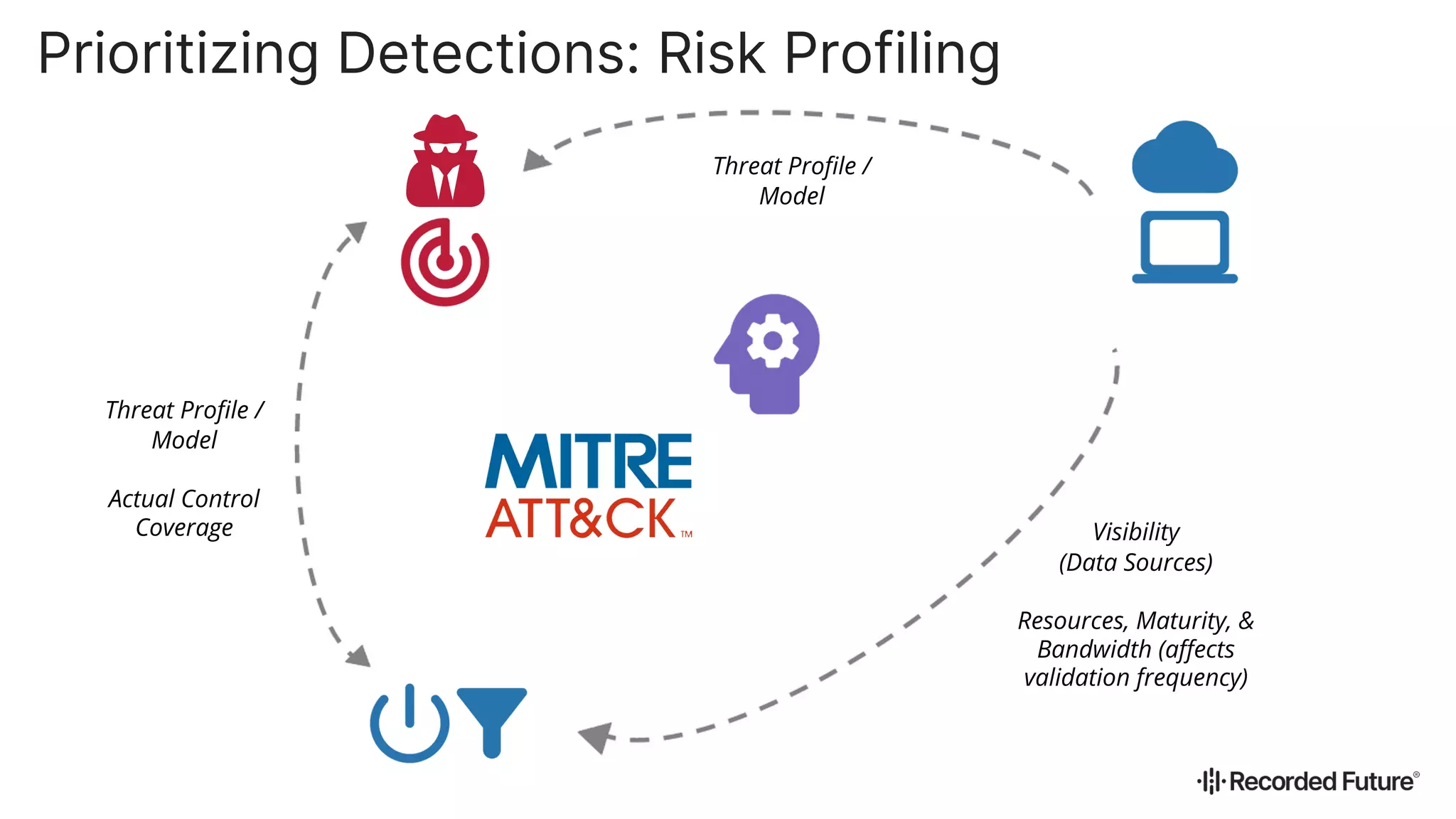
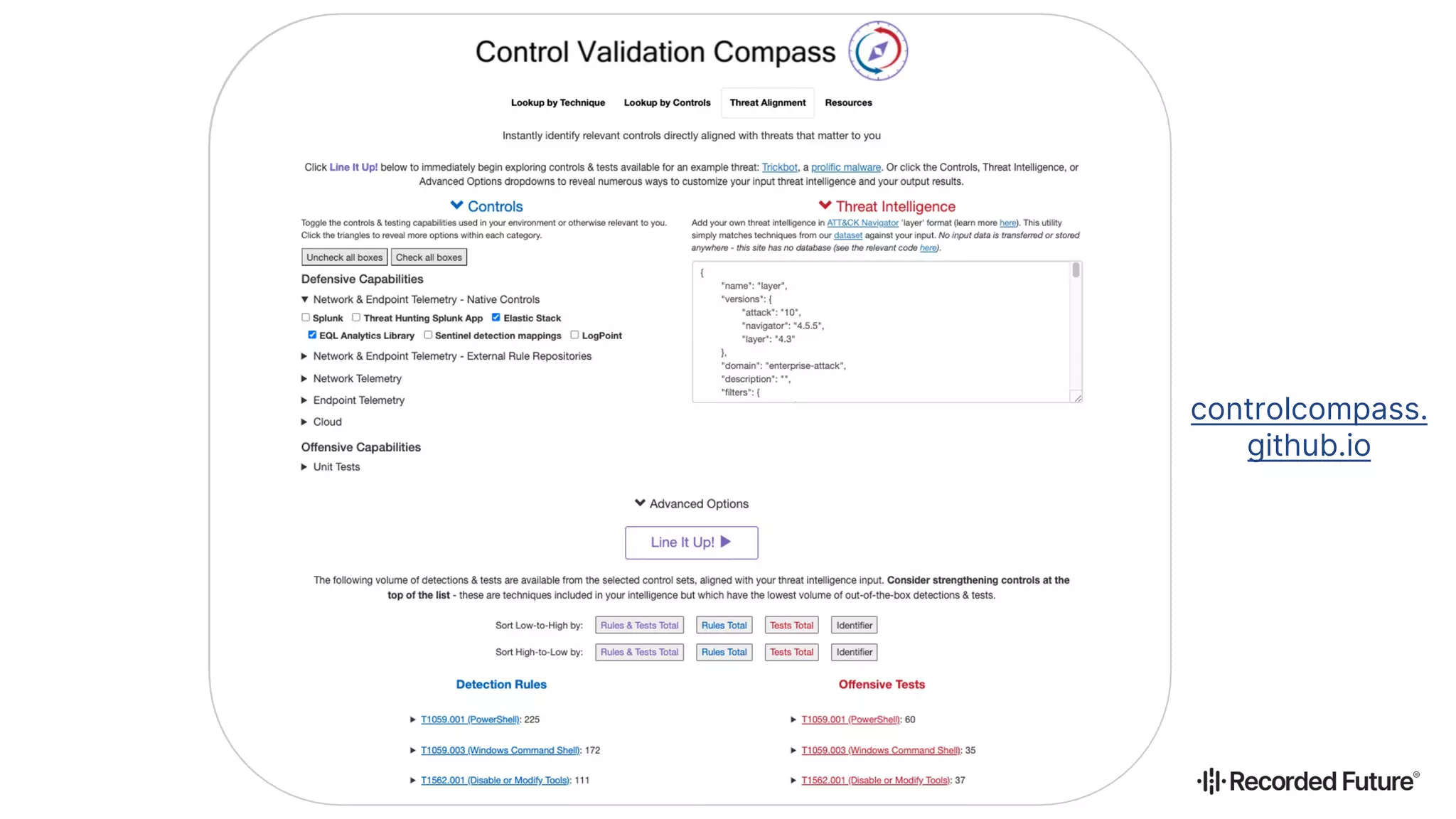
The document discusses the implementation of behavioral detections in cybersecurity using intelligence and the ATT&CK framework as a guiding methodology. It highlights the importance of bridging operational intelligence with security controls to effectively counter threats, including a case study demonstrating the proactive development of detection rules based on emerging malware. Additionally, it emphasizes the classification of threats and tactics, providing resources to guide cybersecurity teams in prioritizing detection efforts.