The document discusses security support for in-network processing in wireless sensor networks (WSNs) utilizing Zigbee technology, including capabilities such as data aggregation and command dissemination. It outlines various security mechanisms like one-way hash chains and μTESLA protocol to manage trust between nodes and aggregators, and describes several pairwise key management schemes for enhancing resilience. Additionally, it addresses network setup overhead, in-network processing performance, and key management protocols for clustered WSNs.
![Closest pair-wise keys pre-distribution scheme:
In this scheme Location information is used to improve the key connectivity. Sensor
nodes are deployed in a two dimensional area similar to a grid. All sensors locations
are predicted by a setup server. Each sensor shares pair-wise keys with its c closest
neighbors. In the key setup each sensor node SA is given a unique key KA and a set
“c” of it’s closest neighbors SB1, . . . , SBc are selected. For each pair (SA, SBi), a pair-
wise key KA,Bi = PRF(KBi |IDA) is generated. All these pair-wise keys and Ids makeup
the keychain of SA, Node SBi only stores the key KBi and the PRF. Each sensor uses
2c+1 units of memory to store its key-chain [3][4]. This scheme makes deployments
of new nodes easier, decreases memory usage, and has good key connectivity if
deployment errors are kept low.
ID based one-way function scheme (IOS):
This scheme is based on a connected r-regular graph G of the expected deployment.
The graph is composed of star-like sub graphs. The sub graphs are used to distributed
the pair-wise keys to the appropriate nodes. Each sensor node is the center of one
star-like graph and a leaf of r/2 star-like sub graphs. Each node uses r + 1 units of
memory to store keys and key IDs . Very good key resilience.
Multiple IOS:
Multiple IOS is meant to improve the scalability of ID based one-way function scheme](https://image.slidesharecdn.com/summarywsn-100617120849-phpapp01/75/Security-Support-in-In-Network-Processing-analysis-of-key-management-in-WSN-12-2048.jpg)
![(IOS). Every node in graph G corresponds to l nodes SA =SA1, . . . , SAl. Each sensor
node SAi stores a common key KA and a secret Hash(KB|IDAi). Every node SBj in the
class of node SB, can use common key KB to generate the secret Hash(KB|IDAi) for
node SAi [3][4]. Memory usage decreases by a factor of l.
Broadcast session key negotiation protocol (BROSK):
A single master key is pre-deployed to all sensor nodes. Sensor node pairs (Si, Sj) then
exchange randomnonce values. The master key Km is used to establish session key
Ki,j = PRF(Km|RNi|RNj). Only one unit of memory is used (by each node) to store the
master key. If the master keyis compromised, then all links are compromised
therefore the scheme has very low resilience .
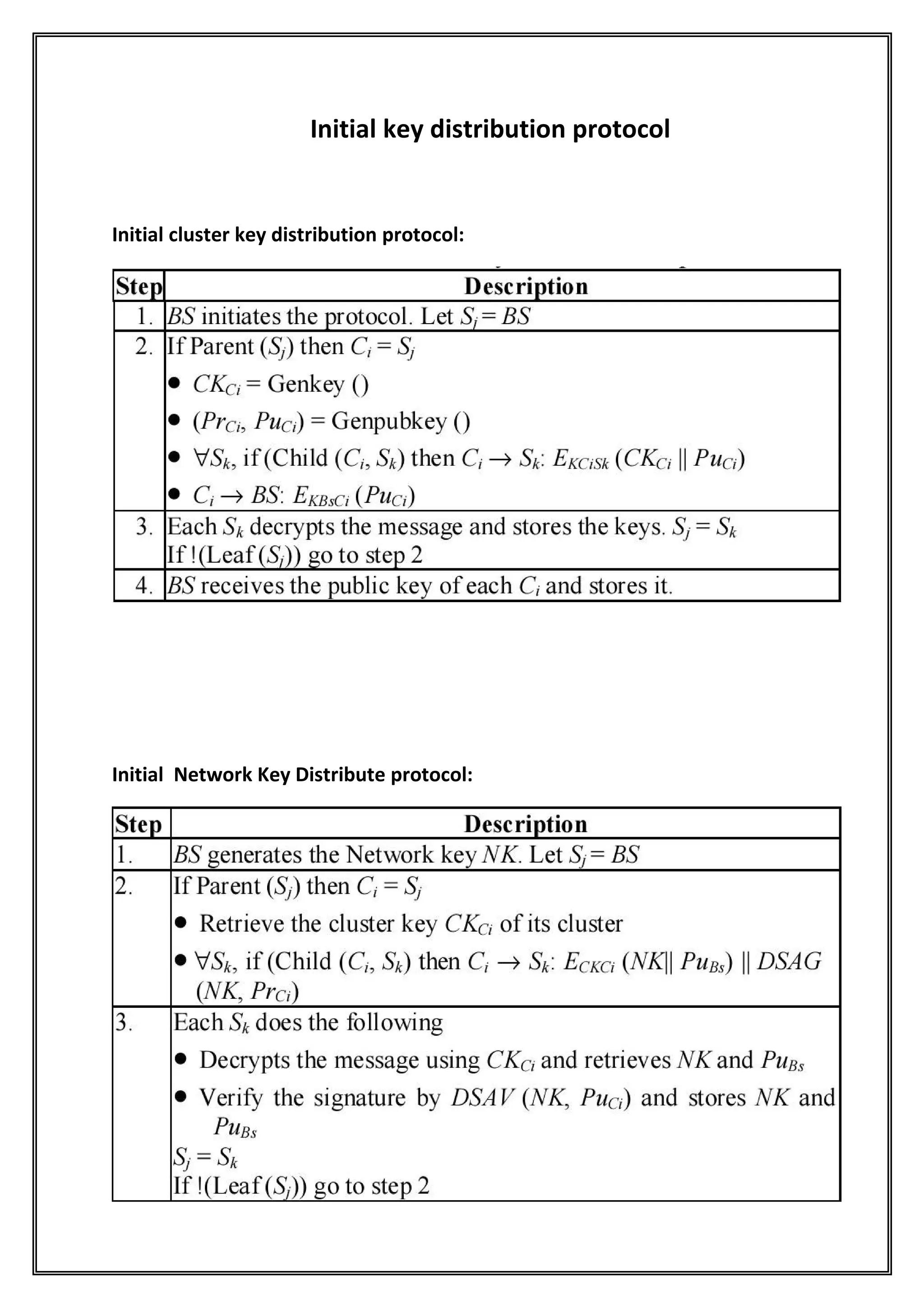
Protocols for Distributed Key Management in Clustered
Wireless Sensor Networks
Aim: To provide security to one-to-all and one-to-one communication
In WSN.
Related Terms:
Rekey Interval, Periodic Rekeying , Rekeying with Cluster Dynamics:
The Rekey Interval can be defined as the period with which encryption key of a node
is changed to a new one. If the network topology does not change within the rekey](https://image.slidesharecdn.com/summarywsn-100617120849-phpapp01/75/Security-Support-in-In-Network-Processing-analysis-of-key-management-in-WSN-13-2048.jpg)