Report
Share
Recommended
Recommended
More Related Content
Viewers also liked
Viewers also liked (20)
Similar to Bt0070 operating systems
PROCESS,THREAD,SYMMETRIC MULTIPROCESSOR,MICROKERNEL
BITS 1213 - OPERATING SYSTEM (PROCESS,THREAD,SYMMETRIC MULTIPROCESSOR,MICROKE...

BITS 1213 - OPERATING SYSTEM (PROCESS,THREAD,SYMMETRIC MULTIPROCESSOR,MICROKE...Nur Atiqah Mohd Rosli
Similar to Bt0070 operating systems (20)
LM9 - OPERATIONS, SCHEDULING, Inter process xommuncation

LM9 - OPERATIONS, SCHEDULING, Inter process xommuncation
SOLUTION MANUAL OF OPERATING SYSTEM CONCEPTS BY ABRAHAM SILBERSCHATZ, PETER B...

SOLUTION MANUAL OF OPERATING SYSTEM CONCEPTS BY ABRAHAM SILBERSCHATZ, PETER B...
BITS 1213 - OPERATING SYSTEM (PROCESS,THREAD,SYMMETRIC MULTIPROCESSOR,MICROKE...

BITS 1213 - OPERATING SYSTEM (PROCESS,THREAD,SYMMETRIC MULTIPROCESSOR,MICROKE...
Recently uploaded
Recently uploaded (20)
The Zero-ETL Approach: Enhancing Data Agility and Insight

The Zero-ETL Approach: Enhancing Data Agility and Insight
Event-Driven Architecture Masterclass: Challenges in Stream Processing

Event-Driven Architecture Masterclass: Challenges in Stream Processing
Intro to Passkeys and the State of Passwordless.pptx

Intro to Passkeys and the State of Passwordless.pptx
Event-Driven Architecture Masterclass: Engineering a Robust, High-performance...

Event-Driven Architecture Masterclass: Engineering a Robust, High-performance...
Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...

Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...
Observability Concepts EVERY Developer Should Know (DevOpsDays Seattle)

Observability Concepts EVERY Developer Should Know (DevOpsDays Seattle)
WebRTC and SIP not just audio and video @ OpenSIPS 2024

WebRTC and SIP not just audio and video @ OpenSIPS 2024
JavaScript Usage Statistics 2024 - The Ultimate Guide

JavaScript Usage Statistics 2024 - The Ultimate Guide
TrustArc Webinar - Unified Trust Center for Privacy, Security, Compliance, an...

TrustArc Webinar - Unified Trust Center for Privacy, Security, Compliance, an...
Introduction to FIDO Authentication and Passkeys.pptx

Introduction to FIDO Authentication and Passkeys.pptx
“Iamnobody89757” Understanding the Mysterious of Digital Identity.pdf

“Iamnobody89757” Understanding the Mysterious of Digital Identity.pdf
Harnessing Passkeys in the Battle Against AI-Powered Cyber Threats.pptx

Harnessing Passkeys in the Battle Against AI-Powered Cyber Threats.pptx
Cyber Insurance - RalphGilot - Embry-Riddle Aeronautical University.pptx

Cyber Insurance - RalphGilot - Embry-Riddle Aeronautical University.pptx
Microsoft CSP Briefing Pre-Engagement - Questionnaire

Microsoft CSP Briefing Pre-Engagement - Questionnaire
ChatGPT and Beyond - Elevating DevOps Productivity

ChatGPT and Beyond - Elevating DevOps Productivity
Hyatt driving innovation and exceptional customer experiences with FIDO passw...

Hyatt driving innovation and exceptional customer experiences with FIDO passw...
Bt0070 operating systems
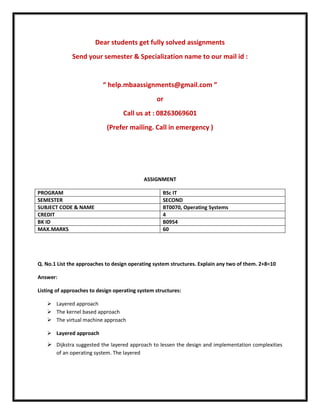
- 1. Dear students get fully solved assignments Send your semester & Specialization name to our mail id : “ help.mbaassignments@gmail.com ” or Call us at : 08263069601 (Prefer mailing. Call in emergency ) ASSIGNMENT PROGRAM BSc IT SEMESTER SECOND SUBJECT CODE & NAME BT0070, Operating Systems CREDIT 4 BK ID B0954 MAX.MARKS 60 Q. No.1 List the approaches to design operating system structures. Explain any two of them. 2+8=10 Answer: Listing of approaches to design operating system structures: Layered approach The kernel based approach The virtual machine approach Layered approach Dijkstra suggested the layered approach to lessen the design and implementation complexities of an operating system. The layered
- 2. 2 Write short notes on: 1. Process Creation 2. Terminating Process 5+5= 10 Answer: 1. Process Creation During the course of execution, a process may create several new proceses using a create-process system call. The creating process is called a parent process and the new processes are called the children of that process. Each of these new processes may in turn create other processes, forming a tree of processes. Process Termination A process terminates when it finishes executing its last statement and asks the operating system to delete it by using the exit system call. At that time, the process should return the data (output) ti its parent process via the wait system call. All the resources of the process, including physical and virtual memory, open files, and I/O buffers, are deallocated by the operating system. Only a parent process can cause 3 Is it possible to check the condition of mutual exclusion through hardware assistance? If yes, how? 10 Answer: Checking for mutual exclusion is also possible through hardware. Special instructions called Test and Set Lock (TSL) is used for the purpose. An important feature is that the set of instructions used for this purpose is indivisible, that is, they cannot be interrupted during execution. The instruction has the format TSL ACC, IND where ACC is an accumulator register and IND is a memory location used as a flag. Whenever the instruction is Q4
- 3. 1. Given a total of 5 units of resource type 1 and 4 units of resource type 2, tell whether the following system is in a safe or unsafe state. Show your work. Type 1 Type 2 Process Used Max Used Max P1 1 2 1 3 P2 1 3 1 2 P3 2 4 1 4 5. What is the concept of virtual memory? Why virtual memory is needed? 3+7= 10 Answer: Virtual memory is a technique that allows execution of processes that may not be entirely in memory. In addition, virtual memory allows mapping of a large virtual address space onto a smaller physical memory. It also raises the degree of multi-programming and increases CPU utilization. Because of the above features, users are freed from worrying about memory requirements and availability. Need for Virtual Memory Technique Every process needs to be loaded into 6 What do you mean by Global OS? State the concept of migration and resource allocation in Global OS. 4+6= 10 Answer: Global Operating System (GOS) The NOS is responsible for activities such as memory and process management on the server. The NOS converts a request into a task, schedules and executes it. Memory and processing power in all other computers in the network is not tapped to the maximum by a NOS. This is exactly what the GOS attempts to do. It has a list of processes executing on different machines and the resources needed by each one of them. Relatively free Dear students get fully solved assignments Send your semester & Specialization name to our mail id : “ help.mbaassignments@gmail.com ” or
- 4. Call us at : 08263069601 (Prefer mailing. Call in emergency )
